
How to protect RDP
You didn’t really think that the ransomware wave was coming to an end, did you? You may be tempted to think so, given the decline in reports about massive ransomware campaigns. Don’t be fooled.
Over the last five years, one of the primary attack vectors for ransomware attacks has been the Remote Desktop Protocol (RDP). Remote desktop is exactly what the name implies, a tool for remotely controlling a PC that gives you all the power and control you would have if you were actually sitting behind it—which is what makes it so dangerous in the wrong hands.
Bruce-force attacks
Threat actors use brute-force password guessing attacksto find RDP login credentials. These attacks use computer programs that will try password after password until they guess one correctly, or run out of passwords. The passwords they guess can be sold via criminal markets to ransomware gangs that use them to breach their victims’ networks.
Once they have RDP access, ransomware gangs can deploy specialized tools to:
- Elevate their privileges (when needed)
- Leave backdoors for future use
- Gain control over wider parts of the infiltrated network
- Deploy ransomware and leave payment instructions
The first three steps are most important for businesses to pay attention to, as they need to be examined after a breach has been noticed. The easiest and cheapest way to stop a ransomware attack is to prevent the initial breach of the target, and in many cases that means locking down RDP.
Securing RDP
If you want to deploy software to remotely operate your work computers, RDP is essentially a safe and easy-to-use protocol, with a client that comes pre-installed on Windows systems and is also available for other operating systems. There are a few things you can do to make it a lot harder to gain access to your network over unauthorized RDP connections:
- Decide if you really need RDP. This is an important question and you should not be afraid to ask it. Even if you are hardened against brute-force attacks, there is always the chance that attackers will find a remote vulnerability in RDP and exploit it. Before you enable RDP for anyone, be sure that you need it.
- Limit access to the users who need it. Reduce the number of opportunities an attacker has to guess a weak password by following the principle of least privilege. This cannot be done from the Remote Desktop settings but requires security policies. We have included a guide on how to do this later in this article.
- Limit access to specific IP addresses. This is another form of following the principle of least privilege. There is simply no need for many IP addresses to have access to your RDP clients. Rather than banning the IP addresses that don’t need access, allow only those that do.
- Use strong passwords. Even the most persistent attacker will only ever guess very weak passwords because it is more cost effective to make a few guesses on a lot of computers than it is to make lots of guesses on one. So the first and most basic form of defence is to have users choose even moderately strong passwords—meaning passwords that don’t appear in lists of the most commonly used passwords, and aren’t based on dictionary words. Of course, getting users to actually do that is notoriously difficult, so you need to use other hardening measures as well.
- Use rate limiting. Rate limiting (such as Malwarebytes Brute Force Protection) has the effect of significantly strengthening the defenses of weak passwords. It works by reducing the speed at which attackers can make login attempts, typically by shutting them out for a period of time after a small number of incorrect guesses. This represents a huge barrier for a computer program looking to race through tens or even hundreds of thousands of password attempts.
- Use multi-factor authentication (MFA). MFA can stop password guessing in its tracks but it can be difficult to roll out and support. Any second authentication factor will make attacks significantly more difficult, but factors that don’t require user interaction—such as hardware keys and client certificates—are the most robust.
- Put RDP behind a VPN. Forcing users to connect to a VPN before they can log in to RDP effectively takes RDP off the Internet and away from password guessing attacks. This can be extremely effective but it comes at the cost of maintaining a VPN, and simply shifts the burden of securing your users’ point of access from RDP to the VPN. Diligent patching is essential. In the last few years ransomware gangs and other cybercriminals have made extensive use of vulnerabilities in popular, corporate VPNs.
- Use a Remote Desktop Gateway Server. This provides additional security and operational benefits, like MFA. The logs it takes of RDP sessions can prove very useful if you find yourself trying to figure out what might have happened after a breach. Because the logs are not on the compromised machine, they are harder for intruders to modify or delete.
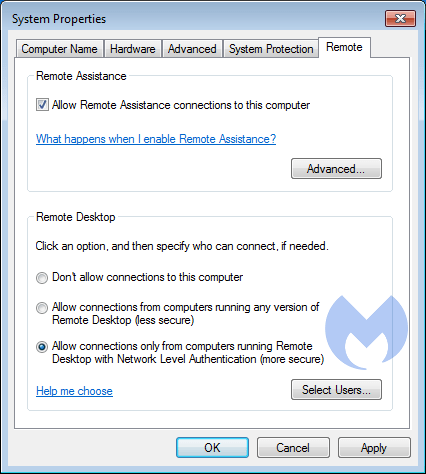
- Do not disable Network Level Authentication (NLA). NLA offers an extra authentication level. Enable it, if it wasn’t already.
Other things that might help
The things in the list below aren’t effective enough to constitute genuine hardening, but might help reduce the volume of attacks you see. They are easy to do but they are not a substitute for the list above.
- Changing the RDP port. Some hardening guides recommend changing the RDP port so that it does not use the default port number, 3389. Although this mightreduce the number of scans that find your RDP clients, our research suggests that plenty of attackers will still find you.
- Retire the Administrator username. Although some password guessing attacks use a variety of usernames, including automatically generated ones, many of them simply try to guess the password for the user named Administrator (or the local equivalent). However, because usernames are not treated as secrets by either users or systems, unlike passwords, you should not rely on the obscurity of your usernames to protect you.
Limiting access to the users that need it
The first step in this process is to create a user group that will be allowed remote access. You can do this in the Group Policy Management Console (GPMC.MSC).
- In this console, select Computer Configuration > Windows Settings > Security Settings > Restricted Groups.
- Right-click Restricted Groupsand then click Add Group.
- Click Browse >type Remote > click Check Names and you should see “REMOTE DESKTOP USERS.”
- Click OK in the Add Groupsdialog.
- Click Add beside the MEMBERS OF THIS GROUP box and click Browse.
- Type the name of the domain group, then click Check Names >click OK > OK.
- On the PC, run an elevated command prompt and type GPUPDATE/FORCE to refresh the GPolicy.
- You should see the group added under the SELECT USERS button on the REMOTE tab of the PC’s SYSTEM PROPERTIES.
Now you can open the related local policies by opening Control Panel > System and Security > Administrative Tools > Local Security Policy > User Rights Assignment.
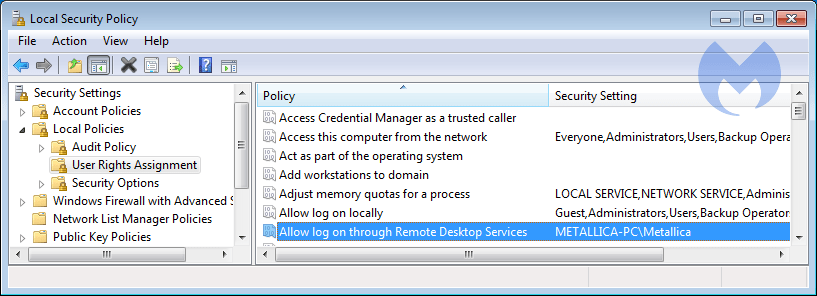
Remove the “Administrators” group from the “Allow log on through Remote Desktop Services” policy and certainly do not grant access to the account with the username “Administrator.” That account is perfect for the intruders—they would love to take it over. Also remove the “Remote Desktop Users Group” as contradictory as that may seem. Because by default, the user group “Everyone” is a member of the “Remote Desktop Users” group.
Now, add the user(s) that you specifically want to have remote access to this system, and make sure that they have the rights they need—but nothing more. Restrict the actions they can perform to limit the damage that they can do if the account should ever become compromised.
Secure your network resources
In the context of RDP attacks, it is also important that you apply some internal safety measures. PCs that can be used remotely should be able to use network resources, but not be able to destroy them. Use restrictive policies to keep the possible damage at bay that any user, not just a remote one, can do.
Aftermath of an attack
If you have been impacted by a ransomware attack via RDP, you’ll need to take some steps to better secure your network and endpoints. After you have recovered your files from a backup or by forking over the ransom, you need to check your systems for any changes the attackers have made that would make a future visit easier for them—especially if you decided to pay the ransom. By paying the threat actors, you have essentially painted a bulls-eye on your own back. You are now a desirable target, because they know you will pay to get your files back, if necessary.
To be sure there are no artifacts left behind, check the computer that was used to access the network via RDP for Trojans and hacking tools, and also any networked devices that could have been accessed from the compromised machine.
This article was originally published in August 2018 and was extensively updated in March 2022. Since this article was first published, Malwarebytes has added Brute Force Protection to the Nebula cloud-based security console. Check it out.



