5 facts to know about the Royal ransomware gang
When we first introduced the Royal ransomware gang in our November 2022 review, little did we know they’d rapidly evolve into one of the most potent threats in our ongoing monthly threat intelligence briefings.
In fact, the Malwarebytes Threat Intelligence team has tracked down a staggering 195 ransomware incidents credited to Royal from November 2022 to June 2023.
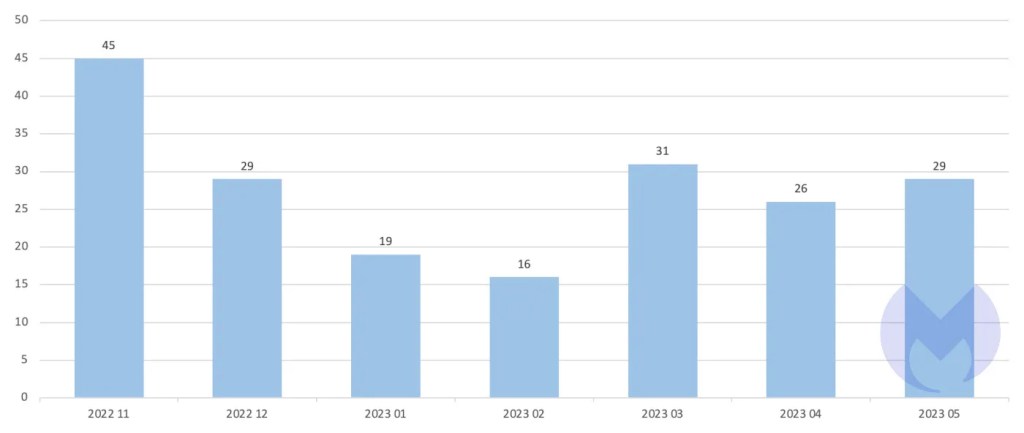
Known Royal attacks up to May 2023
These figures put Royal in a formidable third place for that time frame, trailing behind ALPHV (with 233 incidents) and the relentless LockBit (at 542 incidents).
In the rest of this post, we’ll be shedding some light on five key facts to know about the Royal ransomware gang.
1. 66% of their initial access is done through phishing
It seems there are three things certain in life: death, taxes, and phishing as a reliable attack vector.
Royal likes to send phishing emails with nasty PDFs attached. They have also been spotted using callback phishing attacks to lure victims into installing remote desktop malware.
Once someone falls for Royal’s phishing scam and ends up with malware on their computer, that malware tries to reach out to its command and control (C2) base. Then it starts downloading malicious tools to aid in lateral movement or exfiltration.
2. They have a massive USA bias
The Malwarebytes Threat Intelligence team found that 64% of Royal’s victims are from the USA.
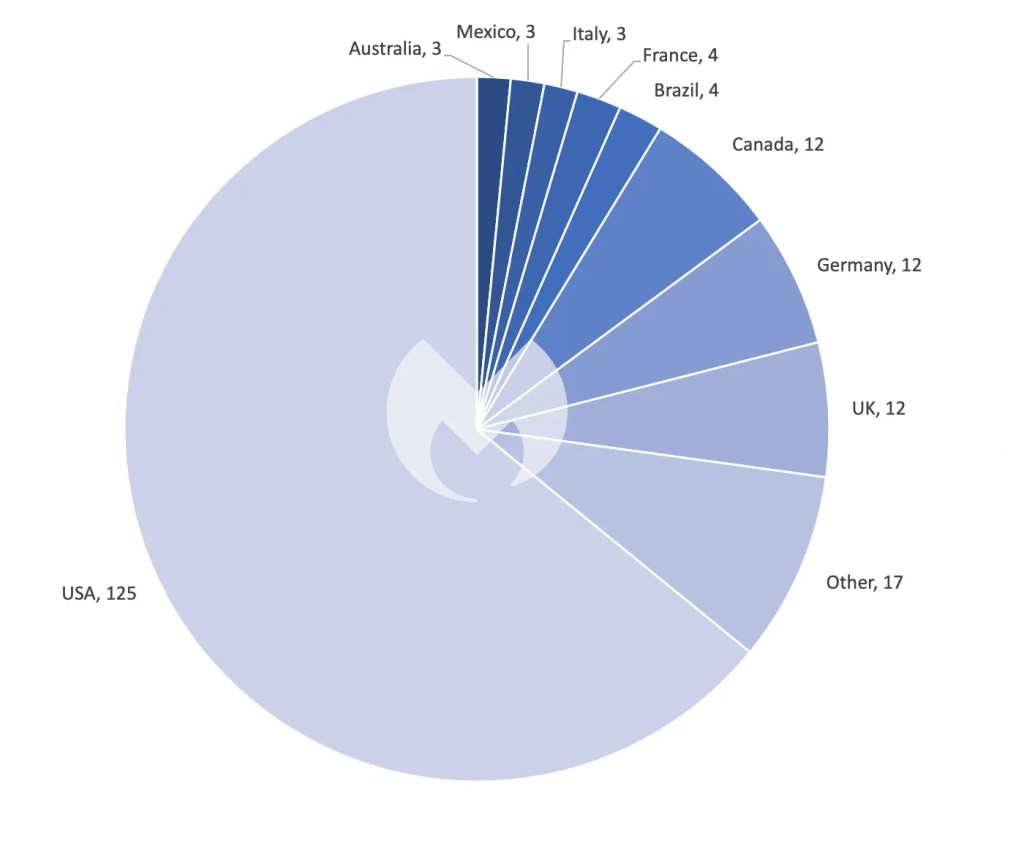
Known Royal attacks up to May 2023 by country
For comparison, 43% of all known ransomware attacks were on the USA in the same November 2022 to June 2023 time period. For gangs with more than 50 attacks, Royal was only second to Black Basta (67%) for attackers on the USA.
3. Cobalt Strike is one of the many legit tools they repurpose for malicious activities
Royal has been spotted using a host of legitimate tools to carry out their attacks under the radar. Just some of these tools include:
- Cobalt Strike: A legitimate commercial pen test to assess network security and simulate advanced threat actor tactics. Attackers use it for command and control, lateral movement, and exfiltration of sensitive data.
- System Management (NSudo): NSudo allows administrators to run programs with full system rights. Attackers use it to execute malicious programs with elevated privileges.
- PsExec (Microsoft Sysinternals): PsExec lets admins execute remote processes. Attackers use it to execute malware on remote systems.
By mimicking normal behavior, these tools can make it extremely difficult for IT teams and security solutions to detect any signs of malicious activities.
4. We’ve observed them reinfecting victims
Shortly after Royal rose to prominence in late 2022, a new customer joined the Malwarebytes Managed Detection and Response (MDR) service. The customer was previously a casualty of a Royal ransomware attack and thought they had dusted themselves off completely.
But soon after plugging in with us, we spotted some shady activities.
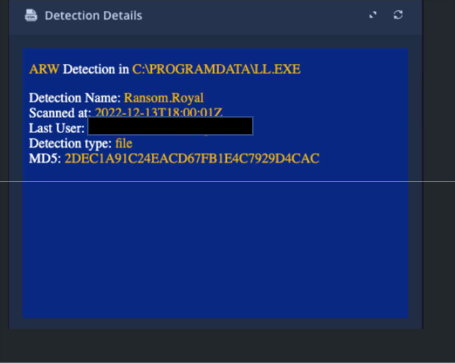
Malwarebytes MDR detecting “Ransomware.Royal” in the client’s network.
It turns out that Royal wasn’t content with having ‘merely’ attacked our customer once—they were still messing around in their system, potentially setting the stage for another damaging attack.
Fortunately, our EDR tech halted the ransomware in its tracks, and our MDR team managed to stop the post-ransomware havoc from spiraling further.
Still, it goes to show that attacks Royal doesn’t simply move on after a successful attack; they stay engaged for future exploitation, if they can help it.
5. The Services, Wholesale, and Technology industries are their top victims
When we look at Royal ransomware’s victimology, no overwhelming pattern stands out like it does for Vice Society.
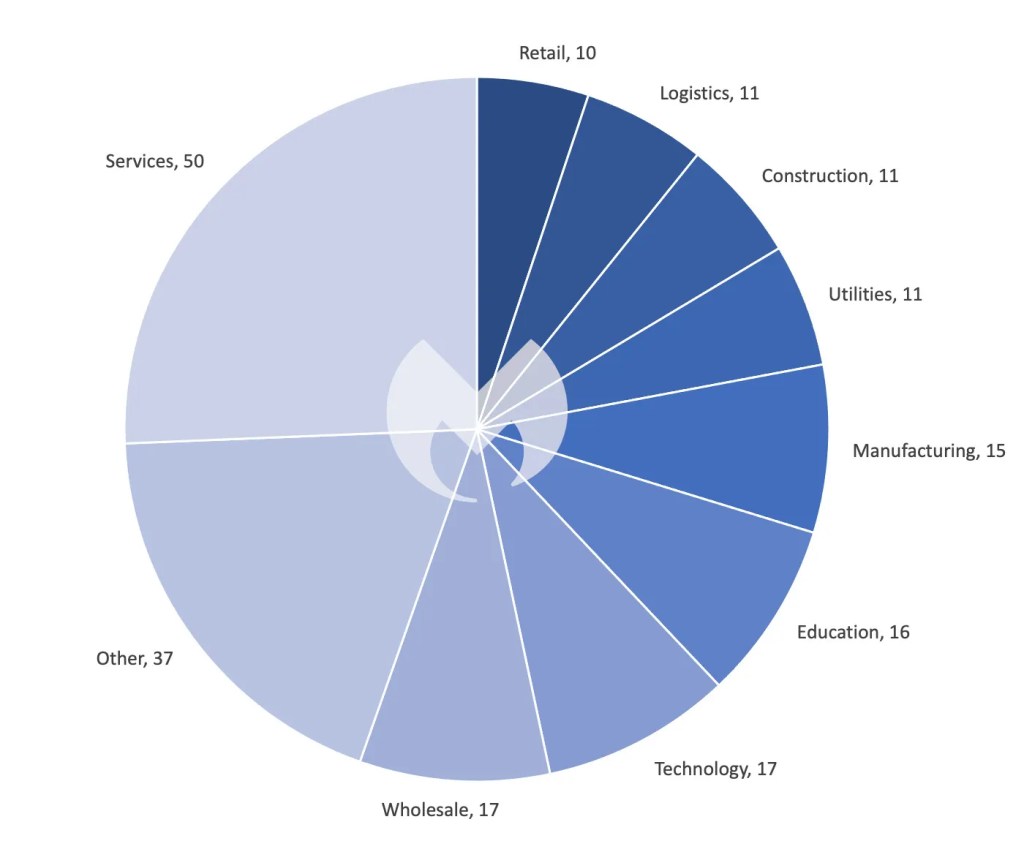
Known Royal attacks up to May 2023 by industry sector
Their victims per industry more or less match the averages across all ransomware gangs, suggesting they are sheer opportunists without a particular industry focus.
Like any ransomware gang, they leverage any potential vulnerabilities and security gaps across sectors, launching their attacks wherever they find the easiest point of entry.
Getting the upper-hand against the Royal gang
Royal has made a big name for itself in a short amount of time.
While it looks like Royal will attack anyone they think is an easy target, it’s safe to say that organizations in the USA should be particularly wary of Royal considering their strong focus on that country.
We recommend the organizations across all sectors follow a few best practices to prevent (and recover) from ransomware attacks from every angle. That includes:
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; disable or harden remote access like RDP and VPNs; use endpoint security software that can detect exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Malwarebytes’ EDR anti-ransomware layer constantly monitors endpoint systems and automatically kills processes associated with ransomware activity, including Royal ransomware.
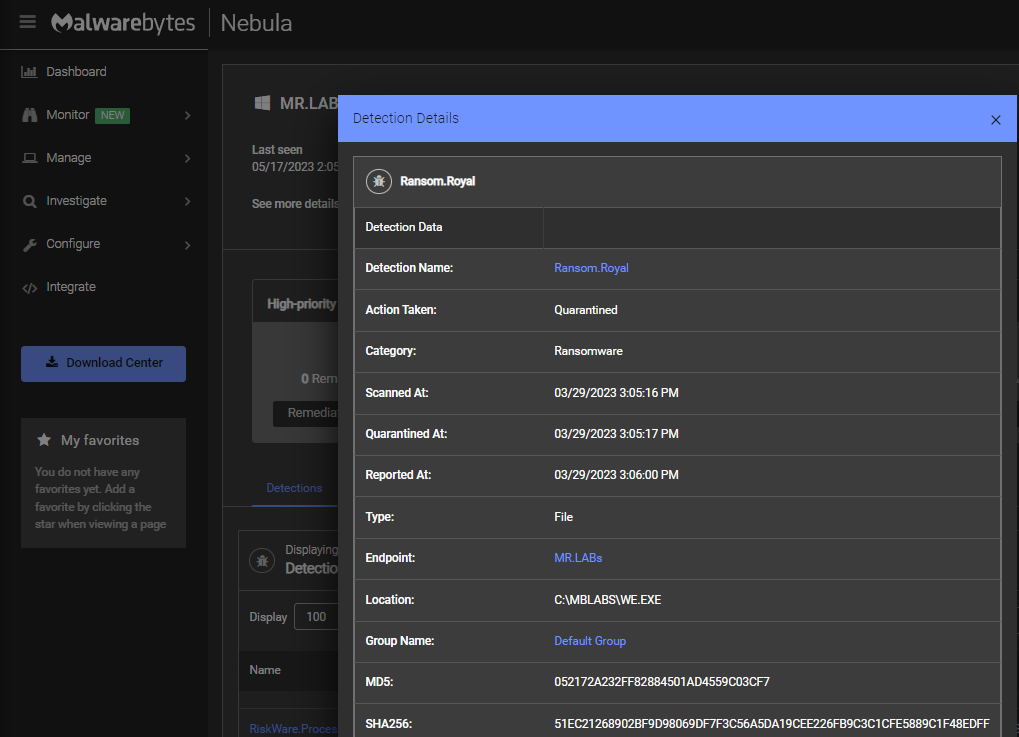
Malwarebytes EDR blocking Royal ransomware On-Execution
In our Ransomware Emergency Kit, you’ll find more tips your organization needs to defend against RaaS gangs.