When removing malware from an iOS device, it is said that users need to restart the device to clear the malware from memory.
That is no longer the case.
Security researchers from ZecOps have created a new proof-of-concept (PoC) iPhone Trojan capable of doing “fun” things. Not only can it fake a device shutting down, it can also let attackers snoop via the device’s built-in microphone and camera, and receive potentially sensitive data due to it still being connected to a live network connection.
Stopping users from manually restarting an infected device by making them believe they have successfully done so is a notable malware persistence technique. On top of that, human deception is involved: Just when you thought it’s gone, it still pretty much there.
The researchers dubbed this overall attack “NoReboot,” and it does not exploit any flaws on the iOS platform. This means Apple cannot patch for it.
How they did it
So how does the malware stop the actual device shutdown from happening while making it look like it did to users? In a nutshell, the researchers hijack the shutdown event on an iOS device. This involves injecting new code to three daemons—programs that run in the background that have their own unique functions: InCallService, SpringBoard, and Backboardd.
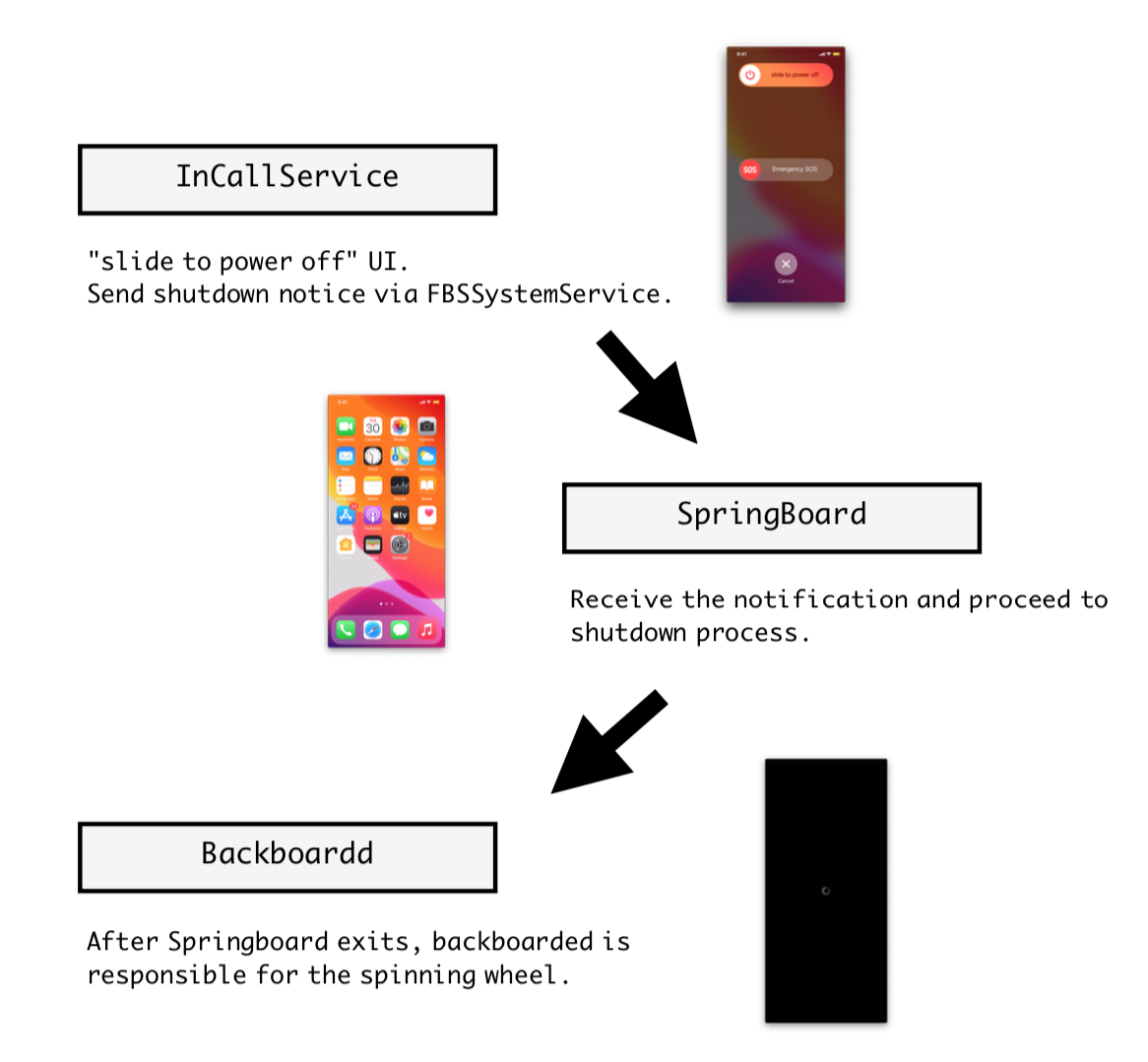
InCallService is responsible for sending the “shutdown” signal to SpringBoard when a user manually turns off the iOS device. The researchers were able to hijack this signal using a hooking process. So instead of InCallService sending the signal to SpringBoard as it’s supposed to, it instead signals SpringBoard and Backboardd to execute the codes injected into them.
The code in SpringBoard tells it to exit, not launch again, and only respond to a long button press. Since SpringBoard responds to user interaction and behavior, the daemon being unresponsive gives the impression that the device is off when, in fact, it’s not.
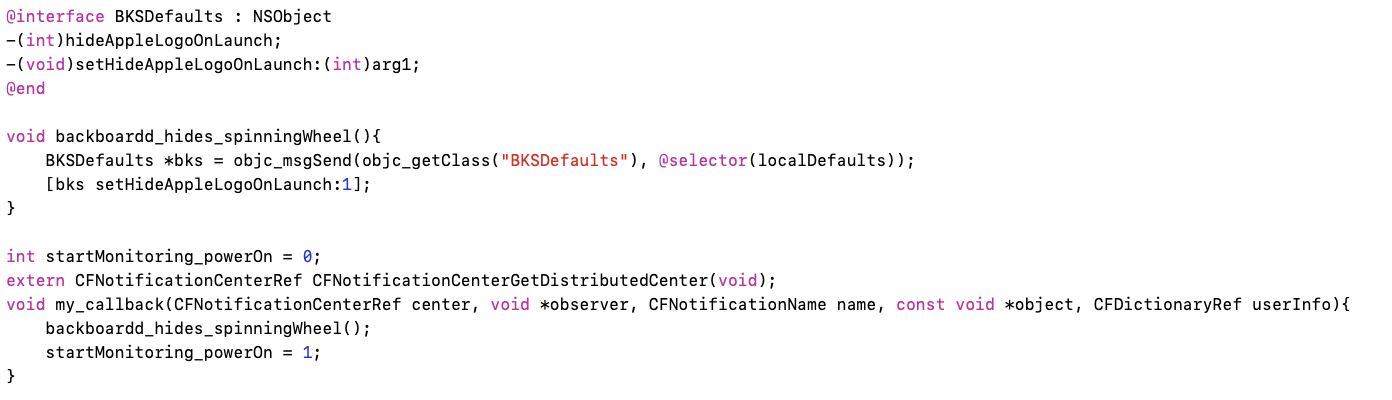
The code in BackBoardd, on the other hand, tells it to hide the spinning wheel animation, which pops up when SpringBoard ceases to work.
At this point, the iOS device looks and feels like a brick. But note that it’s still pretty much on, still connected to the internet, and still has functional features readily available for remote exploitation. Note that once an iOS device is infected with NoReboot, it starts its snooping via the camera.
Just as the device shutdown is simulated, NoReboot can also simulate a device to startup. And the BackBoardd daemon plays a huge role in this. Since SpringBoard is no longer functioning, Backboardd takes control of the screen and responds to user inputs, including long button presses. Backboardd is told to show the Apple logo, a known indicator that the iOS device has indeed been turned off, which makes users let go of the button and stop them from truly rebooting the device. Then SpringBoard is relaunched so Backboardd can give back its privilege to control the screen.
You can read more about how NoReboot works in detail in ZecOps’s post here.
“Is this thing on?”
Since Apple introduced a feature that allows device owners to track their phones even when they’re turned off, things have never been the same. “On” remains on, while “off” is not-quite-off anymore. And this only gives attackers an opportunity to let their malware persist on affected devices.
NoReboot is a mere PoC at this point, but its code is already public. It’s only a matter of time before iOS attackers start incorporating this into their malware kits. That said, let’s arm ourselves with what we can do as users at this point.
If you suspect that your device is compromised by a NoReboot-like malware, you can keep pressing the force reboot buttons after the the Apple logo appears. Remember that this is a simulated reboot, and keeping the restart buttons depressed would force the infected device to truly reboot. iOS device owners can also use Apple Configurator, which you can download for free.
Stay vigilant!
(Kudos to Thomas Reed for additional helpful insights)










