It may well be National Cyber Security Awareness Month, but no matter who you are things can still go wrong in the blink of an eye. Namely, the following Tweet from Essex Police using the #cyberaware hashtag:
The Tweet read as follows:
Be #cyberaware if you shop and bank online - make sure the site's url has 'http://' to protect your data. More here [goo.gl URL]
Shortly after the Tweet was posted, they took it down and followed up with this:
Had they been compromised, or did someone fall asleep at the Twitter wheel? Examining the now deleted missive reveals some definite weirdness here. For starters, it says “http://” will protect your data. This is incorrect – one assumes they forgot to include the “s” at the end of http. Or perhaps whoever posted this Tweet was up to a bit of mischief with a splash of intentionally incorrect advice, assuming they had been hijacked?
Either way, the shortened URL attached to the Tweet is where things become very peculiar. First off: the Goo.gl link was created way back in 2011 – this isn’t something that’s been put together specifically for the occasion of pranking a law enforcement feed.

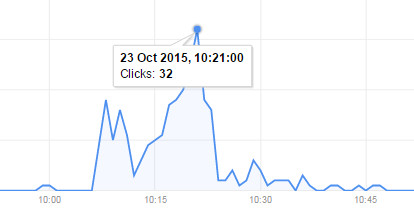
We have a not-so-grand total of 342 clicks since the link was created – and in terms of clicks today, the tally appears to be rather low. I’m not 100% sure of the time the Tweet went out, but if we assume around 10AM, even by half past there’s only been about 30 something clicks at peak clicking time.
Of course, one would argue that even one click is one click too many which is a fair point.
As for the content of the site itself? It’s a redirect which starts with
goo(dot)gl/zNVzg
then
nursing(dot)buybooksales(dot)com/nursing-now-todays-issues-tomorrows-trends-3/?1297072224/
From there, we’re taken to…
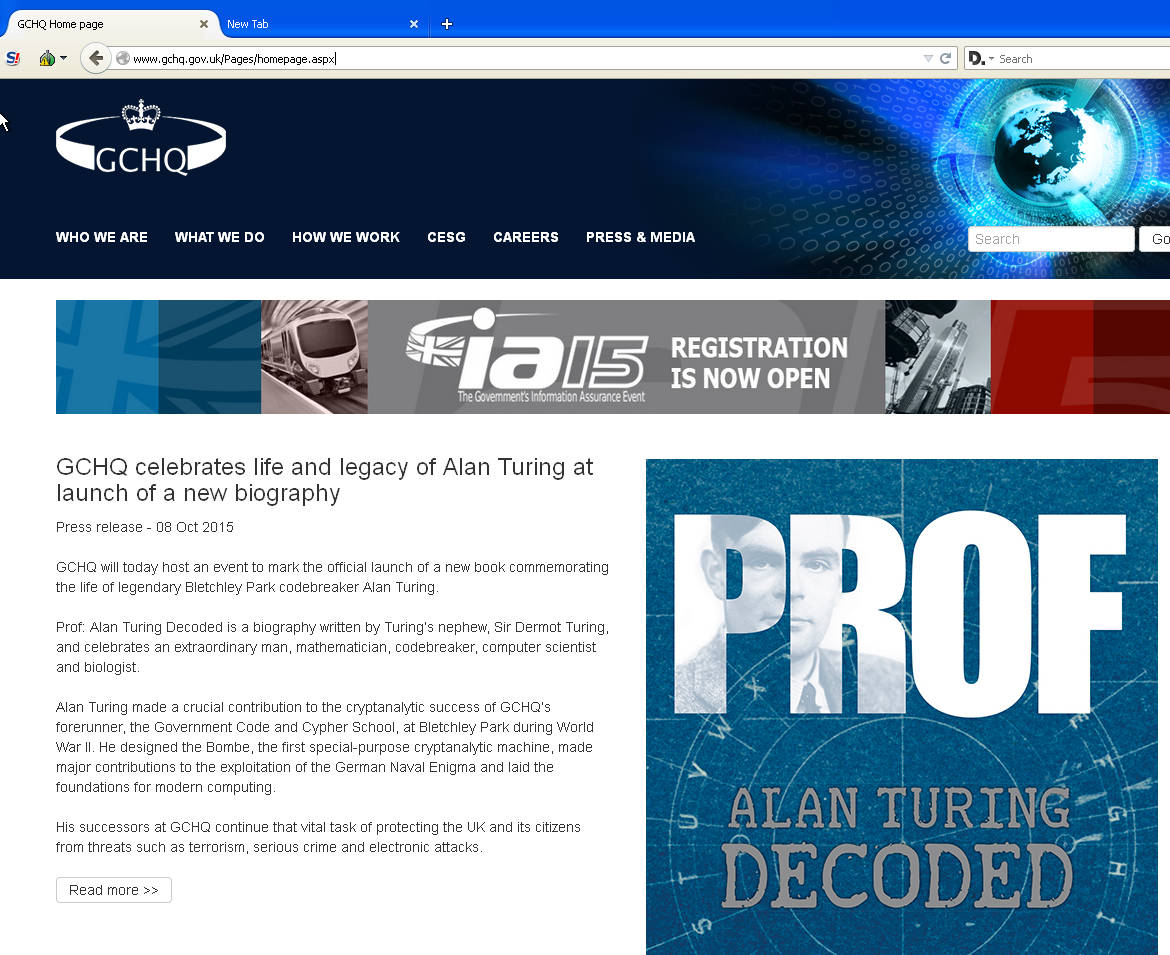
…the official GCHQ website?!
Well, that’s different. And most certainly not “Malicious”.
Elaborate prank? Peculiar stealth recruitment test? I’ve no idea. It’s possible that the original redirect URL pointed to other sites which may well have been malicious and has since been aimed at the GCHQ link for a bit of a giggle. We’ll continue to dig into the details and update this post with any fresh information.
Christopher Boyd










