Last week on Labs, we looked at security threats to headphones, privacy options in the world of law, and wandered through the FBI’s 2018 IC3 online crime report. We also explored another MageCart attack, and we released our 2019 Q1 Crime Tactics and Techniques report.
Other cybersecurity news
- Fooling automated surveillance cameras: Bypassing neural network frameworks with colourful abstract signs. Well, rectangles, to be more accurate. (Source: Arvix)
- VPN traffic raises concerns: Users of NordVPN query traffic they consider to be unusual related to the popular app. (Source: The Register)
- Who keeps your data safe? People think banks are best, but a majority still fear identity theft. (Source: Help Net Security)
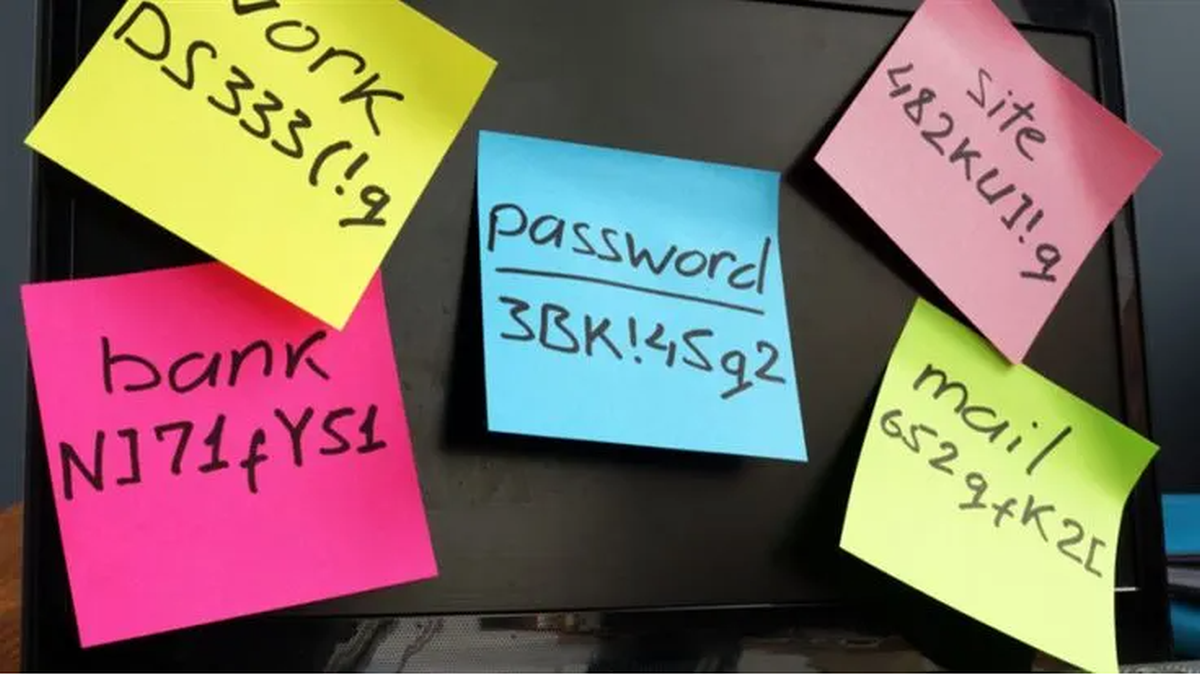
- Microsoft abandons password expiration for Windows 10: MS joins the growing trend for not finding a huge amount of value in needless password changes. (Source: Microsoft)
- Biometrics take a hit in Danish passports: A glitch is responsible for switching left and right hand prints tied to up to a quarter of a million travel documents. (Source: Copenhagen Post)
- A primer to credential stuffing: a nice summary of what, exactly, is involved with this most common of bad Internet practices. (Source: ZDNET)
- Cryptominer targets enterprise, ignores consumers: Beapy almost exclusively targets businesses in Asia, letting consumers temporarily off the hook. (Source: SCMag)
- Fake social: As bogus social media profiles continue to spread, can end-users tell the difference? (Source: Infosecurity Magazine)
- Emotet variant up to no good: compromised devices are being turned into proxy command and control servers, in an effort to make the attack slightly less overt. (Source: Bleeping Computer)
- Avoiding Apple ID phish attacks: They sometimes feel like they’re everywhere, and occasionally look quite convincing. Learn how to spot the signs of a scam. (Source: Heimdal Security)
Stay safe, everyone!