In the continued saga of annoying search extensions we have a new end-of-level boss.
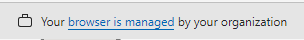
Victims have been reporting browser extensions that were removed by Malwarebytes, but “magically” came back later. Since the victims also complained about the message saying their browser was “managed”, we had a pretty good idea where to look.
Search extensions
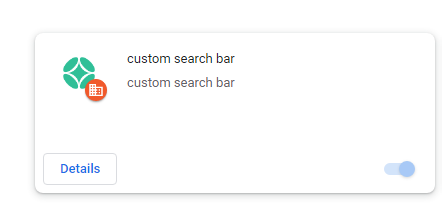
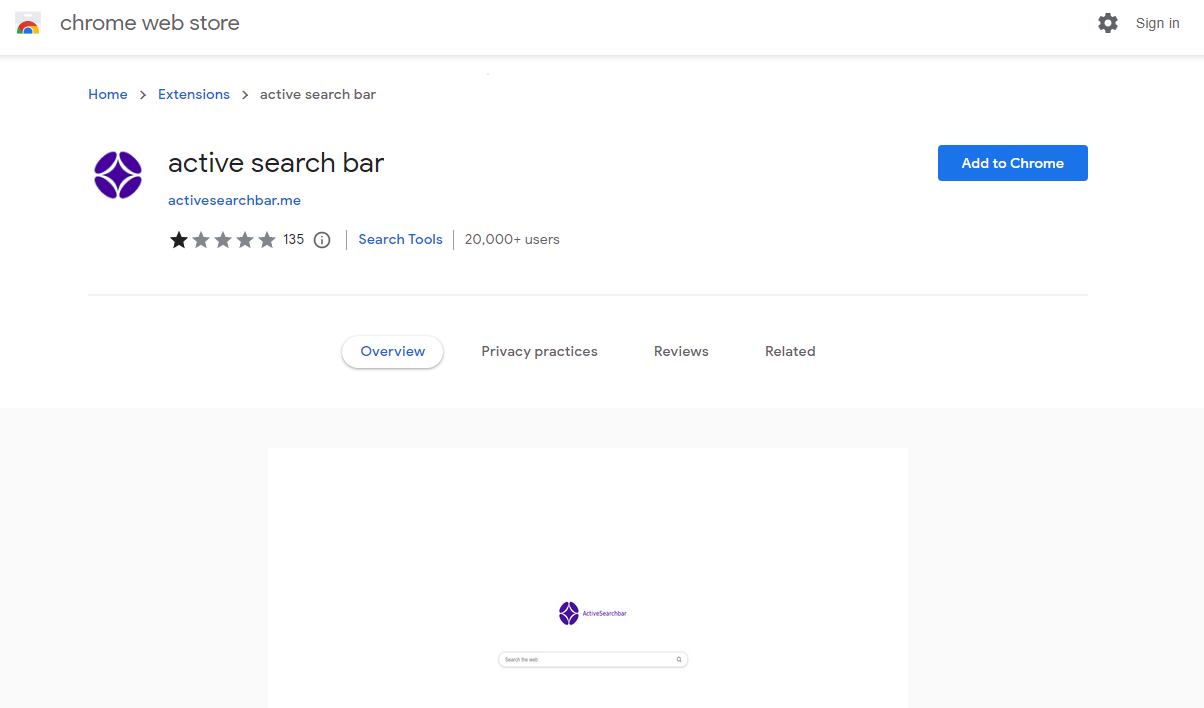
The culprits turned out to be search extensions. Which is often the case when we spot potentially unwanted programs (PUPs) that use malware tactics to get installed and gain persistence.
The search hijackers “active search bar” and “custom search bar” were both available in the Chrome web store at the time of writing even though we reported them days ago.
PowerShell
It took some digging to find the origin, since all we had were the extensions. And when the extensions were installed directly from the webstore, nothing happened out of the ordinary. However, some hunting on VirusTotal soon led me to a few recently uploaded PowerShell scripts that included the string “ExtensionInstallForcelist.” I looked for that string because we know from the past that these registry policies account for the “Your browser is managed” warnings.
$CPath = "HKLM:SOFTWAREPoliciesGoogleChrome
ExtensionInstallForcelist";$EPath = "HKLM:SOFTWAREPoliciesMicrosoftEdgeExtensionInstallForcelist";
The description in the Chromium documentation about the ExtensionInstallForcelist states:
“Specifies a list of apps and extensions that are installed silently, without user interaction, and which cannot be uninstalled nor disabled by the user.”
And to confirm this finding, the victims that provided logs all had one of these PowerShell script listed in their Scheduled Tasks.
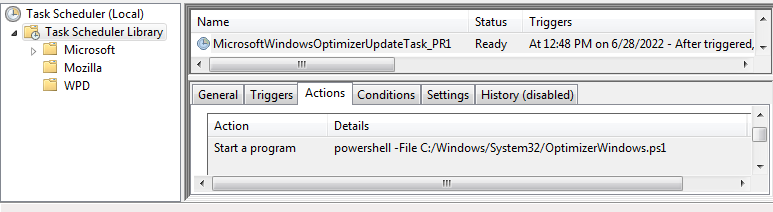
The Scheduled Task was set to run every four hours, which explained why the extensions kept coming back.
Installer
But Scheduled Tasks don’t install themselves either and dropping PowerShell scripts in the System32 folder requires Administrator privileges, so we needed to dig a little further to find an installer.
The domain wincloudservice.com was used as a download location in all the PowerShell scripts so we used that domain as a search parameter in our next stage of VirusTotal hunting. This search eventually returned three installers. What they had in common at first glance was that the filenames all ended with “_x64LTS.exe” and that they were all signed by “Tommy Tech LTD.”
Upon further inspection we noticed that the installers all asked for Administrator privileges twice. The first part installs something that is called “Setup” and the second part installs an application that aligns with the name of the installer. So, it appears that the original installer files were “patched” to add the installer for our browser hijacker. It stands to reason that these installers are offered for download somewhere by the threat actors.
The EULA points to tommytechil.com which is unreachable. I was unable to find an installer that actually dropped an extension in Edge, but the “Your browser is managed by your organization” setting does get enforced.
Javascripts
Malwarebytes customers were protected against these extensions as Malwarebytes’ web protection module blocked the domain wincloudservice[.]com. On inspection, this domain hosted several javascripts including heavily obfuscated files called crypto.js and crypto-js.min.js.
Detection and removal
Malwarebytes detects these browser hijackers as PUP.Optional.ActiveSearchBar and PUP.Optional.CustomSearchBar. Included in the removal procedure are the extension, and the Scheduled Task, which is enough to permanently get rid of the extension.
Some Windows registry changes have been made that will take a system administrator to decide what they want to keep or not.
The registry keys to remove the “Your browser is managed” are:
HKEY_LOCAL_MACHINESOFTWAREPoliciesGoogleChromeExtensionInstallForceList
HKEY_LOCAL_MACHINESOFTWAREPoliciesMicrosoftEdgeExtensionInstallForceList
And another change made by the installer was the registry value:
HKEY_LOCAL_MACHINESOFTWAREMicrosoftPowerShell1ShellIdsMicrosoft.PowerShell\
ExecutionPolicyThe installer set that to “Unrestricted” which may not be your favorite setting. If you are not sure or you have never actively set that policy, the default is
“Restricted”IOCs
Domains:
Installers:
4kvideodownloader_5.22.371_x64LTS.exe
AutoClicker_x64LTS.exe
FPSUnlocker_4.1_x64LTS.exe
PowerShell scripts:
PrintWorkflowService.ps1
WindowsUpdater1.ps1
OptimizerWindows.ps1
Extensions:
custom search bar nniikbbaboifhfjjkjekiamnfpkdieng
active search bar pkofdnfadkamabkgjdjcddeopopbdjhg











