Ransomware review: February 2023
Threat Intelligence Team
Threat Intelligence Team
This article is based on research by Marcelo Rivero, Malwarebytes’ ransomware specialist, who builds a monthly picture of ransomware activity by monitoring the information published by ransomware gangs on their Dark Web leak sites. This information represents victims who were successfully attacked but opted not to pay a ransom.
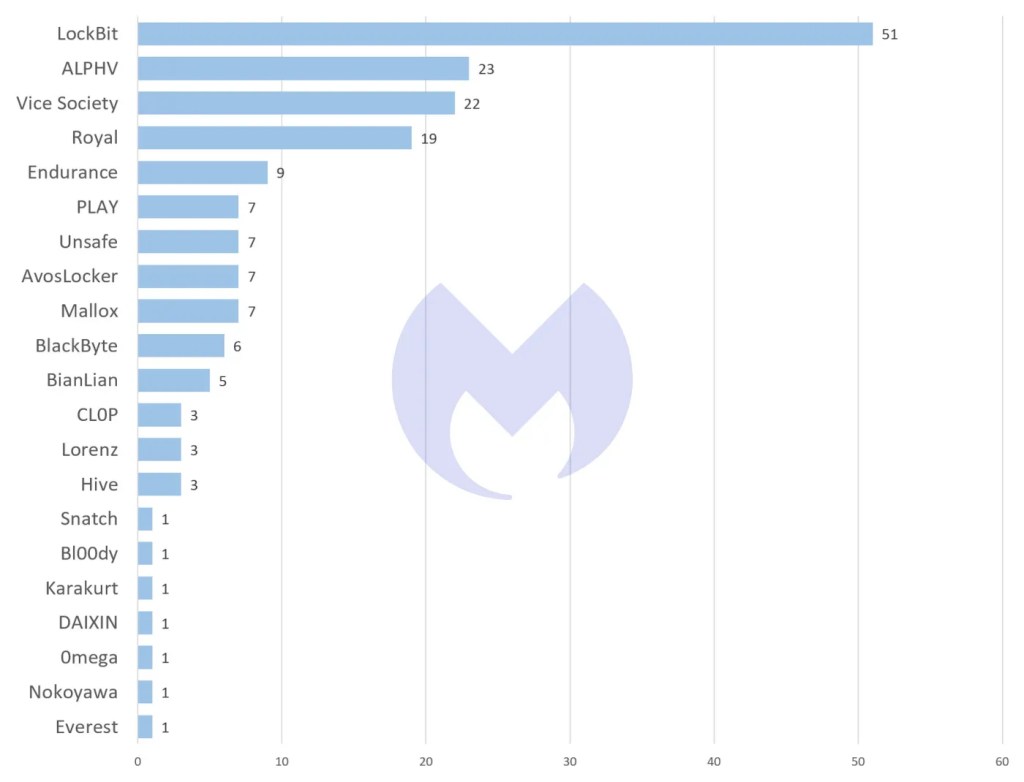
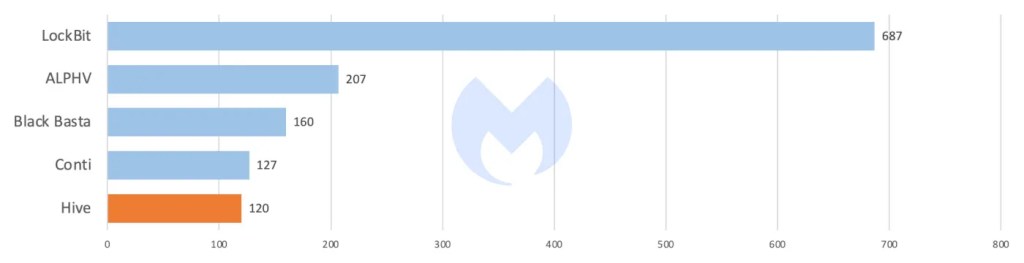
LockBit started off the new year just as it ended the last one, topping the charts once again as January’s most prolific ransomware-as-a-service (RaaS). The Hive ransomware group meanwhile found itself shut down by the FBI.
It’s not all old news for Lockbit, however: Last month the gang was seen using a new Conti-based encryptor named ‘LockBit Green’. This latest ransomware version, the third from the gang after LockBit Red and LockBit Black, shares 89% of its code with Conti v3 ransomware and has already been used to attack at least five victims.
Considering the success of LockBit Black, it’s unusual (and unclear) why the gang is offering a new variant. One possible explanation is that it wants to attract affiliates who are more comfortable using Conti-based ransomware, such as ex-Conti members. Expanding marketing operations, so to speak.
A post on the Dark Web by LockBit (translated from the original Russian) suggests the group is supplementing the ransomware (“lockers”) it already sells, rather than replacing it:
I have repeatedly said that I want to collect as many top lockers as possible in one panel, who have well-known and good sources lying around, write – I will buy. I don’t care what the reviewers think and say. It is important for me to expand the arsenal in my wonderful panel. Each advert decides for himself what to work with or combines several lockers in an attack on one company if time permits. Agree, it would be nice if I had some other Petya Ransomware or something else epic in my panel?
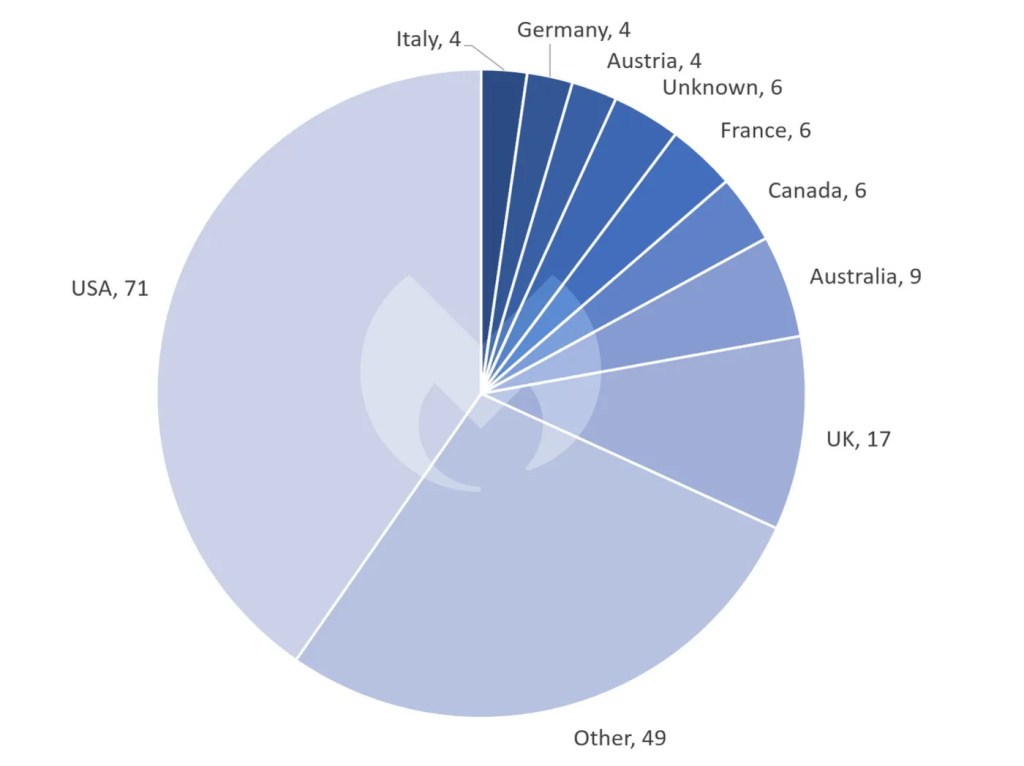
Known ransomware attacks by country in January 2023
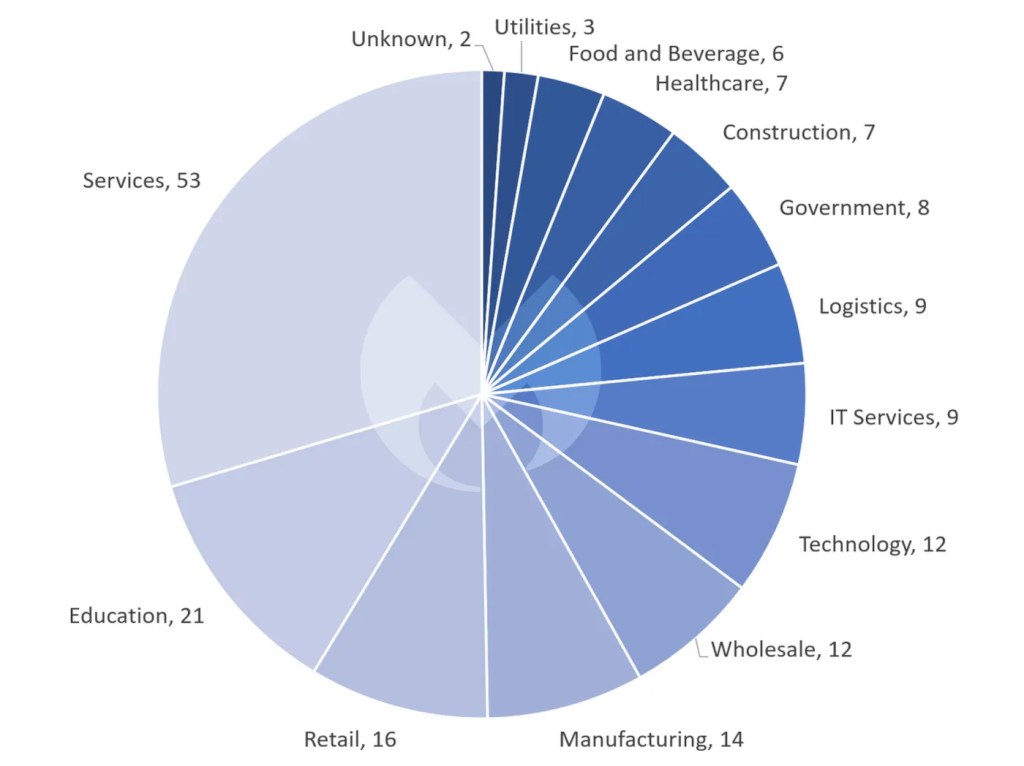
Known ransomware attacks by industry sector in January 2023
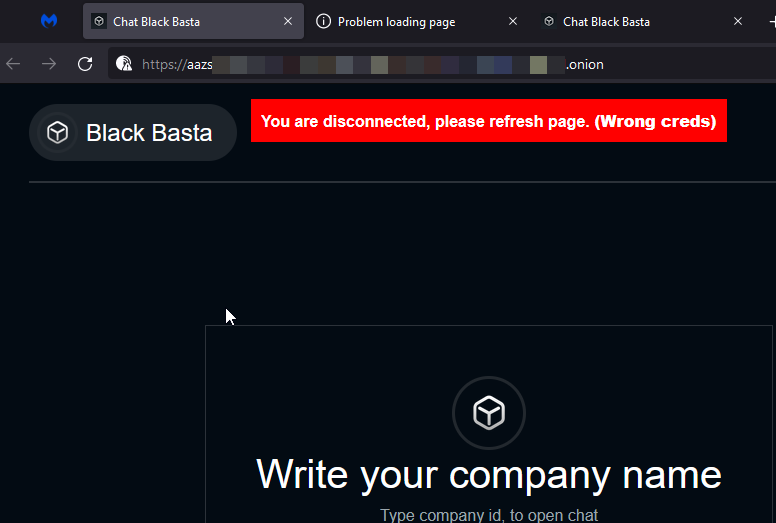
While LockBit was plowing through the new year, however, there was nothing but radio silence from another notorious ransomware player: BlackBasta. Ever since we started tracking them in April 2022, BlackBasta’s high placement every month among the ranks of other ransomware groups has been more or less a foregone conclusion. Their absence of activity in January therefore bears mentioning.
Apparent inactivity by ransomware gangs is complicated by the fact that their Dark Web leak sites only show companies that didn’t pay a ransom, so an extremely successful month for them also looks like an inactive month. A month where nobody refused to pay would be hugely unusual though.
Having said that, the Black Basta News Tor site, where it publishes new victims, has been down for several weeks. We saw that it was reactivated on January 22, but the next day it went down again. The backend to the site used to contact the victims seems to be down as well.
On the other hand, attacks by Vice Society—the ransomware gang responsible for an infamous attack on the LA Unified School District—have shot up to their highest level in three months. Vice Society is believed to be a Russian-based group whose ideal prey appears to be universities, colleges, and K-12 schools. The Federal Bureau of Investigation (FBI) even released a joint Cybersecurity Advisory (CSA) in September, after observing that Vice Society has disproportionately targeted the education sector.
In January, Vice Society published the data of nine schools on its leak site. It’s perhaps not a coincidence then that attacks on the education sector are the highest they have been in three months.
Last month we introduced a newcomer named Endurance, a solo actor who successfully infiltrated big corporations and breached several US government entities. In January the lone wolf managed to crack the top five biggest ransomware gangs for the month, launching successful attacks on places such as car marketplace Autotrader, where they stole data belonging to 1.4 million users. Another newcomer we introduced last month, Unsafe, which recycles leaks from other ransomware groups, added seven new victims to its rap sheet in January.
Play’s surge in December activity fell by about 76% percent in January. At the same time, we witnessed the ‘return of the dead’ with AvosLocker, placing itself back on the map for the first time since October 2022.
Hive seized
Hive ransomware is no stranger to the Threat Intelligence team: It was one of the most widely used RaaS in 2022 and indeed if their 15 attacks in December was any indication, Hive showed no signs of slowing down going into the new year.
Hive’s final chapter came to a close in late January, however, after the United States Department of Justice (DoJ) confirmed it had launched a successful disruption campaign against them.
The disruption campaign has reportedly had access to Hive’s infrastructure since July of 2022. Its access became public on Thursday when Hive’s Dark Web site began showing a notice that “this hidden site has been seized”.
According to the DoJ, the Hive ransomware group has targeted over 1,500 victims in over 80 countries, including hospitals, school districts, financial firms, and critical infrastructure, attempting to extort hundreds of millions of dollars from victims in the United States and around the world.
We can’t say we’re sad to see them go.

Nevada Ransomware
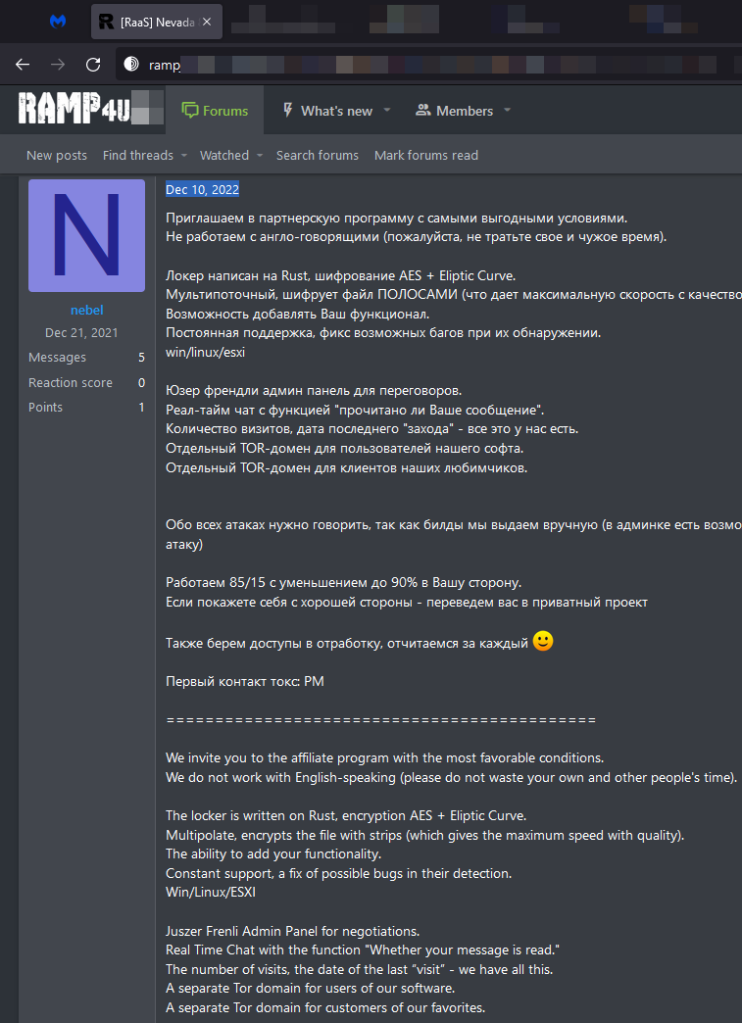
Nevada is a relatively new ransomware which emerged on the Dark Web right before the start of 2023, but it wasn’t until late January that it got a serious upgrade.
On December 10, an actor named ‘nebel’ published a post promoting the project on the RAMP underground community, which is known as a space for initial access brokers (IABs) and Russian and Chinese hackers. On January 30, researchers at Resecurity released a report on how the operators behind the project “updated and significantly improved the functionality of the locker for Windows and Linux/ESXi, and distributed new builds for their affiliates”.
Ransomware revenue down
According to blockchain data platform Chainalysis, ransomware revenue “plummeted” from $765.6 in 2021 to at least $456.8 in 2022. The data is based on an analysis of the cryptocurrency addresses known to be controlled by ransomware attackers.
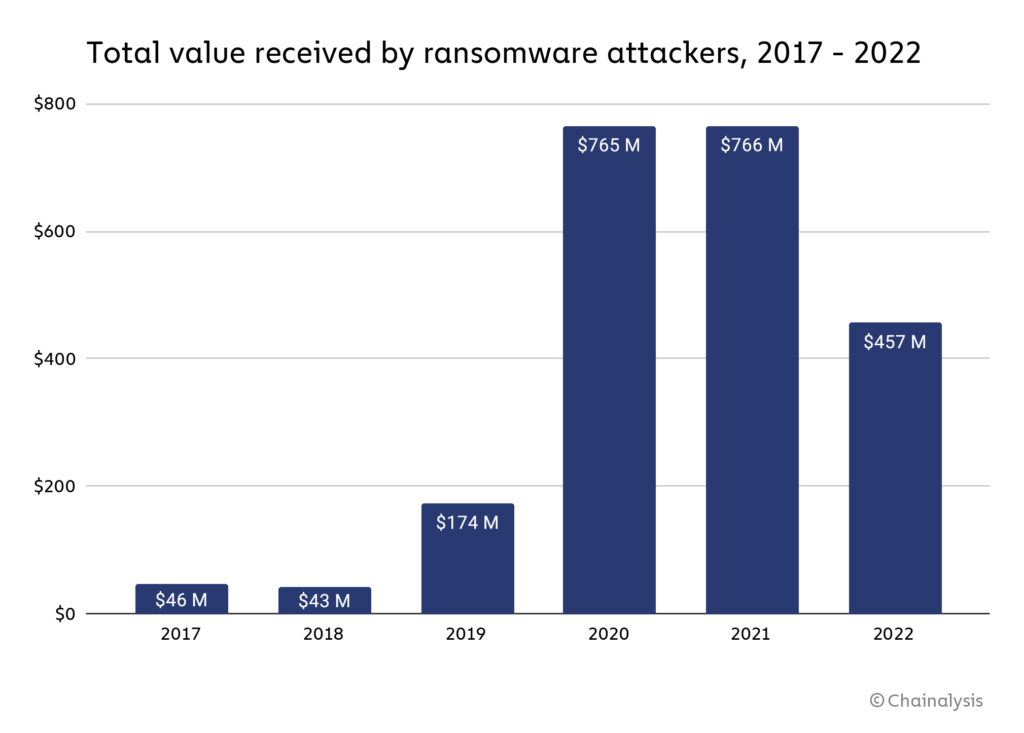
While the real numbers are likely much higher, it does present us with an idea of the development of ransomware payments. Last year’s estimate at this point seemed to show a decline from $765 million to $602 million, but turned out to be a small gain after correction.
According to our own research and Chainalysis, the declining numbers are likely due to victim organizations increasingly refusing to pay ransomware attackers.