Mt. Gox, the “World’s Largest Bitcoin exchange” might be where you want to go if you’re dabbling in Bitcoin.
However, there are many ways things can go horribly wrong – people with mischief in mind may send you convincing looking (yet entirely fake) URLs, which look like the real thing but aren’t. At that point, everything from phish pages to Malware drive-bys are the order of the day.
Good advice oft-repeated is to type in the URL yourself to ensure you don’t fall victim to shenanigans. However, the caveat here is to always watch out for typos. See if you can spot the sneakily inserted letter in the below URL which turns mtgox(dot)com into something else entirely:
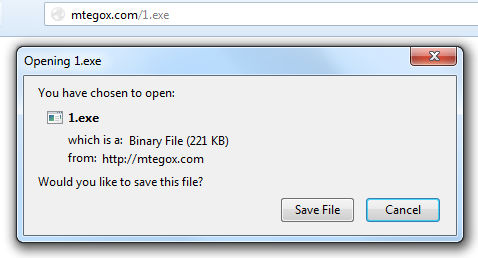
“Mtegox(dot)com”
The site (currently returning server down messages) was a repository of files up to no good, and it would have been all too easy to drive end-users to this particular URL under the pretense of “This file is needed to do x with your Bitcoins”.
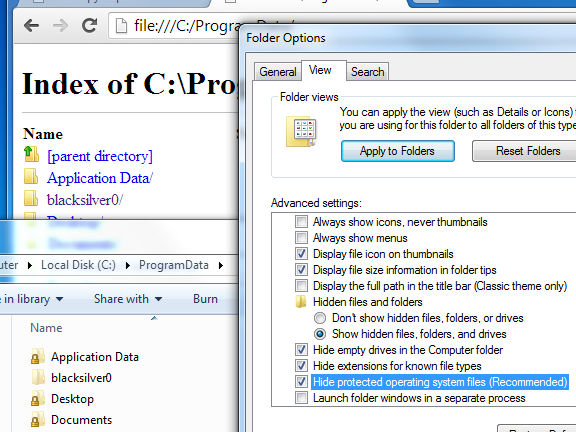
Running the executable deletes the original file, placing additional folders and files into the hidden depths of the infected machine. To see any of the below, you’d need to enable hidden files / folders as visible to see the Program Data folder and untick “hide protected operating system files” to see the folder containing the rogue executable.
That particular foldername shows up in a couple of sandbox reports and other pieces of analysis, including Malwr, a Joe Sandbox report and Lavasoft with the last two referencing a dayzstreaming website offering up yet more files.
Malwarebytes Anti-Malware detects the above as Spyware.Zbot.ED, and it is currently pegged at 39/49 on VirusTotal.
As already mentioned, there were plenty of other files ready and waiting to go to war with your PC from the top of this particular mountain so please be careful with your typing fingers and be sure to double-check any and all “gox” themed URLs sent your way.
One might be down right now, but there could well be many more out there harbouring all sorts of files you’d rather not have running on your system.
Christopher Boyd










