
APT attacks: Exploring Advanced Persistent Threats and their evasive techniques
Cyber criminals come in all shapes and sizes.
On one end of the spectrum, there’s the script kiddie or inexperienced ransomware gang looking to make a quick buck. On the other end are state-sponsored groups using far more sophisticated tactics—often with long-term, strategic goals in mind.
Advanced Persistent Threats (APT) groups fall into this latter category.
Well-funded and made up of an elite squadron of hackers, these groups target high-value entities like governments, large corporations, or critical infrastructure. They often deploy multi-stage, multi-vector approaches with a high degree of obfuscation and persistence.
But for every small-to-medium-sized business (SMB) out there asking themselves “Why would an APT group care about me?” We have the answer.
SMBs can be stepping stones to bigger targets—especially if they’re in a supply chain or serve larger entities. A whopping 93% of SMB execs even think nation-state hackers are using businesses like theirs as a backdoor into the country’s digital defenses.
In this post, we’ll break down how APT groups work, explain their tactics and evasive techniques, and how to detect APT attacks.
How APT groups work
The aim of APT groups is not a quick hit, but a long-term presence within a system, allowing them to gather as much information as they can while remaining undetected.
APTs stand apart from typical cybercriminals in several key ways:
- Motive: Unlike ordinary cybercriminals, APTs are primarily driven by the acquisition of intelligence. While they might engage in activities that yield financial gains, their primary funding comes from the state they serve, not from their operations.
- Tools: APTs have access to advanced tools and zero-day vulnerabilities. They keep these under wraps for as long as they can, only resorting to destructive malware when necessary.
- Crew: APTs consist of experienced and motivated individuals who work in close coordination with one another. This is a stark contrast to traditional cybercriminals, where distrust often prevails.
So, how does an APT work its dark magic? Here’s a quick rundown:
- Step 1: Reconnaissance. This could be anything from figuring out whether there’s sensitive data or information worth stealing to making a hit list of employees or ex-employees.
- Step 2: Infiltration. Usually, this involves some crafty social engineering, like spear phishing or setting up a watering hole to deliver custom malware.
- Step 3: Establishing a foothold. APTs need someone inside the target’s network to run their malware.
- Step 4: Expanding their reach. This might involve further deployment of malware, reconnaissance of the network, or other activities aimed at consolidating their position.
- Step 5: Data acquisition. The ultimate goal is to acquire the desired data. They might need to get more access in the network to do this.
- Step 6: Maintaining presence. Once they’re in, they might need to create more entry points or even leave a backdoor open for a return visit. If they’re done, they’ll clean up their mess to cover their tracks.
While not all these steps are required in every case, and the time and effort expended on each can vary widely, this provides a general framework for understanding how APTs operate.
Evasive techniques of APT attacks
Alright, now that we know the basics of how APTs operate, let’s dive into the specifics of their tools, techniques, and procedures (TTPs).
| TTP (MITRE ATT&CK) | Description |
|---|---|
| Phishing (Spear-phishing Attachment, Spear-phishing Link) | APT groups frequently initiate targeted spear-phishing attacks, often combined with social engineering and exploitation of software vulnerabilities, to gain initial access to a target network. |
| Execution through API (T1059.005) or User Execution (T1204) | Once inside a network, APTs use legitimate system tools and processes to carry out their activities in a way that blends in with normal network activity and avoids detection. |
| Exploitation for Client Execution (T1203) | APT groups frequently discover and exploit zero-day vulnerabilities — these are software flaws unknown to the software’s vendor at the time of exploitation. |
| Lateral Movement (Tactic ID: TA0008) | After gaining initial access, APTs use lateral movement techniques, such as Pass the Hash (PtH), to explore the network, elevate their privileges, and gain access to more systems. |
| Exfiltration Over C2 Channel (T1041) | APTs typically employ advanced, stealthy techniques for stealing data, such as splitting it into small packets, encrypting it, or sending it out during normal business hours to blend in with regular traffic. |
| Establish Persistence (Tactic ID: TA0003) | APT groups use techniques like multiple backdoors, rootkits, and even firmware or hardware-based attacks to maintain access to a network even after detection and remediation efforts. |
| Supply Chain Compromise (T1195) | APTs sometimes compromise software or hardware vendors to exploit the trust relationships between those vendors and their customers, thereby gaining access to the customers’ systems. |
In a word, APT groups use methods like “living off the land” (utilizing built-in software tools to carry out their activities), fileless malware (malware that resides in memory rather than on disk), encryption (to hide their communication), and anti-forensic measures (to cover their tracks).
Breakdown of different APT groups
Attribution is always a bit thorny when it comes to different APT groups, but some groups are rather well-known and their origin has become clear. A naming convention that not everyone follows is: Chinese APT actors are commonly known as “Pandas,” Russian APTs as “Bears,” and Iranian APTs as “Kittens”.
Some examples:
- APT28 aka Fancy Bear (Russia)
- Nemesis Kitten (Iran) a sub-group of Iranian threat actor Phosphorus (APT35)
- APT1 aka Comment Panda aka unit 61398 of the People’s Liberation Army (China)
Countries typically have different groups that focus on different targets, but generally speaking, some of the most frequently hit sectors are governments, aerospace, and telecommunications.
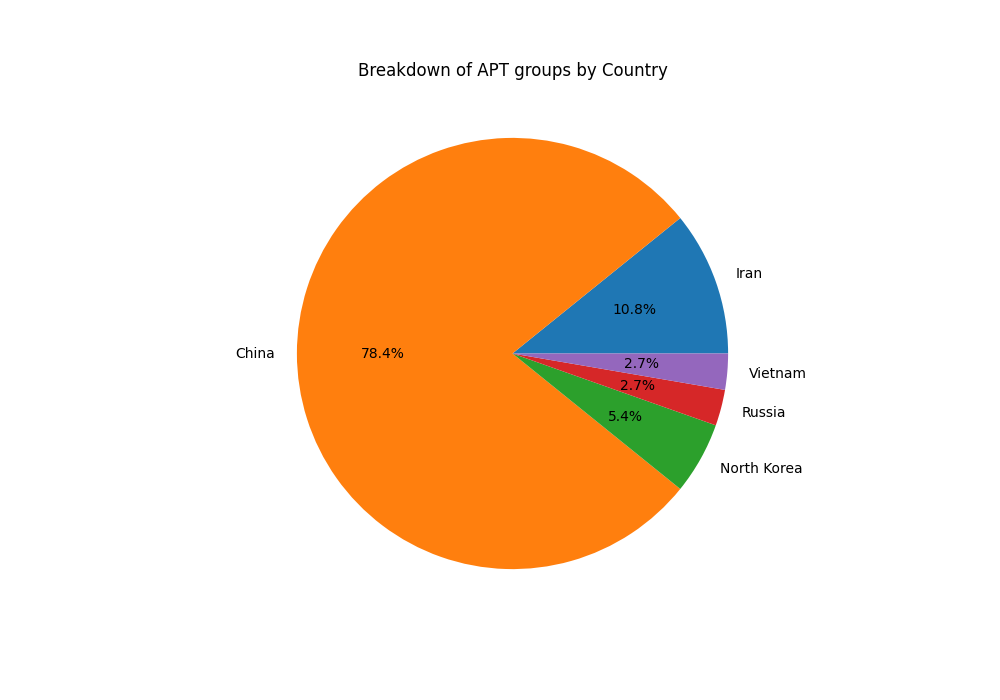
According to the cyber threat group list compiled by MITRE ATT&CK, we’re aware of over 100 APT groups worldwide. The majority of these groups have ties to China, Russia, and Iran. In fact, China and Russia alone are reportedly connected to nearly 63% of all these known groups.
For the purposes of this article, I compiled data on 37 different APT groups listed by American cybersecurity firm Mandiant and broke them down by country. I also ran numbers of the most frequently mentioned target industries; as this data comes from a relatively small sample size, treat these as rough estimates.
Detecting Advanced Persistent Threats (APTs)
You’ve got a few tricks up your sleeve when it comes to detect APTs on your network.
You can use things like Intrusion Detection and Prevention Systems, or IDS/IPS for short, which keep an eye on your network traffic. Regular check-ups on your logs and network can also give you clues.
Then there’s following bread crumbs known as Indicators of Compromise (IoCs) and watching for any weird behavior from users or end devices. But here’s the thing, these threats are getting smarter and trickier.
That’s where Endpoint Detection and Response (EDR) comes in. Let’s take a look at how EDR can help level up your defense game against these APTs.
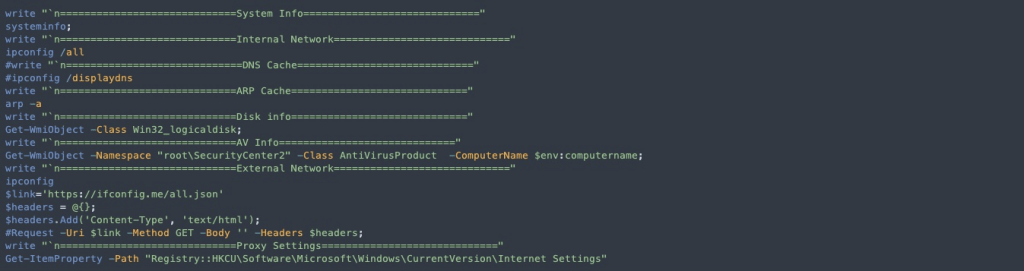
Consider, for example, the fairly common case of an APT group using Mimikatz, an open source tool for Windows security and credential management, to extract credentials from memory and perform privilege escalation. MITRE lists at least 8 APT groups observed to use Mimikatz for this exact purpose.
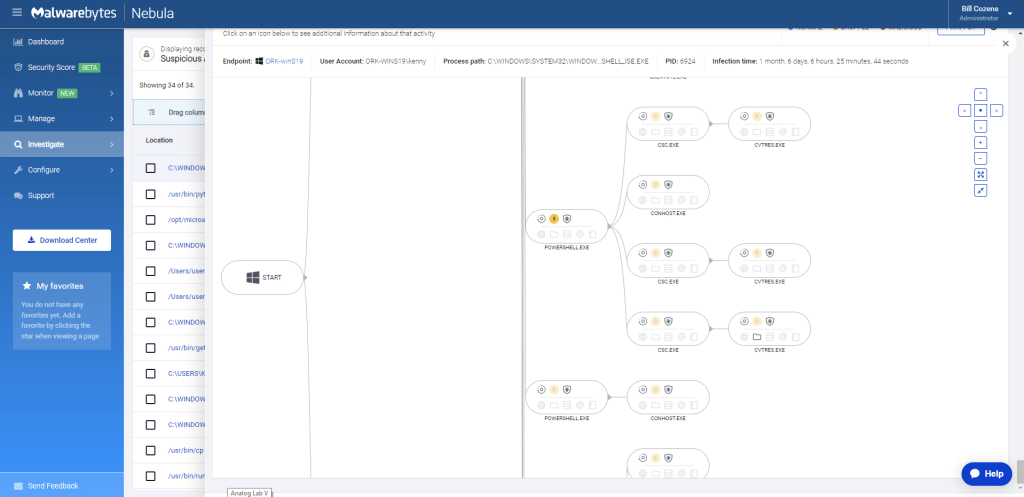
Using Malwarebytes EDR, we can find suspicious activity like this and quickly isolate the endpoint with which it’s associated.
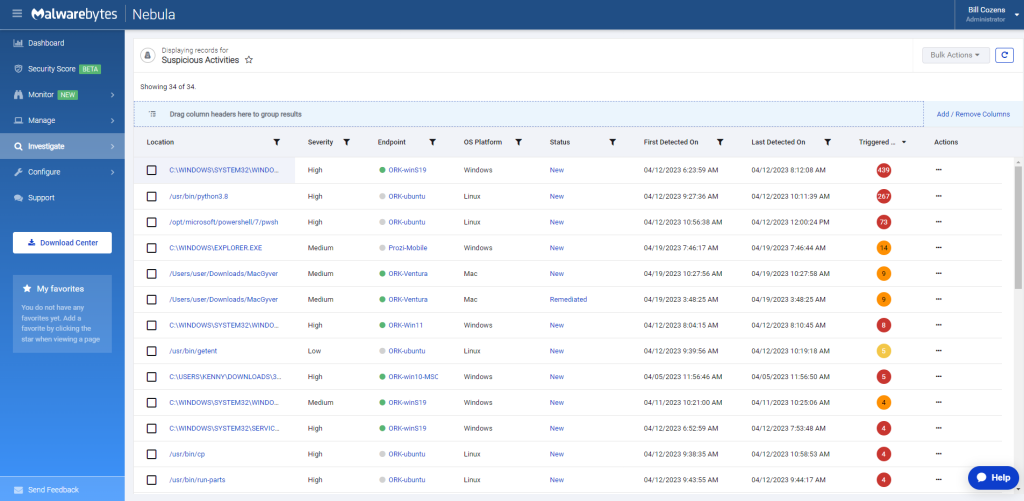
Clicking into a high-severity alert, we’ll see that we have categorization of rules to help a maybe newer or less savvy security expert understand what’s going on with this process.
What we see here is the actual categorization of behaviors that Malwarebytes witnessed in this process. Each of these little bubbles has been color coded to help you understand the severity of this issue.
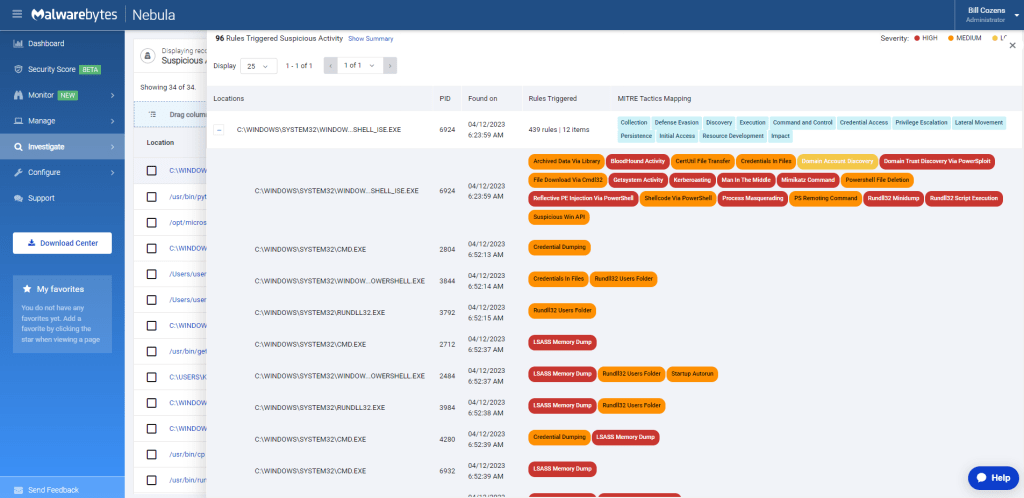
At the bottom, we have a detailed process timeline as well. Clicking into any of these nodes, we get a lot of rich context information about what this process did.
As a security analyst or an IT admin, the first question you typically ask when an incident occurs is: What happened? Do we know if it’s malicious? What is the actual extent of the potential damages? And so on.
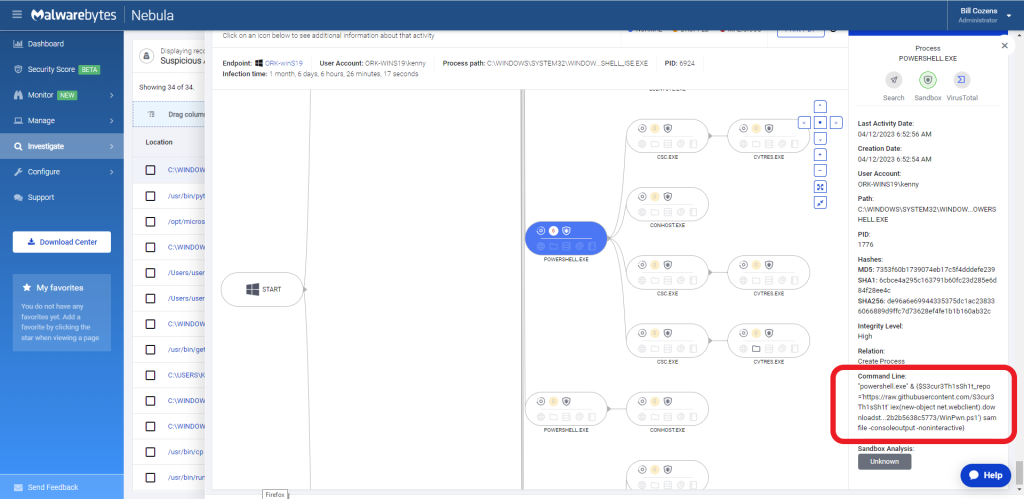
This is really suspicious looking code that could definitively be a sign of an APT on the network. This PowerShell command is downloading and executing Mimikatz from a remote server. Let’s remediate ASAP!
Closing this view out we’ll find a “Respond” option in the upper-right hand corner with a drop-down menu to “Isolate Endpoint“.
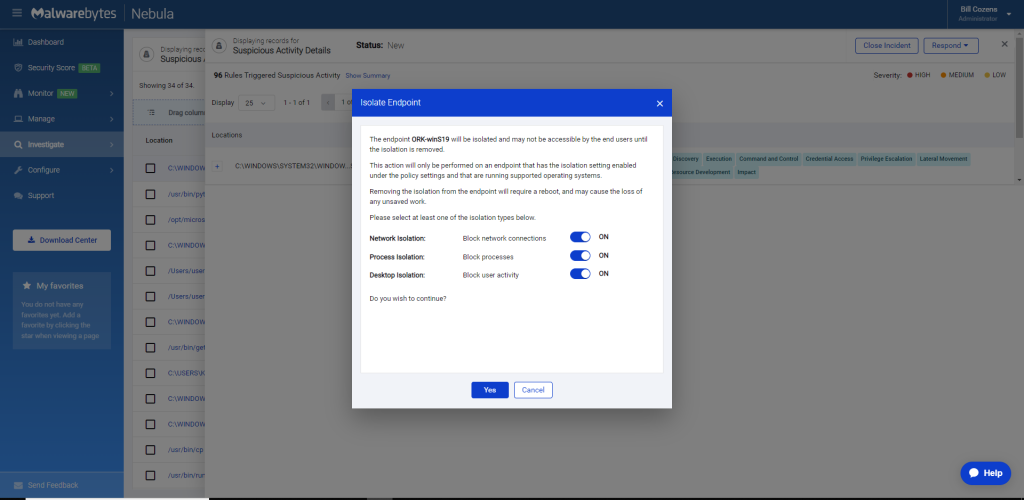
We have three layers of isolation that we can provide: network isolation, process isolation, and desktop isolation.
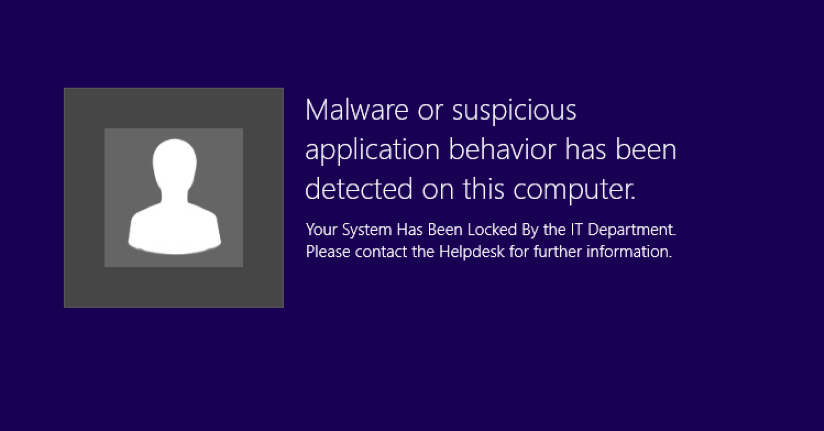
The network and process isolations are intended to give us the ability to quarantine that machine and prevent it from doing anything that is not authorized by Malwarebytes.
What this means is, we can still use our Malwarebytes console to trigger scans to perform other tasks and to review data, but the machine otherwise can’t communicate or run anything else.
Want to see Malwarebytes EDR in action? Try now.
Respond to APT attacks quickly and effectively
Managed Detection and Response (MDR) services provide an attractive option for organizations without the expertise to manage EDR solutions. MDR services offer access to experienced security analysts who can monitor and respond to threats 24/7, detect and respond to APT attacks quickly and effectively, and provide ongoing tuning and optimization of EDR solutions to ensure maximum protection.



