Spyware.HawkEyeKeylogger
Short bio
Spyware.HawkEyeKeylogger is Malwarebytes’ detection name for a commercial system monitor application distributed by Hawkeye Products. It may have the capabilities to harvest stored credentials, keystrokes, screenshots, network activity, and other information from systems where this software is installed. It may also covertly monitor user behaviour and harvest personally identifiable information including names and passwords, keystrokes from emails, chat programs, websites visited, and financial activity.
Spyware.HawkEyeKeylogger may be able to covertly collect screenshots, video recordings, or it may activate any connected camera or microphone. Collected information may be stored locally and later retrieved, or may be transmitted to an online service or location.
Symptoms
Spyware.HawkEyeKeylogger may run as a start-up entry and may be visible as running processes on compromised machines. Alternatively, this spyware may also be configured in a manner which prevents visible processes and start-up entries.

Type and source of infection
Spyware.HawkEyeKeylogger may be distributed using various methods. This software may be packaged with free online software, or could be disguised as a harmless program and distributed by email. Alternatively, it may be installed by an individual with physical or remote access to the computer.”>
Protection
Malwarebytes protects users from the installation of Spyware.HawkEyeKeylogger.
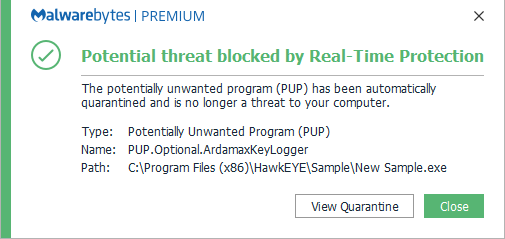
Malwarebytes detects and removes Spyware.HawkEyeKeylogger.
Home remediation
Malwarebytes can detect and remove many Spyware.HawkEyeKeylogger infections without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Spyware.HawkEyeKeylogger with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
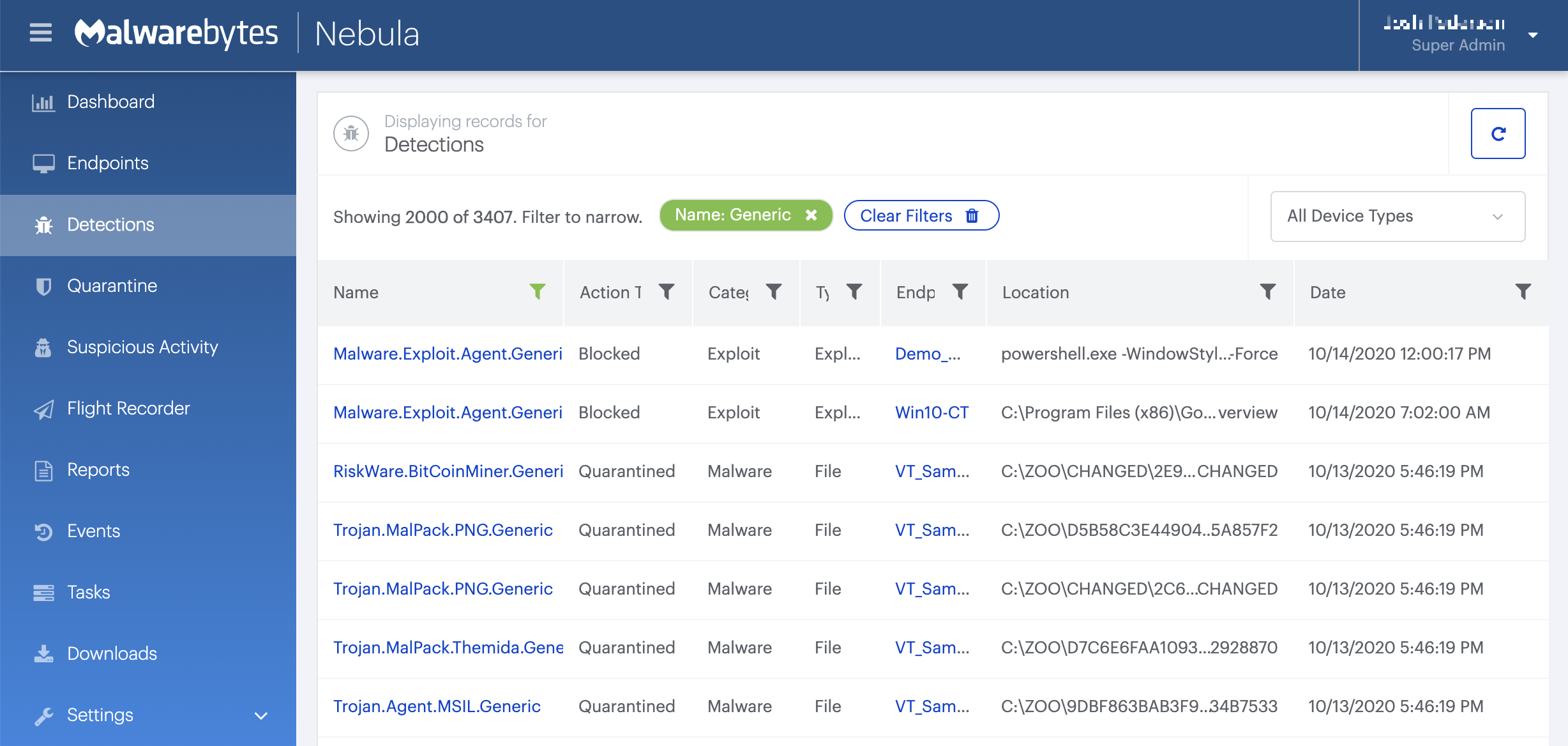
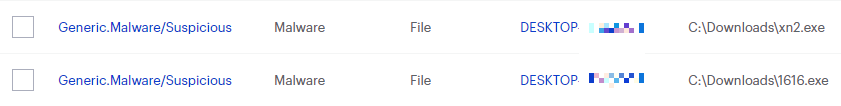
On the Quarantine page you can see which threats were quarantined and restore them if necessary.
Malwarebytes removal log
A Malwarebytes log of removal will look similar to this:
Malwarebytes www.malwarebytes.com
-Log Details- Scan Date: 3/27/18 Scan Time: 12:22 AM Log File: 35f8ee73-3187-11e8-80eb-00ffc8517b86.json Administrator: Yes
-Software Information- Version: 3.4.4.2398 Components Version: 1.0.322 Update Package Version: 1.0.4502 License: Premium
-System Information- OS: Windows 7 Service Pack 1 CPU: x64 File System: NTFS User: DE-WIN7\Fwiplayer
-Scan Summary- Scan Type: Threat Scan Result: Completed Objects Scanned: 296004 Threats Detected: 9 Threats Quarantined: 0 (No malicious items detected) Time Elapsed: 3 min, 4 sec
-Scan Options- Memory: Enabled Startup: Enabled Filesystem: Enabled Archives: Enabled Rootkits: Disabled Heuristics: Enabled PUP: Detect PUM: Detect
-Scan Details- Process: 1 PUP.Optional.ArdamaxKeyLogger.Generic, C:\PROGRAMDATA\XDUSAU\BST.EXE, No Action By User, [7307], [260508],1.0.4502
Module: 1 PUP.Optional.ArdamaxKeyLogger.Generic, C:\PROGRAMDATA\XDUSAU\BST.EXE, No Action By User, [7307], [260508],1.0.4502
Registry Key: 0 (No malicious items detected)
Registry Value: 1 PUP.Optional.ArdamaxKeyLogger.Generic, HKLM\SOFTWARE\WOW6432NODE\MICROSOFT\WINDOWS\CURRENTVERSION\RUN|BST START, No Action By User, [7307], [260508],1.0.4502
Registry Data: 0 (No malicious items detected)
Data Stream: 0 (No malicious items detected)
Folder: 0 (No malicious items detected)
File: 6 PUP.Optional.HawkEye, C:\USERS\FWIPLAYER\DESKTOP\HAWKEYE.LNK, No Action By User, [4609], [245599],1.0.4502 PUP.Optional.ArdamaxKeyLogger.Generic, C:\PROGRAMDATA\XDUSAU\BST.EXE, No Action By User, [7307], [260508],1.0.4502 Spyware.KeyLogger, C:\USERS\FWIPLAYER\APPDATA\ROAMING\Microsoft\Windows\Recent\BST.01.lnk, No Action By User, [3808], [80844],1.0.4502 Spyware.KeyLogger, C:\PROGRAMDATA\XDUSAU\BST.01.EXE, No Action By User, [3808], [80844],1.0.4502 PUP.Optional.ArdamaxKeyLogger, C:\USERS\FWIPLAYER\APPDATA\ROAMING\Microsoft\Windows\Recent\BST.02.lnk, No Action By User, [3611], [86580],1.0.4502 PUP.Optional.ArdamaxKeyLogger, C:\PROGRAMDATA\XDUSAU\BST.02.EXE, No Action By User, [3611], [86580],1.0.4502
Physical Sector: 0 (No malicious items detected)
(end)
Traces/IOCs
You may see these entries in FRST logs: HawkEye (HKLM-x32\…\HawkEye) (Version: – ) () C:\ProgramData\XDUSAU\BST.exe
Associated files:
- Bst.exe
- hawkeyekeylogger.exe





