Ransom.SunCrypt
Short bio
Ransom.SunCrypt is Malwarebytes’ detection name for a specific Ransomware as a Service (RaaS) variant that uses a very aggressive approach towards its victims.
Symptoms
Victims will find the ransome note named: YOUR_FILES_ARE_ENCRYPTED.HTML
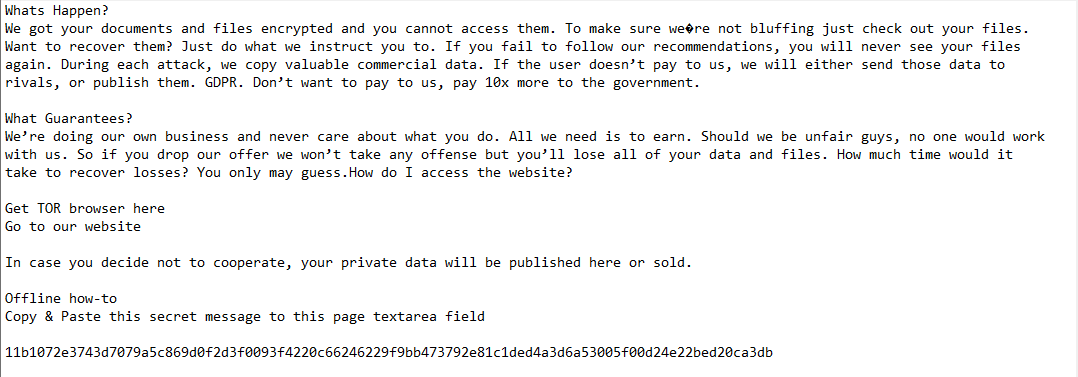
When encrypting files, it will append a hexadecimal hash to the end of each file name.
Type and source of infection
Ransom.SunCrypt is ransomware. Ransomware in general makes files on the victims system unusable until the ransom is payed. Ransom.SunCrypt not only encrypts a victims files, but also threatens to publish them. The SunCrypt ransomware is distributed as a DLL file and is installed through a heavily obfuscated PowerShell script. In some cases they have been seen partnering with Trickbot to gain access to compromised networks.
Aftermath
Recovering from a ransomware attack can be a painstaking process even if the victim decides to pay it can take a considerable time to recover without adequate, recent, and organized backups, or a roll-back technology.
Not paying the SunCrypt ransom can lead to exposure of exfiltrated data on the dark web, and DDoS attacks by the SunCrypt affiliates.
Protection
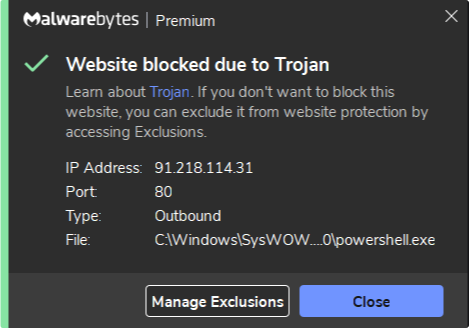
Malwarebytes blocks traffic to the C&C server
Home remediation
Malwarebytes can detect and remove Ransom.SunCrypt without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Take note, however, that removing this ransomware does not decrypt your files. You can only get your files back from backups you made before the infection happened.
Business remediation
How to remove Ransom.SunCrypt with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
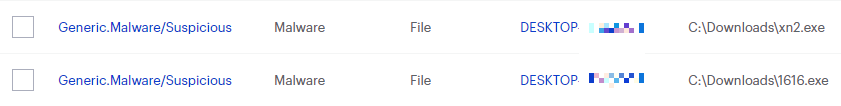
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
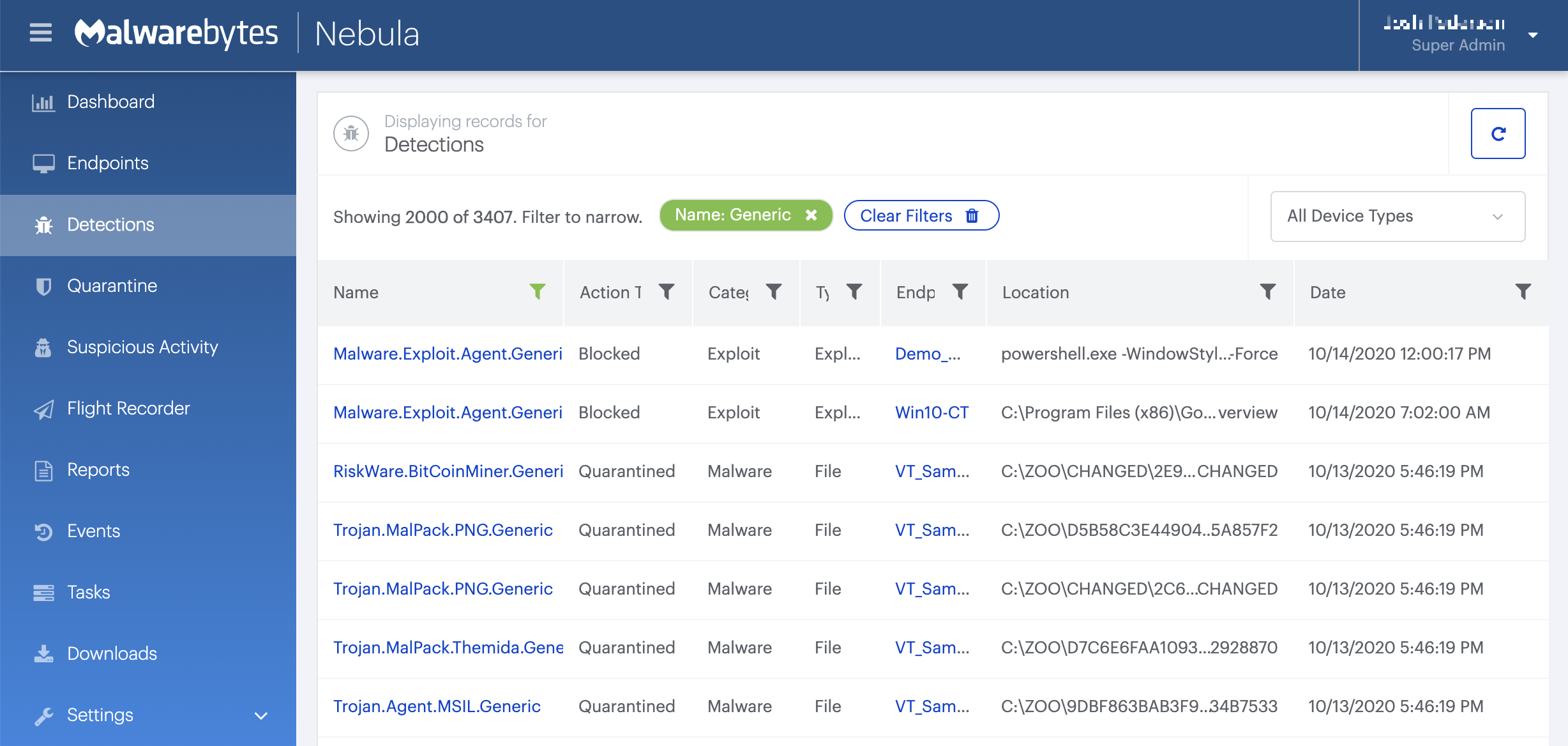
On the Quarantine page you can see which threats were quarantined and restore them if necessary.
All component/technology detections are passed to the remediation engine for complete removal from infected systems. This industry leading technology uses patented techniques in identifying all cohorts or associated files for a single threat and removes them all together to prevent malware from resuscitating itself. If you are using Malwarebytes Ransomware Rollback technology, it allows you to wind back the clock to negate the impact of ransomware by leveraging just-in-time backups.
Traces/IOCs
C&C:
91.218.114.31
Ransom note:
YOUR_FILES_ARE_ENCRYPTED.HTML





