Author’s Note: We at Malwarebytes continue to do our part in educating our product users and constant blog readers about day-to-day online threats and how they can avoid falling prey to them. “PUP Friday”, our latest attempt at getting users acquainted with files they may need to watch out for in the Wild Web, offers an in-depth look at some interesting and quite notable potentially unwanted programs (PUPs). Expect to see this type of content pushed out twice a month at the end of a work week.
Looking at the latest Yontoo browser hijackers leads us to believe that they have shifted their interest from Firefox to Chrome.
We have discussed Yontoo before as a PUP that has two faces. The official installer used to target Firefox and Internet Explorer. Now they have shifted to Chrome. A few in between have been doing both Chrome and Firefox, but were less intrusive towards Chrome. More precisely, they did not change the Start- and Home-page.
Why the change?
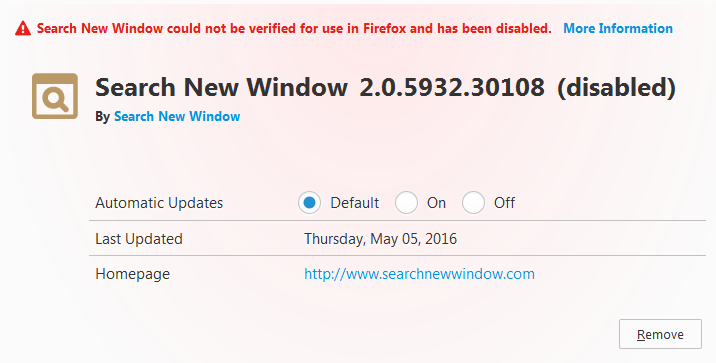
Of course we can only guess, but a good reason seems to be the fact that Firefox started disabling their browser Extensions as they could not be verified. So maybe we can chalk this one down as a victory for those guidelines.
I guess even if their extensions would make it through the guidelines required by Firefox, it would take too much time and energy to do this for all the new versions that Yontoo keeps putting out there. Why they apparently have stopped targeting Internet Explorer is a mystery to us at this point in time. Maybe they are planning a similar move to target Edge with newer variants.
What does it do to Chrome?
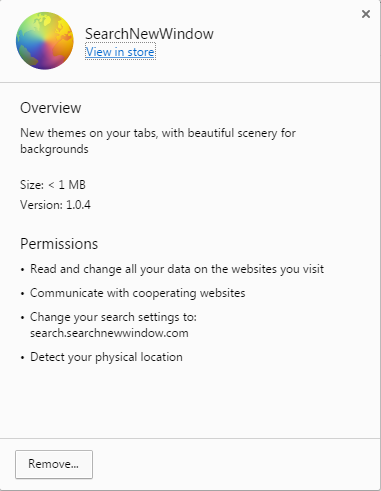
These are the permissions that the new version gets.
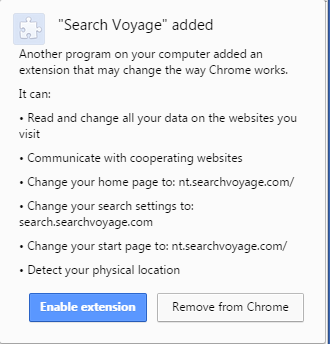
The hybrid versions that targeted both Chrome and Firefox were a little less intrusive as they did not change the Start- and Home-page in Chrome.
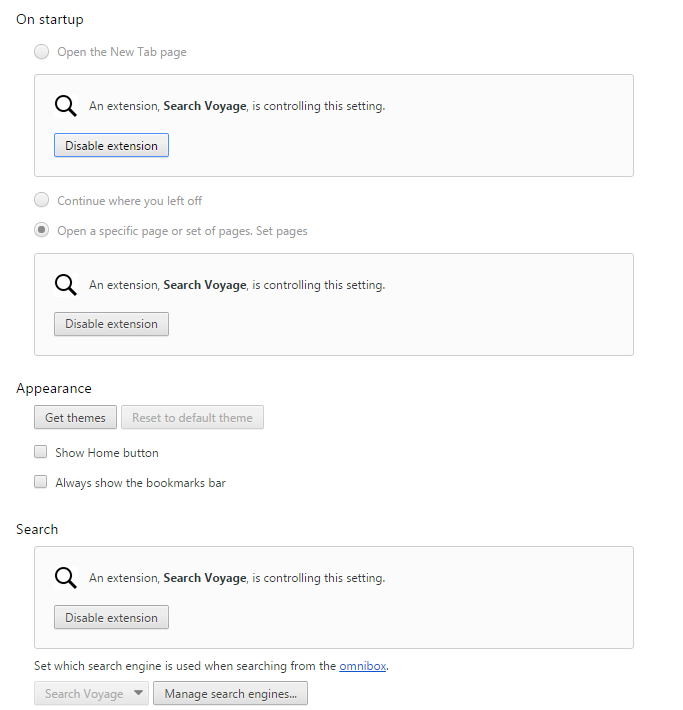
Besides changing these settings the Yontoo extensions also control several settings for Chrome until you disable the extension.
Summary
We took a closer look at the new versions of the Yontoo browser hijackers and took a stab at guessing why they made the switch from Firefox to Chrome.
Extra file information
Md5 Search New Window installer 1f9ec8189ce7a8e0b1057b518714ccca
Md5 Tide Search installer 4cdff17f8ab9b8056ecdcef35bdd26db
Md5 Search Voyage installer 89e2b736e401f53e3159b046b4b46ace
Links
In our removal guides you can find additional screen-shots and logs showing the added files, folders and registry keys.
New versions:
removal guide for Search Voyage
The hybrid version we used as an example:
removal guide for Search New Window
As always: Save yourself the hassle and get protected.
Pieter Arntz











