What is adware?
Adware is a type of malicious software that secretly installs itself on your device and displays unwanted advertisements and pop-ups. In some cases, adware can even track your online behavior and display personalized ads. Adware is short for advertising supported software, designed to throw advertisements up on your screen, most often within a web browser. Some security professionals view it as the forerunner of the modern-day PUP (potentially unwanted program). Typically, it uses an underhanded method to either disguise itself as legitimate, or piggyback on another program to trick you into installing it on your PC, tablet, or mobile device.

“Adware is unwanted software designed to throw advertisements up on your screen.”
Here’s how it happens. You go online with your nice, well-behaved browser, only to see it fly into a virtual tantrum, as an onslaught of advertisements either pops up, slides in from the side, or otherwise inserts itself to interrupt and even redirect your intended activity. And no matter how much you click to close those windows, they keep buzzing you like flies at a picnic.
Adware generates revenue for its developer by automatically displaying online advertisements in the user interface of the software or on a screen that pops up in the user’s face during the installation process. And that’s when you start seeing dubious miracle weight loss programs, offers for get-rich-quick secrets, and bogus virus warnings that invite your click. Also, you might experience new tabs opening, a change in your home page, findings from a search engine you never heard of, or even a redirect to a NSFW website.
Mind you, it does happen that legitimate software applications do use online advertising, with ads that are typically bundled within the program and that display in ways the program developer specified. Adware is an altogether different kettle of rotten fish. You might download it without understanding its intent. Or it might land on your PC by means of legitimate software within which it’s secretly buried. Whatever the path, it all boils down to some program on your computer showing you advertisements that do not come from the websites you are visiting.
Once adware hijacks your device, it might carry out all sorts of unwanted tasks. The software’s functions may be designed to analyze the location and which Internet sites you visit, and then present advertising pertinent to the types of goods or services featured there. While adware is more of a pesky nuisance than a harmful malware threat to your cybersecurity, if the adware authors sell your browsing behavior and information to third parties, they can even use it to target you with more advertisements customized to your viewing habits. And it doesn’t matter whether you are using Chrome, Firefox, or other browsers: It affects all of them.
Here are a few typical telltale signs that you have adware on your system:
- Advertisements appear in places they shouldn’t be.
- Your web browser’s homepage has mysteriously changed without your permission.
- Web pages that you typically visit are not displaying properly.
- Website links redirect to sites different from what you expected.
- Your web browser slows to a crawl.
- New toolbars, extensions, or plugins suddenly populate your browser.
- Your Mac starts automatically installing unwanted software applications.
- Your browser crashes.
Stop annoying adware from spamming your device
Ads slowing your device down? Scan and remove adware that’s hiding on your device.
Try Malwarebytes Premium free for 14 days.
How do I get adware?
There are two main ways by which adware sneaks onto your system. In the first one, you download a program—usually freeware or shareware—and it quietly installs adware without your knowledge, or permission. That’s because the program’s author signed up with the adware vendor. Why? Because the revenue generated by the advertisements enables the program to be offered gratis (although even paid software from an untrustworthy source can deliver an adware payload). Then the adware launches its mischief, and the user learns there’s a price to pay for “free.”
“There are two main ways by which adware sneaks onto your system.”
The second method is just as insidious. You’re visiting a website. Maybe it’s a trusted site; maybe it’s a sketchy one. Either way, it can be infected with adware, which takes advantage of a vulnerability in the user’s web browser to deliver a drive-by download. After it burrows in, the adware starts collecting your information, redirecting you to malicious websites, and throwing more advertisements into your browser.
Types of adware
For all the ways adware tries to dig into your PC or other device, most adware strategies qualify as browser hijackers. These interlopers specialize in modifying Internet browser settings without the user’s knowledge or consent. Typically, hijackers change the homepage and default search settings. You’re happily surfing along when suddenly the ads start pummeling you. You might naturally assume that the ads originate from the site you’re visiting, but they aren’t. But since they appear in the form of pop-ups or pop-unders, they seem that they are embedded in the site itself.
Once again, there are adware programs that change your start page, your search engine, or even fiddle with the shortcuts on your computer that open your browsers. There is also, of course, different adware for different devices and operating systems. So you might have to cope with mobile/Android adware, Mac adware, or Windows adware.
History of adware
In the beginning, meaning from roughly 1995 on, industry experts considered the first ad-supported software to be part of the larger category of spyware. Soon, security professionals began to differentiate adware from spyware as a less harmful type of PUPs. They were even seen as “legitimate,” at least in theory, because legal businesses with actual offices and payrolls were creating adware software.
But the affiliates to these legitimate businesses often spread their adware without themselves being checked for legitimacy by the adware vendor. Unchecked, the adware proliferated by every means at their disposal—peer-to-peer sites, botnets, instant messaging infections, and the aforementioned browser hijacks.
With enough time, adware vendors started to shut down their badly behaved affiliates, and issued denials of responsibility for the affiliate’s actions. This was a common pattern of activity during peak adware years, which flourished from about 2005 to 2008. After that, governing authorities started to issue large fines for these offenses, which drove the biggest adware players to pick up their code and leave. More recently, browsers have been cracking down with adblockers, and adblock plugins are ubiquitous. Although these measures protect users from adware, they also cause websites to lose revenue from legitimate ads.
Today, although adware persists, it is usually viewed as a form of PUP, which presents a threat level below the category of malware. Nonetheless, adware remains popular and always charts highly in our analysis of top consumer detections. In the second half of 2018, adware placed second behind banking Trojans (e.g. Emotet) as the number one consumer detection. One reason is, the volume of adware is on the rise, perhaps thanks to proliferation of mobile devices and adware making its way into mobile apps. However, adware makers today are consolidating power. In order to stay afloat, they’re using techniques more aggressive than simply hijacking, including hiding within Trojans, bundling with adfraud components, or demonstrating rootkit capability, making them difficult to remove.
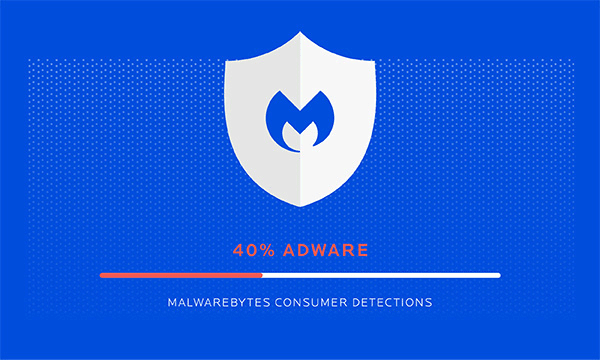
“Adware is now Malwarebyte’s top consumer detection.”
Mac adware
It used to be that Mac users had no adware fears. For one thing, Macs have a built-in anti-malware system called XProtect, which does a decent job of catching known malware. Then there’s the fact that cyber criminals focus mostly on Windows PCs, as they are a more prolific target compared to the installed Mac base. But recently that’s changed fast. According to counts of the number of new Mac malware families to appear in 2017, they increased by more than 270 percent compared to those in 2016. Adware specifically for Macs first started to emerge in 2012; and since then, Mac adware variants have proliferated, developed both in secret by hackers and organized crime bad guys, as well as by seemingly legitimate corporations who claim to sell bona fide software with real-world uses. In the latter instance, the adware hides in plain sight as fine print in a long, small-type installation agreement. You know, the kind nobody reads. So when you click on the agreement, you accept its terms, and viola, the spam ensues. Those behind the adware are not doing anything illegal. At least technically, that is.
For the most part, adware for Macs rides inside a Trojan, malware that takes its name from the Trojan horse of Greek mythology. The Trojan portrays itself as something you want. Maybe a player, or some kind of plug-in. It might even be skulking around inside a legitimate software download from a disreputable site. Either way, it promises you one thing, but delivers adware in a bait-and-switch.
As far as the signs of a Mac adware infection go, they mirror the symptoms you see on Windows systems. Ads pop up where they shouldn’t be—literally everywhere. Something changes your homepage without so much as a how do you do. Familiar web pages just don’t look right anymore, and when you click on a link, you find yourself redirected to an entirely different site. It might even substitute a new search engine for your regular one.
So in the end, Macs, while less vulnerable than Windows computers, can still have a security problem with adware. More on what to do about it below.
Mobile adware
There’s not much real estate room on a mobile’s screen. So when a mysterious icon moves into your start screen, or scads of ads start clogging your notification bar, you’ve probably got an uninvited adware guest. No big surprise, since thousands of Android apps now contain the gift that keeps on shoving icons and ads at you without warning.
There are two methods through which mobiles come down with adware: through the browser and through downloaded applications.
- Infection by browser refers to a known exploit, caused by the way most browsers handle redirections executed by JavaScript code. It’s a weakness that can cause ad pop-ups; and advertising affiliates know about it, and how to exploit it. If your mobile’s browser has been compromised, then the best way to block the pop-ups is to use a different browser, disable JavaScript, or install a browser with ad blocking. Another remedy to pop-ups is to back out of them using Android’s back key. Or you can clear your history and cache, which will also stop the ads from coming back.
- Infection by downloaded applications refers to getting infected with persistent ads through adware apps installed on a phone. They present in different forms, from full screen ads inside and outside of the infected app, to the device notifications and on the lock screen. Typically, a third-party app store installs this kind of adware app. So it’s best to avoid third-party app stores, although even Google Play has been an unwitting source of adware-infested apps.
Despite its being an annoying pest, take some small comfort in the fact that such adware is generally not blatantly malicious, threatening your device like malware might. Many of the free apps you download to your phone often include third-party ad content, providing software developers an alternative revenue stream so you can have their offering for free. Still, adware is not generally benevolent; so faced with a free app that stuffs your device with adware, and a paid program that plays nicely, consider the best choice for you.
Who do adware authors target?
Conventional wisdom is, adware’s main intended victims are individuals, as opposed to businesses. And it follows the individual user across any path of opportunity—from Windows PCs and Macs, to mobile phones, and virtually all browsers. It calls to potential victims through the “too good to be true” model, offering something for nothing in a scam that can suggest new games, movies, or special deals.
“Adware’s main intended victims are individuals.”
How to remove Adware?
If you suspect adware has compromised your Mac or Windows PC, there are a few steps you can take to remedy the infection. First, back up your files, regularly. You can try to remove the adware through the pertinent utility on your operating system (i.e., Add/Remove on the Windows platform). But this requires that you can identify the adware program’s name, or that the adware doesn’t have a Resuscitator, which are files designed to bring a program back to life after an uninstall.
If that is the case, then download a legitimate cybersecurity program such as Malwarebytes for Windows, Malwarebytes for Mac, Malwarebytes for Android, Malwarebytes for Chromebook, and Malwarebytes for iOS. All are free to try, and are designed to search and destroy adware, PUPs, and any new forms of malware lurking on the scene. Run a scan and, if there are any nasties hiding away in your machine, it’ll bag, tag, and dump them for you. At this point, it’s a good idea to change your password, not only for your PC, but also your email, your social media accounts, your favorite shopping sites, and your online billing centers.

For a deeper dive, read:
How do I protect myself from adware?
Use caution and practice safe computing. That means thinking twice before immediately downloading and installing any new software—especially freeware. Read the terms and conditions like a lawyer before agreeing to them, and quit out of the download process if anything smells like a permission to load adware. Avoid torrent sites, illegal downloads, and never ever open an app from an unknown source, even if it comes to you under the guise of a known email contact.
Finally, even before all the above precautions, download a reputable cybersecurity program for your PC or mobile phone. Perform scans frequently, and keep your updates, well, up to date. Of course, we recommend any of our Malwarebytes family of anti-malware products as a prudent measure: Malwarebytes for Windows, Malwarebytes for Mac, Malwarebytes for Android, Malwarebytes for Chromebook, and Malwarebytes for iOS. By arming yourself with knowledge, and protecting yourself with a robust cybersecurity program, you can take the steps necessary for an adware-free life online.