Endpoint security has never been more important, and with the increasing complexity of the security stack, choosing the right solution can be confusing. The good news is that there is a guide available to help organizations navigate this complex landscape: the “Endpoint Security Evaluation Guide” eBook.
One of the biggest challenges in selecting an endpoint security solution is ensuring that it can protect against both existing and emerging threats, without negatively impacting system performance or causing too many false positives. This is where MRG Effitas’ independent lab assessment comes in.
Evaluating endpoint security today
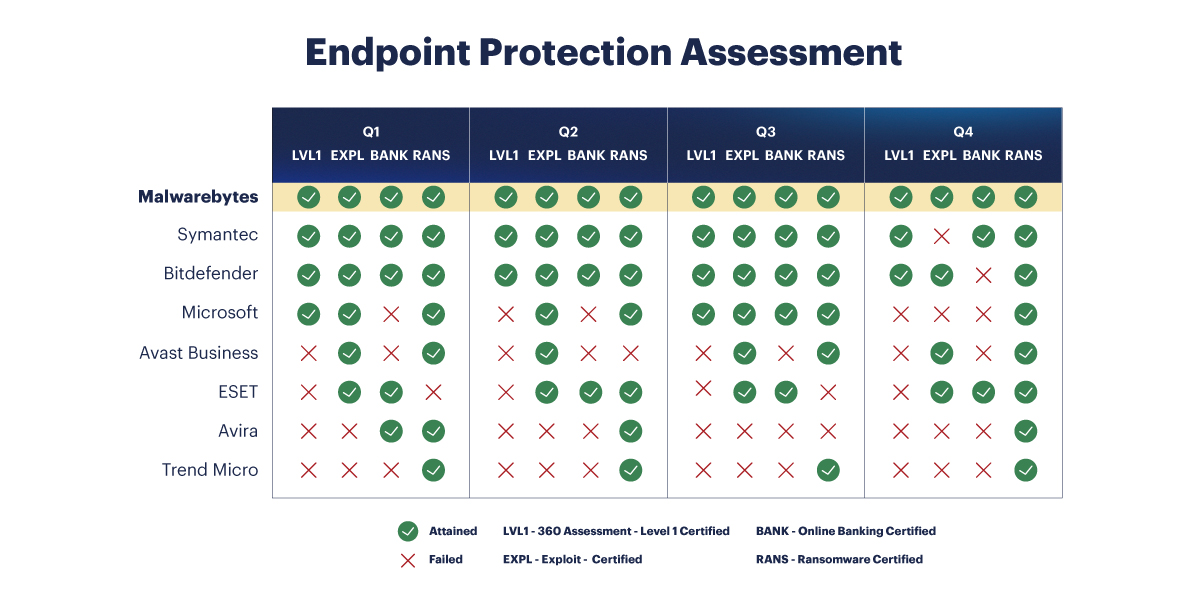
MRG Effitas’ 360° Assessment & Certification evaluates endpoint security vendors against nine vital criteria for efficacy, performance, and reliability. These include blocking potentially unwanted applications, preventing exploit and post-exploitation techniques, and blocking in-house ransomware samples. Based on a product’s performance on these criteria, MRG Effitas awards four certifications: 360° Level 1, 360° Exploit, 360° Online Banking, and 360° Ransomware.
Malwarebytes is a well-known name in the endpoint security industry, and it’s no surprise that they were put to the test in MRG Effitas’ 360° Assessment & Certification. The “Endpoint Security Evaluation Guide” eBook features Malwarebytes’ results on the assessment and includes head-to-head matchups of Malwarebytes versus each participating vendor. One shining takeaway is that Malwarebytes was the only vendor to win every certification in 2022.
Read our recap blog for the full results: https://www.malwarebytes.com/blog/business/2023/03/malwarebytes-only-vendor-to-win-every-mrg-effitas-certification-award-in-2022
In today’s complex threat landscape, it is more important than ever to choose an endpoint security solution that can effectively protect against a wide range of threats, while minimizing false positives and system impact. The “Endpoint Security Evaluation Guide” eBook, based on MRG Effitas’ independent lab assessment, is an essential tool for any organization looking to make an informed decision about endpoint security. Download below!