Ransom.GandCrab
Short bio
Ransom.GandCrab is Malwarebytes’ detection name for a family of ransomware that encrypts important files and asks for a ransom to decrypt them. There are several versions of Ransom.GandCrab as the threat actors keep working on it. They all target Windows systems.
Symptoms
The first thing users of affected systems notice is usually the ransom note when the encryption has altready finished.

Type and source of infection
Ransom.GandCrab scans the infected system and any network shares for files to encrypt. You can recognize the version of GandCrab by looking at the extensions the encrypted files have:
- Version 1 gives the .gdcb extension
- Version 2 and 3 give the .crab extension
- Version 4 gives the .krab extension
- Version 5 gives a randomized 5 letter extension
Ransom.GandCrab is spread in many different ways:
- malspam
- exploit kits
- social engineering
- fake cracked software sites
Aftermath
For some versions of Ransom.GandCrab there are free decryption tools. You can check the NoMoreRansom! for which ones they are currently available.
Protection
Malwarebytes protects users from Ransom.GandCrab by using real-time protection.
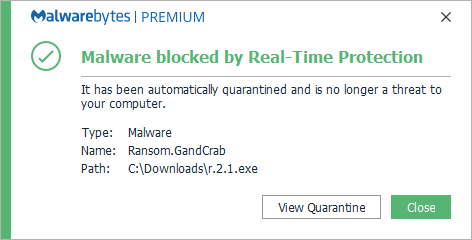
and Malwarebytes protects users from Ransom.GandCrab by using Anti-Ransomware technology.
Business remediation
Malwarebytes can detect and remove Ransom.GandCrab on business machines without further user interaction. To remove Ransom.GandCrab using Malwarebytes business products, follow the instructions below.
How to remove Ransom.GandCrab with Malwarebytes Endpoint Protection
-
- Go to the Malwarebytes Cloud console.
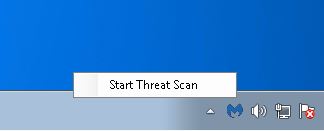
- To allow you to invoke a scan while the machine is off the network, go to Settings > Policies > your policy > General.
- Under Endpoint Interface Options, turn ON:
- Show Malwarebytes icon in notification area
- Allow users to run a Threat Scan (all threats will be quarantined automatically)
If you have infected machines that are not registered endpoints in Malwarebytes Endpoint Protection, you can remove Ransom.GandCrab with our Breach Remediation tool (MBBR).
-
-
- Log into your My Account page and copy your license key. The key is needed to activate MBBR tool.
- Open your Cloud console.
- From a clean and safe machine, go to Endpoints > Add > Malwarebytes Breach Remediation. This will download the MBBR zip package.
- Unzip the package.
- Access a Windows command line prompt and issue the following commands: mbbr register –key:
mbbr update Note: You must substitute your license key for . - Copy the MBBR folder to a flash drive.
- From an infected, offline machine, copy the MBBR folder from the flash drive.
- Start a scan using the following command: mbbr scan –full –ark –remove –noreboot
- Refer to the Malwarebytes Breach Remediation Windows Administrator Guide for all supported scanning commands.
-
Use the “rollback files encrypted by ransomware” option in Malwarebytes Endpoint Protection and Response if the infection was caught after it had encrypted some files. This may be the case if the infection was not caught by the Real-Time-Protection module, but by the behavioral based Anti-Ransomware Technology.
Home remediation
Malwarebytes can detect and remove Ransom.GandCrab without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Take note, however, that removing this ransomware does not decrypt your files. You can only get your files back from backups you made before the infection happened.





