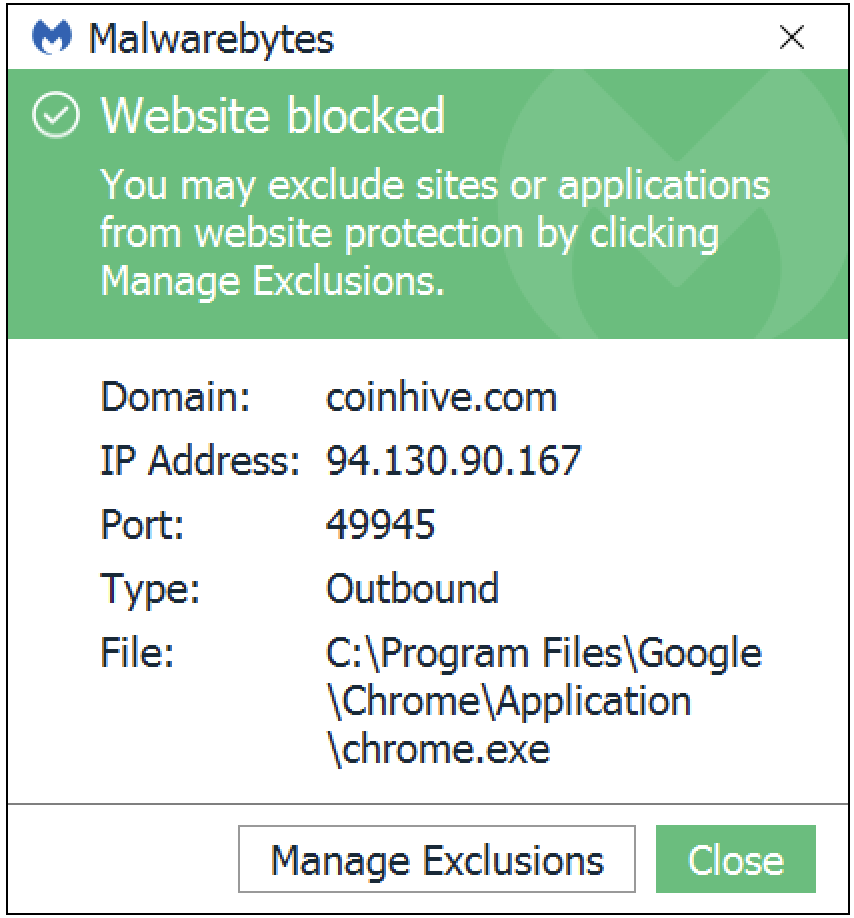
If you’ve encountered a Malwarebytes web protection block for coinhive.com over the last few weeks, you are either glad about it, angry about it, or don’t really care.
Since September 19, the second-most frequently blocked website for our customers has been Coinhive, a website that provides users with cryptocurrency miners they can deploy on their own sites. When we observe an immense amount of blocking—in this case, over 130 million blocks in a few weeks—we try to explain why we do so.
In this post, we’ll describe what Coinhive is and what it’s doing to merit blocking. Lastly, we’ll tell you how to exclude coinhive.com from being blocked by Malwarebytes, if you decide to do so.
What is cryptocurrency mining?
Do you remember when Bitcoin (BTC) first came out? It was under the radar for a while. Mainly, hobbyists and folks involved in the development of the cryptocurrency paid attention to it. After a few years, Bitcoin has become more and more popular, leading to the emergence of an army of Bitcoin miners. “Miner” is generally a term used to describe software or hardware used to crunch numbers in order to earn a small share of cryptocurrency. At times, “miner” can also be used to describe the person who is doing the cryptocurrency mining.
As the popularity of Bitcoin increased, so did the number of people who got involved in BTC mining, which resulted in a bit of a mixed bag of technologies being created, distributed, and (in some cases) forced to install. A person with the intent and means can run dedicated BTC miners, collect their share until a decent amount has been accumulated, and then exchange the coins for goods, services, or government-backed money.
Cryptocurrency miners, or cryptominers, are highly resource intensive. This is because they ask the system to quickly conduct immense calculations it probably wasn’t designed to do. This is fine if you have the hardware for it, but if you are running a 10-year-old system you bought off the shelf, it can not only decrease the speed and efficiency of your system, but even damage the hardware.
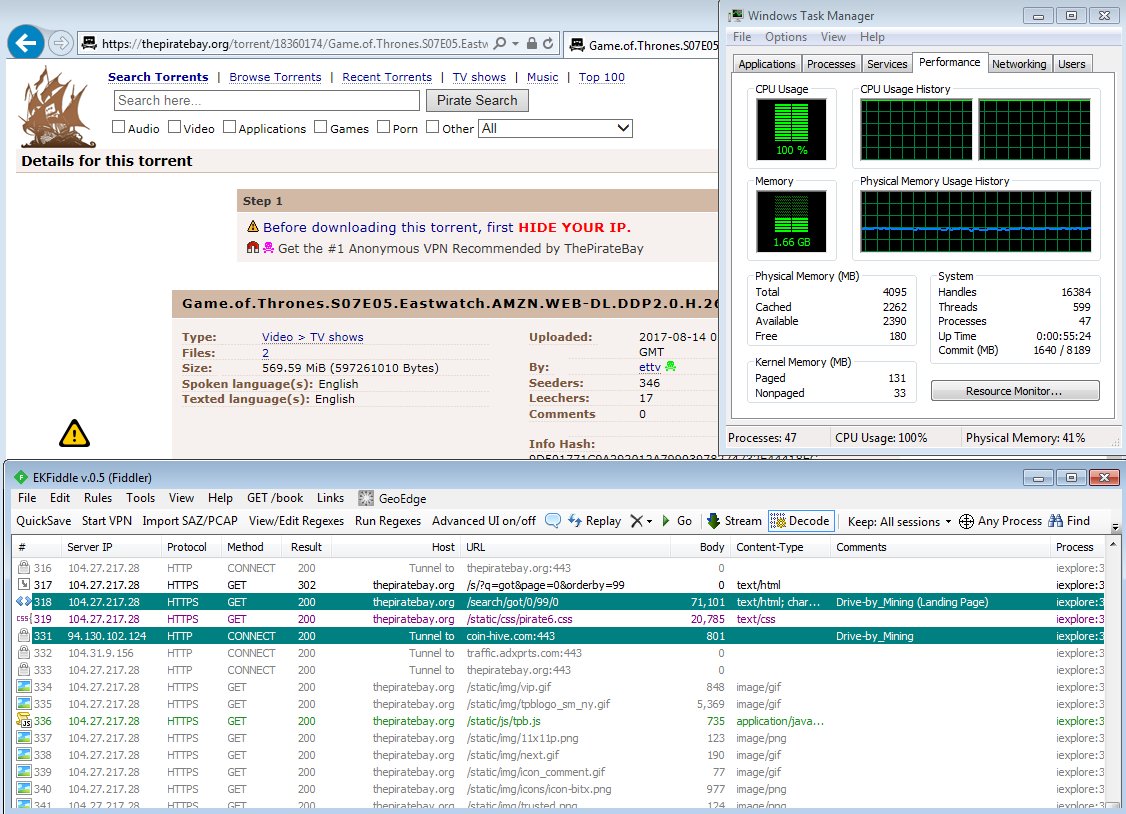
Miner running on system while visiting The Pirate Bay. Notice the 100 percent CPU usage.
Over the last few months, we’ve observed that miners are now included with sketchy software and malware to make more money for their creators. Bitcoin exchange rates have skyrocketed, and the amount of money that can be earned by mining BTC is incredibly low. Because of this, new cryptocurrencies have popped up—thousands of them! According to Mashable, Bitcoin ranks first in their list of most popular cryptocurrencies. The other most popular coins are:
- Ethereum
- Litecoin
- ZCash/Monero
- EOS/Cardano/Bancor
- Tezos
While these are the most promising for future development and integration into mainstream payment methods, they are also the most vulnerable, because there has been heavy investment in their growth. It is no surprise then that more than one of these cryptocurrencies have had miners put in places they didn’t belong.
What is Coinhive?
Coinhive is a service that provides cryptocurrency miners you can deploy on your website using JavaScript. The coin of this particular realm is Monero, and it totes the claim that using JavaScript miners is an alternative to advertising revenue.
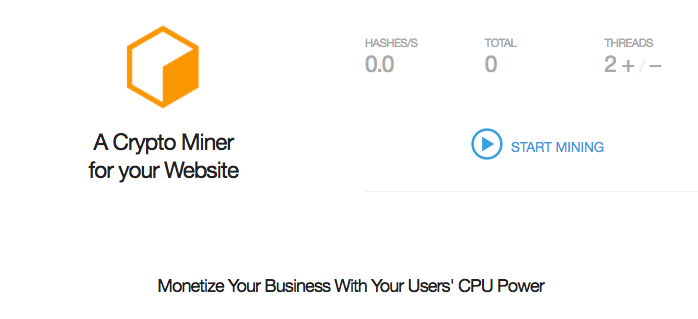
Coinhive offers API access for website owners to deploy a miner on their site, have it communicate with the Coinhive remote server and, unfortunately, allow the miners to be run on user systems without their knowledge or permission.
Why are we blocking it?
We do not claim that Coinhive itself is malicious. The concept of allowing website owners to use an alternative to advertising in order to make a profit is a noble one, especially since ads have been plagued by everything from fake news to malvertising. The execution of it is another story.
The reason we block Coinhive is because there are site owners who abuse this service by refusing to ask for their users’ permission to start running CPU-gorging applications on their systems. A regular Bitcoin miner could barely make a dent in CPU—or it could suck up processing power like an industrial space vacuum.
The JavaScript version of a miner allows customization of how much mining to do per user system, but leaves that up to the site owner, who may end up slowing down your computer experience to a crawl in order to squeeze out every drop of coin in the cyber bucket.
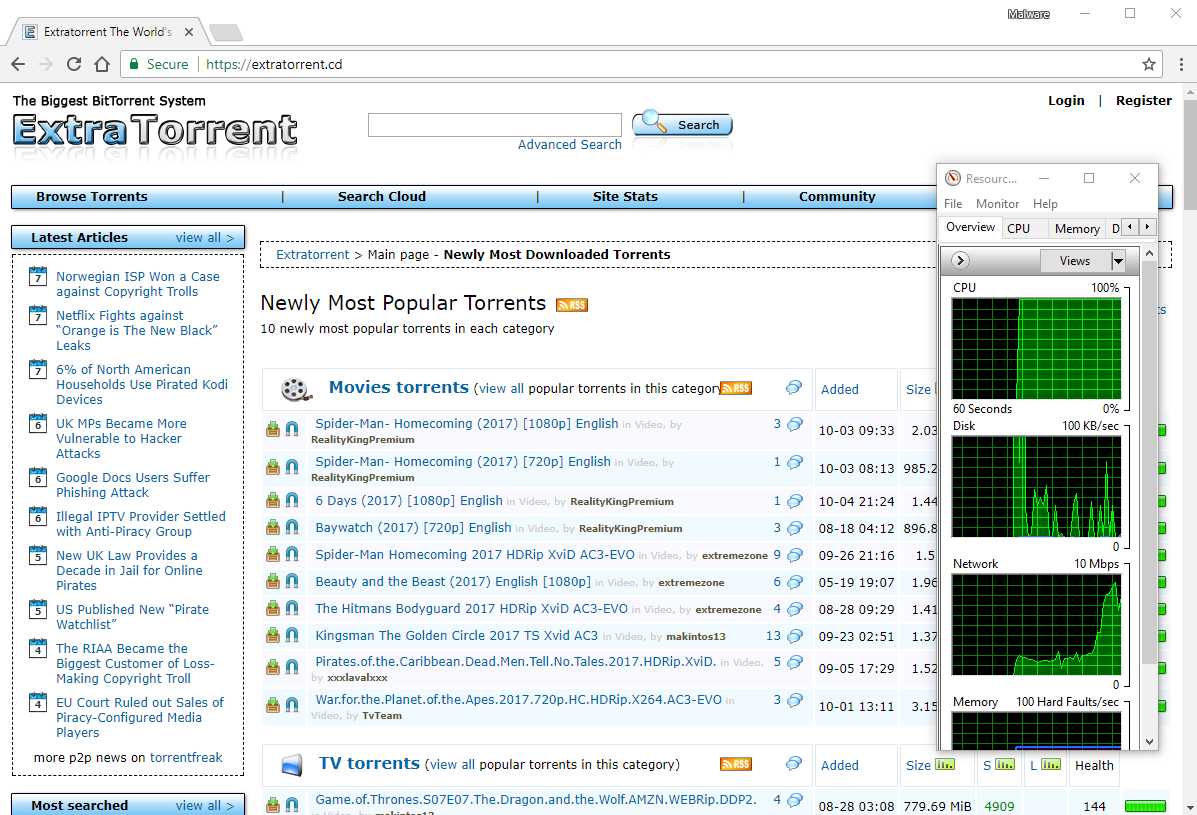
Another torrent site running a Monero miner in the background.
We block Coinhive so that greedy website owners cannot abuse the technology in order to jack egregious amounts of CPU from unaware and otherwise less informed users.
How to add an exception
At Malwarebytes, we want to arm our users with knowledge about threats and the tools to protect themselves from those threats. However, we are not in the business of censoring or restricting access to something people want to use. For cases like Coinhive, it’s a grey area: Yes, it can be abused, but those that know about cryptocurrency miners and wish to use them responsibly may want access to this technology.
So in addition to telling you why we block this site and the danger associated with it, we will also tell you exactly how to get around our block.
Step 1: Go to the Exclusion tab
In Malwarebytes for Windows, there is a tab for exclusions in the Settings area. You can navigate there manually or, after trying to reach coinhive.com (and getting a notification from us), you can just click the Manage Exclusions button at the bottom of the notification.
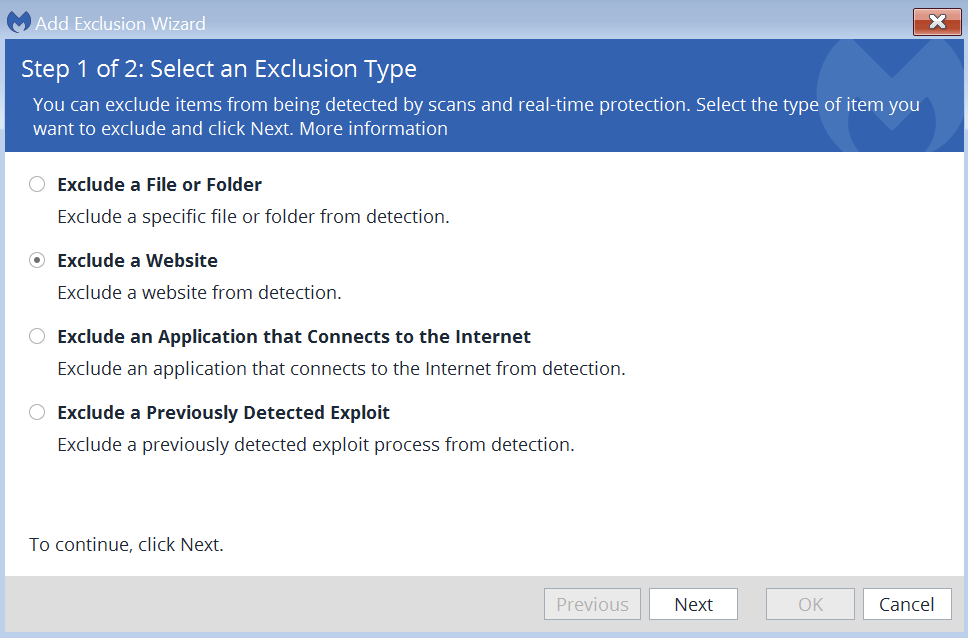
Step 2: Select exclusion type
Your next step is to select what kind of exclusion you want to make. You’ll be able to allow anything from applications to websites, and even previously-detected exploits. In the case of Coinhive, click the Exclude a Website radio button and press Next.
Step 3: Add the exclusion
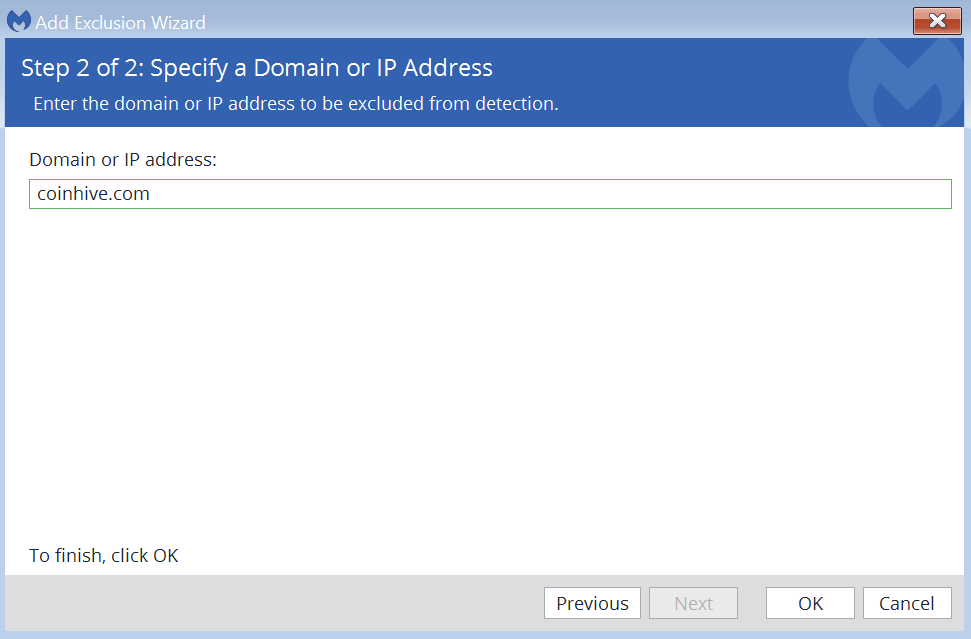
Finally, Malwarebytes will ask you the website URL or IP address of the site you want to exclude. For Coinhive, you need to exclude its website URL—coinhive.com—and its IP address—94.130.90.152.
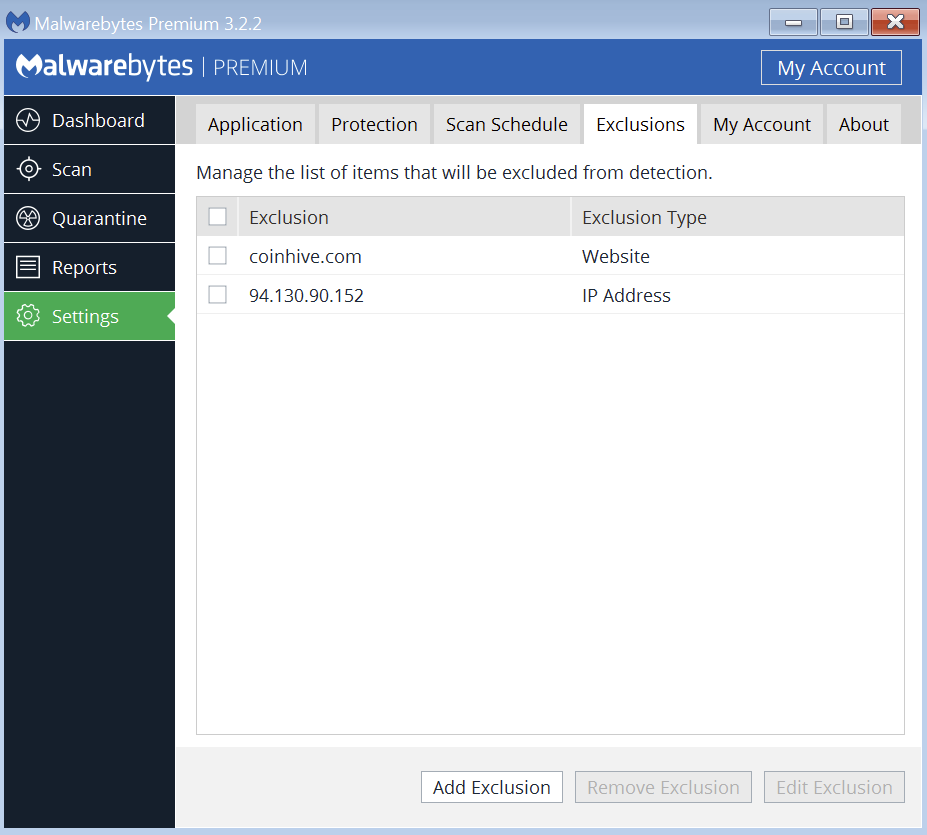
After you complete adding the exclusion, your exclusion list in the Malwarebytes interface should look like this:
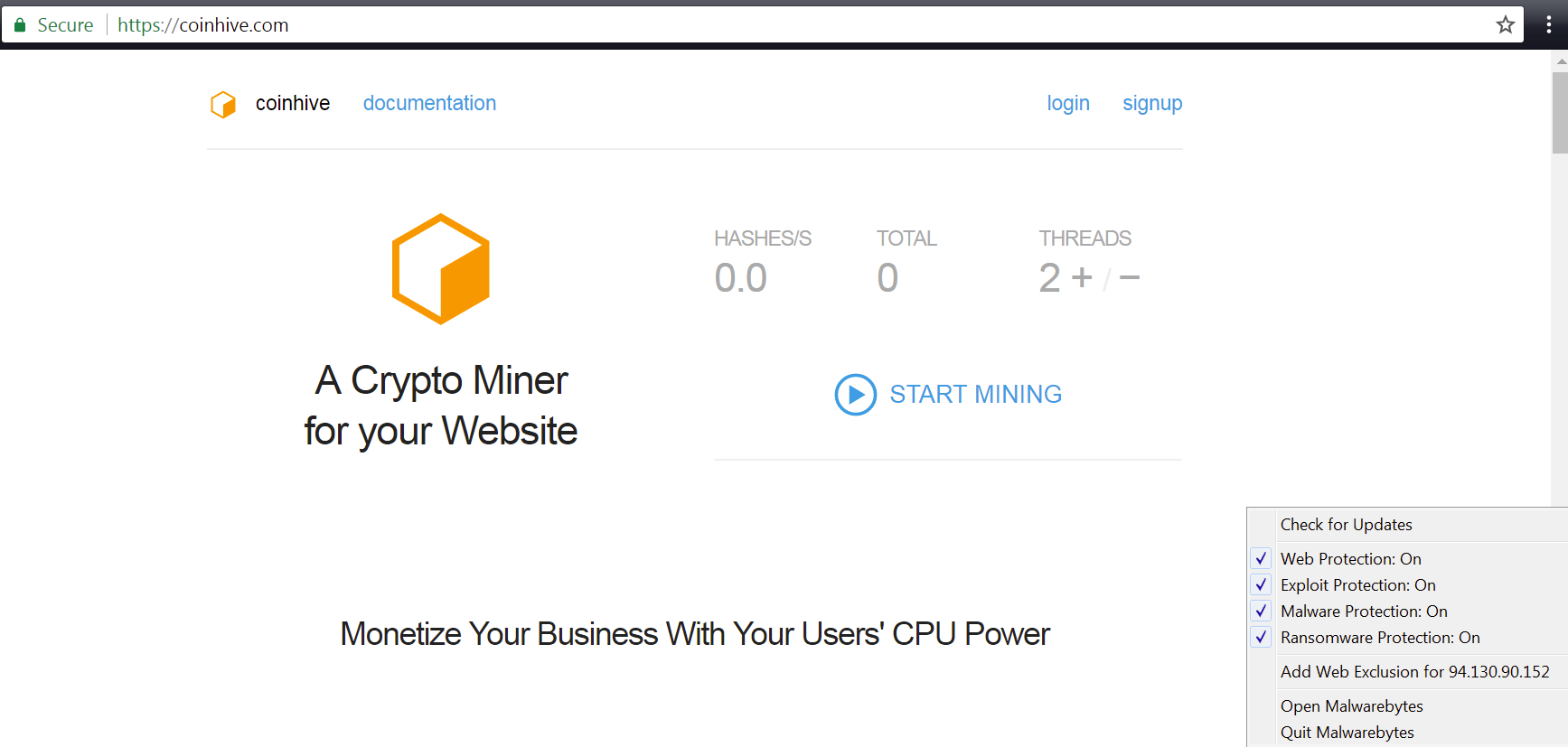
Step 4: Test to see if it worked
Your final step is to navigate to coinhive.com and make sure it’s no longer blocked. If it is, go back in to your Exclusions list and make sure you entered the URL and the IP address correctly. (I tested this myself and it works.) If you’ve done everything correctly, you should be able to navigate to the Coinhive website and use the miners without a problem, even with full Malwarebytes protection enabled.
For more information about adding exclusions to your instance of Malwarebytes for Windows, please check out this Knowledge Base article that guides you through every type of exclusion.
We hope some of you who were upset about our detection will now understand why we decided to block this and similar websites (see list below). There is a lot of controversy over not only this case but also mining technology in general. Moving forward, we need to make sure we use cryptomining responsibly and securely.
All new technologies have growing pains. The key is to make sure we learn lessons from the past, ensure that the technology we use is secure, and that the spirit of why the technology was created in the first place continues in its new evolutions.
We watched as the advertising industry evolved in a way that made it easy for cybercriminals to use their platforms to attack users. We really don’t want to see miners go down the same path, and we hope it isn’t already too late.
Thanks for reading, safe surfing, and catch you next time!
Other mining sites we block
- coinnebula.com
- crypto-loot.com
- ws03.coinnebula.com
- ws02.coinnebula.com
- ws013.coinhive.com
- ws012.coinhive.com
- ws014.coinhive.com
- ws008.coinhive.com
- ws030.coinhive.com
- xmr.pool.minergate.com
- ws009.coinhive.com
- ws011.coinhive.com











