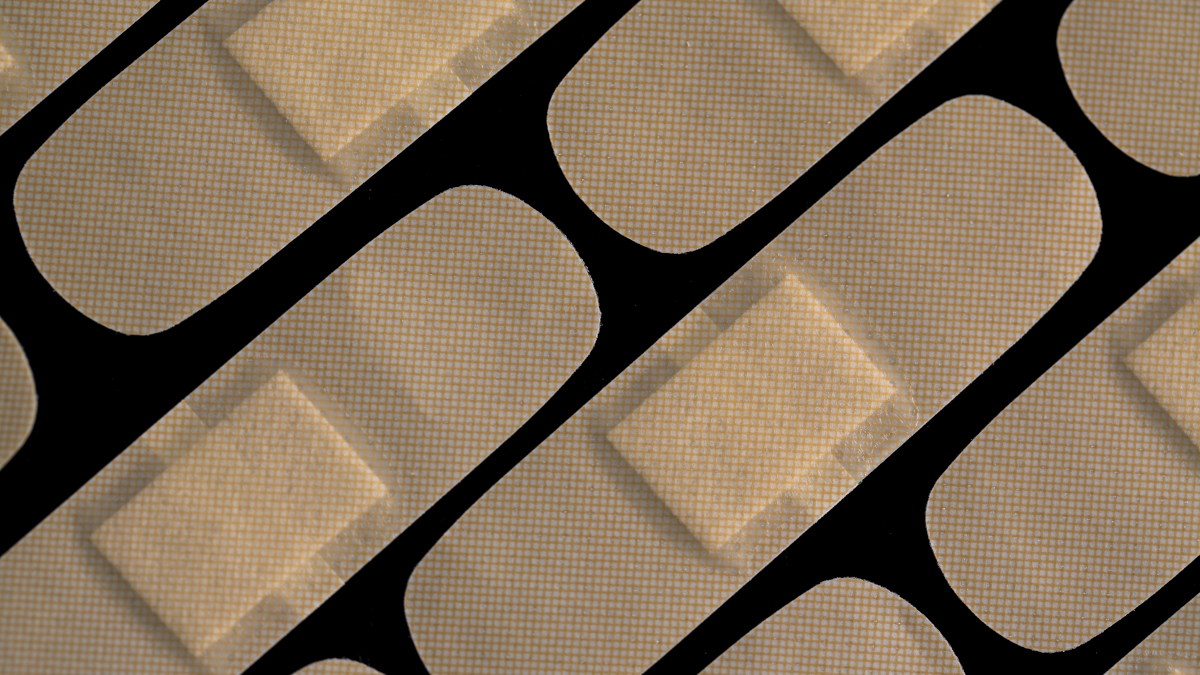
It looks like patching a wormable Remote Code Execution (RCE) bug in the HTTP stack of Windows 10 and Windows Server is likely to be top of most sysadmins’ todo lists after reading May’s Patch Tuesday updates. The monthly bug bonanza also features three other critical items among its 55 patches.
Although the wormable RCE (CVE-2021-311660) is not known to have been exploited in the wild, Microsoft warns that the attack complexity is low, and that “An attacker can expect repeatable success against the vulnerable component” with no need for authentication or user interaction. It has given the vulnerability a CVSS score of 9.8 out of 10.
The attack on the vulnerable component could be triggered by no more than a specially crafted packet. Since that packet is processed by http.sys, which runs in the kernel, the malicious code runs with commensurate privileges.
Worms that turned
A wormable flaw is one that can be used to create a network worm, a bit of malware that replicates itself across a network. Network worms invade a vulnerable system and then use it to launch further attacks on other vulnerable systems. Because each infected computer can infect many others, network worms have the potential to replicate exponentially and spread with alarming speed. (In fact, even if a worm has no malicious payload, the volume of activity it generates can be enough to cause significant problems by itself.)
Where vulnerable systems are accessible from the Internet, network worms can spread around the world in a matter of minutes or hours. In 2003, the infamous SQL Slammer worm infected all 75,000 its global, Internet-accessible victims within ten minutes of the attack starting. More recently, the WannaCry ransomware worm spread around the globe (and into and through numerous computer networks along the way) and infected hundreds of thousands of targets in a single morning.
Although worm-ability poses a significant risk, it isn’t by itself a guarantee of criminal success. Sometimes turning a vulnerability into an exploit is simply too difficult, or the results too unreliable to create a viable attack. Readers may remember the furore that surround the May 2019 Patch Tuesday, which featured a fix for a wormable RDP vulnerability, know as CVE-2019-0708, later dubbed BlueKeep. The widely-expected, globe-trotting RDP worm never materialised. Despite the appearance of proof-of-concept code, no widespread attacks ever occurred. Perhaps criminals simply found no need for an RDP worm that was bound to attract a lot of unwanted attention while they were having sustained success simply milking so many weak RDP passwords.
Those responsible for Windows systems should assume that criminals have read the same information they have and are poring over the fixes in an attempt to reverse engineer them. Act accordingly: you are in a race, patch as soon as you can.
Critical issues
The other critical patches made available this May include CVE-2021-26419, a scripting engine flaw that can be triggered by having an Internet Explorer user (yes, somehow that dinosaur among Internet users is still not extinct) visit a malicious website. Or, perhaps more likely, the flaw can be triggered from Microsoft Office documents. According to Microsoft, an attacker “could also embed an ActiveX control marked ‘safe for initialization’ in an application or Microsoft Office document”. Who could have guessed that in 2021 we’d still be finding ways to attack people with documents.
CVE-2021-28476 is an RCE vulnerability in the Hyper-V component of numerous Windows versions, with a CVSS score of 9.9. The flaw allows guest machines to meddle with their hosts, a strict security no-no. Microsoft reports that the most likely result of this meddling is denial of service but the flaw has the potential to trigger “device specific side effects that could compromise the Hyper-V host’s security.”
The last of the four critical vulnerabilities from this month’s lode is CVE-2021-31194, an OLE Automation RCE about which the company has little to say. Taciturn it may be, but it does tell us the bug has a CVSS of 8.8 and it’s rated critical, both signals you should patch it anyway.
Overall this month’s patch Tuesday is small compared to recent months, which we hope will be a relief to any sysadmins kept busy by recent Exchange vulnerabilities.
Take your rest while it’s (relatively) quiet. You know it won’t last.
Update May 18, 2021
In case you need any more incentive to patch the wormable http.sys flaw CVE-2021-31166, Proof-of-Concept (PoC) code was released on GitHub on May 16 and it is… disarmingly uncomplicated. A video accompanying the PoC code shows a Windows computer being forced to restart thanks to a simple HTTP request, generated by a 14-line Python script (that could easily be boiled down to curl one-liner).
Microsoft wasn’t kidding when it said the attack complexity was low.
Update May 24, 2021
Over the weekend Bleeping Computer reported the research of Jim DeVries, showing that the 2004 and 20H2 versions of Windows 10 and Windows Server running Windows Remote Management (WinRM) are also vulnerable to CVE-2021-31166. Enterprise Windows endpoints have WinRM enabled by default.