Fuzzing, or fuzz testing, is defined as an automated software testing method that uses a wide range of invalid and unexpected data as input to find flaws in the software undergoing the test.
The flaws do not necessarily have to be security vulnerabilities. Fuzzing can also bring other undesirable or unexpected behavior of the software to light. But it’s good to realize that bugs discovered through fuzzing account for the majority of new CVE entries.
The purpose
Ensuring software quality is becoming more essential, but sometimes collides with deadlines, complex software engineering, and dependencies on other software. As such, fuzzing has become part of the quality assurance (QA) procedure before software is released. But it doesn’t stop there. After the release, the number of testers might go up, but not every one of them will be doing it for your benefit.
Fuzzing is particularly useful for exposing potential security vulnerabilities like:
- Memory leaks. A memory leak is a type of bug that occurs when a computer program incorrectly manages memory allocations in a way that memory which is no longer needed is not released. Memory leaks slow down the system up to a point where the system or the running process crash.
- Control flow errors and other runtime errors. A control flow error is an erroneous jump throughout an executing program induced by external disturbances. Runtime error is an umbrella term for any error that occurs during execution of a program.
- Race conditions. A race condition, or race hazard, is the behavior of a system where the output depends on the sequence or timing of other uncontrollable events. It becomes a bug when events do not happen in the order the programmer intended.
All these types of bugs can be exploited when the outcome is more or less predictable and can be used to work in the attackers’ advantage. The goal of fuzzing for bug bounty hunters is to induce unexpected behavior of an application and see if it leads to an exploitable bug.
Input types
The idea behind fuzzing is to release different types of input and look for hiccups. A crash or other strange behavior may mean that you are on to something. After the test you can repeat the input that caused the abnormality and test similar types of input to work out what might be the underlying reason. Causing unexpected behavior is only the first step when you are working out a vulnerability.
An application may have more than one attack surface. One can, for example, pass arguments to an application in several ways: Through the graphical user interface (GUI), by using command line options, or by using it on malformed or specially crafted files.
Web applications
The software undergoing the fuzzing can also be a web application. Web application fuzzing is mostly deployed to expose common web vulnerabilities, like injection issues, cross-site-scripting (XSS), and more. When testing online web applications, keep in mind that you want to test the application itself, not the infrastructure it is running on. In other words, leave some room for the regular users.
Test types
While it is understandable that at face value fuzzing sounds as if you are about to throw the kitchen sink at an application and see what sticks, but even fully automated methods will be more effective with some preparation. The input used to fuzz an application could either be crafted for a specific purpose, or randomly generated, but it helps to exclude input types that you already know the application will not accept.
A common approach to fuzzing is to define lists of values that have a bigger chance of raising an issue (fuzz vectors) for each type. These can be extremes, like very large numbers, or known issues from similar applications, like escaped characters or Structured Query Language (SQL) commands.
Rules of engagement
Note that many applications take exception to uninvited penetration testing. Check if the developer or owner of the software you want to scrutinize has a bug bounty program and read the guidelines to participate. Depending on which country you live in, and where the software owner resides, you could be breaking the law if you don’t follow the rules.
Existing fuzzing software
Below are some interesting leads if you want to find more in-depth information about fuzzing.
OSS-Fuzz is a fuzzing platform to make open source software more secure and stable. It was launched by Google as a response to the Heartbleed vulnerability. To be accepted to OSS-Fuzz, an open-source project must have a significant user base and/or be critical to the global IT infrastructure. Since its launch, OSS-Fuzz has become an important service for the open source community, helping get more than 8,000 security vulnerabilities and more than 26,000 other bugs in open source projects fixed.
One of the most well-know fuzzing tools is Burp Suite. Burp Suite is a powerful tool out of the box, but it can grow with you as you become more experienced. The professional version offers the opportunity to integrate automated and semi-automated processes with manual tooling. If you are starting or want to try it first, there is a Community Edition, or you can trial the Professional version for 30 days.
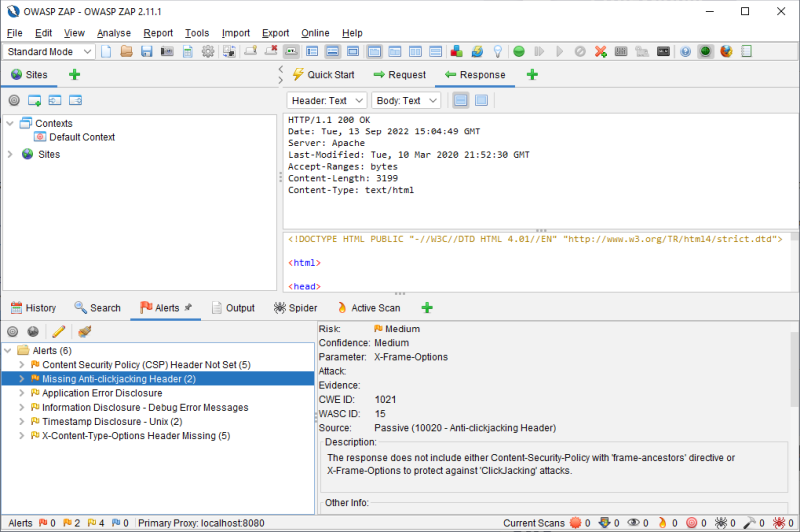
Another web app scanner which is certainly worth mentioning is OWASP ZAP. OWASP Zed Attack Proxy (ZAP) is a free, open-source penetration testing tool being maintained under the umbrella of the Open Web Application Security Project (OWASP). ZAP is designed specifically for testing web applications, and is both flexible and extensible. At its core, ZAP is what is known as a machine-in-the-middle proxy. It stands between the tester’s browser and the web application so that it can intercept and inspect messages sent between browser and web application, modify the contents if needed, and then forward those packets on to their destination.
Many other free fuzzing tools can be found if you search for them, and some are really useful for specific purposes, but you should keep in mind that most of them require an advanced knowledge level before you can expect any useful results. Many are command line tools and/or require you to have Python installed.
Even then it can be a steep learning curve, but it is one that is well worth it, in my opinion. Let us know your experiences in the comments, below.











