This was the third and final day of the CanSecWest conference. To keep with our weather theme, yes, it did finally rain in Vancouver. But enough of that, let’s get started.
Network Threat Detection Via Machine Learning – Brandon Niemczyk
There are two models for machine learning: discriminative and generative. We don’t know how long network streams are so we need to break them down in small parts by packets or by time. The researchers used DNS to identify malicious agents on a network capturing 7 million unique hosts. They labeled DNS data with known infected hosts if there was a request to a known C2 server or if hosts were trying to resolve a random domain name. The results were that new CnC servers were found and that hosts classified as “probably infected” could now be labeled “infected”.
Exploit Detection – Haifei Li, Chong Xu
Fuzzing is cool but it won’t help to understand the application. We do DNA comparison for similarities. Watering holes attacks are targeting specific environments, certain language packs, etc making them more tricky to detect quickly. Network activities, crashes are strong indicators when checking suspicious documents (PDF, Office). A Big data approach not only helps exploit detection but also benefits advanced security research.
Combating the Advanced Memory Exploitation Techniques: Detecting ROP with Memory Information Leak – Stanley Zhu, Chong Xu
The speakers described two Return-oriented Programming (ROP) exploitation approaches: a statically loaded module base information + ROP, and a memory information leak +ROP. Microsoft’s EMET has ROP detection and Intel has something called ‘Pin tool’. The researchers presented their own approach: to separate valid entries from invalid ones and then try to trap the invalid execution. This is done by copying the .text section of the ROP module to a new memory region, setting the memory attribute of the original .text section to NO_EXECUTE, before finally hooking the INT 0xe and capturing the page fault in kernel mode.
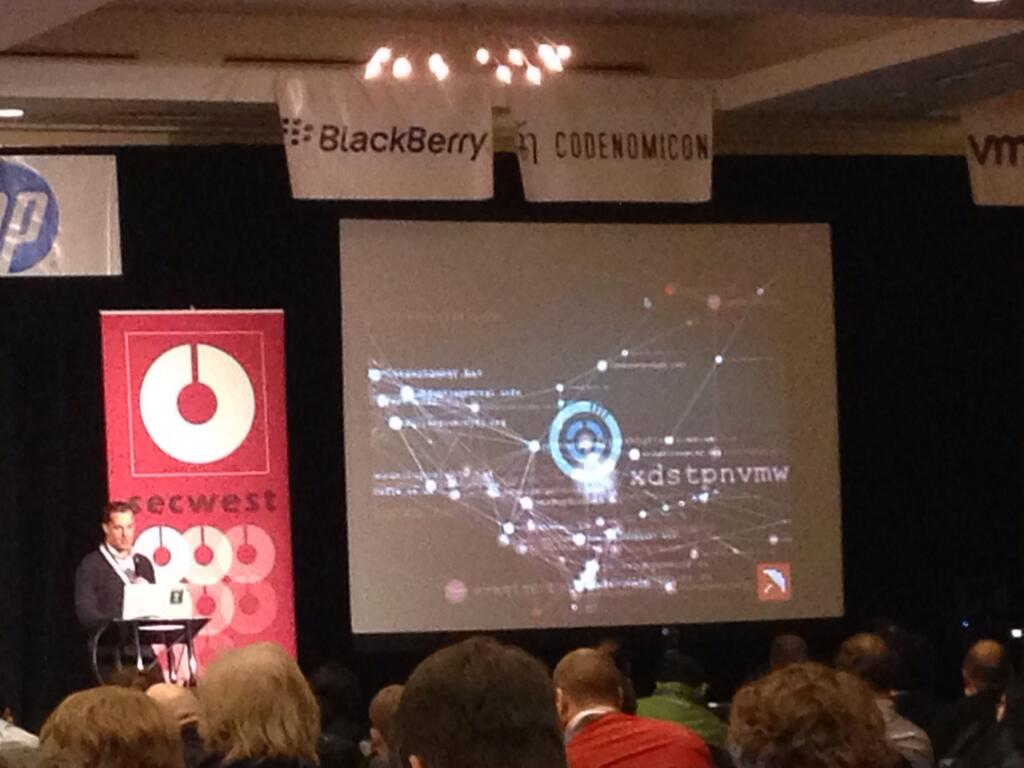
Intelligent Use of Intelligence: Design to Discover – Ping Yan, Thibault Reuille
The speakers introduced a 4-D approach to data: time, space, transactions/network and hunches before showing a pretty cool 3D security graph. The researchers showed how they could analyze clusters of cryptolocker’s domain name algorithm (DGA).
The Art of Leaks: The Return of Heap Feng Shui – Tao Yan
The speaker described the memory structure of an array in jscript9 where one can leak any object address allocated in jscript9. You can read and write the absolute address beyond the int32ArrayBuffer. This can give an attacker the capacity of reading and writing the whole process memory for a leak + ROP. Mitigations include randomization of IE’s custom heap and slicing the big-sized management structure into small pieces.
Outsmarting Bluetooth Smart – Mike Ryan
Bluetooth Smart, Bluetooth Low Energy, BLE are all the same thing. The speaker used gatttool to do some Bluetooth fuzzing on targets then went on to crash the Bluetooth stack on one of his devices.
And that’s it for this 2014 edition of CanSecWest!










