What does modern remediation look like?
Addressing your modern remediation needs
Your business needs modern remediation using an enterprise-grade solution to help manage and remediate your endpoints at scale.
The time required to remediate these incidents is substantial, often taking hours just to re-image a single endpoint. Lengthy dwell time and time-consuming re-imaging can often feel inevitable. Malwarebytes can significantly cut dwell time and lower the time and costs normally associated with constantly re-imaging endpoints.
“Malicious or criminal data breaches take an average of 197 days to identify and another 69 days to contain.” – Ponemon Institute
Essential components of remediation

Isolation of infected endpoints
During a cyberattack, it’s critical for you to isolate your endpoints to prevent the threat from spreading across your network. Malwarebytes’ Granular Endpoint Isolation uses network isolation, process isolation, and desktop isolation techniques to lock an attacker out and prevent malware from connecting to command and control servers.
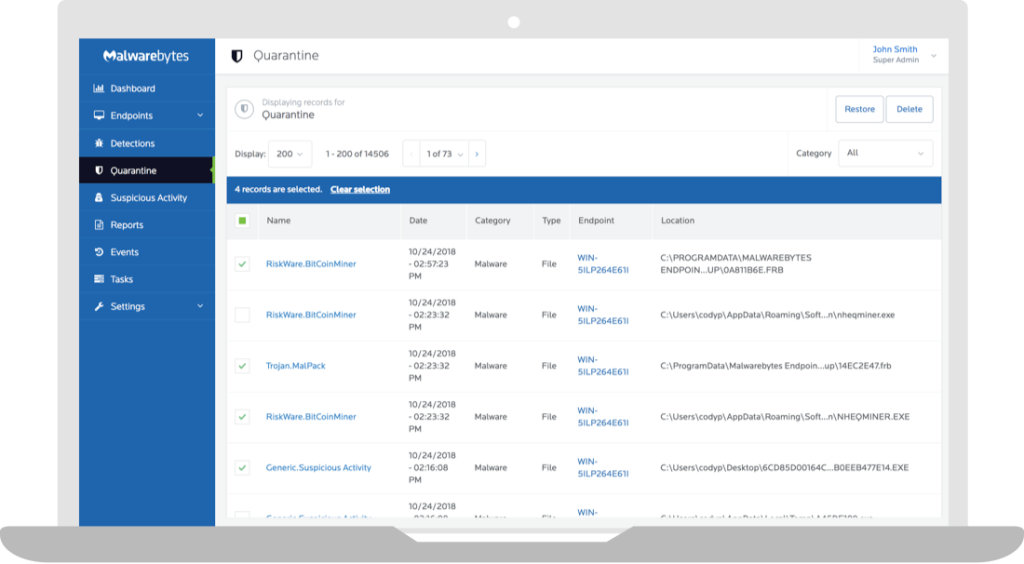
Thorough remediation of infections
Looking beyond threat prevention, your business needs to remediate detected threats after an attack. Most endpoint security solutions are unable to comprehensively clean up an infected or compromised endpoint.
In addition to real-time Multi-Vector Protection layers, Malwarebytes leverages our proprietary Linking Engine technology to thoroughly remove the primary threat payload along with detecting and removing dynamic and related threat artifacts from the endpoint. Malwarebytes uses our globally-trusted remediation to return your endpoints to a truly healthy state—without impacting the end user.e.
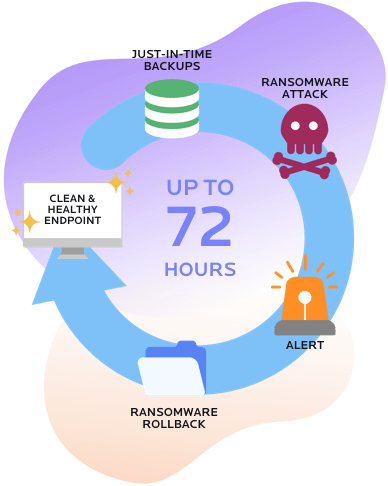
Recovery of lost or damaged files
Ransomware attacks are devastating for any business. Your business needs the ability to rapidly recover from a ransomware attack. Malwarebytes uniquely delivers Ransomware Rollback capabilities that allows your business to roll back encrypted, damaged, or deleted files for up to 72 hours.
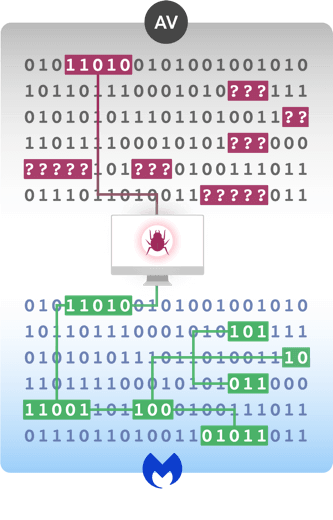
Powerful modern remediation for your business
Malwarebytes Endpoint Protection keeps your business endpoints reliably safe from advanced cyberattacks using Multi-Vector Protection with static and dynamic detection techniques. It also integrates thorough and effective remediation with proprietary Linking Engine technology.
Need protection, detection, and response capabilities?
Check out Malwarebytes Endpoint Detection and Response