TeslaCrypt is a piece of Ransomware which encrypts your data and locks it behind a “Pay up some serious cash or no files for you” series of messages designed to inspire fear and a liberal slice of money being thrown at the TFT.
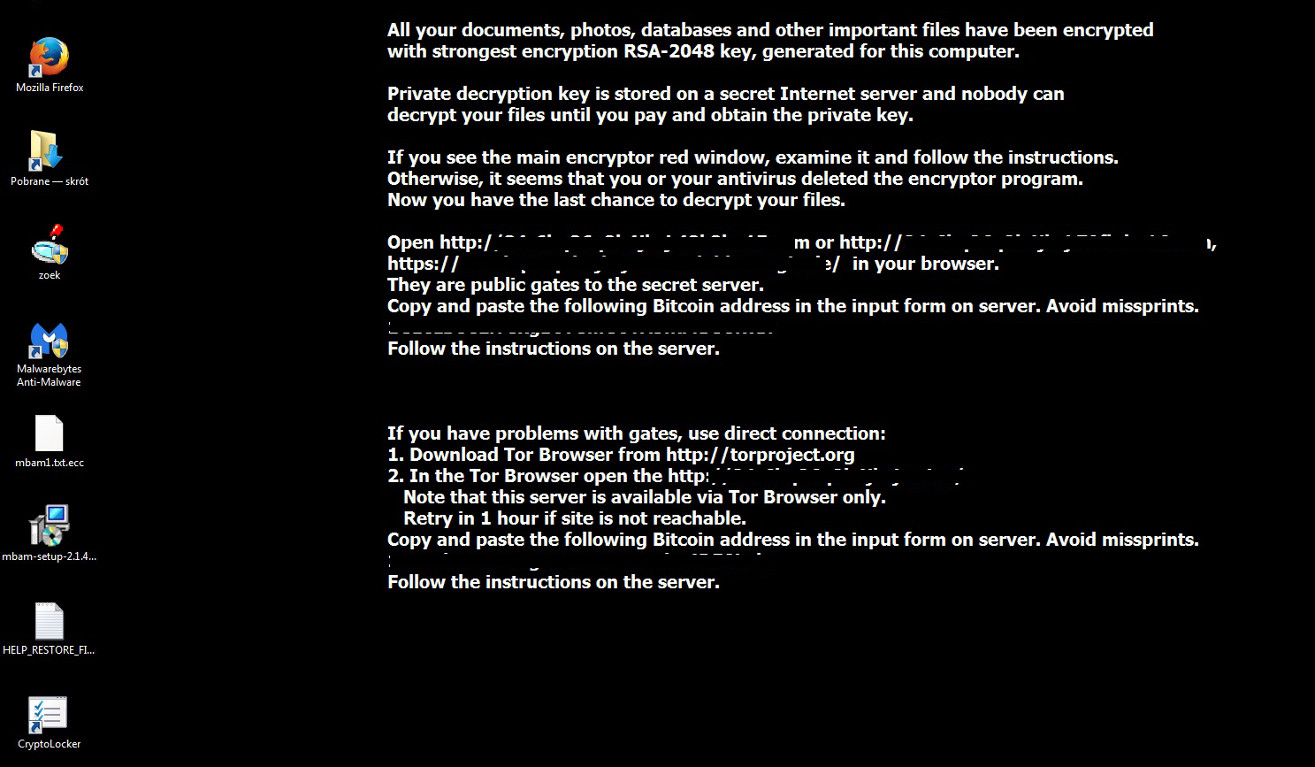
All your documents, photos, databases and other important files have been encrypted with strongest encryption RSA-2048 key, generated forthis computer.
Private decryption key is stored on a secret internet server and nobody can decrypt our files until you pay and obtain the private key. Recently, it's been showing up in malware scams involving Nuclear EK (exploit kit). In the linked example, a Flash exploit targeted an out of date Flash install and bam - that's all she wrote.
Ransomware authors typically go after files they imagine to be most valuable to the PC owners being hijacked - there's always going to be the temptation to pay the scammers if baby photos or crucial tax documents have been locked up behind a paywall. The psychological pressure of the countdown timer certainly isn't going to help matters.
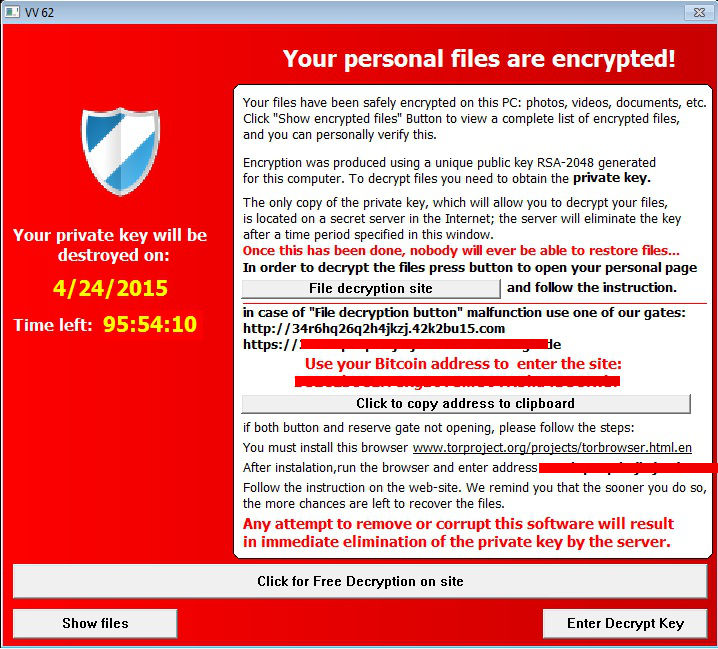
Your private key will be destroyed on: 4/24/2015
Time Left: 95:54:10
Any attempt to remove or corrupt this software will result in immediate elimination of the private key by the server Scary stuff.
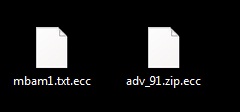
Once on board, all of your files will look like the below, sporting the .ecc file extension which signifies you've been hijacked and unauthorised encryption is now the order of the day:
With TeslaCrypt, the Malware author's brainwave was to start targeting video game files and iTunes alongside the more typical photographs, documents and archives.
However, it appears that the creators of these files may not have quite understood the digital ecosystems they've decided to go after with the latest addition to their "hit list". There's a lengthy list of game titles - both single player and online - which could fall victim to the TeslaCrypt hijack hammer of doom, but in most cases the game files can be restored even if the affected PC owner didn't do any manual backups (important safety tip: ALWAYS do manual backups).
Here, then, is an examination of some of the titles caught up in TeslaCrypt's crosshairs, and what you can do about it should you find yourself affected. Again, we stress that you should be backing your files up anyway - you may be able to get your gamefiles back with little fuss, but all those non-gaming files you have are in danger from lots of forms of Ransomware anyway. With that out of the way:
1. Game platform or standalone?
Your PC games will either be tied to a gaming platform / content distribution system such as Steam / Origin / uPlay, or they'll be standalone efforts. A standalone title used to be a DVD case at the bottom of your bookshelf leading to inevitable "Where is disc 4 of 6 aaargh" type issues. It's not clear if the version of Resident Evil 4 targeted by TeslaCrypt is of the online gaming platform variety, or the ancient "Where is the disc aaargh" variety but any loss involving games and Ransomware all boils down to the game's distribution method.
If we're talking about discs, you're out of luck without manual backups - your save game is gone, but the game files are safe on your disc (assuming you can find it. Try the back of the couch or that novel looking coaster in the front room). If we're talking about the Steam version of Resident Evil 4, then your gamefiles will be gone - but you can redownload them with the push of a button once you're back on a fully functional PC. The savegames will be safe and sound, living in Steam's Steam Cloud.
Got that?
(Old) Physical Media: Gamefiles safe, savegames and customisation (such as mods) gone
Digital Media: Gamefiles gone but redownloadable, customisation (such as mods) gone, savegames (probably) safe
The exception to physical media is that some PC games can still be bought on discs which are just there to provide the gamefiles - you'll still need to register the game to an online service such as Steam, and / or a publisher specific service such as RockStar Social Club.
You're going to ask me about that "Probably" now, aren't you?
2. The Problem of "Probably"
Many game platforms enable cloud saving for games because lots of people tend to move between machines while playing (you might want to go from desktop to laptop while on a trip, for example). It's just less fuss than messing about with USB sticks and trying to find the occasionally obscure save game location jammed in the AppDataLocal folder.
We already know Steam does this, and you can find out which titles use the feature with a simple search:

3,616 entries listed under Steamcloud. Steam has around 4,500 games on the service currently, so there's a good chance you'll be playing something with it enabled.
Origin does cloudsaves too, as does Uplay. The only major exception to this is the DRM free Gog.com, which sells titles as standalone digital games not connected to a platform. This means no cloudsave functionality, however they do have a platform in the works so it might be available in the near future.
Now that we've looked at what's likely to be at stake depending on how you're installing your games and which platform you're on (if any), let's look a few example titles which have been named in relation to this threat. For simplicity's sake, we'll assume all games mentioned are digital download versions only - no CDs, because you're going to have to be backing up those saves manually in that case anyway.
Take Call of Duty, a typical title on Steam targeted by TeslaCrypt. This could get confusing fast as there are lots of CoD games on digital release, and there's no additional information with regards which CoD games are targeted. With that in mind: Call of Duty Ghosts 1 & 2, Advanced Warfare and Modern Warfare 2 & 3 all make use of Steam Cloud. It's the same deal for other games on Steam currently under attack - some have Steam Cloud support (Metro 2033, Saints Row 2), some don't (Bioshock 2, F.E.A.R).
In all cases, you'll be able to redownload your gamefiles & saves through a combination of the Steam platform itself and backing up your files manually for non-cloud supported titles.
Half-Life 2 and Valve created games in general are also going to live to fight another day as any game made by Valve supports Steam cloud saves.
3. Mods and other Add-ons
There's a huge amount of ways to make alterations to PC games via the art of Modding, but thankfully the solution to lost mods is pretty straightforward. If you're using mods for a game directly from Steam Workshop, you can just redownload through Steam. Otherwise, you're probably getting your mods from Nexus - same deal applies. If you didn't have a specific mod backed up manually and the creator pulled it offline while you were fighting against a hijack then sorry - unless they reupload it you won't be able to get it back. In terms of moddable games under attack from Teslacrypt, the main singleplayer titles are the following and they tend to have varying quirks and oddities which you'll need to account for:
Fallout 3 - This one has no cloud support on Steam. Given that the game can last 100+ hours, it's a good idea to be backing up saves anyway due to their occasional habit of corrupting and breaking the game.
Dragon Age: Origins - A bit of a weird one. There's no cloud save for this on Steam. On Origin, the Dragon Age games used to have cloud saves (well, at least one of them did) but according to that thread the functionality was removed in preparation for the release of Dragon Age 3. Yet another "hundreds of hours of my life have vanished" title, so manual backups should be applied here.
Skyrim - Uses Steam cloud for saves, so that plus easy mod availability will work in your favour. I guess you really don't mess with the Dragonborn.
5. MMORPGs (Massively Multiplayer Online Role-Playing Games)
A lot of MMORPGs are TeslaCrypt targets, from WarCraft 3 to DayZ (another Steam title) and League of Legends. Many of these games tend to save your general progress in the cloud, but not your specific saves (ie progress in a particular mission). I'm not getting into debates over whether Minecraft is a MMORPG, but as with the other titles where progress isn't saved in the cloud a common solution is to sync with cloud services.
6. Development Tools
Anybody spending a lot of time working with Unreal Engine or Unity3D may well already be backing up their files, but you never know. Losing hundreds of hours on an important project which gets hijacked by Teslacrypt isn't going to make your boss feel like going on a coffee run anytime soon, so you should probably start reading up on backing up UE and Unity. Losing game data is frustrating for sure, but there could be real financial impact by losing access to content made with these programs.
If you're still not sure what to do in terms of manually setting up cloud saves via storage services, consider trying the popular GameSave Manager program. It works with both FTP services and many cloud providers.
Conclusion
Scammers trying out new things is always going to be a cause for concern, especially if they come up with something particularly inventive or deadly. Here, it looks like a case of "Trying it because we can" in relation to the game files targeted. By the same token, TeslaCrypt goes after iTunes - which, should disaster strike, is just a case of redownloading MP3 files permanently tied to your iTunes account. An inconvenience, to be sure - but not quite the same as "All my work documents and wedding photos and the last 3 years of my life which I intended to backup but never did have just gone up in smoke."
Which, by the way, this piece of Malware can do. So don't get complacent! Whether we're talking games, music, word documents or important photographs in relation to fire, theft, hijack or blown hard drive the end result is the same - hours of time wasted as you (hopefully) check your last backup to see what you didn't get around to copying. Backing up your files is one of the best things you can possibly do alongside having layers of protection on your PC.
Get into the habit now - you'll be glad you did if something goes wrong further down the line.
Christopher Boyd (Thanks to Radek for the screenshots)










