Security researchers at Akamai have published a blog about a new Magecart-alike web skimming campaign that uses compromised legitimate sites as command and control (C2) servers.
A web skimmer is a piece of malicious code embedded in web payment pages to steal personally identifiable information (PII) and credit card details from customers of the site.
Since the code is executed on the client’s side, the malicious behavior is hard to detect by the website’s owner since it will not be picked up by web application firewalls (WAFs) and other measures to keep the server safe.
This campaign is different since it relies on legitimate but compromised sites to make the traffic look genuine. Since these sites normally operate as legitimate businesses, they are less likely to raise suspicion when connecting to a victim. The target sites are running digital content management systems like Magento, WooCommerce, WordPress, and Shopify, but contain a variety of vulnerabilities.
The Akamai researchers uncovered numerous digital commerce websites that have fallen victim, and say that it is reasonable to assume that there are additional legitimate websites that have been exploited as part of this extensive campaign.
Some of the victim organizations see hundreds of thousands of visitors per month which could potentially result in thousands of victims that have their credit card data and PII stolen. Especially since the campaign has been going unnoticed for close to a month for many of the victims.
In this campaign there were two kinds of victim sites:
- Host victims: Legitimate websites that are hijacked for the purpose of hosting the malicious code used in the attack. They are compromised to behave as an attacker-controlled server.
- Web skimming victims: Instead of directly injecting the attack code into the website’s resources, the attackers employ small JavaScript code snippets as loaders to fetch the full attack code from the host victim website.
In some cases, the exploited host websites appear to have been abused in both ways.
The code used on the web skimming victims is designed to look like popular third-party services such as Google Tag Manager or Facebook Pixel. This method is popular among web skimmers because it helps the malicious code blend in seamlessly, disguising its true intentions.
CMS security in a nutshell
Spilling your customers’ PII and credit card details can be very damaging for your reputation, so it’s important to make sure they can visit and use your website safely.
There are a few obvious and easy-to-remember rules to keep in mind if you want to use a CMS without compromising your security:
- Choose your CMS with both functionality and security in mind
- Choose your plug-ins wisely
- Update as soon as you can
- Keep track of the changes to your site and their source code
- Use 2FA
- Give user permissions (and their levels of access) a lot of thought
- Be wary of SQL injection
- If you allow uploads, limit the type of files to non-executables and monitor them closely.
For websites that require even more security, there are specialized vulnerability scanners and application firewalls that you may want to look into. This is especially true if you are a popular target for people that would love to deface or abuse your website.
If the CMS is hosted on your own servers, be aware of the dangers that this setup comes with some additional risks. Use network segmentation to keep the website server separated from other work servers.
IOCs
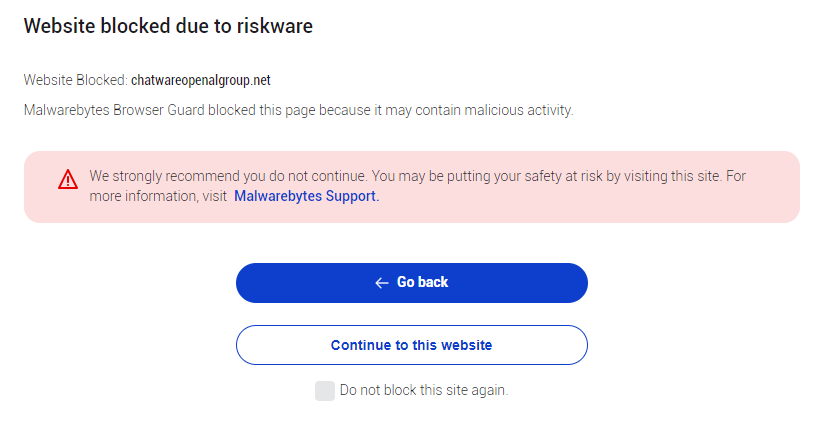
Malwarebytes Browser Guard blocks the receiving domains of the stolen data:
byvlsa.com
chatwareopenalgroup.net
Malwarebytes EDR and MDR removes all remnants of ransomware and prevents you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.











