Apple, for the most part, has been able to escape the wrath of malware authors compared with its main competitor, Android.
When talking about malware on iOS, most of the time we hear more about proof-of-concepts getting into the App Store than actual malware.
However, researchers from the Georgia Institute of Technology have discovered a way to circumvent Apple’s “walled gates” and managed to get an app with malicious behaviors past Apple’s review process. Dubbed “Jekyll Apps”, these apps look benign on the surface but contain hidden code revealed at run-time.
Apple’s review process for apps has always been highly praised and the reason for the lack of malware entering their App Store. The app approval process can take up to a few days before receiving feedback, so it’s believed apps are being thoroughly investigated.
The Jekyll apps have three methods of attack and evasion; one involves the use of private APIs, which gives it access to undocumented functionality. Apple frowns upon the use of private APIs in apps published in the App Store, and at times app’s using them are removed.
In the case of Jekyll apps, they get past the review process by using different obfuscation techniques and dynamically loading code. By using these private APIs, the Jekyll apps can gain access to SMS functionality and other confidential data.
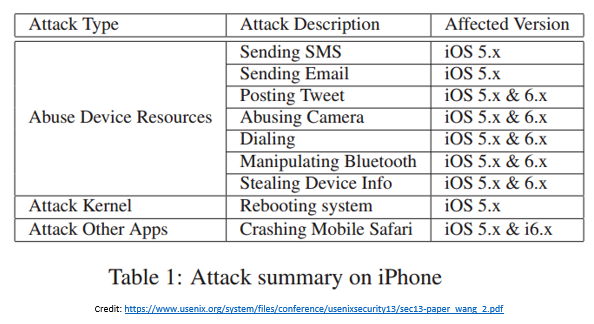
Second, Jekyll apps target vulnerabilities in the kernel such as IOKit drivers. By accessing vulnerable device drivers, the Jekyll apps are able to gain access to even more functionality.
Finally, a Jekyll app can exploit a third-party app and use its functionality as an attack vector. In one scenario the Jekyll app can target Mobile Safari—the native browser for iOS—and is able to exploit URL requests made by third-party apps. 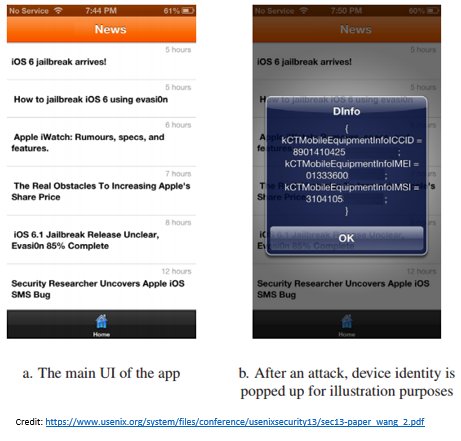
These are some pretty malicious behaviors, fortunately the idea behind the Jekyll app is just a proof-of-concept and was not downloaded by any iOS users.
However, this wouldn’t be the first time the App Store has been infiltrated by a researchers proof-of-concept.
Back in 2011, developer Charlie Miller made news on Apple’s blacklist by publishing a malicious app. His app was able to download and run unsigned code, bypassing Apple’s checks.
Although it seems bad that this malicious app was able to get by Apple’s review process, it’s really a good thing as it points out a weakness in the process where Apple can improve.
Currently, no “real” malware has been found to be using these techniques to access Apple’s App Store. Proof-of-concepts like these can expose weaknesses that malware authors could use, but ultimately it will improve overall security for targeted resources.
When using your mobile devices, stick to trusted sources for apps, and do a little background investigation of your own like reading app and developer reviews when downloading.









