Endpoint Detection
& Response
Industry-proven through award-winning protection, ThreatDown EDR stops attacks against workstations and servers with security that catches what other solutions miss.
Cybersecurity challenges
Attacks are evolving
71%
Companies impacted by ransomware last year1
Agent sprawl = complexity
55
Average number of cybersecurity tools deployed at a company2
Lack of budget and resources
80%
Security alerts ignored3
1 2023 Malwarebytes State of Malware Report. 2 Anomali’s Cybersecurity Insights Report 2021. 3 ThreatDown Research
Keep threat levels down
Protect your organization’s workstations, servers and more with award-winning prevention, detection and response

Award-Winning
Next-Gen Antivirus Protection
Consistent top ranking of Level 1 certification in MRG Effitas 360 degree testing and #1 Endpoint Security Suite by G2.
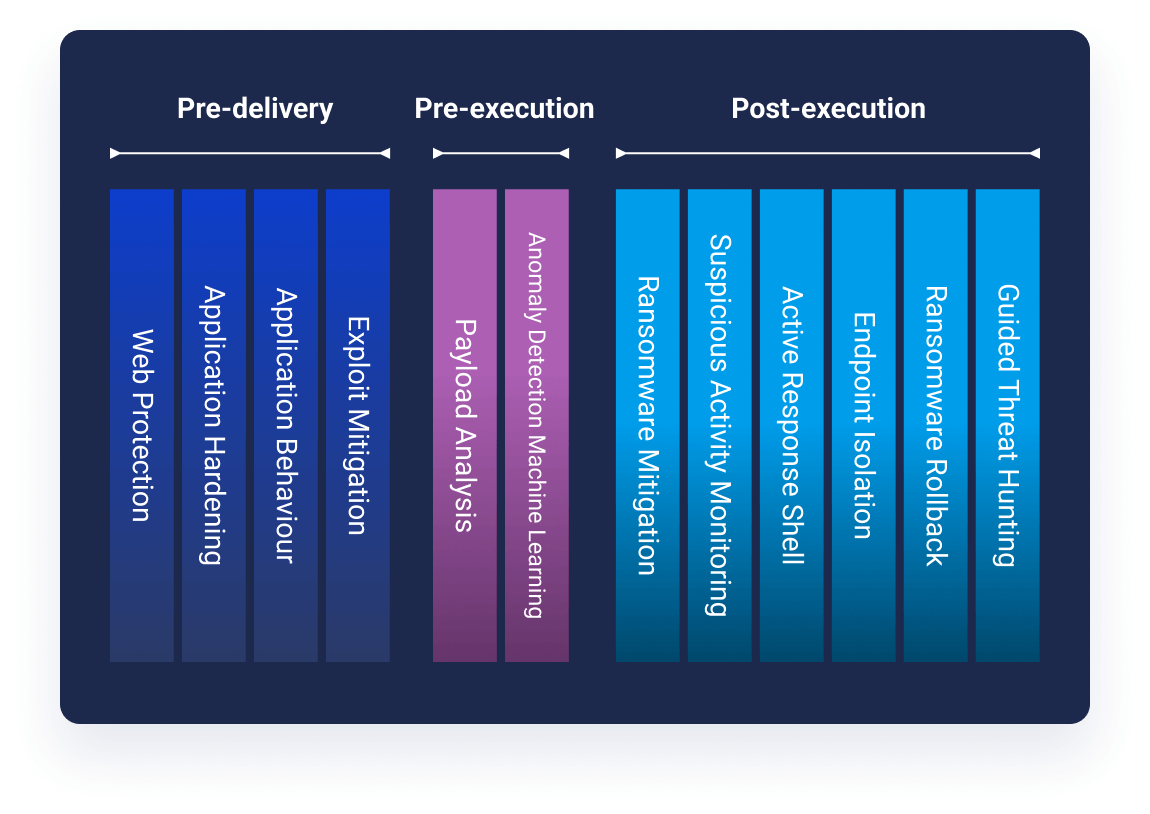
Accurate Detection & Fast Response
AI, machine learning and heuristics technologies detect and interrupt payload delivery before malicious actions can execute.

Ransomware Rollback
Restore files that were encrypted, deleted, or modified in an attack. Its Patented Linking Engine removes all malware traces, artifacts and configuration changes; to return customer devices to a healthy state and to prevent ransomware reinfection.
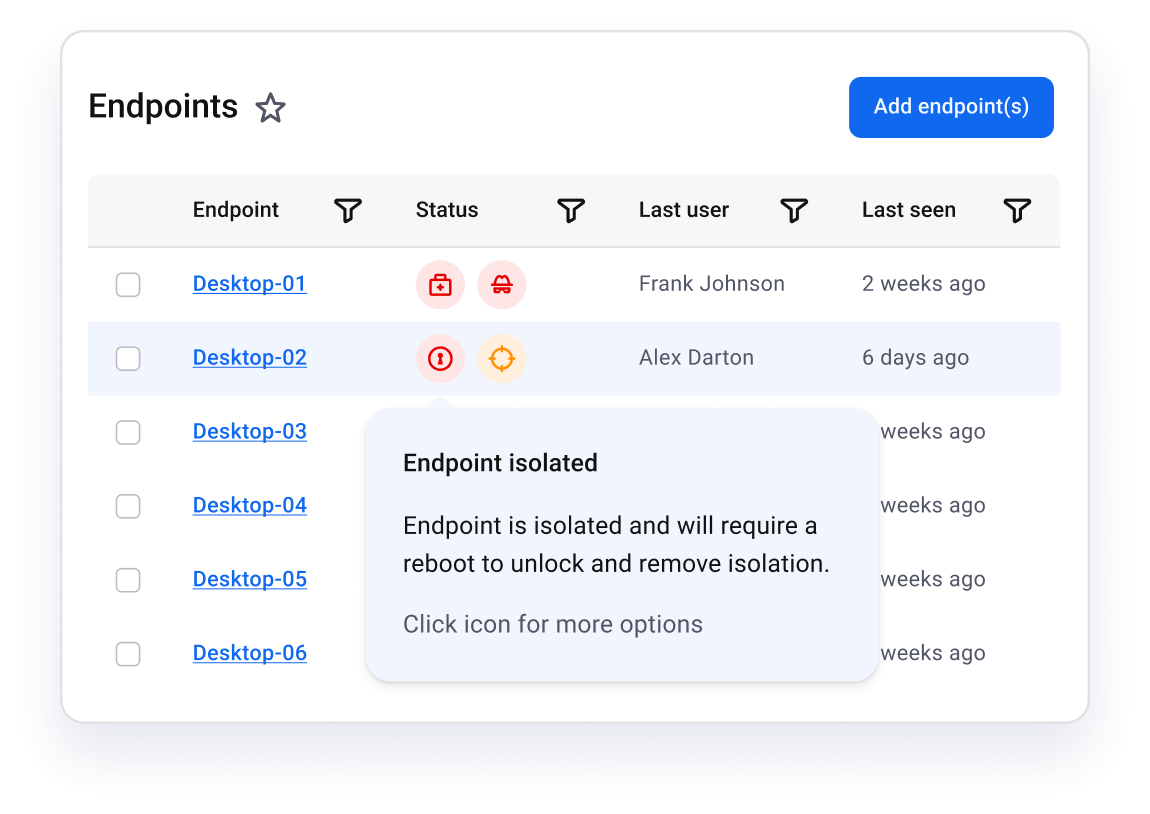
Attack Isolation
The only solution that isolates at all three levels:
- Network — limit device communications and stop malware from “phoning home”
- Process — halt malware and maintain employee productivity
- Desktop — block access logins and keep devices online for analysis
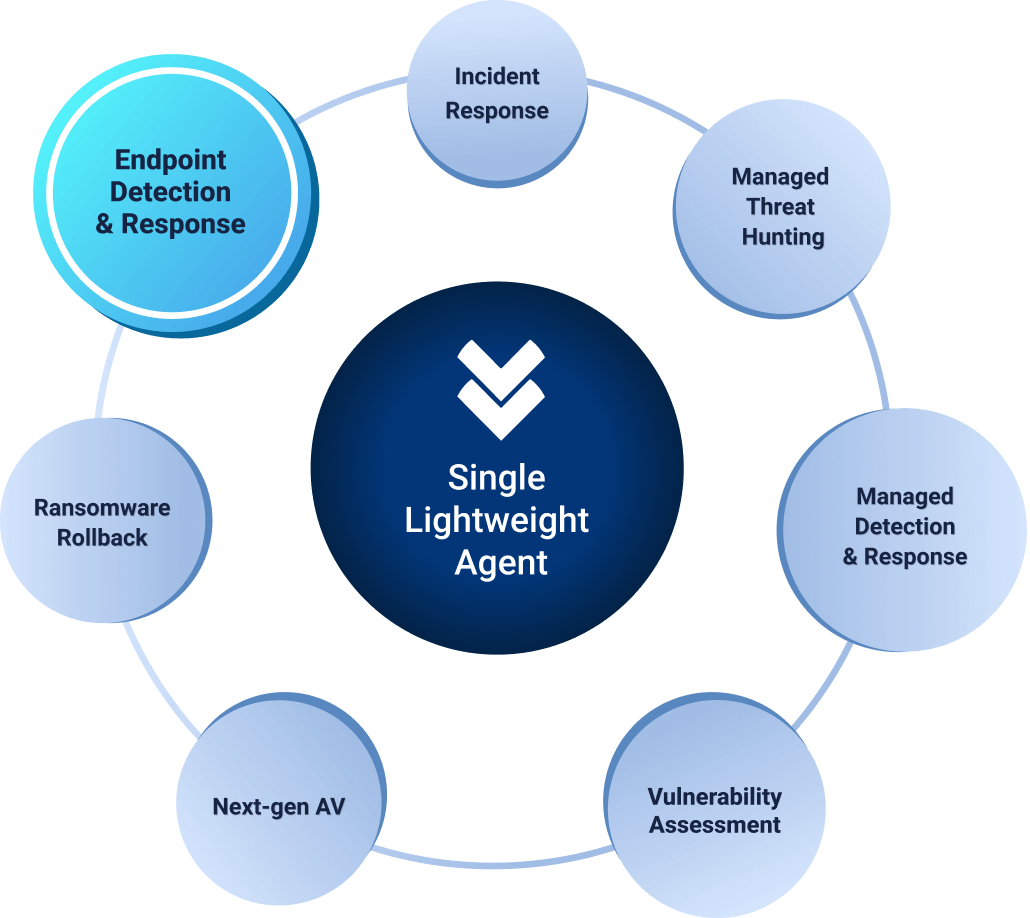
Single, Lightweight Agent
Our single, lightweight agent simplifies your security, reduces costs, easily deploys in minutes without a reboot and doesn’t slow down your system.
“ThreatDown EDR’s ransomware rollback and automated malware remediation capabilities are a great sales point. If we have a detection, we can go into that machine and hit the rollback, and we basically go back in time to before there was an infection.”
Logan Evans, Director of Information Systems
Coffee County School District

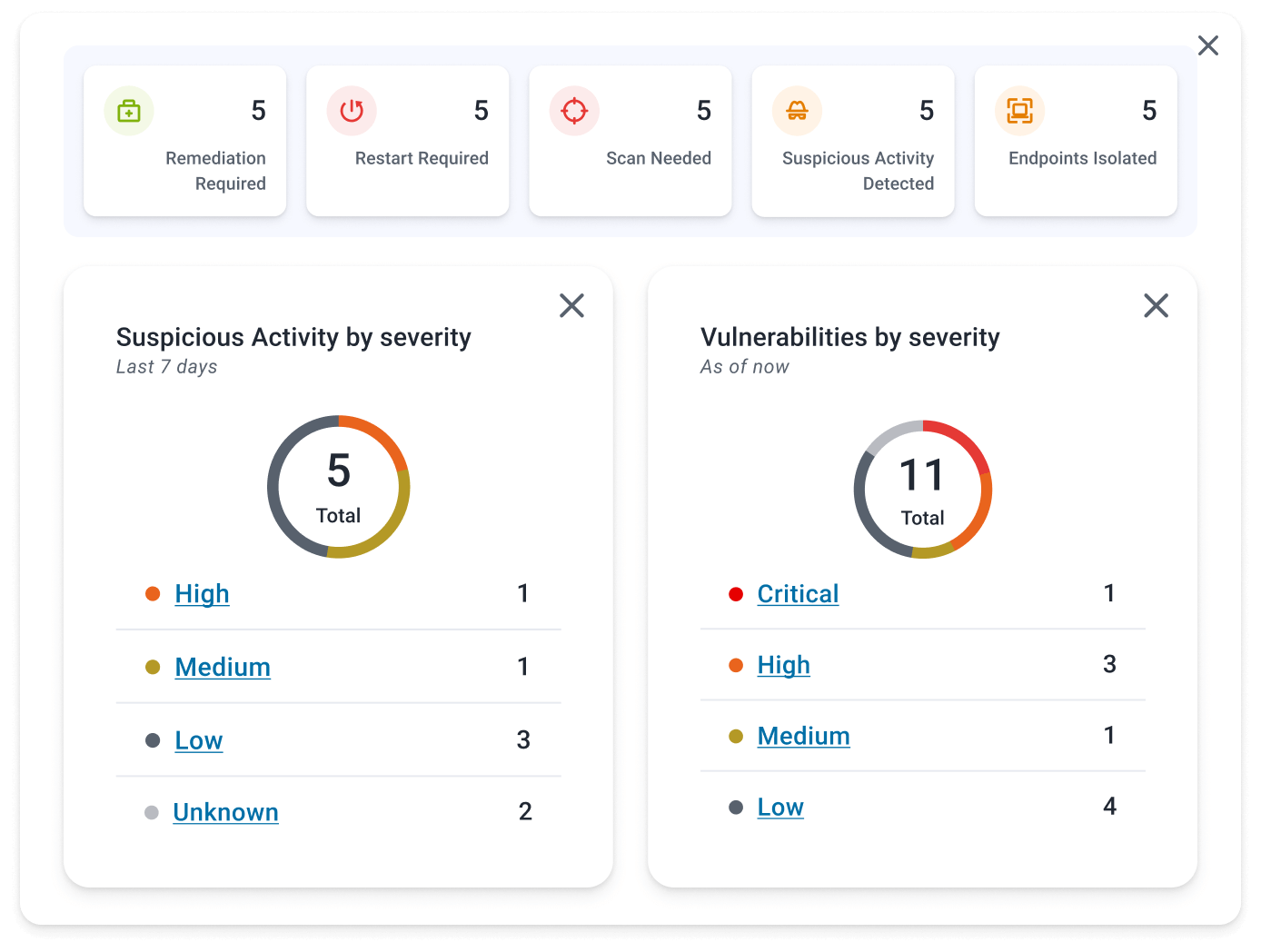
Bring your threat levels down with Security Advisor
Visualize and optimize your security posture in just minutes.
- At-a-glance security score
- Issue prioritization
- Instant advice & action
EDR powers these bundles
Core
Next-gen AV and threat surface reduction.
Annual pricing
/ per endpoint
What you get:
-
Incident response
-
Next-gen AV
-
Device control
-
Block unwanted applications
-
Vulnerability Assessment
Optional add-ons:
-
Core for Servers /
-
Mobile Security / $10
Advanced
Everything in Core plus expanded threat surface protection.
Annual pricing
/ per endpoint
What you get:
-
Incident response
-
Next-gen AV
-
Device control
-
Block unwanted applications
-
Vulnerability Assessment
-
Ransomware Rollback
-
Endpoint Detection & Response
-
Patch Management
-
Managed Threat Hunting
Optional add-ons:
-
Advanced for Servers /
-
Mobile Security / $10
Elite
Everything in Advanced plus fully managed detection and response.
Annual pricing
/ per endpoint
What you get:
-
Incident response
-
Next-gen AV
-
Device control
-
Block unwanted applications
-
Vulnerability Assessment
-
Ransomware Rollback
-
Endpoint Detection & Response
-
Patch Management
-
Managed Detection & Response (includes Threat Hunting)
Optional add-ons:
-
Elite for Servers /
-
Mobile Security / $10
Ultimate
Everything in Elite plus protection against malicious websites.
Annual pricing
/ per endpoint
What you get:
-
Incident response
-
Next-gen AV
-
Device control
-
Block unwanted applications
-
Vulnerability Assessment
-
Ransomware Rollback
-
Endpoint Detection & Response
-
Patch Management
-
Managed Detection & Response (includes Threat Hunting)
-
DNS (Web Content) Filtering
Optional add-ons:
-
Ultimate for Servers /
-
Mobile Security / $10