It’s no secret that ransomware is one of the most pressing cyber threats of our day. What worse, ransomware gangs have increased their attacks on a range of vulnerable industries, with disruptions to business operations, million-dollar ransom demands, data exfiltration, and extortion.
With Malwarebytes Endpoint Detection and Response, however, you can fight—and defeat—advanced ransomware that other security solutions miss.
In this post, we’ll walk through what it looks like to deal with a ransomware attack using Malwarebytes EDR.
- Part 1: Your data has been encrypted!
- Part 2: Pinpointing the ransomware
- Part 3: Isolating the endpoint infected with ransomware
- Part 4: Remediating the ransomware
- Accelerate and simplify your ransomware defense with Malwarebytes EDR
Part 1: Your data has been encrypted!
Prior to this demo, we ran a ransomware sample on the virtual machine (VM) that we’ll be demonstrating from. Below, you’ll see that the VM is currently in an infected state.

As you can see, our files have in fact been encrypted by the ransomware across multiple directories with the “.encrypt” extension.
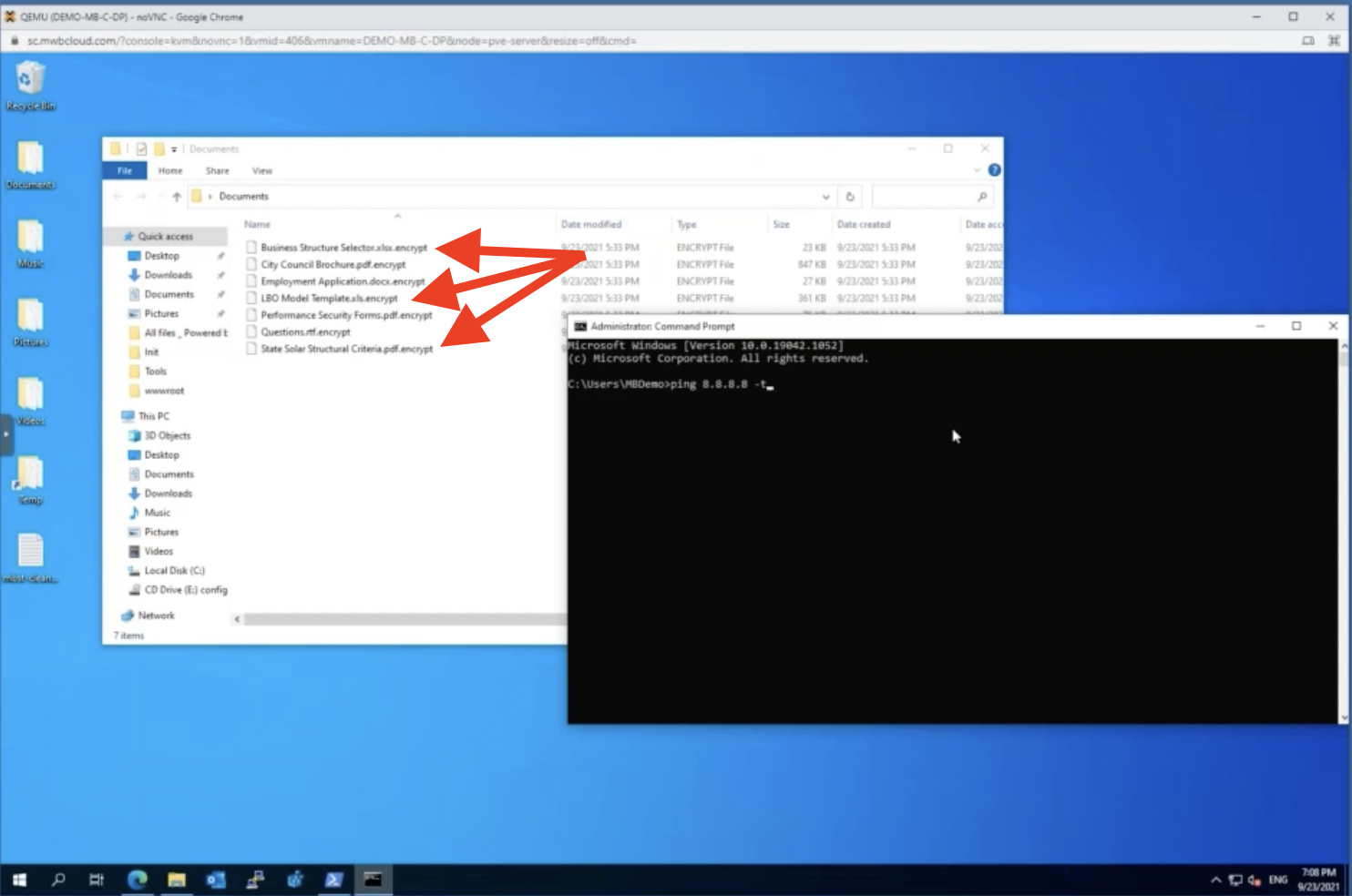
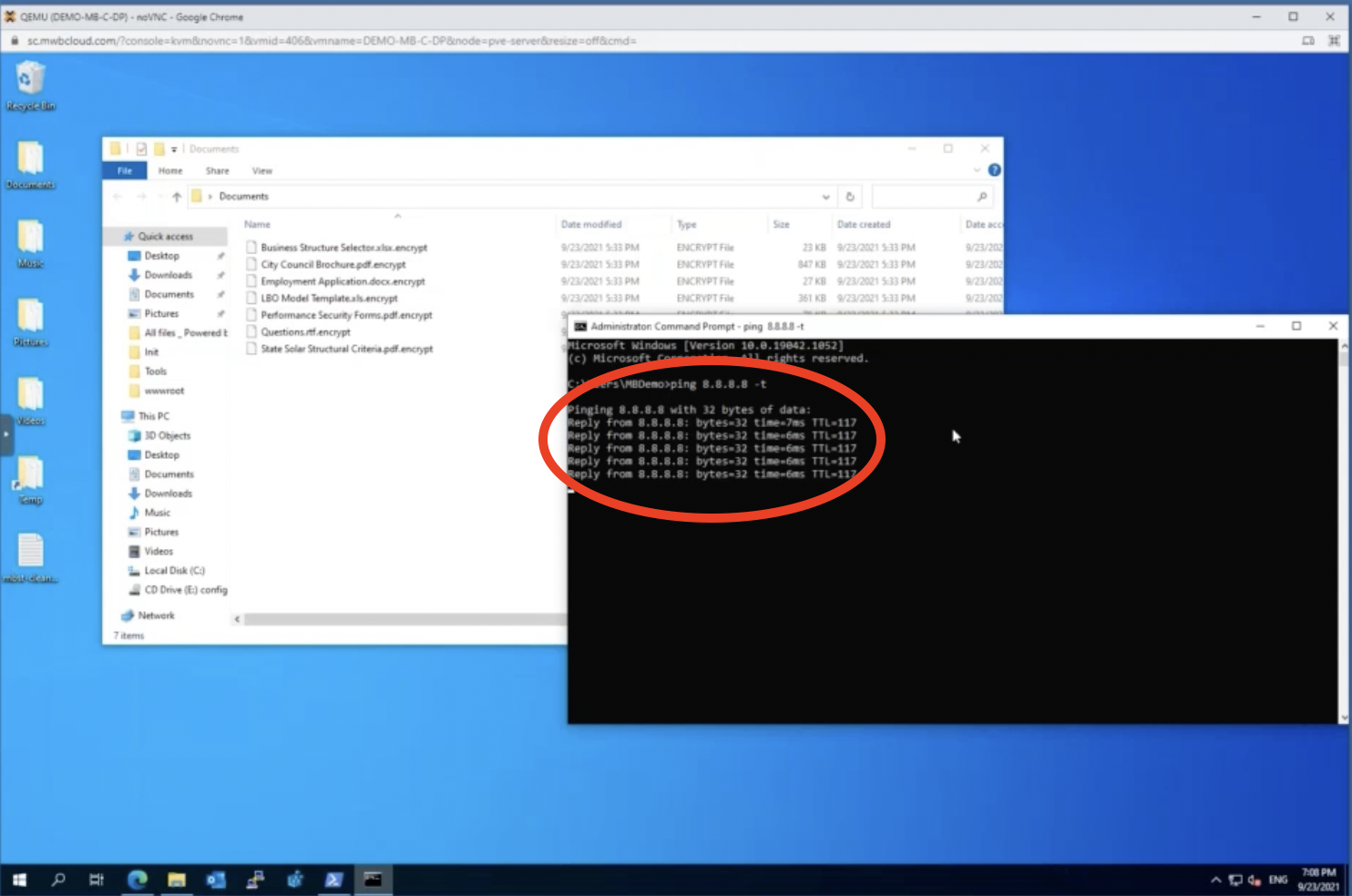
Let’s start a ping to Google’s DNS server. The reason that we’re going to do this is to help demonstrate some of the functionality that Malwarebytes has later.
Just keep in mind that right now we can effectively communicate out to the internet. But we’ll come back to that later.
Part 2: Pinpointing the ransomware
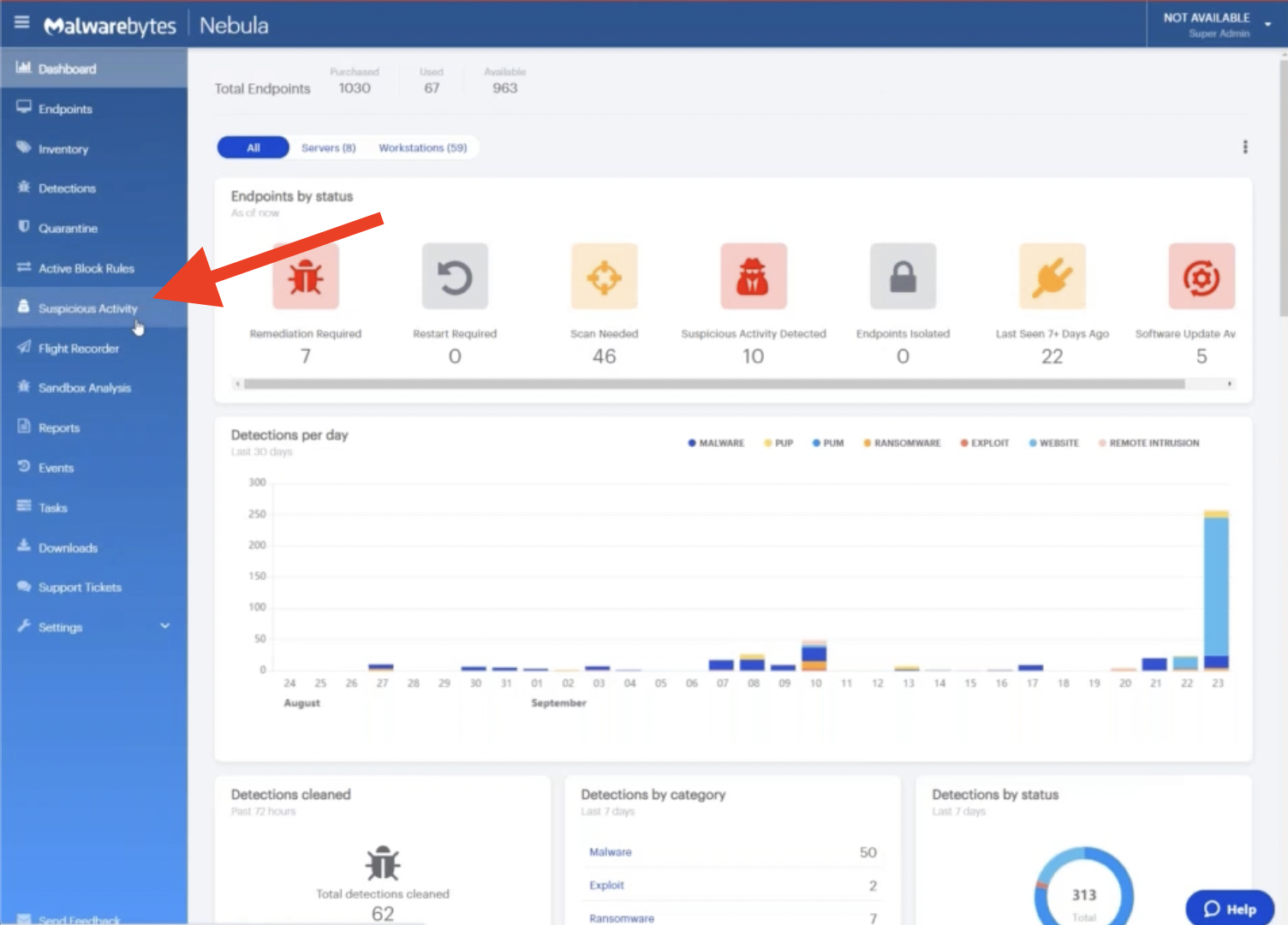
Now, let’s switch to our Nebula console. Below, you’ll see the dashboard for Malwarebytes Nebula, our cloud-hosted security operations platform that allows you to manage control of any malware or ransomware incident.
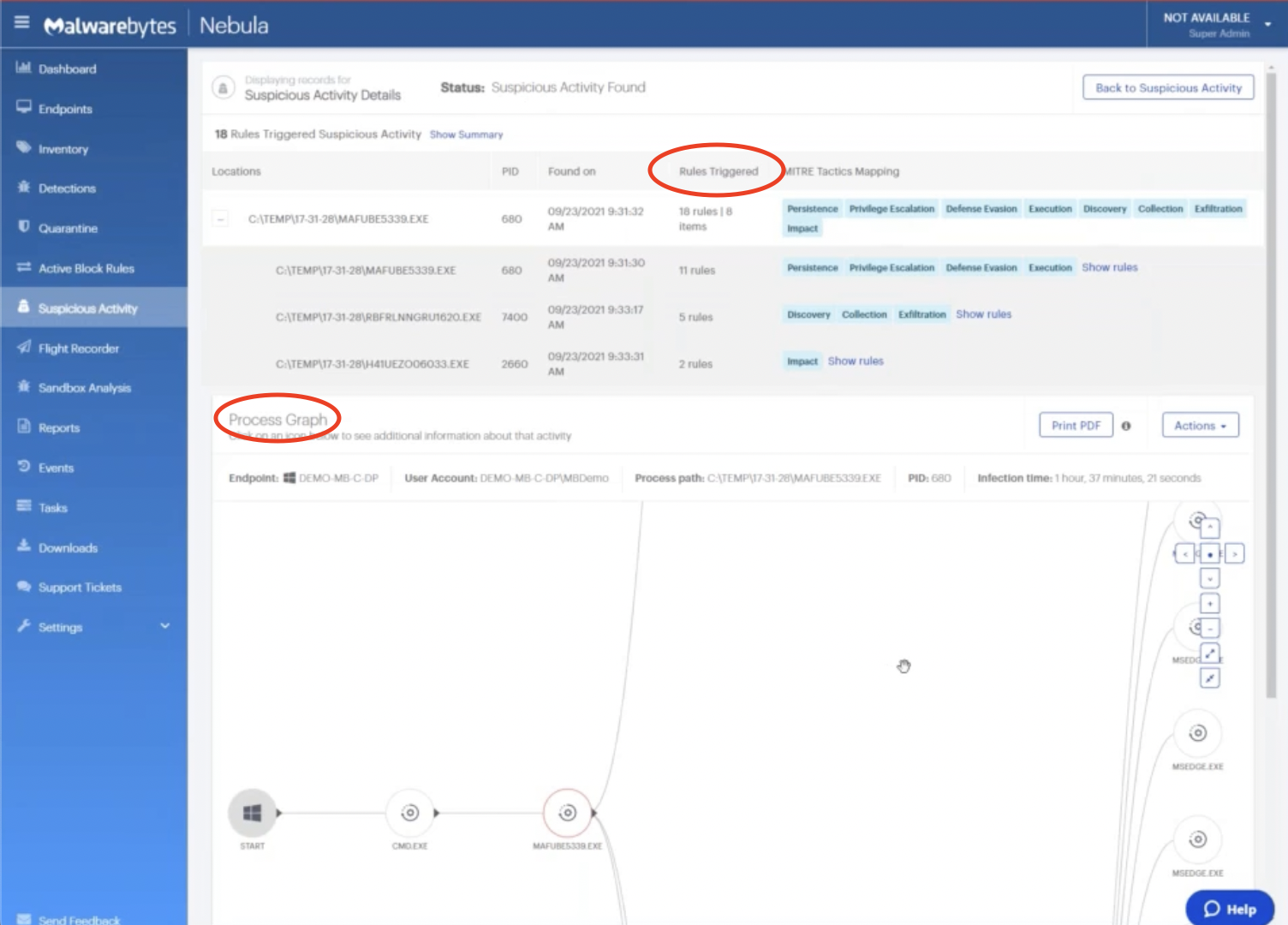
Click into the Suspicious Activity section of the console.
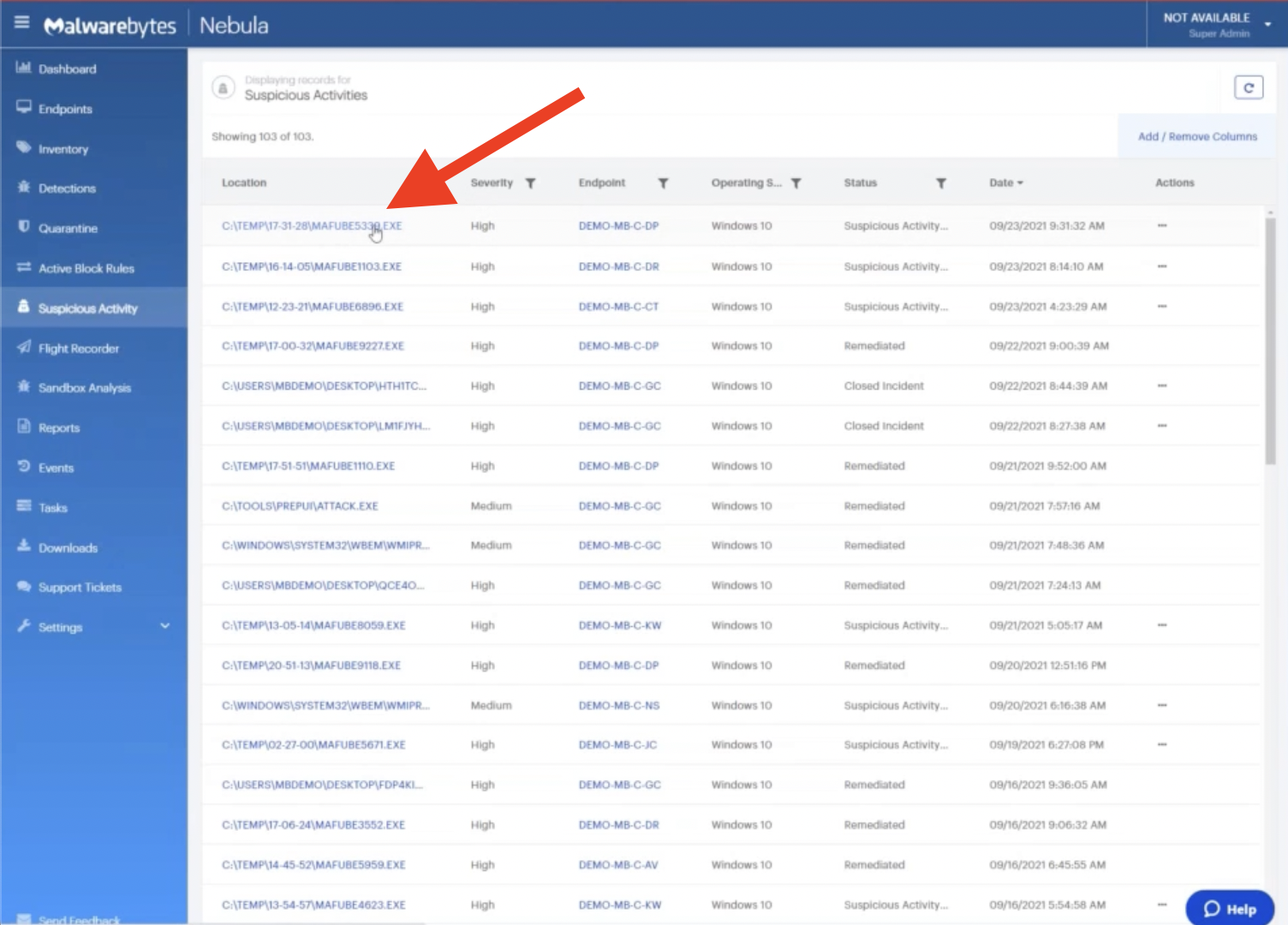
Right at the top, we can see that activity, a process that ran today at 9:31am.
Let’s click on this executable and start diving into how an IT admin or security analyst could use Malwarebytes to help respond to a ransomware situation, as well as effectively contain it.
Up at the top here, we have categorization of rules to help a maybe newer or less savvy security expert understand what’s going on with this process.
At the bottom, we have a detailed process timeline as well.
Let’s expand here by clicking Show rules.
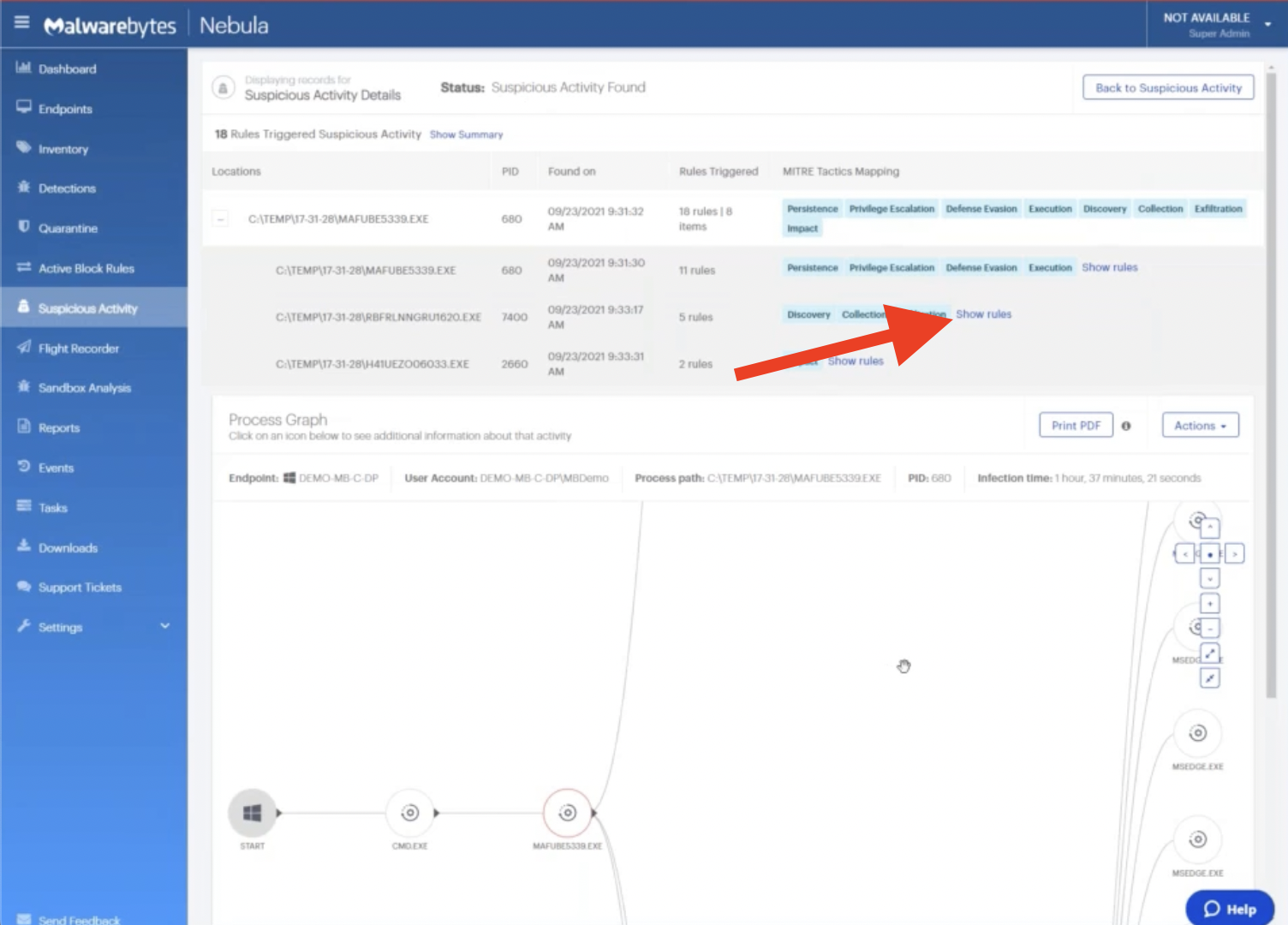
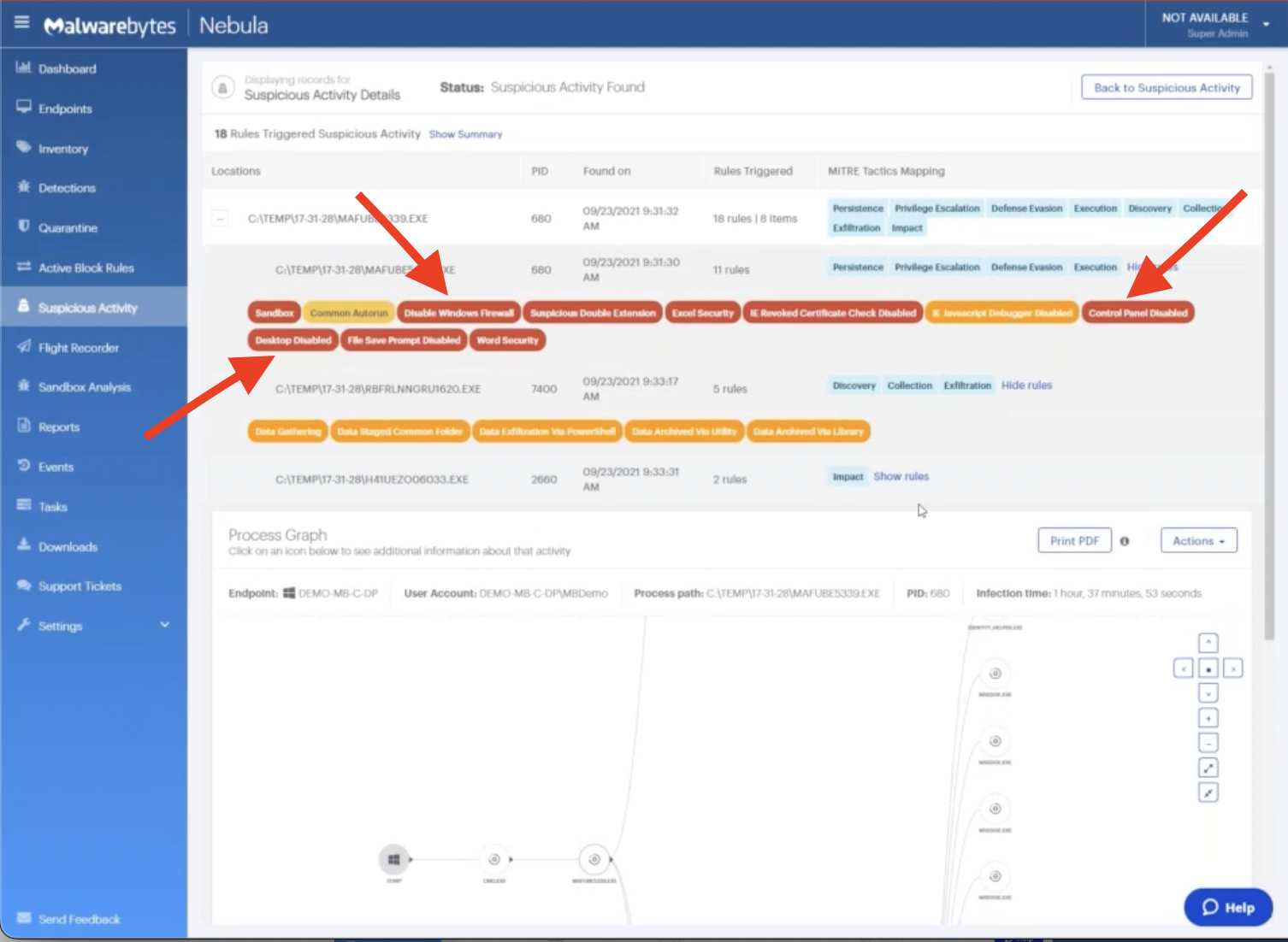
What we see here is the actual categorization of behaviors that Malwarebytes witnessed in this process. Each of these little bubbles has been color coded to help you understand the severity of this issue.
We follow a pretty simple mechanism: Red is high severity, orange is medium severity, yellow is low severity. All of these behaviors are things that Malwarebytes actually witnessed this process doing on our endpoint.
As you can see, there’s a lot of questionable behavior here. Things like disabling Windows Firewall, turning off the control panel, turning off the desktop activity; lots of things that would be concerning to a security expert.
Now, for someone who is not as familiar with some of these behaviors, or maybe there’s a technique that you’re not aware of, you can hover over them for more details.
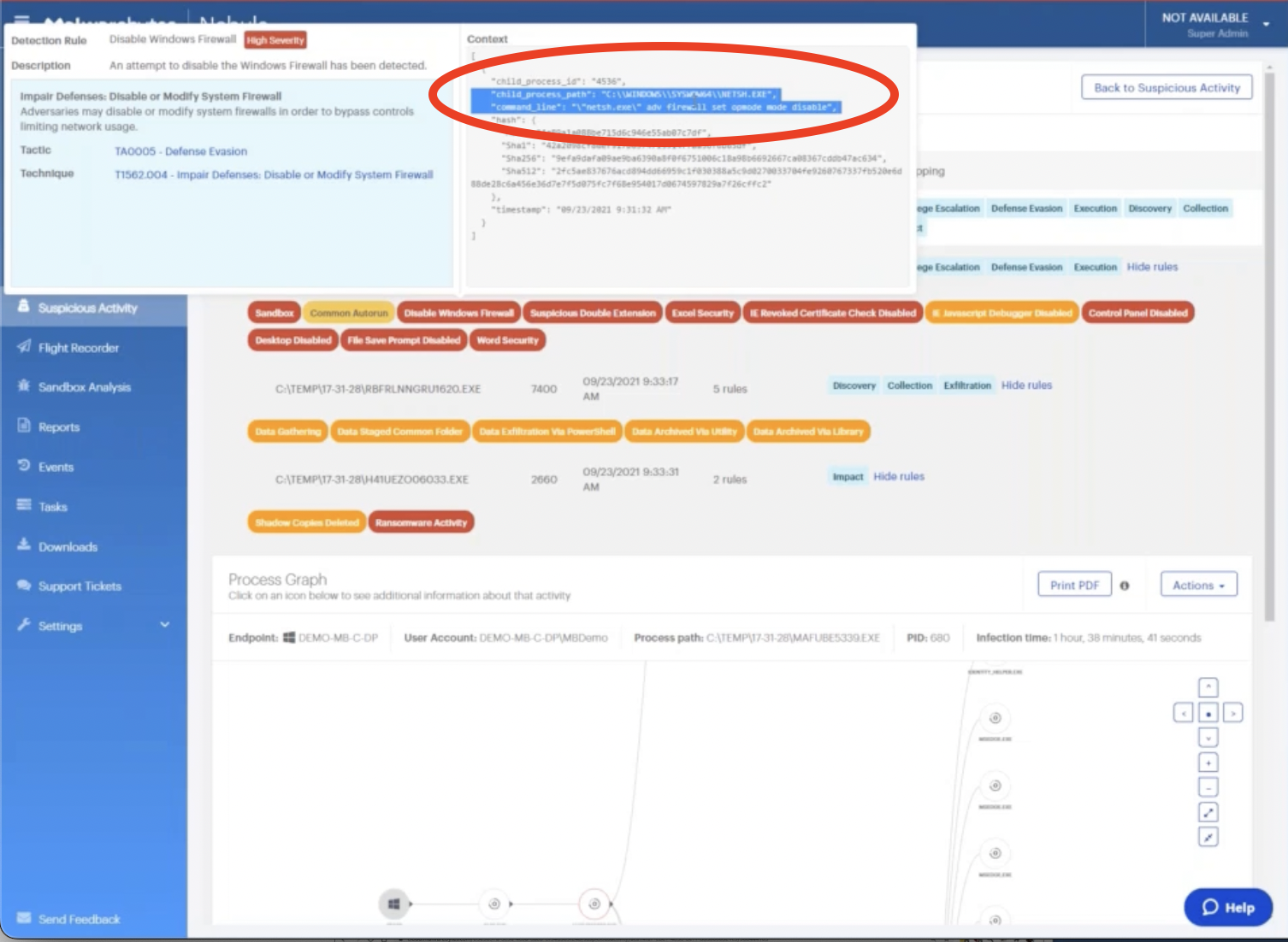
So for example, if we hover over the disable Windows Firewall behavior that we saw, on the left, you’ll see that we’ve been partnering with the MITRE foundation and using its attack framework to give you context and a common set of terms that you can use to identify and understand these tactics.
On the right, we see the command line context for this process in our organization.
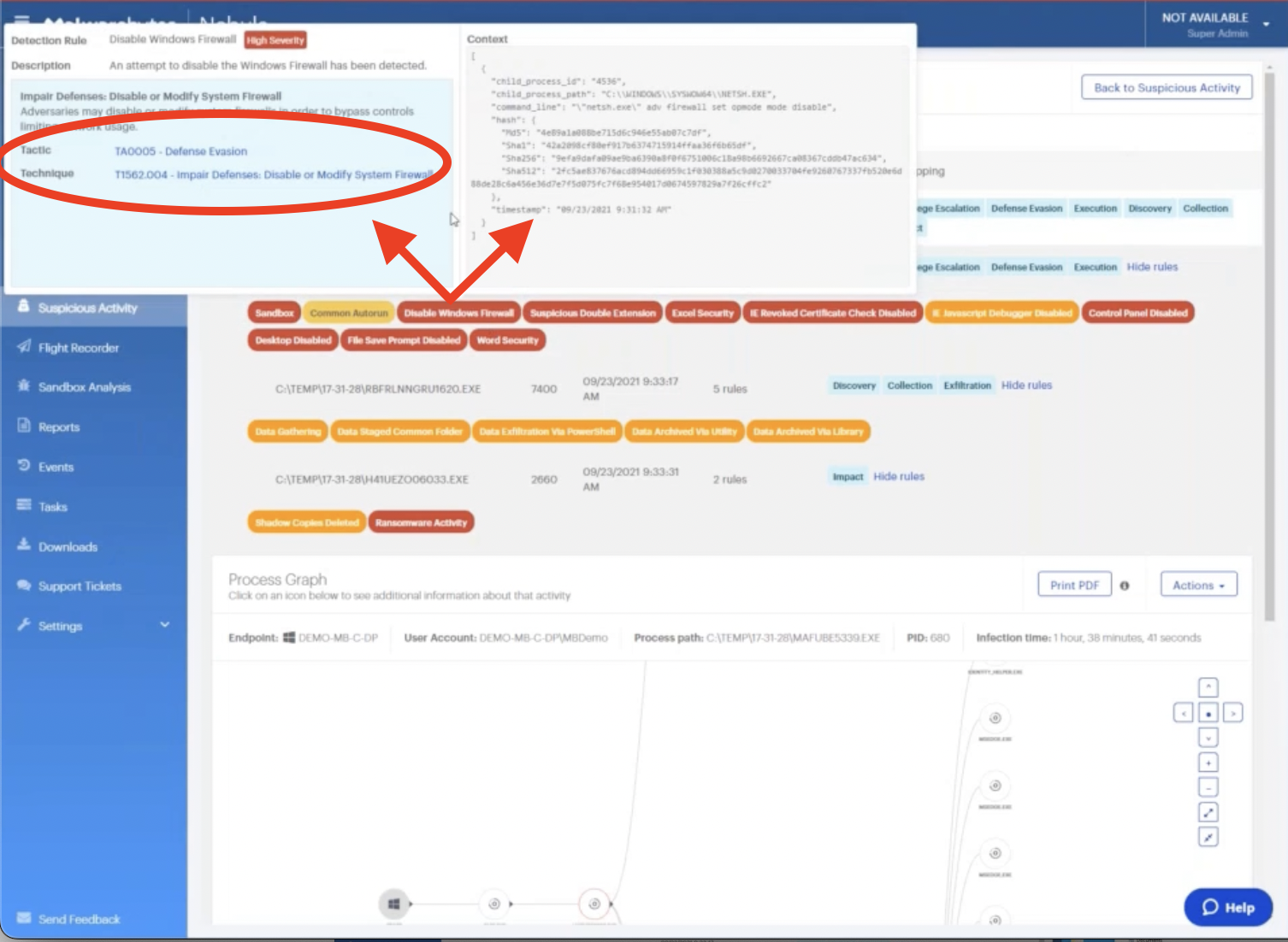
We can see the exact time that it ran and the file hashes, so if we needed to do further investigation, we have those available. And most importantly, we’ve highlighted below the command line actually used to execute this technique on our machine.
So again, in the context of disabling the firewall, this might be something we do in testing or as part of our troubleshooting process.
We can use this context to help understand if this is something that we have done intentionally – or if it’s possibly something that an attacker is doing to compromise our environment.
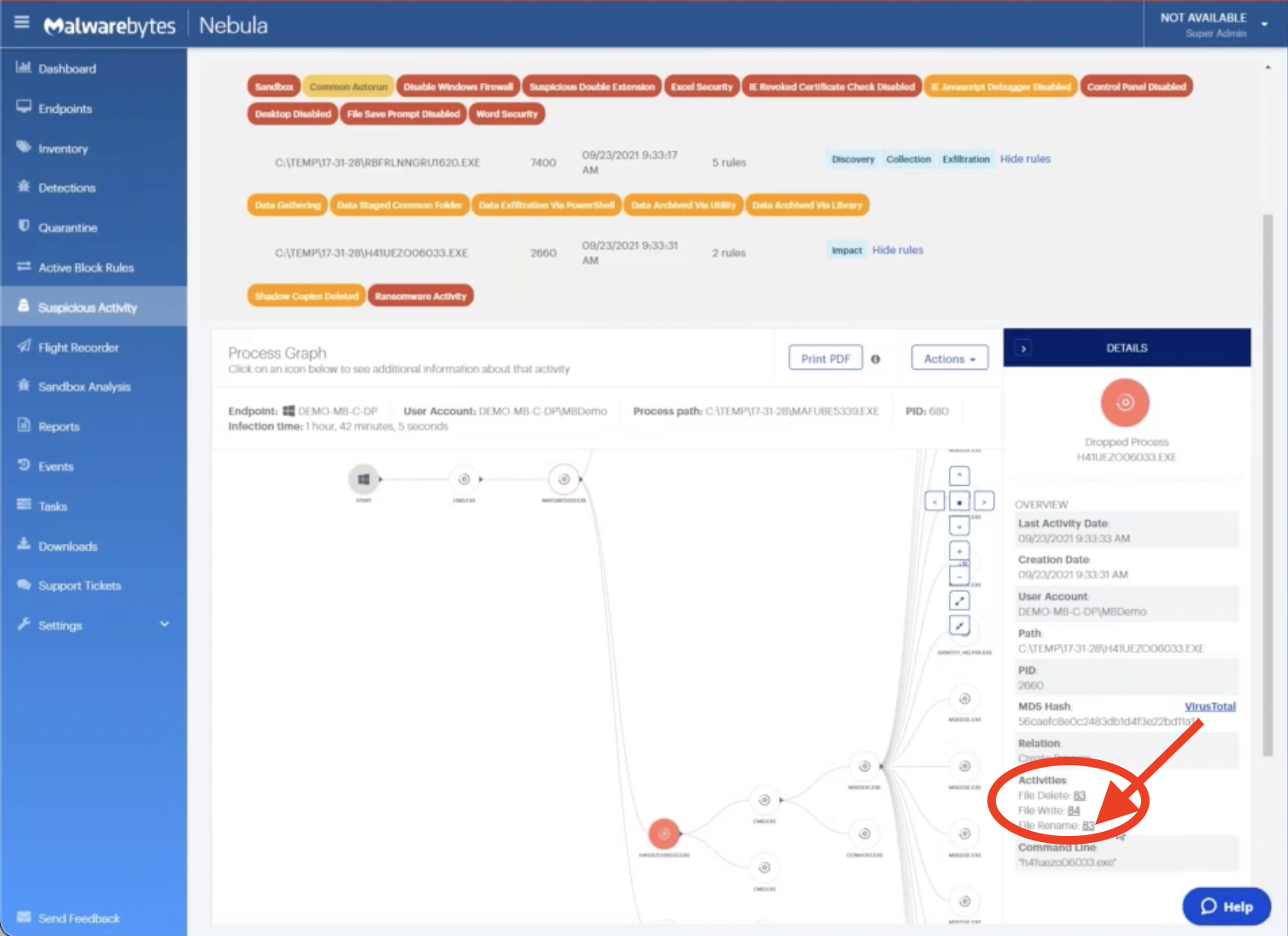
Let’s navigate now down to the bottom half, where we can see the actual specific details of this process.
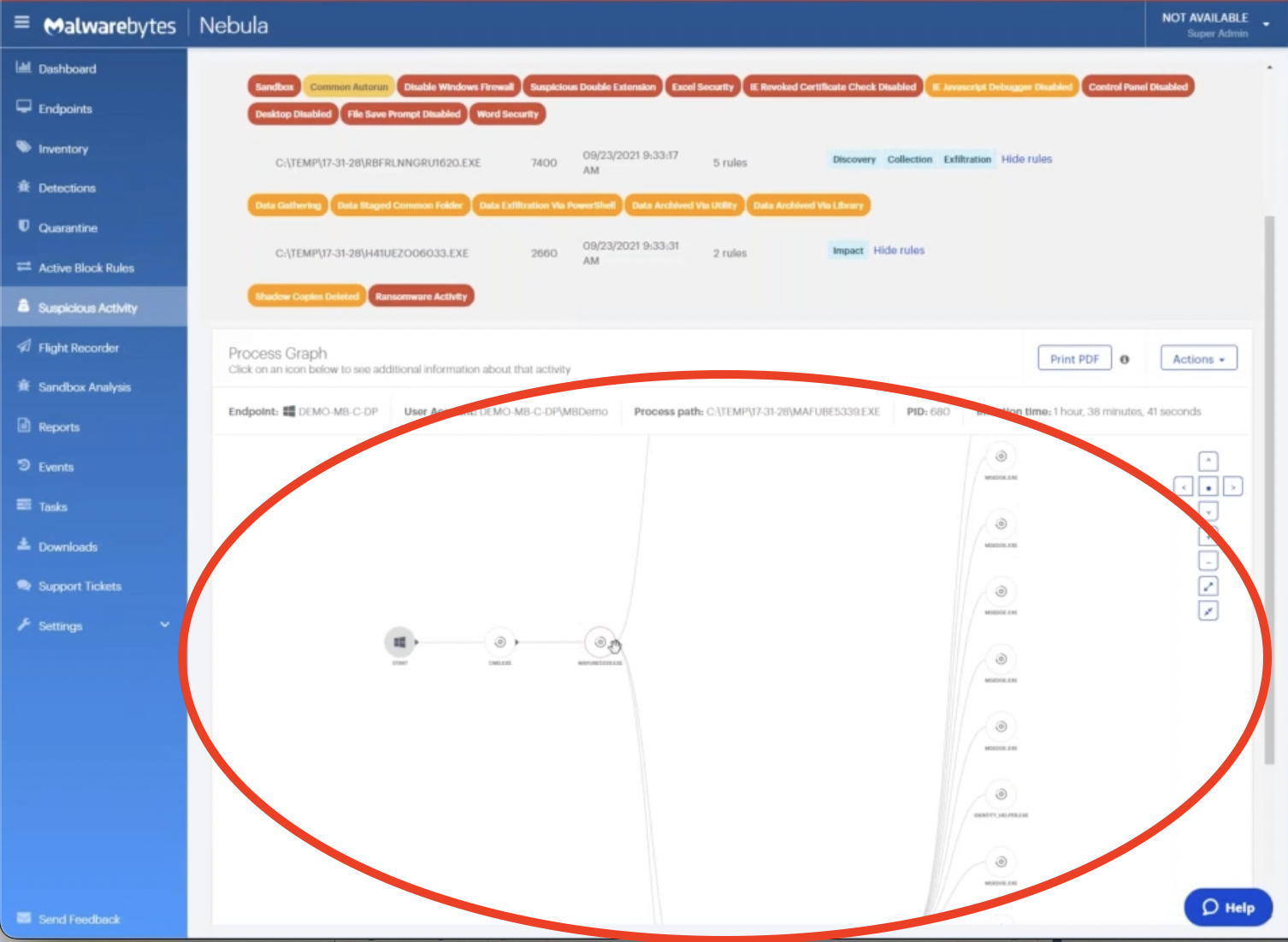
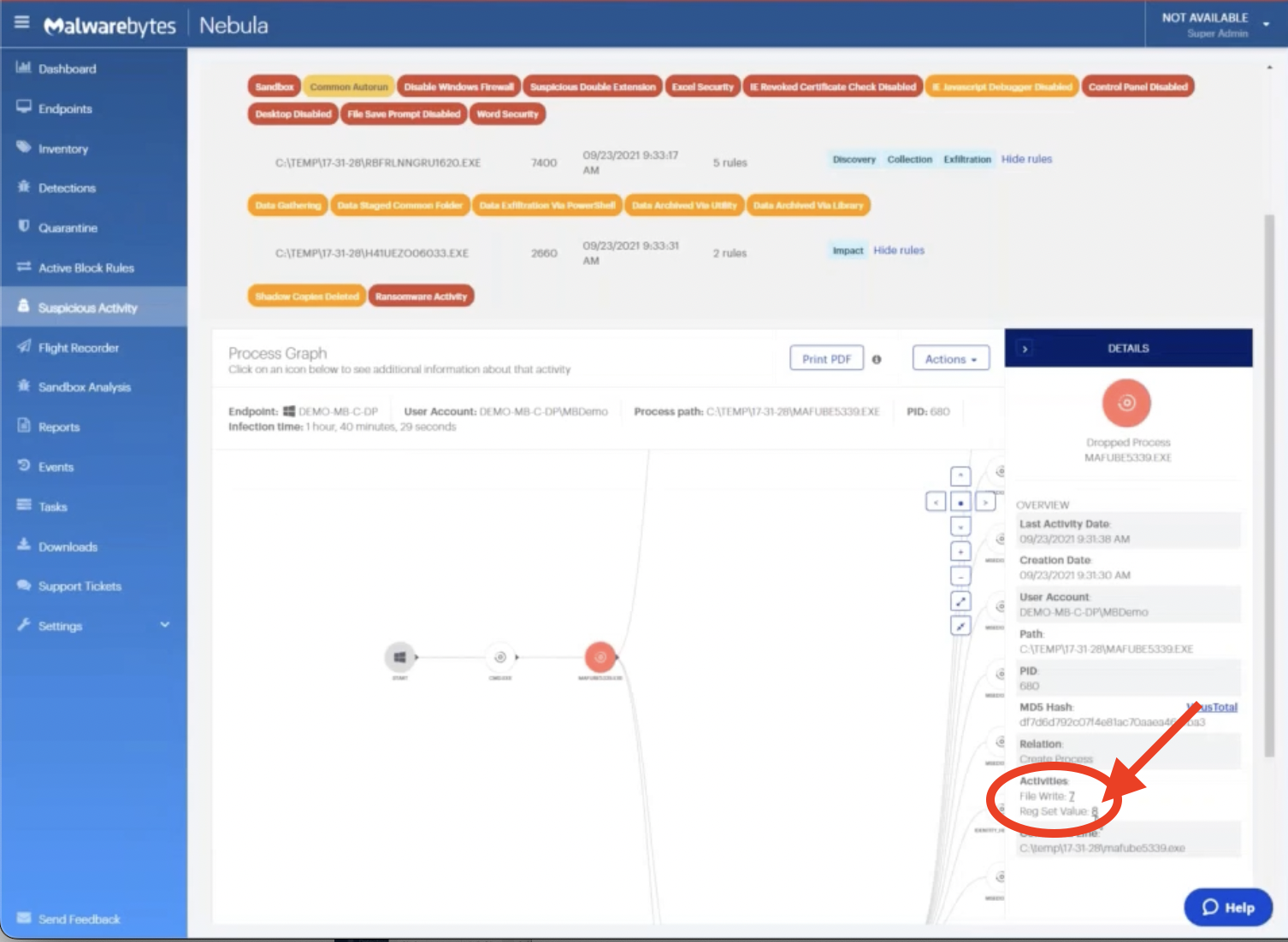
Clicking into any of these nodes, we get a lot of rich context information about what this process did.
As a security analyst or an IT admin, the first question you typically ask when an incident occurs is: What happened? Do we know if it’s malicious? What is the actual extent of the potential damages? And so on.
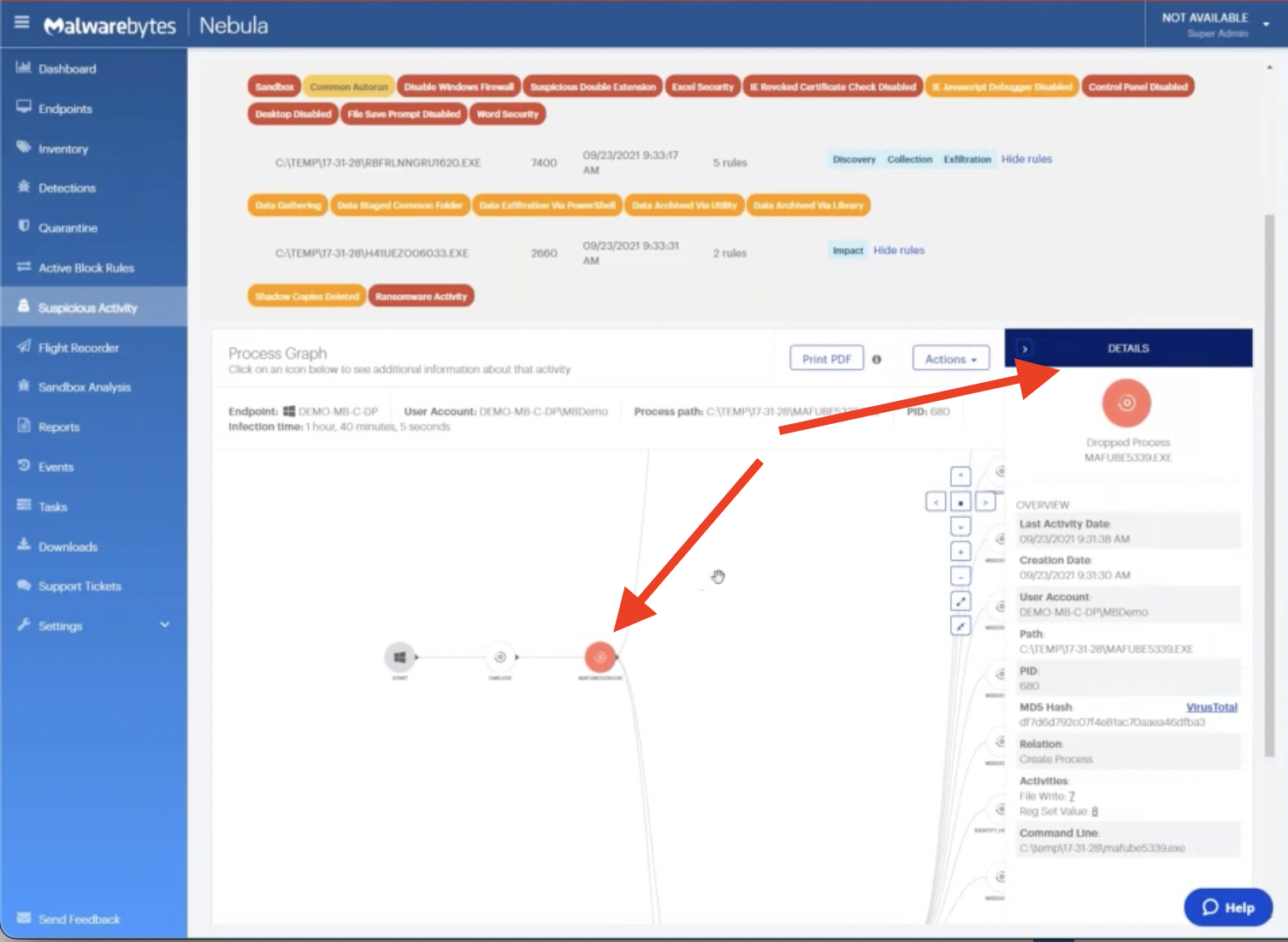
So here, we can navigate through to see everything that’s happened on this machine.
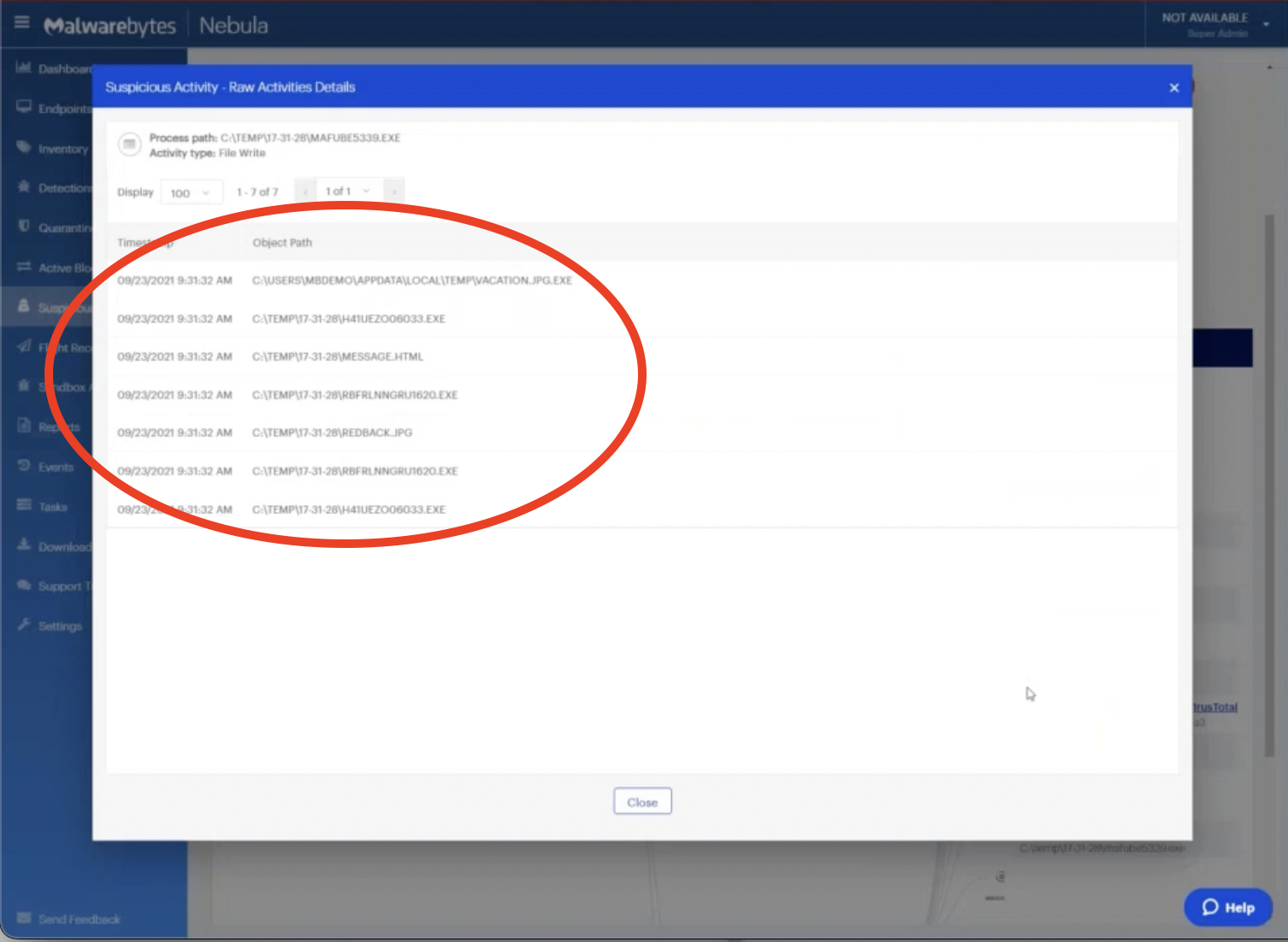
For example, if we click on File Write, we can see every artifact or file left behind by this process.
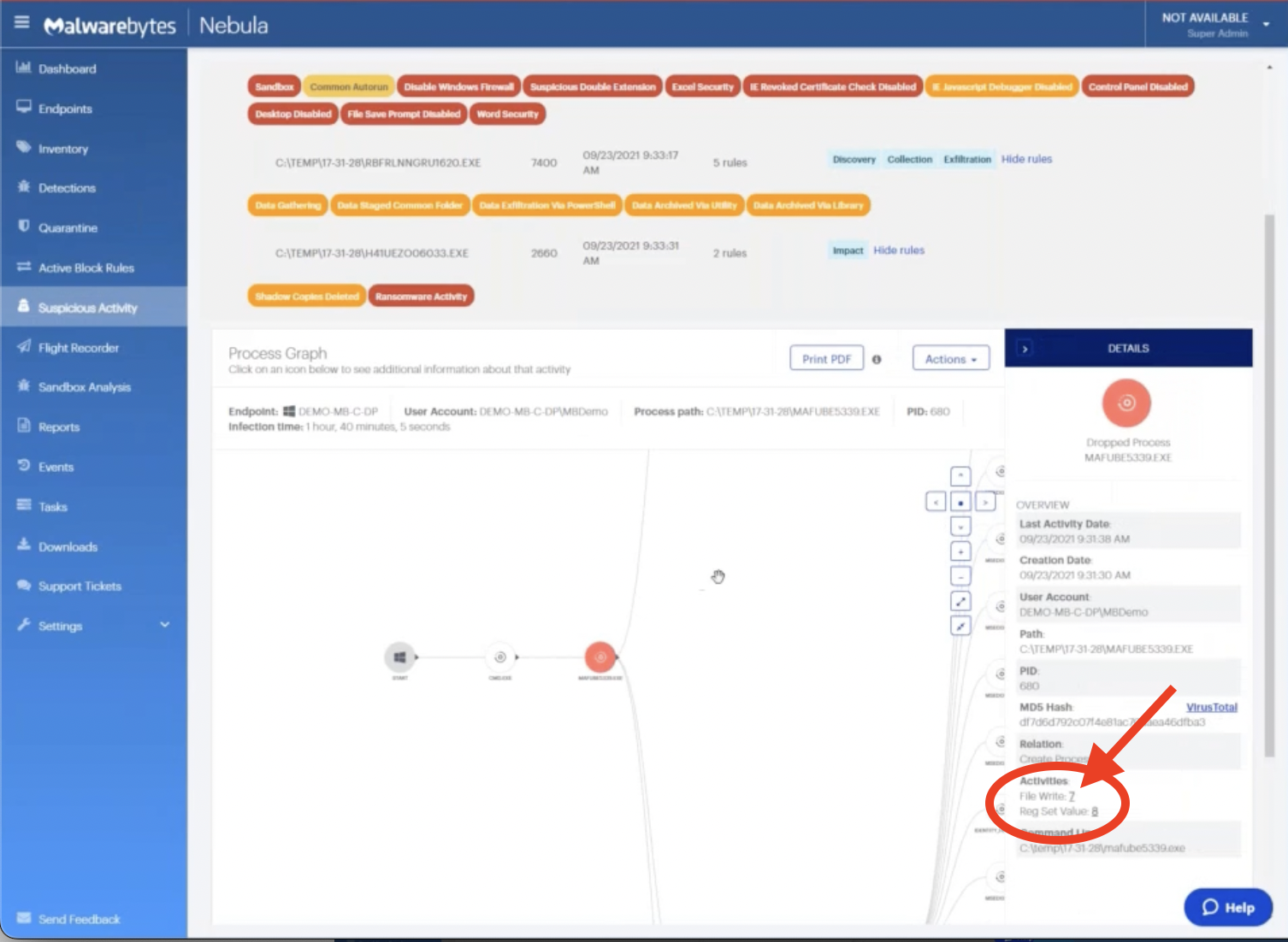
Similarly, we can click on Reg values to see what registry changes were made on that system.

Part 3: Isolating the endpoint infected with ransomware
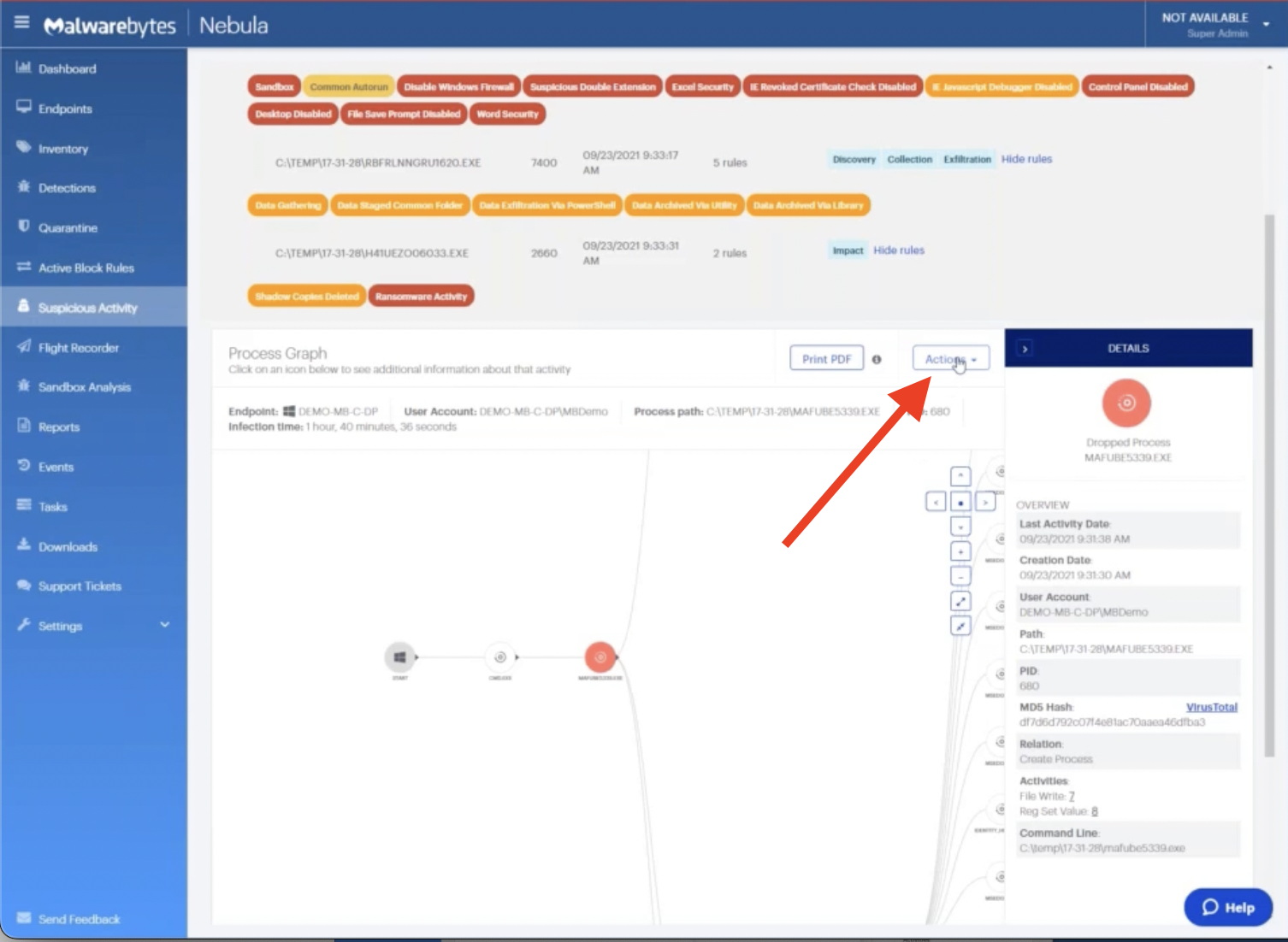
Now, as we’re continuing our investigation, we’re looking at this and deciding it looks pretty suspicious – it’s probably unwanted or a potentially damaging activity. So as a safeguard, we’re going to use the first response mechanism in Malwarebytes, which is our isolation capability.
From the Actions menu, let’s choose to isolate this machine with Isolate Endpoint.
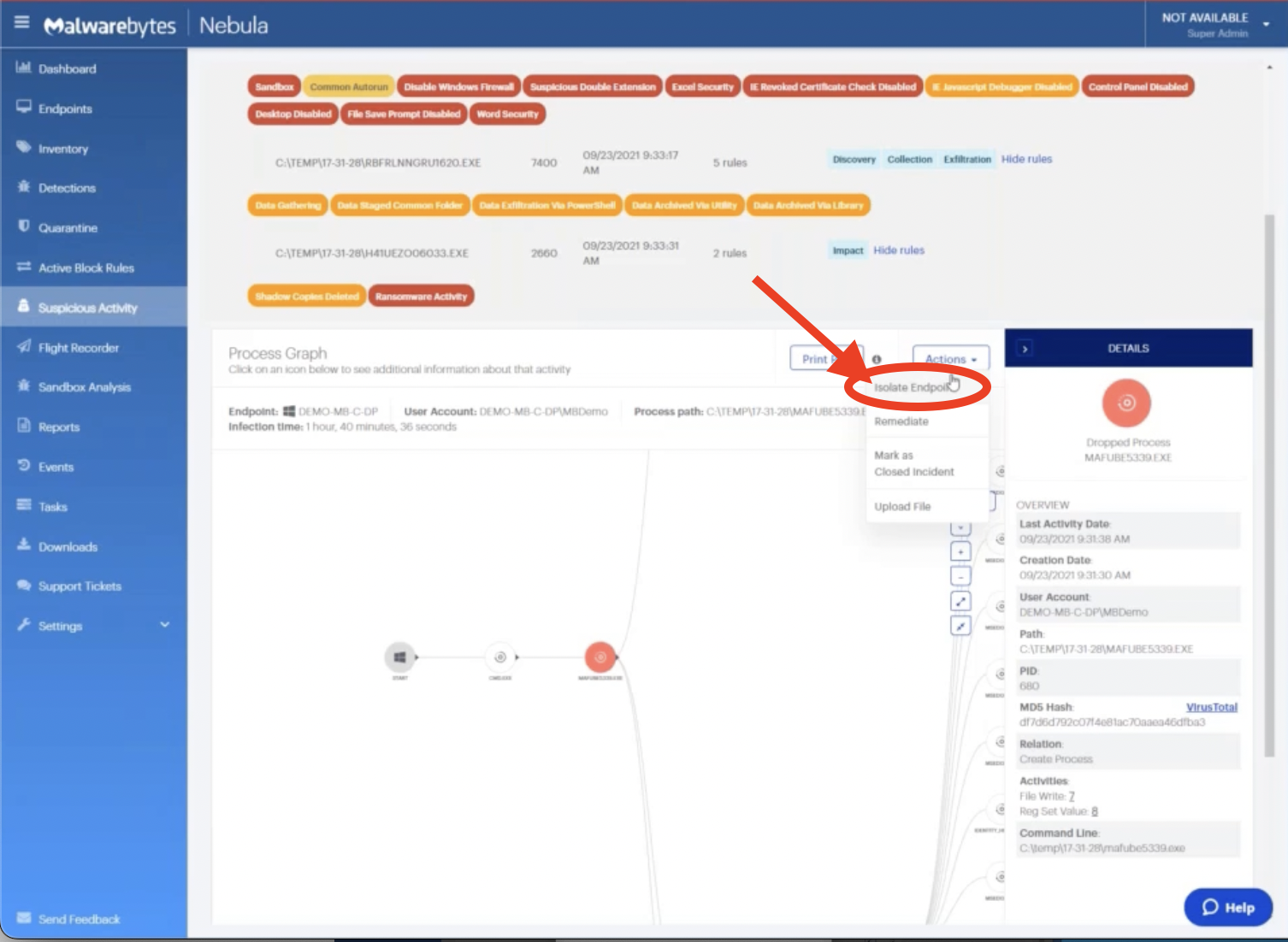
We have three layers of isolation that we can provide: network isolation, process isolation, and desktopisolation.
The network and process isolations are intended to give us the ability to quarantine that machine and prevent it from doing anything that is not authorized by Malwarebytes.
What this means is, we can still use our Malwarebytes console to trigger scans to perform other tasks and to review data, but the machine otherwise can’t communicate or run anything else.
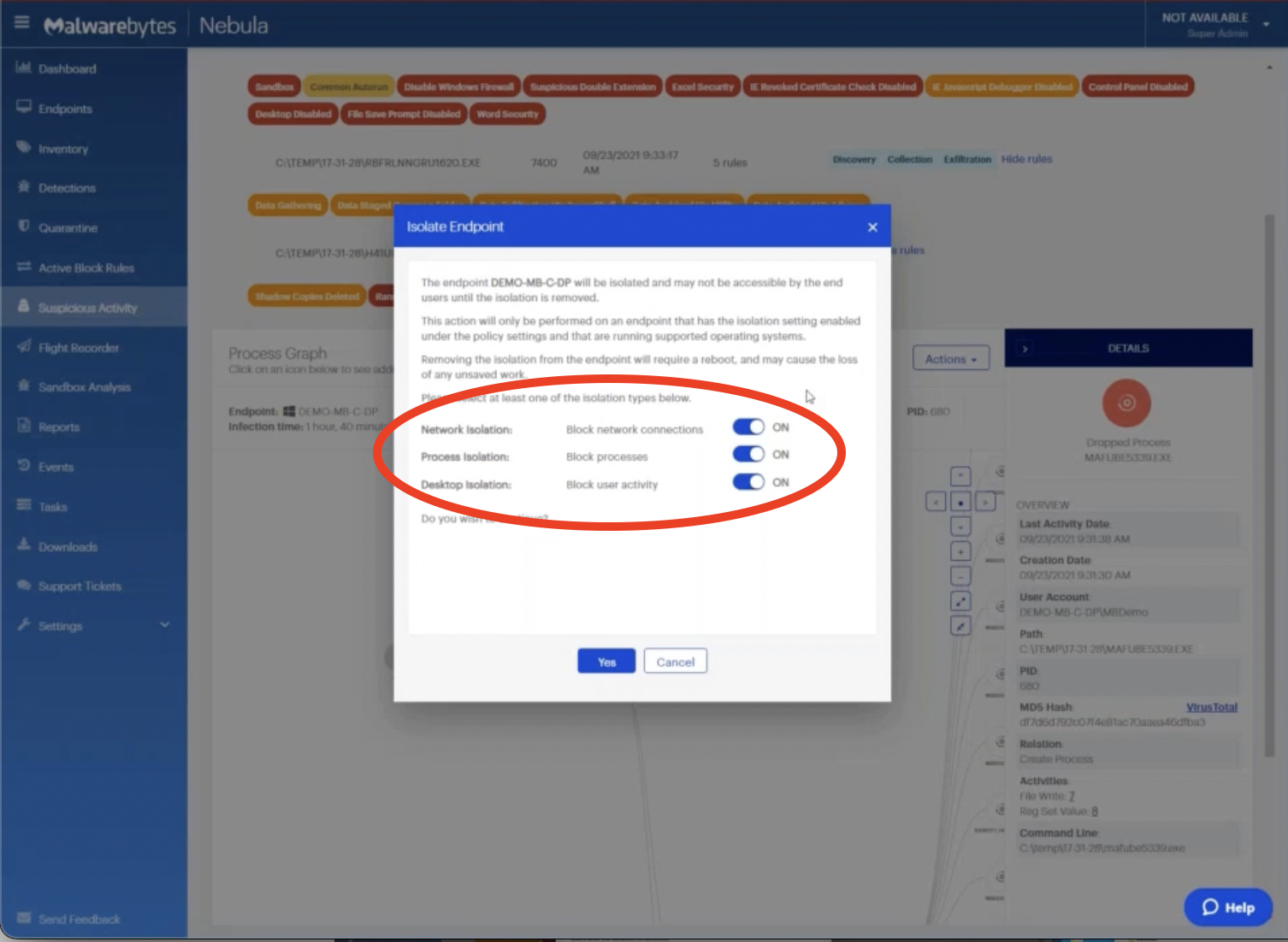
For this demonstration, we’re just going to use network isolation so that we can simulate preventing this machine from spreading an infection laterally in the environment.
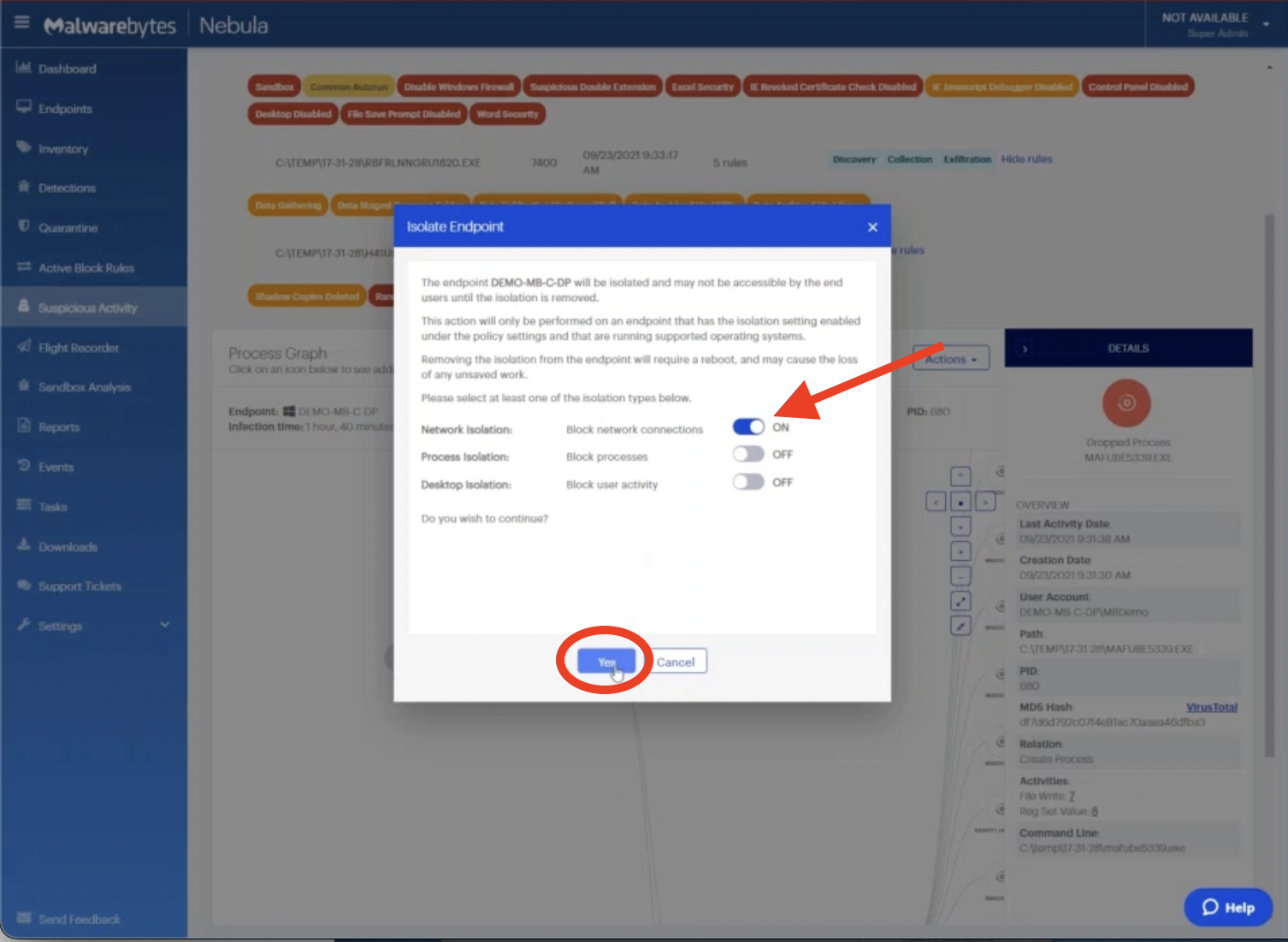
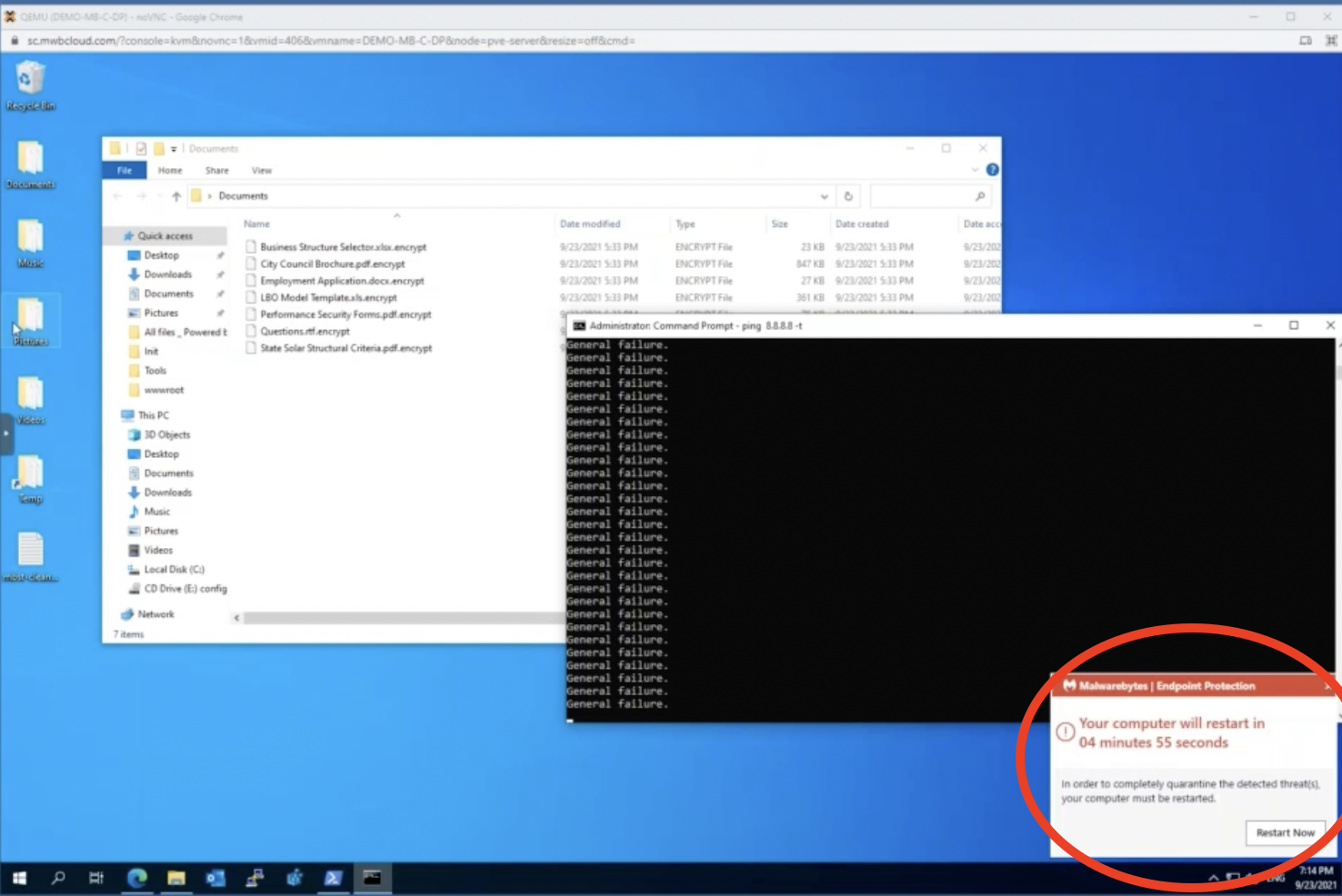
Notice as we send that isolation command, the ping to Google immediately begins to fail – showing that that machine can no longer communicate to the internet.
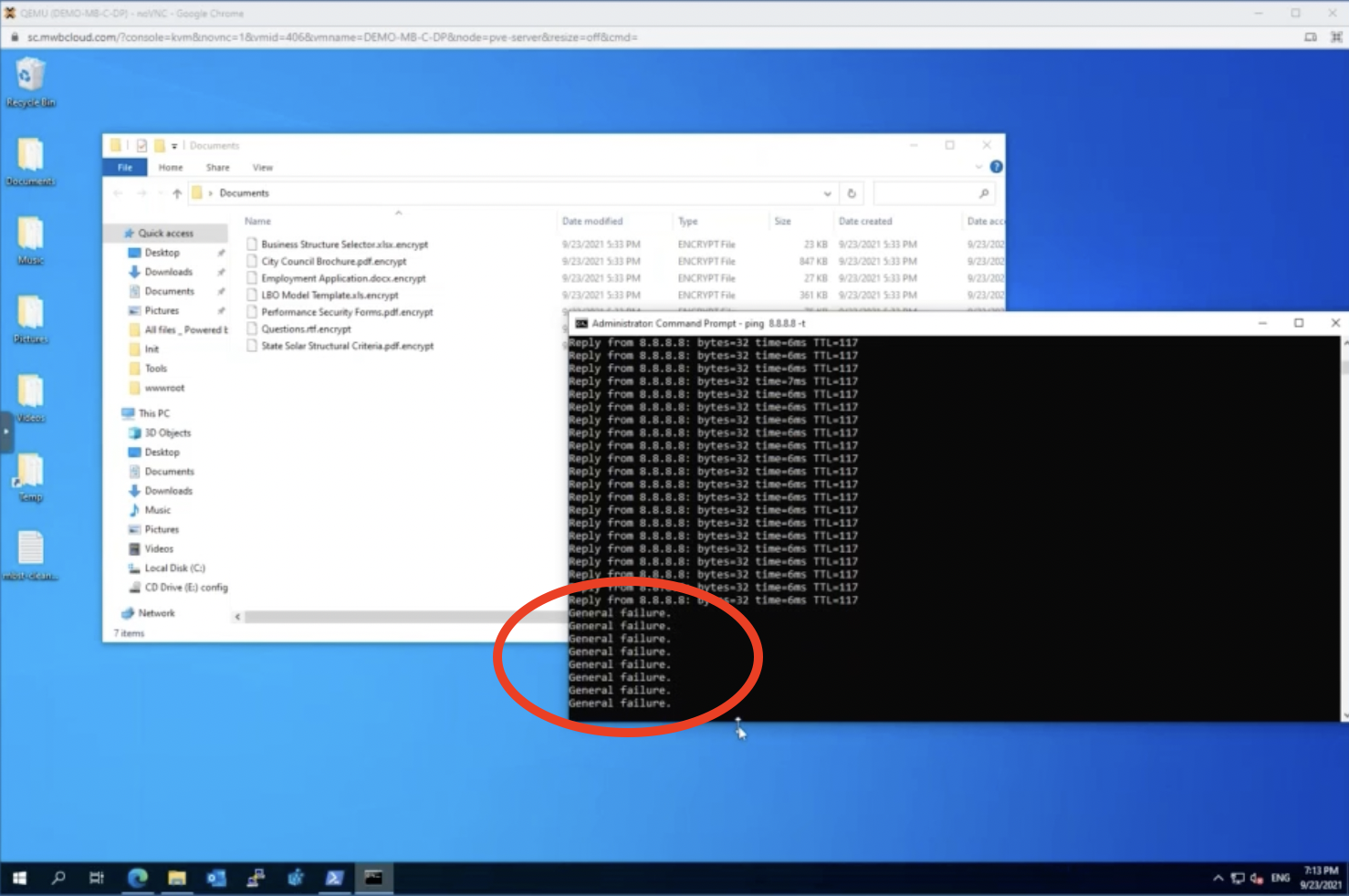
Now that we’ve isolated this device, let’s continue our investigation further.
Part 4: Remediating the ransomware
Below, we see a process here with a large amount of file activity, namely file renames.
Let’s click into this. This is where Malwarebytes witnessed the ransomware attack actually occurring—so we see those files changing to not their normal versions, but to the .encrypted versions of the same file.
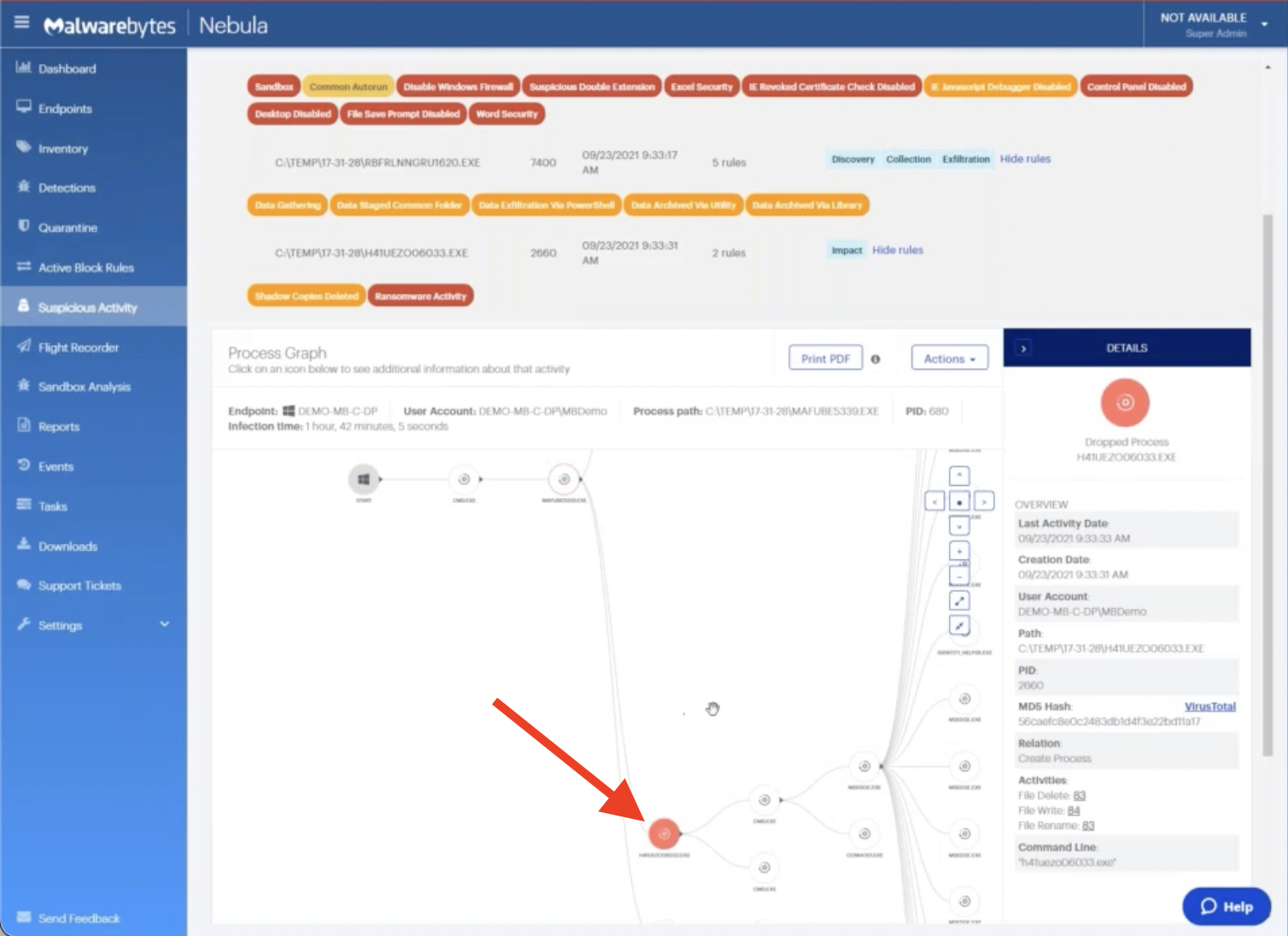
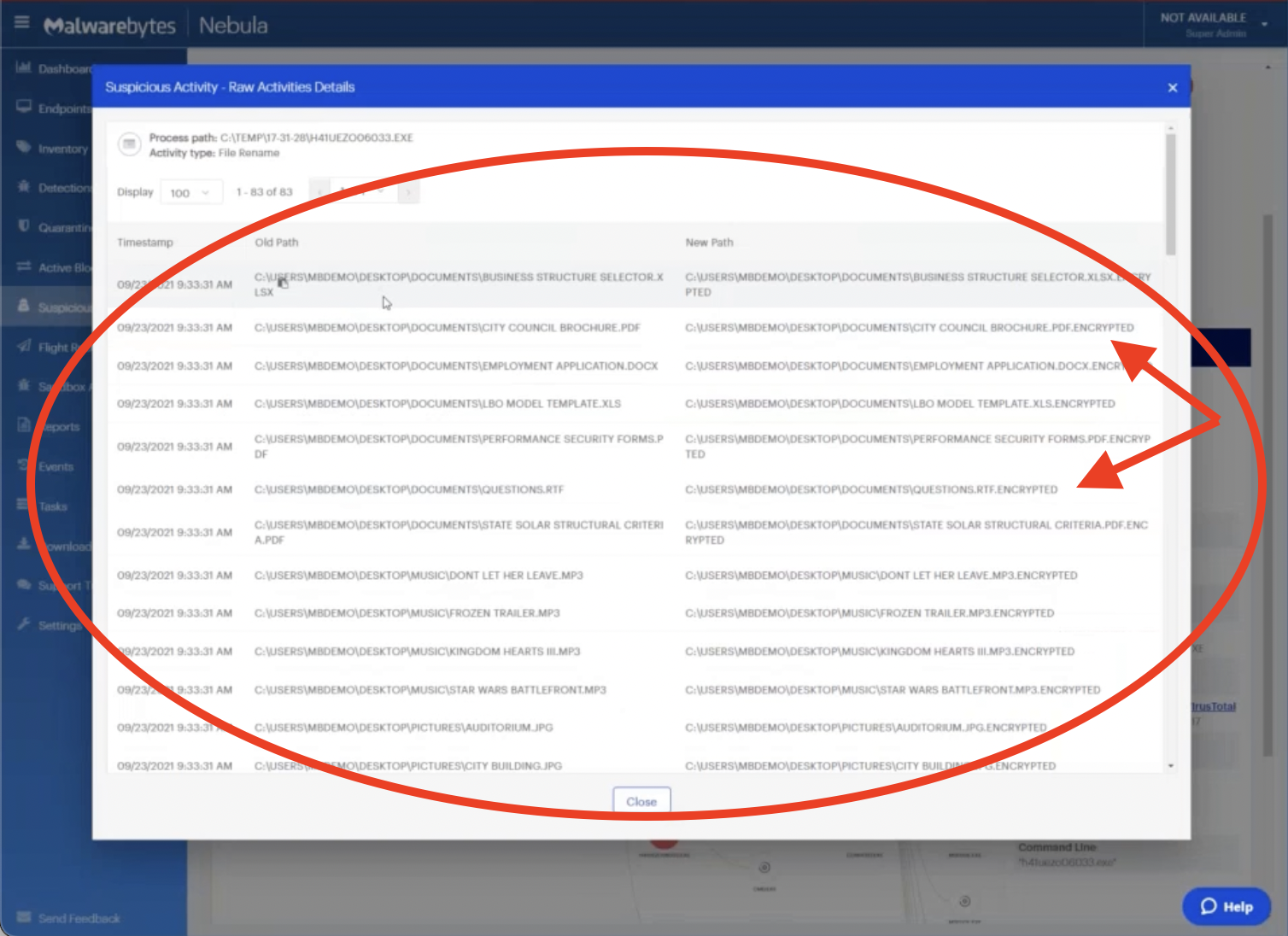
What makes Malwarebytes unique in our EDR capabilities is when we see behavior like this (something that could compromise your files due to encryption or deletion or other types of malicious activity) we’ve actually created backups of all of the files that were targeted by this process stored locally on this machine.
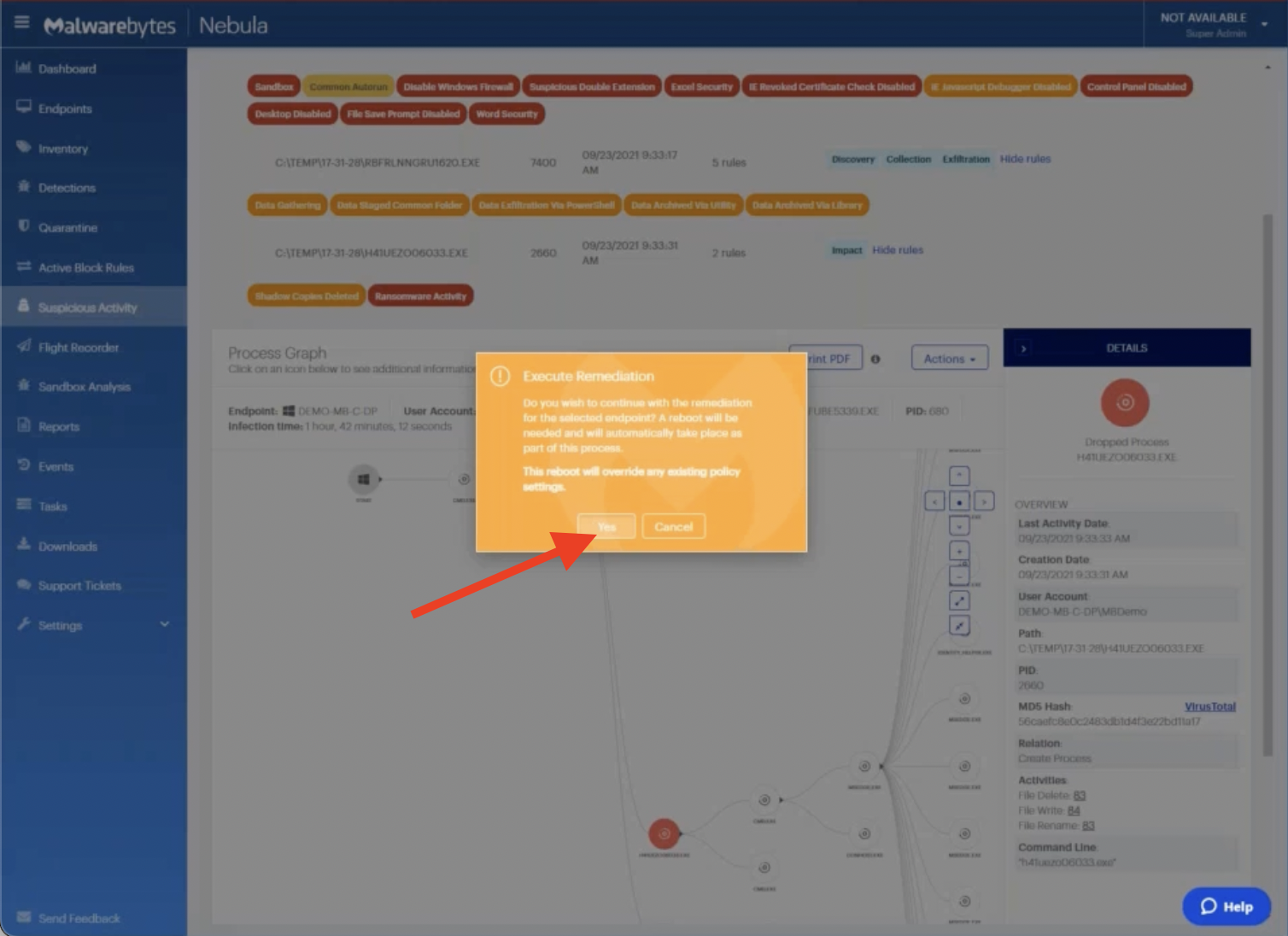
Now that we’ve identified that this is unwanted and malicious behavior, what we’re going to do is initiate a rollback action.
Effectively, we’re telling Malwarebytes that we did not want this activity: this is something that happened on our machine that we never authorized and that we did not want. So when we go to Actions, and then Remediate, this will send a customized script to this endpoint and it will look at all of the behavior we witnessed in this process graph here.
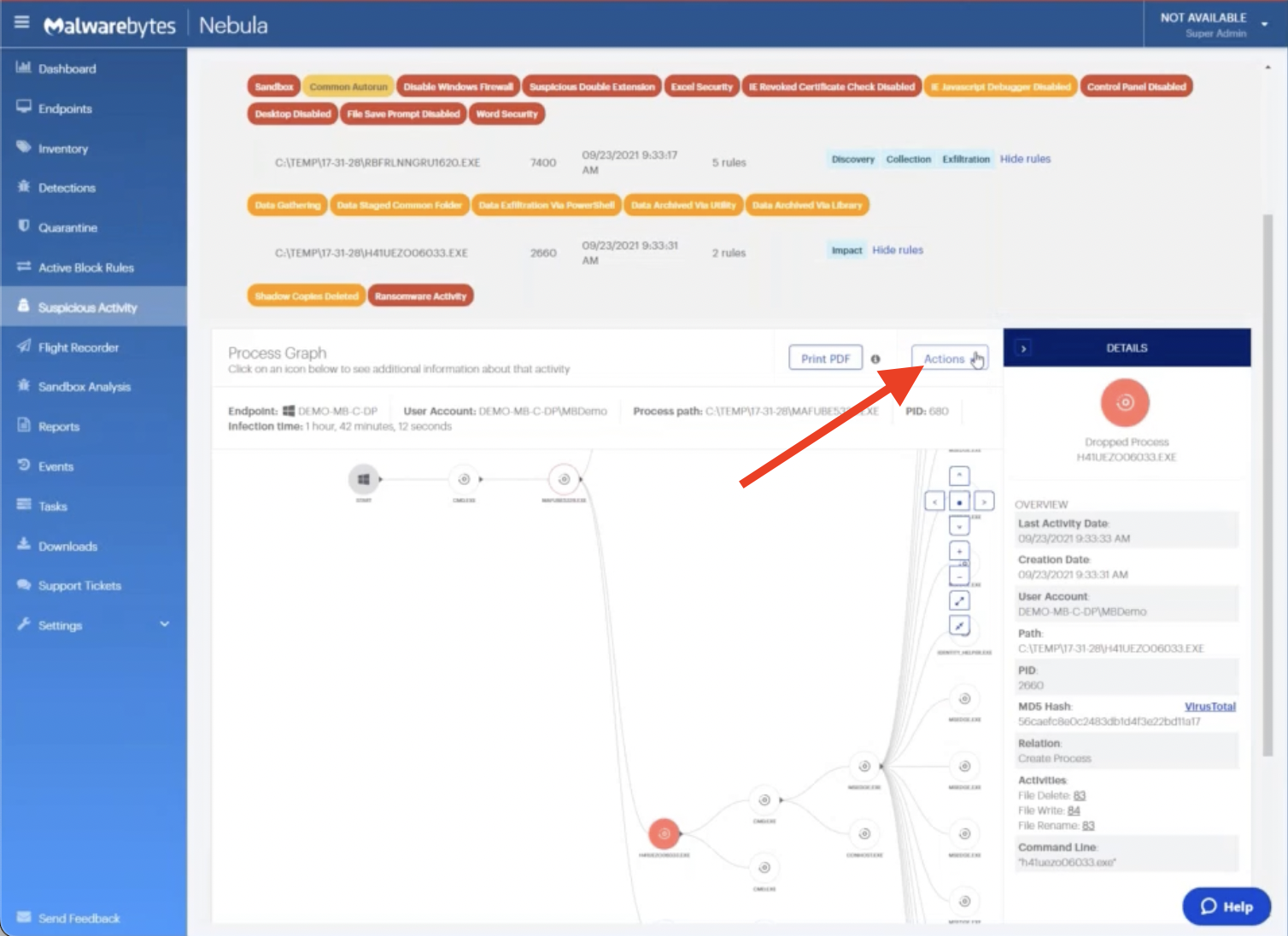
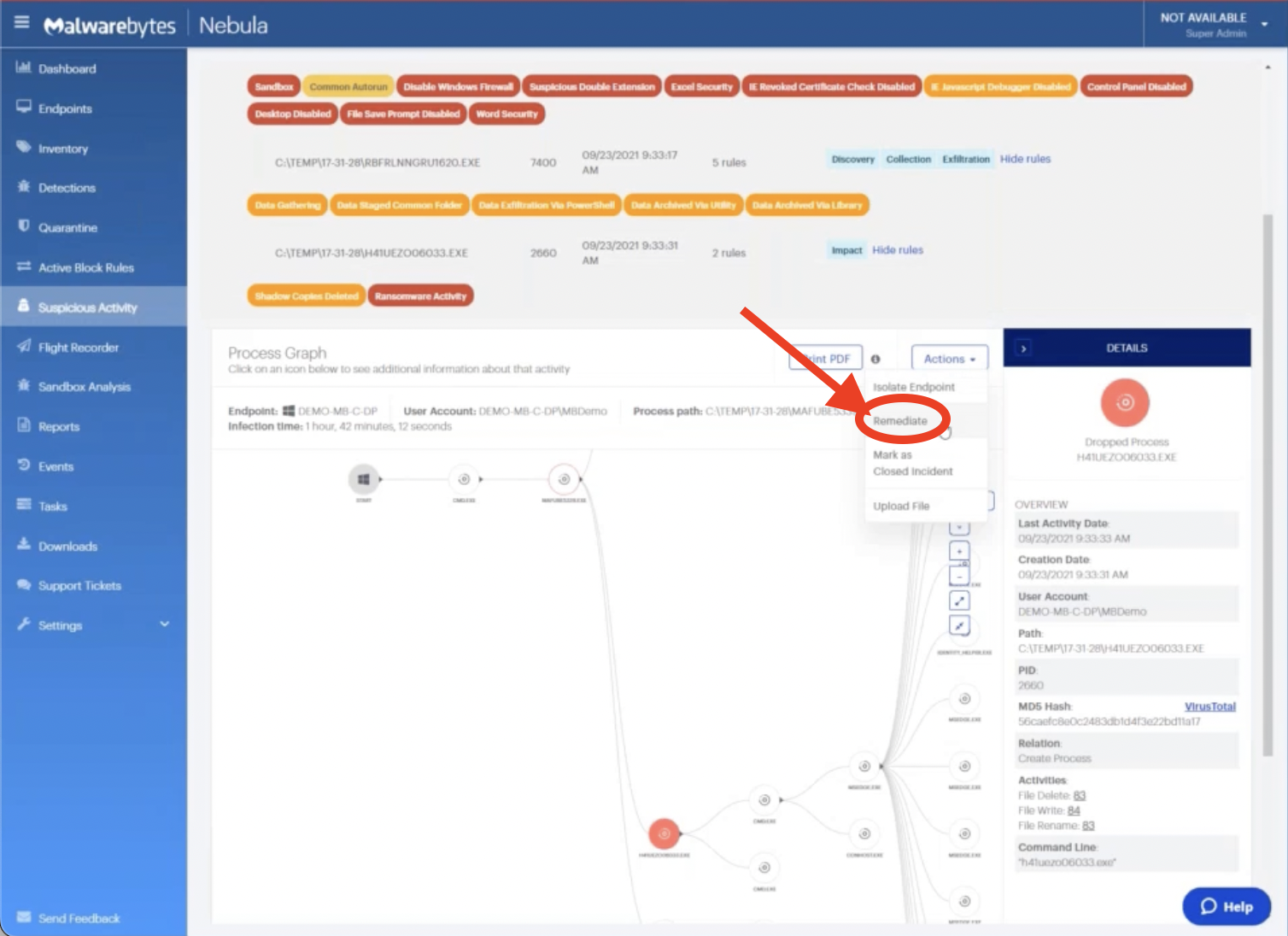
This will create a customized remediation plan for this machine, where it will iterate backwards through the behavior, resolving any potential issues that might have arisen.
One of the things that it’s going to do in this process is look for those backup versions of the files we created and restore those to the end user.
We can see on the right that our virtual machine received the command and it needs to restart to finish the process. Let’s restart it now so that we can see it carry out the backup!
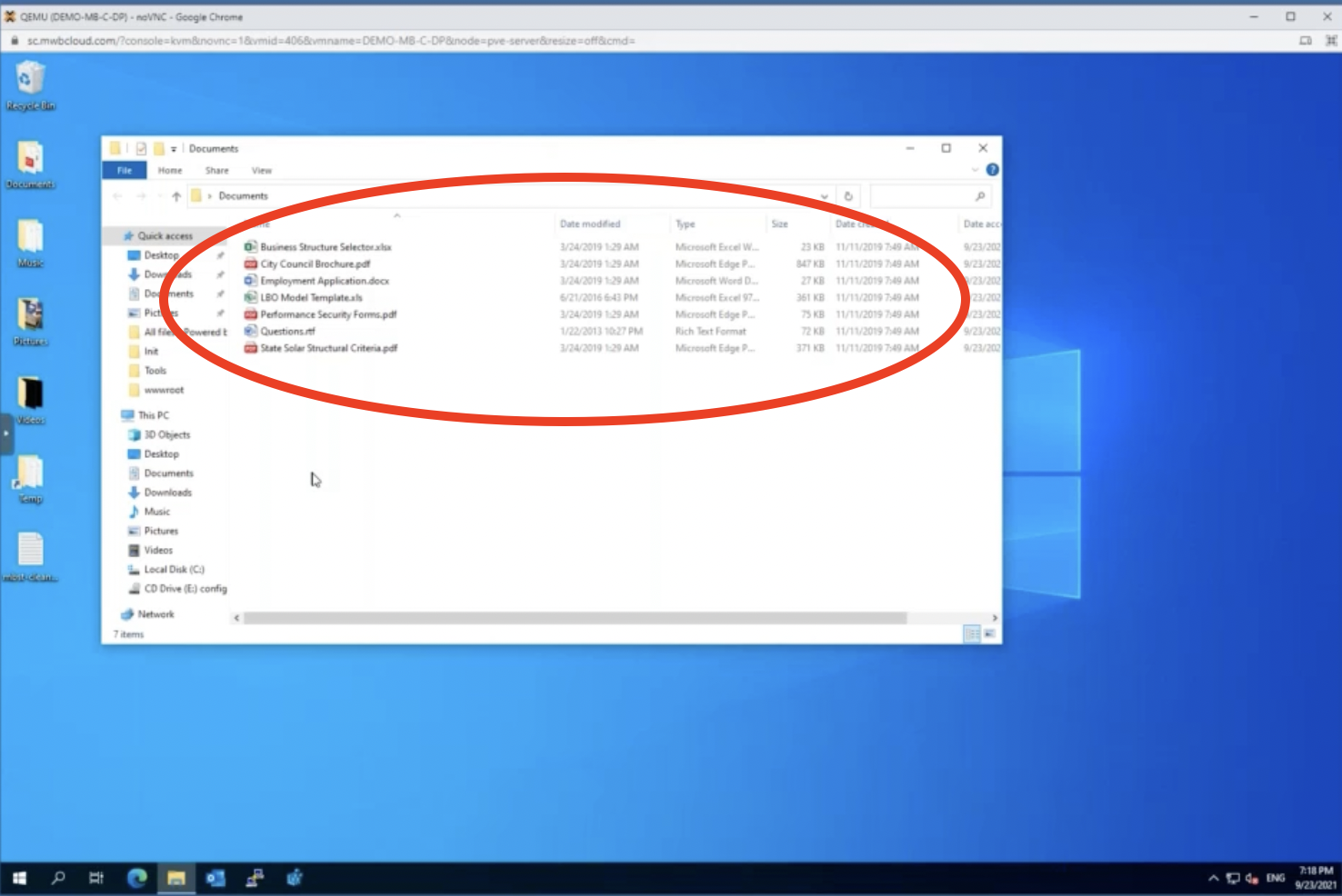
After the machine reboots, we can open these folders and actually see that all of our files have been returned to their original version.
Accelerate and simplify your ransomware defense with Malwarebytes EDR
In this post, we seamlessly looked at the activity that ransomware exhibited, found a recovery plan for it, then implemented that plan.
In short, this is not a tool where you’re going to have to devise a customer mediation plan, where you’re going to have to iterate through hundreds of IOCs or complex readouts with an EDR solution to build a manual recovery solution – you simply need to tell Malwarebytes to resolve the issue.
When it comes to ransomware mitigation, we’ll take the wheel from you – freeing up a lot of time in your day as an admin or an analyst. Read about how a leading automotive manufacturer and distributor used Malwarebytes EDR to simplify their ransomware remediation.
Malwarebytes EDR prevents, detects, and responds to ransomware, malware, trojans, rootkits, backdoors, viruses, brute force attacks, and “zero-day” unknown threats so you can avoid business disruption and financial loss.
Complete cyberthreat protection starts here
Looking for more demos of Malwarebytes EDR? Watch the webinar!











