Spyware.KpotStealer
Short bio
Spyware.KpotStealer is Malwarebytes’ detection name for a family of spyware that steals information from browsers, chat clients, and email clients.
Type and source of infection
Spyware.KpotStealer is often dropped on a system as a payload by droppers or exploit kits. Spyware.KpotStealer is sometimes detected as a Trojan because besides stealing information from several programs like Chrome, Firefox, Skype, Telegram, and Outlook it is also capable of receiving commands from the C&C server.
Protection

Malwarebytes blocks Spyware.KpotStealer
Home remediation
Malwarebytes can detect and remove Spyware.KpotStealer without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Spyware.KpotStealer with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
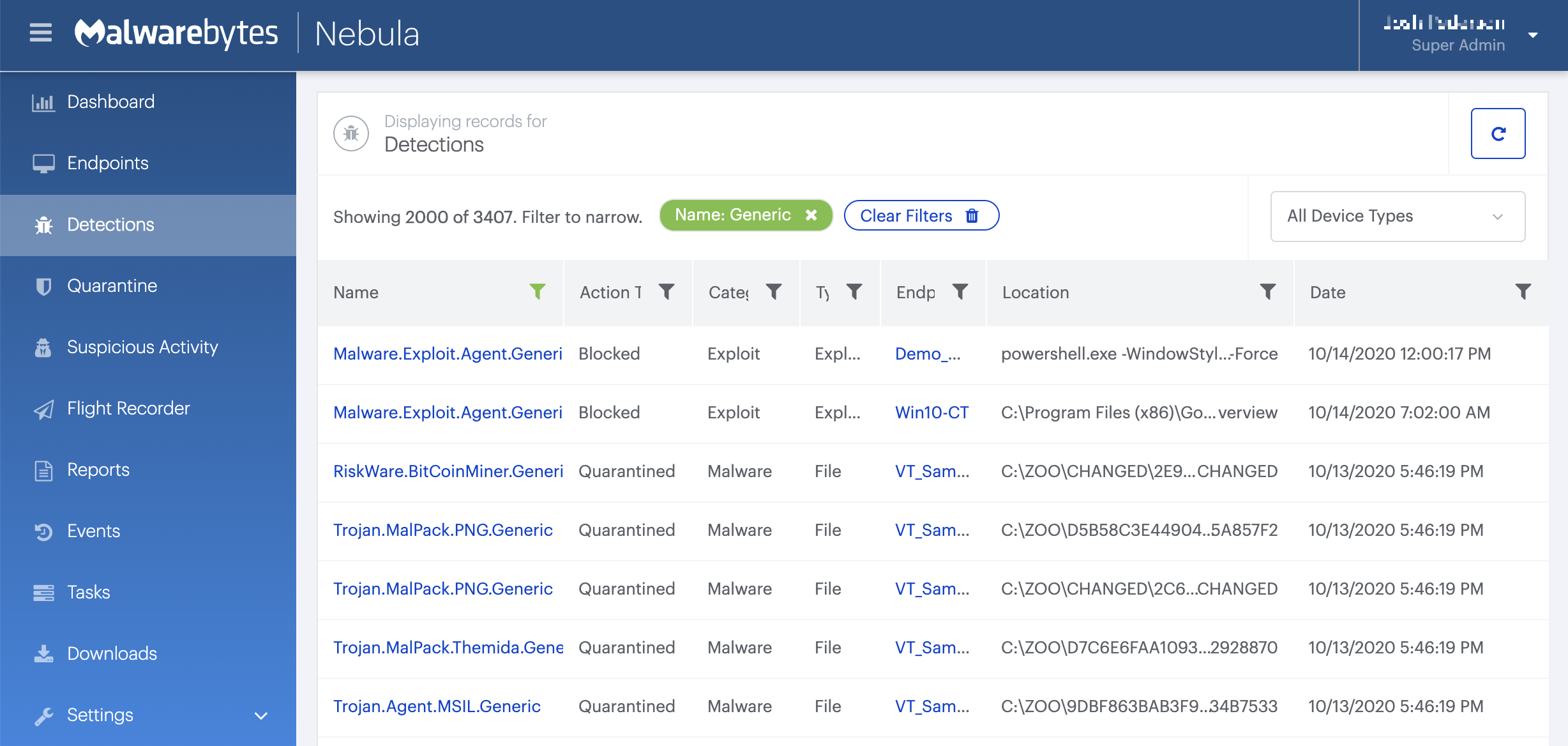
On the Quarantine page you can see which threats were quarantined and restore them if necessary.