DNSSEC is short for Domain Name System Security Extensions. It is a set of extensions that add extra security to the DNS protocol. This is done by enabling the validation of DNS requests, which is specifically effective against DNS spoofing attacks. DNSSEC provides the DNS records with a digital signature, so the resolver can check if the content is authentic.
The reason for this post was the recent SIDN report that concluded that the DNSSEC security status in the Netherlands left a lot to be desired. To name a few, the banking sector and the ISPs were lagging behind. Especially compared to the government sector, which has to be fully compliant by the end of 2017 and is now at a level of 59% of all domain names to be cryptographically secured and signed.
Background of the report
Included in the investigation were only .nl domains, so companies of a more international nature, that might be using other Top Level Domains (TLDs) were not included in the research. Let’s hope that companies of this nature are more advanced in this regard. On a grand total of approximately 5.7 million domains 46% were signed.
Additional security
Not only is DNSSEC a security feature by itself, it also provides a platform for additional features like:
- DKIM (DomainKeys Identified Mail)
- SPF (Sender Policy Framework)
- DMARC (Domain-based Message Authentication, Reporting and Conformance)
- DANE (DNS-based Authentication of Named Entities)
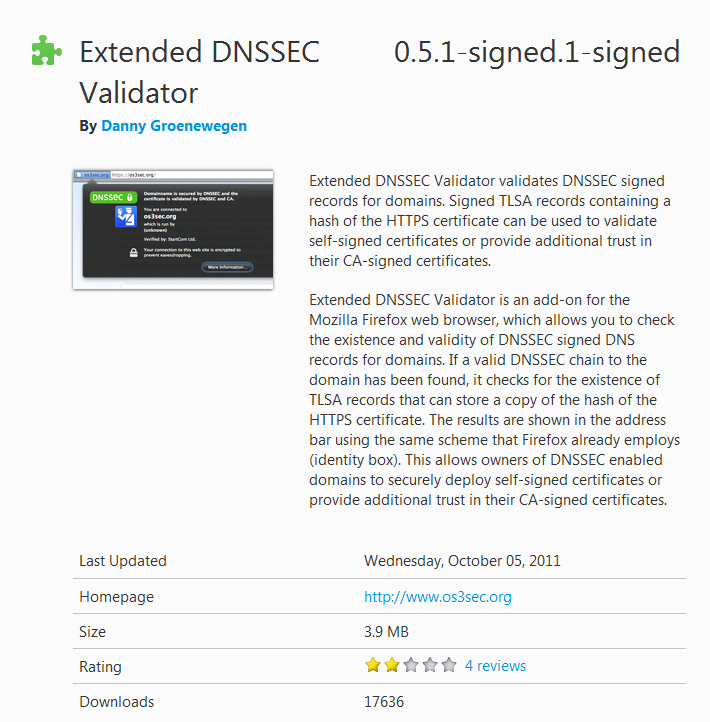
Especially DANE, which is a protocol that allows Transport Layer Security (TLS) certificates to be bound to Domain Name System (DNS) names, is considered a major step forward in security after some certificate authorities (CA) providers have been breached and any CA could issue a certificate for any domain name. This is why we say that the green padlock is required, but not enough. Going forward it’s important to know that all the popular browsers support DNSSEC and most of them support DANE (for some browsers you may need a plug-in), so implementation of this extra security should put a major dent in the possibilities for DNS spoofing.
Major conclusions of the report
Personally I was surprised, almost shocked, to find out that only 6% of the banking sites had their domains signed, the worst of all the investigated groups of domains. Especially worrying as the move from physical to on-line banking has been progressing steadily in recent times. The percentage for all financial corporations was at 16%. Other sectors where we would expect better figures:- ISPs (Internet Service Providers) 22%
- Stock exchange listed companies 12%
- Internet shops 30%
- Telecom providers 33% and worst of all, of the 4 biggest providers with an .nl domain, none contributed to that score.
So, even though the number of signed domain names has grown considerably over the past two and a half years (the previous report on this subject), some sectors are heavily lagging behind, and in particular some sectors where we would hope and expect otherwise.
Your country
If you have any similar figures about these numbers in your country, let me know in the comments. I would like to make some comparisons.
Pieter Arntz