Recently-patched Apache Struts vulnerability used in worldwide attacks
Attackers are exploiting a critical vulnerability in Apache Struts 2 that was patched recently. Struts is a very popular open source platform to develop applications and websites.
On December 7, 2023, Apache announced versions 6.3.0.2 and 2.5.33 of Struts were now available to address a potential security vulnerability listed as CVE-2023-50164.
The vulnerability affects Apache Struts versions:
- 2.0.0 through 2.5.32
- 6.0.0 through 6.3.0.1
- 2.0.0 through 2.3.37 (EOL, no longer supported)
The vulnerability that has a CVSS score of 9.8 out of 10, lies in the frameworks’ file upload functionality and can be exploited to achieve remote code execution (RCE). There is an easy to follow proof-of-concept (PoC) available, which makes it easier for cybercriminals to exploit the vulnerability.
Basically it’s a path traversal flaw that allow attackers to read, and possibly write to, restricted files by inputting path traversal sequences like ../ into file or directory paths. The flaw is caused by parameter confusion, where an attacker can first capitalize a parameter in the request and then submit an additional parameter (in lowercase) that overrides an internal file name variable. That allows an attacker to bypass the built-in check and leave the path traversal payload in the final filename.
This allows a successful attacker to plant a web shell, a malicious script used by an attacker that allows them to escalate and maintain persistent access. In this case, the attacker gets the ability to write a server-side rendered file, such as a JSP (Jakarta Server Pages) file, into a target directory. The JSP payload is executed as soon as the attacker requests the file from the server and the server is compromised. Several international organizations like the Australian Cyber Security Centre (ACSC), the French Computer Emergency Response Team (CERT-FR), and content delivery giant Akamai are warning that they are seeing active exploitation.
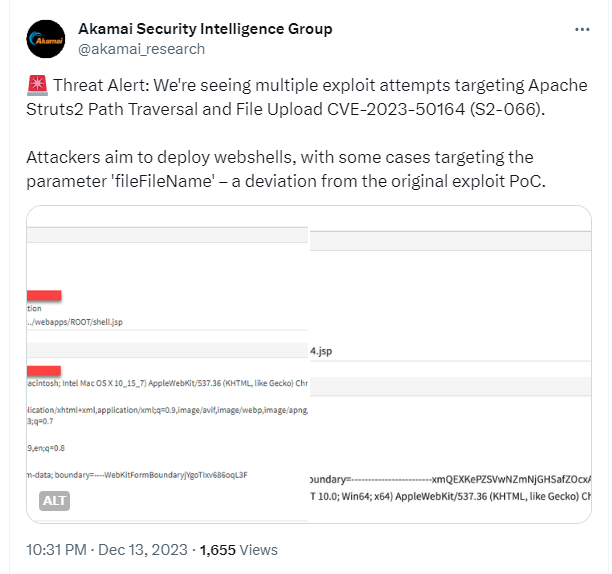
Tweet by Akamai
Because of the relative ease-of-use, we can expect to see a lot more of these attacks.
Update now
Users and administrators are encouraged to review the Apache Security Bulletin and upgrade to Struts 2.5.33 or Struts 6.3.0.2 or greater. There are no workarounds.
According to Apache this is a drop-in replacement and upgrade should be straightforward. The new versions can be found on the Struts download page.
Besides updating, additional measures may include:
- Sanitization checks on uploaded file data.
- Limit server application permissions to allowed directories.
- Track which applications in use within your environments are using Struts frameworks.
- On internet facing Java systems monitor for newly created files outside directories where they are expected.
- Continue to monitor the situation and respond to new information as it comes to light.



