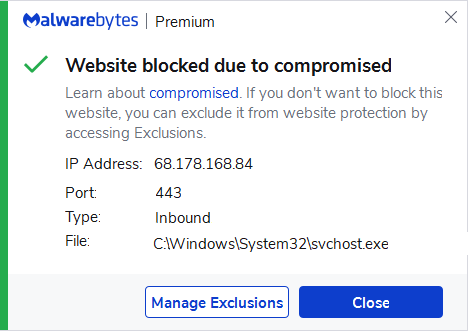
68.178.168.84
Short bio
This range of IP addresses have been found to be involved in RDP probes or attacks. This is a block of incoming traffic – meaning the IP address being blocked is scanning and/or attempting to force its way into your machine via different ports. These attacks can last anywhere from a few hours, days, to a week. IP ranges will be probed by the compromised systems followed by an attempt to brute force their way into machines in order to infect them with ransomware.
The most common method of accessing machines is via Windows Remote Desktop Protocol (RDP). We recommend you check to see if you have the Remote Desktop enabled and if so, disable it. For more information, see How to use Remote Desktop. If you need to use Remote Desktop, see our Malwarebytes Labs article How to protect RDP on how best to lock it down.
Protection
Malwarebytes blocks the IP 68.178.168.84 because it has been compromised.
What you can do
Given that Malwarebytes is blocking the attackers, you do not need to worry and no further action is required.
If the block alerts are interfering too much with your daily work, it may help if you add the IP address you see in our Alert to the Windows Firewall.
To view the IP address in our alert:
- Open Malwarebytes for Windows > click the Detection History card.
- Click the History tab.
- Under the Event column, open the Real-Time Protection detection report.
Exclusion
Should users wish to visit a blocked IP Address and exclude it from being blocked, they can add it to the exclusions list. Here’s how to do it.
- Open Malwarebytes for Windows.
- Click the Detection History
- Click the Allow List
- To add an item to the Allow List, click Add.
- Select Allow a website.
- Select Add an IP address and enter the IP address that you wish to exclude.
- Click on Done and the IP address should appear in your Allow List.
Please note that allowing these inbound scans could lead to an infection of your system.





