On September 20, 2022, the official Twitter account for 2K Support tweeted an important message from the Customer Support team.
The tweet said an unauthorized party illegally accessed the credentials of one of the vendors of the helpdesk platform. The attacker then used that access to send out communications that contained a malicious link.
The email
There is some confusion about the email, which is clear from reading the replies and tweets on 2K support. From what we managed to put together based on the tweets and what little information 2K provided, the first email looked similar to this one:
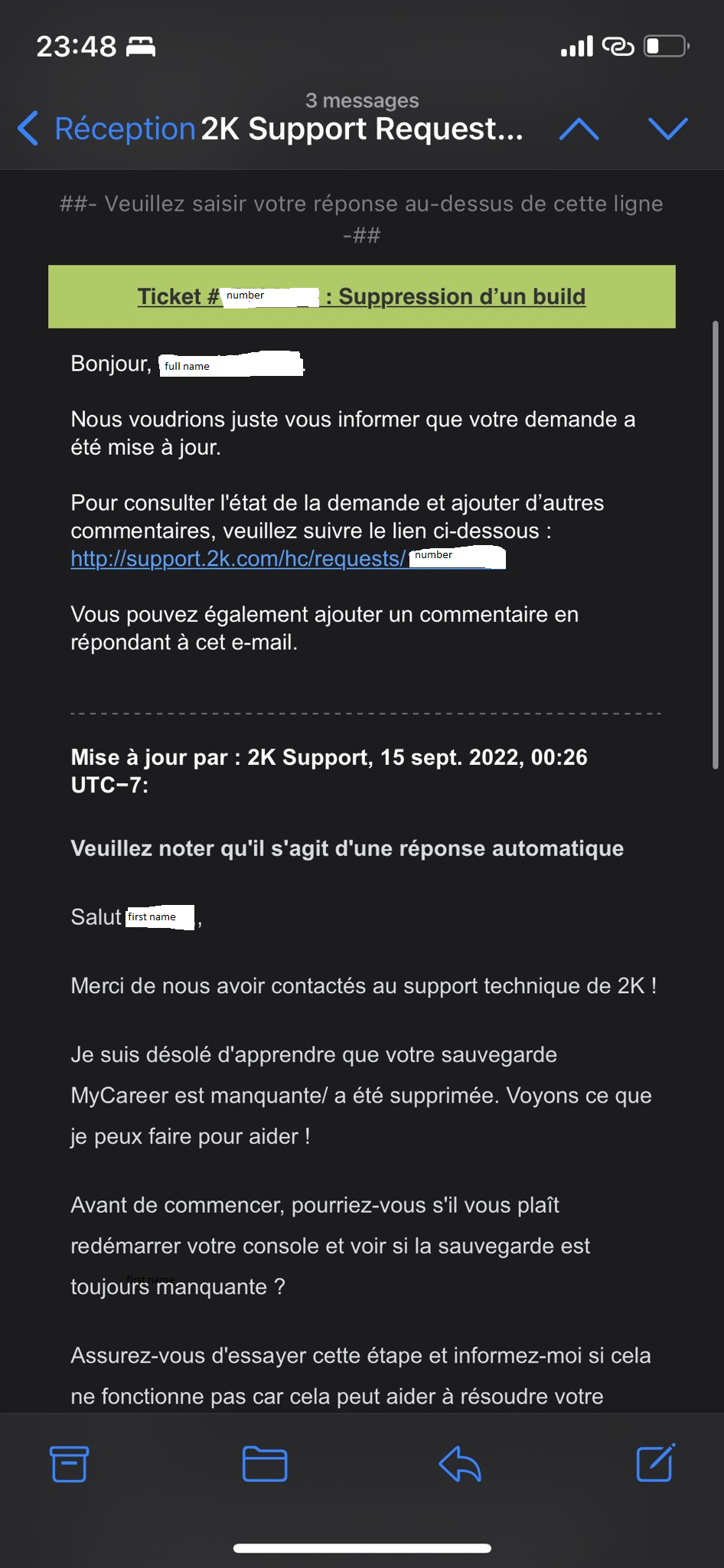
In some cases, these were followed by a second email that looked similar to this one.
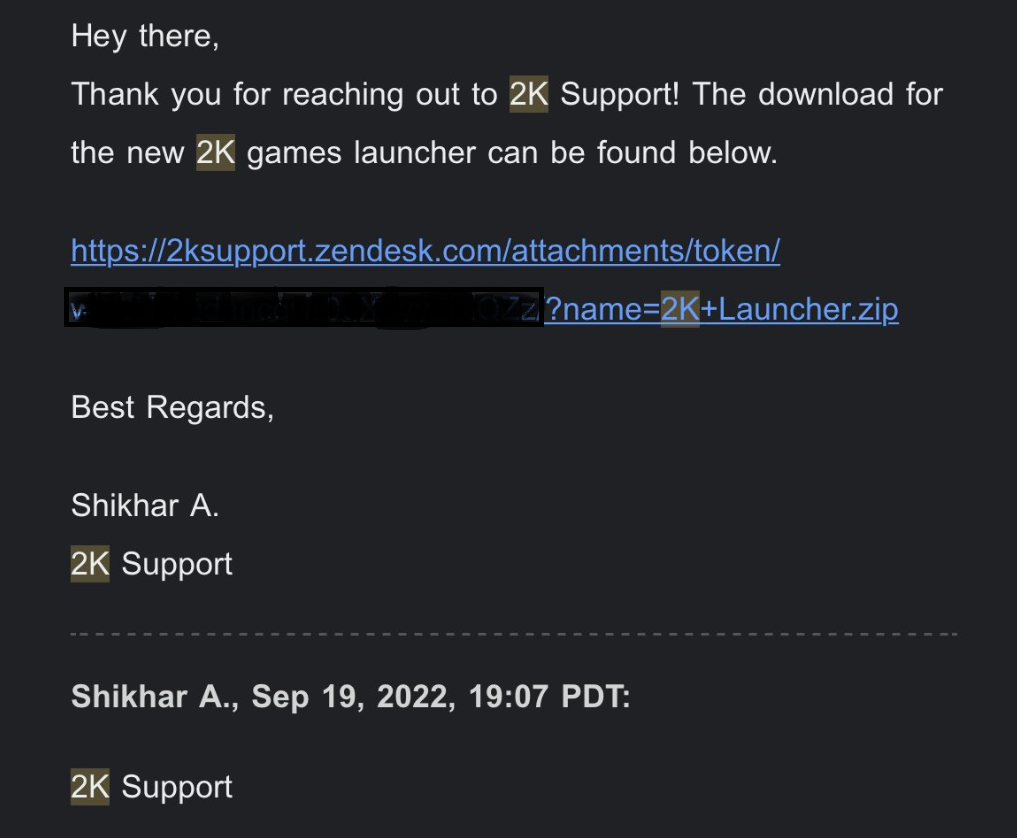
At the point of writing, clicking the link in the first mail will take you to a login screen for the 2K games support site and the link in the second email takes you to a Zendesk page which tells you that this “help center” no longer exists.
The malware
In the case of the first email, visitors were taken to a support ticket that contained a link to the same file (2K+Launcher.zip). In the case of the second email, the email itself container a direct link to the malware.
The zip file contains an executable called 2K Launcher.exe. It does display a 2K logo, but if you look at the Properties, you will notice the original filename is Plumy.exe. Both the Description and the Product name have it listed as 5K Player.
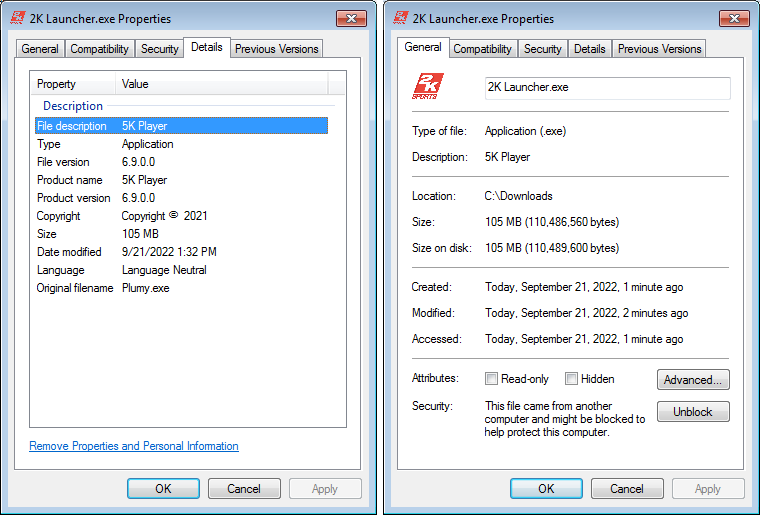
The malware turns out to be RedLine infostealer. RedLine specializes in stealing banking information from a system’s clipboard. It also attempts to steal other data from the affected system, like browser history, cookies, and saved browser passwords.
Info stealers like this are usually delivered to an affected system when users download them under false pretenses, often disguised as popular software or cracks.
Supply chain
Breaking into the supply chain like this can give an attacker access to a large amount of potential victims. Most of the customers in this case had open tickets, so they weren’t surprised to receive an email from the Support desk. And it’s not uncommon for Support desks to send out files for system analysis, which can help support to pinpoint the problems customers might have with the installation of their product or any other hardware or software conflicts.
Mitigation
Anyone that has downloaded the file must now do a full system scan to remove any malware.
If you have executed the file, this means that information from and about your system may have been sent to the attacker.
What can you do to limit the dangers of stolen information as much as possible?
- Change the passwords that might have been stolen for every website you can remember logging into. Depending on how your browser stores the passwords, you may have to do the same for every password that the browser remembers for you. All modern web browsers come with a built-in password manager that offers to store your login credentials, but the degrees of security encryption are very diffferent.
- If your email account has been compromised, change that password first as other credentials may be sent to you by mail and still end up in the wrong hands. Some online shops even send you a password in plain-text.
- Keep a close eye on your banking and eMoney accounts. Use the activity alerts that some banks offer.
- Keep tabs on your posts in social media. It may look silly to check what you have supposedly posted yourself, but imagine someone else doing it for you.
Extra precautions
- Enable 2FA wherever possible.
- Do not re-use passwords, and consider a password manager to generate and remember all your passwords for you.
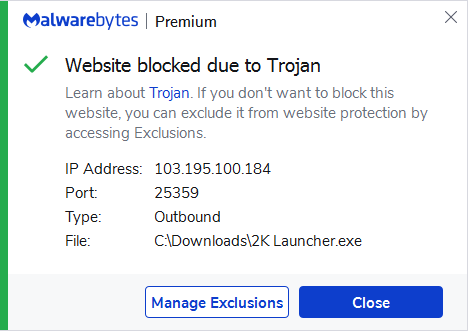
Malwarebytes customers were protected against this attack because the Premium version blocked the C2 server that the 2K Launcher.exe contacts when it is executed.