Trojan.Dropper.SFX
Short bio
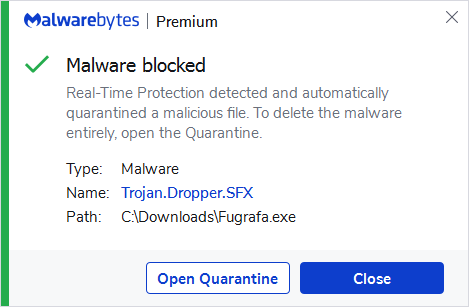
Trojan.Dropper.SFX is Malwearebytes’ generic detection name for Trojan droppers that arrive on the affected system as self extracting archives.
Type and source of infection
Droppers are helper programs for various types of malware such as Trojans and rootkits. Usually they open a way for attack by downloading/decompressing and installing the core payload. Downloaders often appear in non-persistent form. They install the malicious module and remove themselves automatically. In such a case, after a single deployment they are no longer a threat. More dangerous variants are persistent. They copy themselves to some random, hidden file and create registry keys to run after the system is restarted, attempting to download the malicious modules again. When the downloaded file is run, a self extracting dropper first extracts itslef and then downloads other malware and installs it on a system. Most of the time, the user gets infected by using some unauthenticated online resources. Infections are often consequences of activities like:
- Clicking malicious links or visiting shady websites
- Downloading unknown free programs
- Opening attachments sent with spam
They may also be installed without user interaction, carried by various exploit kits.
Protection
Malwarebytes blocks Trojan.Dropper.SFX by using real-time protection.
Home remediation
Malwarebytes can detect and remove Trojan.Dropper.SFX without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Trojan.Dropper.SFX with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections pageto see which threats were found.On the Quarantine page you can see which threats were quarantined and restore them if necessary.





