An Exploit for Mozilla’s Firefox version 17 is making headlines, not simply because it is a zero-day but mainly because it appears to be part of an operation to uncover the identity of people using the Tor Browser to view child pornography.
Last Saturday, it was reported that the FBI wanted to extradite who they called the ‘largest child-porn dealer on the planet’. The next day, several services offered by the Tor network ceased to exist, prompting many to look into the issue.
It wasn’t too long before malicious code that had been injected in a large number of hidden websites was uncovered. The code was not just your run-of-the-mill exploit, but a Zero-Day that affected a specific version of Firefox, one that happened to be bundled in the Tor Browser.
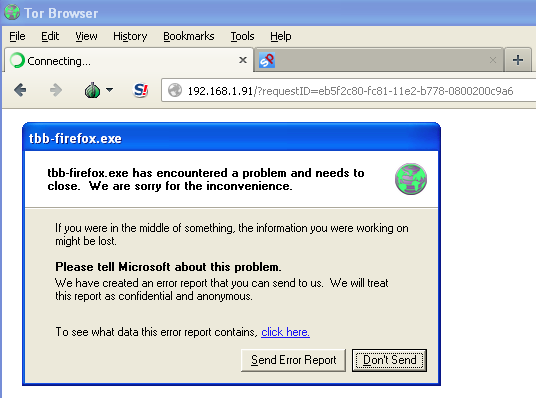
A new exploit delivered on hidden websites which targets the Firefox browser bundled in Tor but not the latest Firefox seems a bit strange.
More clues came after analysis of the shell code revealed that there was no malicious payload to this exploit, but one very distinct feature: a request to a server hosted in the US fetching the victim’s real IP address. Very clever indeed.
If you add all these elements together, this looks like a law enforcement operation, although we might never know for sure.
The Tor Browser is used around the world by all sorts of people who wish to remain anonymous online. In several countries with oppressive regimes, it is the only way for dissidents to browse the Internet freely and not risk going to jail.
Tor bounces your Internet connection over several networks and hides your machine’s real IP address. With an IP address, one can determine your physical location, Internet Service Provider, etc…
The ability to hide one’s identity is something cyber-criminals have cherished for a long time and while Tor can be used for legitimate purposes, unfortunately one cannot prevent it from being abused by malicious actors.
This discovery is likely to spark many debates about the spying programs. While taking down pedophiles should be applauded, does the end justify the means?
What about innocent users that may have been caught in the cross fire and face possible legal consequences for browsing to other ‘legal’ hidden websites that were poisoned with that malicious code? Or security researchers simply studying the exploit code?
Fair enough, the exploit was very targeted and most likely only meant to affect the right kind of people. But what would it take for it to be deployed on regular websites? It could certainly be done.
While this zero-day does not affect users running the latest version of Firefox, many people still are on previous releases. It is only a matter of time before the code is grabbed by malware authors and added to mainstream Exploit Kits.
If you are running Firefox, please update to the latest version.
[Edit] Starting from version 16, Firefox automatically updates itself, unless you have (or malware has) disabled this feature.









