
Yes, Chromebooks can and do get infected
Thomas Reed
Thomas Reed
As a Mac malware specialist, I’ve seen more than my share of folks saying “Macs don’t get viruses” over the years. I’ve seen and experienced first-hand that this isn’t true—even on iOS, where despite having tight, built-in security, iPhones are still capable of getting infected by rare malware. I suppose that I shouldn’t be surprised, then, when I hear someone claim that “viruses on Chrome OS don’t exist.”
Although it’s certainly true that viruses—the class of malware that spreads itself by injecting malicious code into other processes—really don’t exist to a significant degree these days, even on Windows, it’s definitely not true that any platform is impervious to malware. Chromebooks are no exception.
No admin permissions, no problem, right?
Despite popular belief, Chromebooks don’t actually run Android. They run a system called Chrome OS, where all Android apps are run in emulation. There are certainly some security improvements in Chrome OS over Android. For example, the powerful device administrator permissions on Android are unavailable on Chrome OS, limiting the amount of “bad” that malware can do.
So, if malware can’t get those permissions, it’s not serious, right? Wrong!
If I had a dime for every time I heard someone minimize some new piece of Mac malware because it couldn’t get root permissions, I’d be able to take my wife out to a nice dinner. But these permissions aren’t always relevant. Bad guys can get away with a lot of bad stuff, including stealing user data, phishing for passwords, hijacking CPU power for the purpose of a botnet or cryptomining, and more, all without admin permissions. The same is true on Chrome OS.
Android malware = Chromebooks malware
Let’s take a look at a few examples of Android malware that would work perfectly well on Chrome OS, as they don’t require anything Chrome OS doesn’t provide.
First, consider the Buzzfeed story of apps from Chinese companies that engaged in ad fraud. These apps didn’t require anything more than permission to access a number of different bits of user data. Admittedly, there was no legitimate reason those apps had to access some of that data, but when installing a new app, people are prone to click past any requests just to get the app working.
These apps don’t really do much harm to the user, of course. The primary target of the fraud are the advertising networks. But that doesn’t make it okay, and any time an app like this is “wildly over-permissioned,” as the Buzzfeed article puts it, there’s the chance of an update to the app resulting in more malicious behavior.
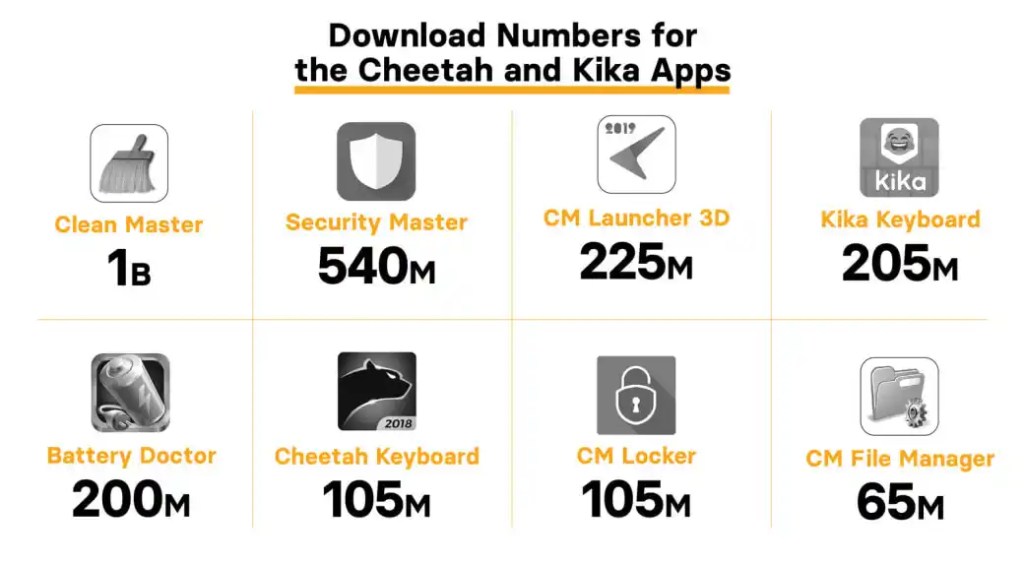
Image credit: Buzzfeed
A more malicious example comes in the form of some malicious cryptocurrency wallet apps found on Google Play. These apps would not require any particular device permissions, as their sole purpose is to trick the user into storing cryptocurrency in the fake wallets supported by these apps. In reality, any cryptocurrency stored cannot be withdrawn later. The perpetrator essentially stole money from the victims—and they could easily do the same to Chromebook users.
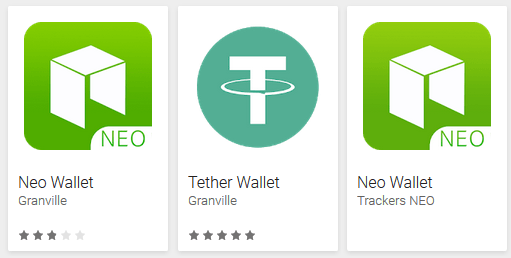
Image credit: Lukas Stefanko
Of course, affected users would have to be using cryptocurrency, so one could argue that they’d be more tech-savvy and less likely to fall for such scams. That’s not necessarily the case, but okay, let’s take a look at another example.
Consider the threat from fake antivirus software. This is software that poses as an antivirus, but provides none of the actual benefits. As described on our own blog, a family of fake antivirus software has been floating around since 2013. At one point, it was charging users $1.99 for the privilege of scanning the device, but covered up the fact that this was $1.99 per week!
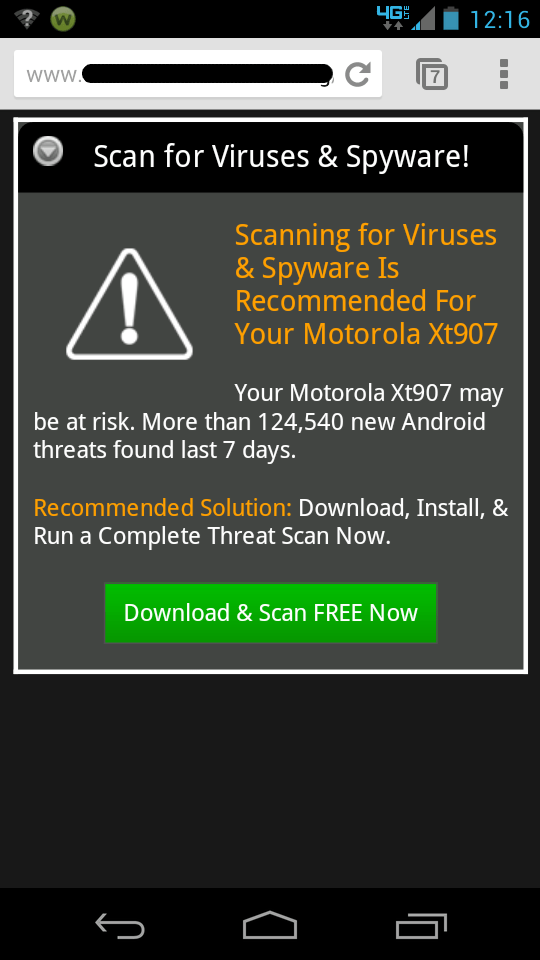
This is the kind of scam many people routinely fall for and it’s universal—device, OS, and platform agnostic. Any major computer system will be afflicted with this scourge, with the exception of iOS, and even that was once plagued by fake antivirus scams. (In fact, that’s the only kind that could exist on iOS, due to the impossibility of scanning the system in any way.) If I had a dime for every person I’ve encountered who has been tricked out of their money by scammers like these, I’d have enough to take my wife out for dinner and a show!
Mac and Chrome OS parallels
For a long time, people have said that Macs don’t get viruses. People have also said that the Mac App Store is the safest place to download apps. The same has been said of Chrome OS. Unfortunately, neither is actually true. Apps from the Mac App Store are sandboxed, just like the ones from Google Play on Chrome OS.
That hasn’t stopped criminals from making lots of money off the Mac App Store, however. I’ve documented many Mac App Store apps over the last few years that have defrauded users in a variety of ways. None of them have required root permissions, or exploits, or any other advanced malware techniques. Yet they have stolen user data and scammed users out of their money. I’ve worked hard to identify these apps, ensure that they are detected by Malwarebytes for Mac, and get them removed from the App Store when possible.
There should be no false illusions that Chrome OS is any different; it is not. The same tricks that are so successful on macOS can be equally effective on Chrome OS, and Malwarebytes has top-notch mobile malware researchers who work hard every day to keep Android and Chromebook users safe from such threats.
But does my Chromebook really need antivirus?
Since there is, definitively, already malware that can affect Chromebooks, it’s reasonable to install antivirus software on a Chromebook. And since Chromebooks are increasing in popularity, it’s also reasonable to assume cybercriminals will continue to develop more malware to get their piece of the pie. Once Pandora’s Box has been opened for a device, operating system, browser, or other platforms, we’ve never once seen the bad guys back away from it.
However, there is a catch to all of this. And to discover the catch, you must first answer this question: Does your Chromebook support Google Play?
Not all Chromebooks do. If yours does not, it cannot download malware through Google Play, much less third-party app stores, because it cannot download any apps at all. In such a case, you could use the free Malwarebytes browser extension beta for protection against browser-based attacks such as phishing or malicious websites and tech support scams, and that would be the most security you’d need (at the moment).
For those with Google Play, sure, you could simply try being careful about what you download. However, anyone can potentially be tricked by just the right malicious app with a large number of fake 5-star ratings, or just the right scam. If that concerns you, Malwarebytes for Android (and Chrome OS) is here to help.



