In the spirit of this upcoming Halloween season, we thought we’d provide you with a list of the top five scariest mobile threats in our book.
The list is organized from least to most haunting, based on my own humble opinion gathered from several years as a mobile threat researcher. Of course, my opinion has also been formed by the data we’ve collected within the last few months that shows which threats have been terrorizing customers the most. Without further ado, these are the top threats that haunt my dreams.
5) The clinking of locks and chains
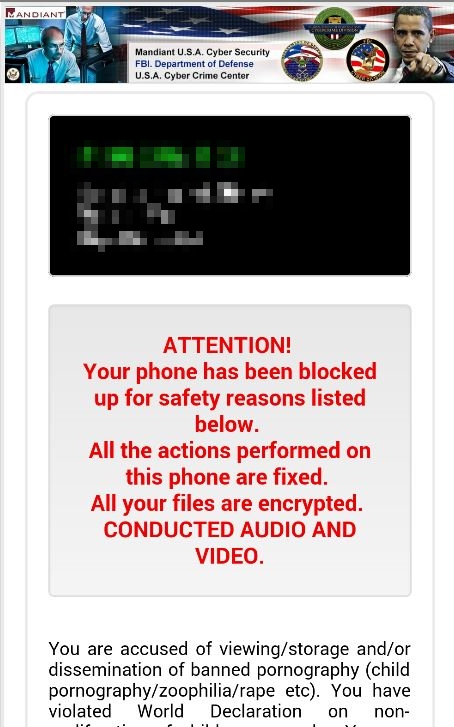
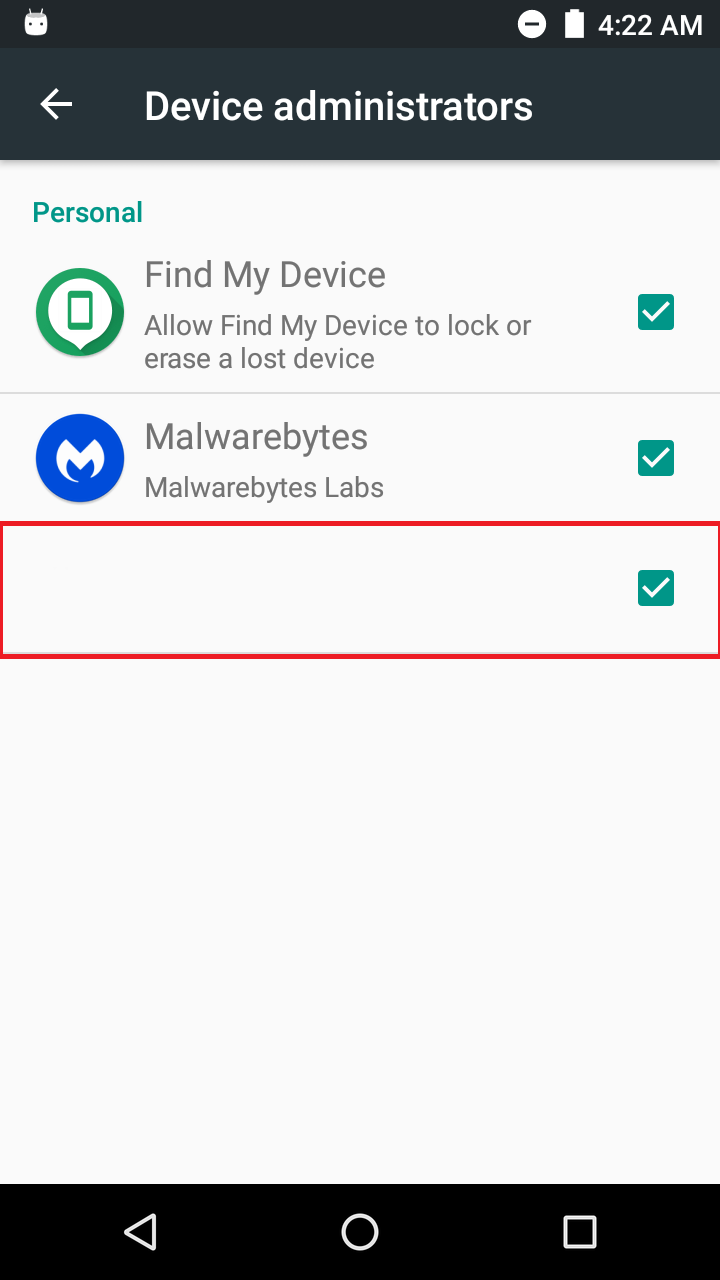
Although not the most prevalent mobile malware (thank goodness), mobile ransomware’s nastiness will give you the chills. It starts by tricking users into giving away their device administrator rights. Afterwards, the ransomware offers a treat of locking the device from any use unless you pay a ransom.
Even scarier, some mobile ransomware threatens prosecution by law enforcement, claiming illegal activities have been conducted on the device. This is all a hoax, as law enforcement would never request paying a fine through payment methods like Bitcoin or gift cards. The most popular mobile ransomware family is detected by Malwarebytes as Android/Ransom.SLocker.
4) Guerrilla warfare
As a mobile researcher, it sometimes feels like a war out there. This is especially true with the mobile malware
3) Dashing from ghosts? No, to the top of detections list!
Android/Adware.MobiDash will make your skin crawl! It’s one most highly-detected threats we’ve seen on customers’ Android devices! As if possessed, MobiDash goes above and beyond the typical low-level adware. It starts by sneaking its way into getting device administration rights. Once given, the user will be doomed with ads on his lock screen.
Good luck uninstalling, as some versions are especially good at hiding themselves in plain sight!
2) Lurking in the shadows…of code!
Another high-ranking threat found on customer’s Android devices,
1) The one that keeps me up at night: Adups
Seriously, I have lost sleep over this one. Adups and I have a long history:Mobile Menace Monday: Adups, old and new
Mobile Menace Monday: upping the ante on Adups
Adups comes in many forms, but the most prevalent is Android/PUP.Riskware.Autoins.Fota. This variant can potentially auto install malware like Android/Trojan.Guerrilla, and Android/Trojan.HiddenAds. As addressed in the blogs linked above, it’s a preinstalled system app(s). Thus, it cannot be uninstalled through the device’s information page, only disabled. However, the nightmare gets worse—Adups can’t even be disabled. Not even a mobile scanner can remove or disable it.
So how do we deal with this Freddy Krueger of a mobile threat? Well, you’re going to have to defeat it in a different realm: the realm of ADB command line tools, a part of Google’s Android Studio. Luckily, we found a wake to wake up from the nightmare, as we recently updated a guide on how to fully uninstall (not just disable) Adups. Beware, though, this tutorial is not for the faint of heart, and only recommended for advanced users.