Ransom.Ragnar
Short bio
Ransom.Ragnar is Malwarebytes’ detection name for a family of ransomware also known as RAGNAR_LOCKER.
Symptoms
Victims will find the ransome note named RGNR_
Type and source of infection
Ransom.Ragnar is ransomware. Ransomware in general makes files on the victims system unusable until the ransom is payed. Ransom.Ragnar not only encrypts a victims files, but also threatens to publish them. Ransom.Ragnar is spread in the form of a preinstalled and preconfigured Windows XP virtual machine that runs the ransomware on the victim’s system.
Aftermath
Recovering from a ransomware attack can be a painstaking process even if the victim decides to pay it can take a considerable time to recover without adequate, recent, and organized backups, or a roll-back technology.
Not paying the Ragnar_Locker ransom can lead to exposure of exfiltrated data on the dark web.
Protection
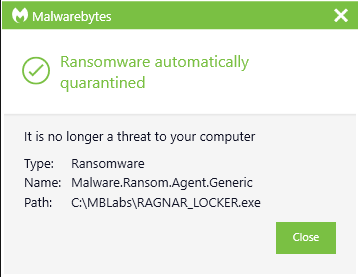
Malwarebytes blocks Ransom.Ragnar
Home remediation
Malwarebytes can detect and remove Ransom.Ragnar without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Take note, however, that removing this ransomware does not decrypt your files. You can only get your files back from backups you made before the infection happened.
Business remediation
How to remove Ransom.Ragnar with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
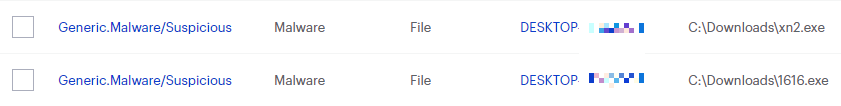
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found. 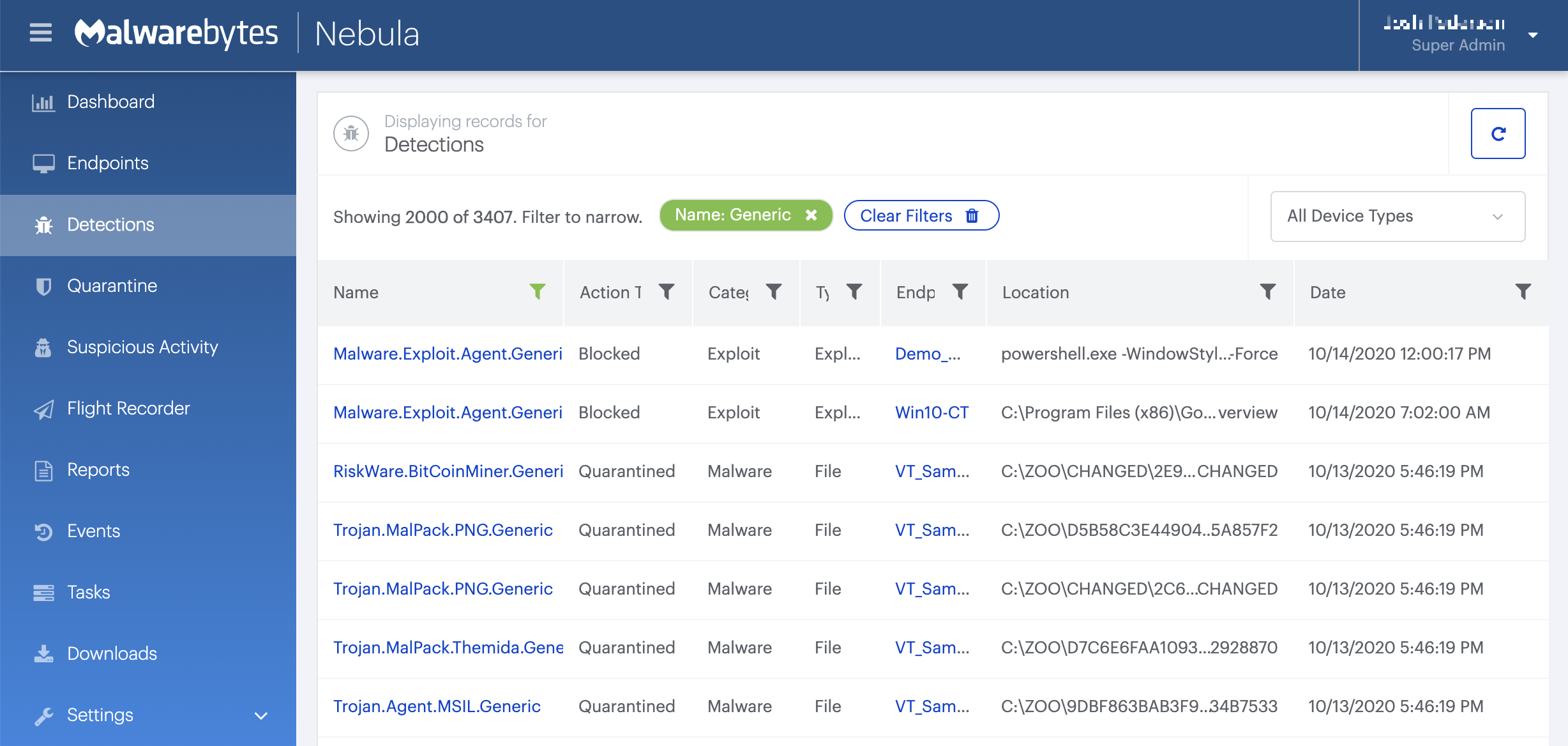
Traces/IOCs
File extensions:
.ragnar_ Ransom notes: RGNR_





