
FAQ: How does ThreatDown ransomware rollback work?
As the old cybersecurity saying goes: “It’s not if, but when.”
Everyone and their grandma have repeated this foreboding maxim about the nature of ransomware attacks, but sadly, that doesn’t make it any less true. Time and again we’re reminded that ransomware can slip past even the best defenses.
Prevention alone, it seems, can only take us so far—so when ransomware hits, organizations need a way to emerge safely from the fallout, data intact.
Enter Malwarebytes Ransomware Rollback, which rescues your data from encryption by effectively “turning back the clock” of a ransomware attack. Dr. Strange style.
But how does it work, exactly? And what are some of the advanced settings that are available?
Let’s dive into the finer details in this post.
How It Works
The bedrock of Ransomware Rollback is a kernel mode driver to monitor file system changes and make a copy of files before modification. This includes self-protection against attack to the backups.
Malwarebytes Endpoint Detection and Response (EDR) first spends a 14-day period learning what applications on the system can be trusted. During this time, it logs the various applications that typically interact with files. After this period, the EDR establishes a list of trusted, or “whitelisted,” applications.
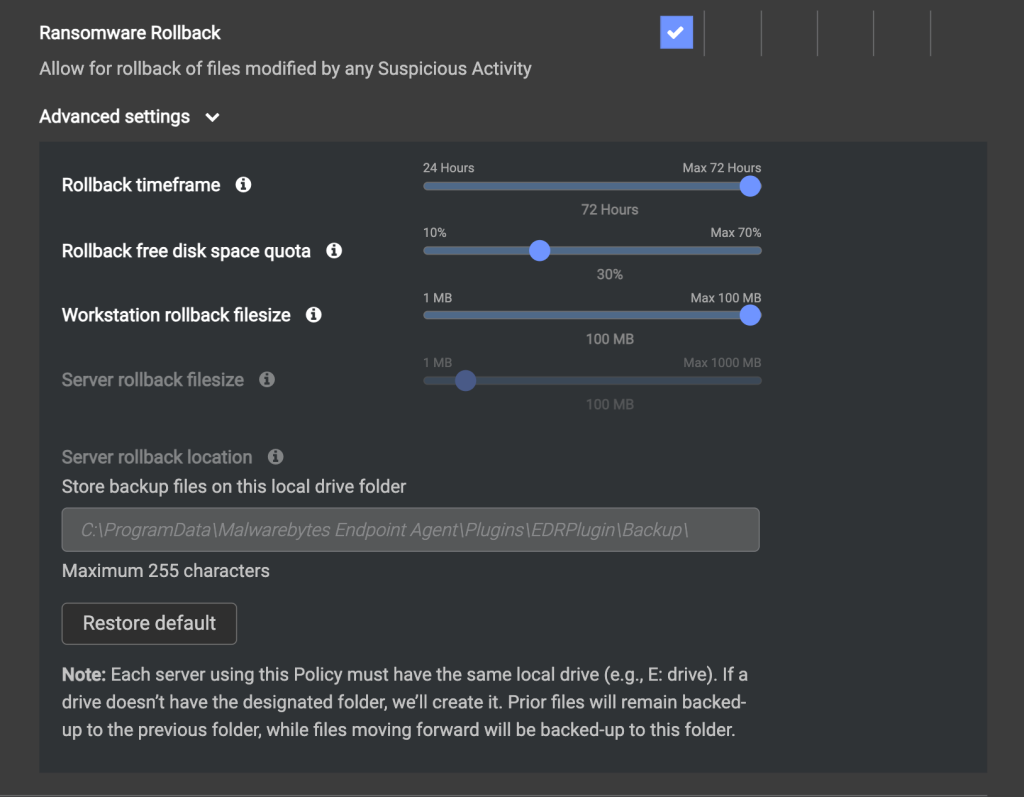
Advanced settings includes additional features for Ransomware Rollback. Learn more here.
For performance optimization, an application that is on the whitelist is ignored.
Before any application can make any changes, apart from ignored applications, Malwarebytes EDR saves a backup copy of the file it’s trying to modify. It is unknown at the time of modification whether a process is malicious, so every file is backed up.
If the application is later found to be ransomware that encrypts the file, making it unreadable and demanding a ransom for its decryption, the EDR system can use the backup copy it saved to restore the file to its previous state. This is what is meant by “rollback.”
When all’s said and done, the system effectively nullifies the ransomware attack by ensuring a recent clean, unencrypted copy of the file is always available.
FAQ
Does ransomware rollback use Volume Shadow Copy Service?
No, ransomware rollback does not use Volume Shadow Copy Service. Instead, it uses proprietary and patent-pending technology, with protected folders as malware often targets the Volume Shadow Copy Service.
How does the service know which files to restore, is it a snapshot?
Backups are continuous, for any files modified, and are not a snapshot
The process making the change is recorded for each file. Subsequently when a rollback is performed, it is precise because only files modified by the specific process are restored.
Where is the rollback cache stored in the system?
The rollback cache is stored in a hidden Windows system folder. Typically, you can find it under: C:ProgramDataMalwarebytes Endpoint AgentPluginsEDRPluginBackup.
Does ransomware rollback always use some amount of disk space? Why is that?
Yes, ransomware rollback always uses some disk space due to its buffer and cleanup operations. This means there will always be some small disk space used by the feature.
For every file modified, e.g., documents, pictures, etc., space for a copy is required. If there is no activity, then after a few days there would be zero used. However, if ransomware encrypted 10 Gb of files, then there would be 10 Gb of backup/before copies.
How much space does the rollback cache take up on a typical laptop or desktop?
On a typical laptop using common applications like Microsoft Office, the endpoint usually uses less than 200MB of space for a 72-hour rollback window and a maximum individual file size of 20MB – 100 Mgb.
If a computer is under attack and 10 Gb of files were encrypted, how much space would we use for the ‘before’ encryption file backup?
If a computer is under attack and 10 GB of files were encrypted, we would use approximately 10 GB of space for each ‘before’ encryption file. The system will back up the files in their original state before encryption, so the space used is equal to the size of the original files.
How far back can I rollback if my files are encrypted by ransomware?
By default, ransomware rollback stores the last 48 hours and is configurable up to 72 hours of file changes for files. You can alter these parameters in the Endpoint Protection Advanced policy.
What types of files does ransomware rollback back up? Are there any limitations or exclusions?
Ransomware rollback preemptively backs up all file types including pictures, documents, JSON/XML configurations, EXEs, unless they are explicitly excluded, globally excluded, or exceed the maximum file size.
What happens to my files in case of a ransomware attack if my disk is full?
If the hard drive is full and file encryption starts without enough disk space for a backup copy of the files, the data will be lost. Therefore, it’s crucial for users to monitor for low disk space.
Does Malwarebytes clean up files that have been backed up by Endpoint Detection and Response (EDR) after 72 hours?
Yes, our system is designed to be self-cleaning. Files that are backed up by EDR are frequently cleaned, if they are older than the configured period.
Try Ransomware Rollback Today
To recap, Malwarebytes Ransomware Rollback is a last-resort recovery tool within Malwarebytes EDR, designed for swift recovery after other defense layers have been compromised.
While useful, Ransomware Rollback doesn’t replace classic backups or EDR’s other proactive measures like Suspicious Activity Monitoring. It’s a rarely needed, but vital last-resort option.
Read our Ransomware protection with Malwarebytes EDR: Your FAQs, answered! article for more on how Malwarebytes EDR stops ransomware attacks.
For a more technical deep-dive into Ransomware Rollback, check out https://service.malwarebytes.com/hc/en-us/articles/4413802760851-Configure-Ransomware-Rollback-in-Nebula


