Trojan.FakeMBAM
Short bio
Trojan.FakeMBAM is Malwarebytes’ generic detection name for Trojans that pose as a Malwarebytes product.
Type and source of infection
Trojan.FakeMBAM are files that are made to look like they are Malwarebytes products, either because they seem to be signed by Malwarebytes, have Malwarebytes Version Info, or because the name of the file would lead users to think so.
Protection
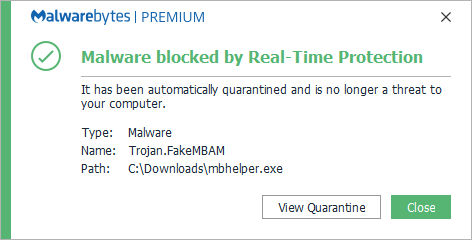
Malwarebytes blocks Trojan.FakeMBAM
Home remediation
Malwarebytes can detect and remove Trojan.FakeMBAM without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get startedbutton.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Trojan.FakeMBAM with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
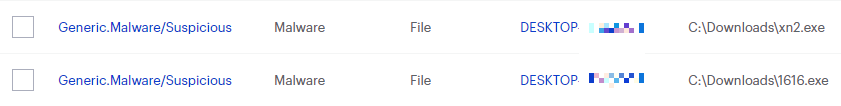
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
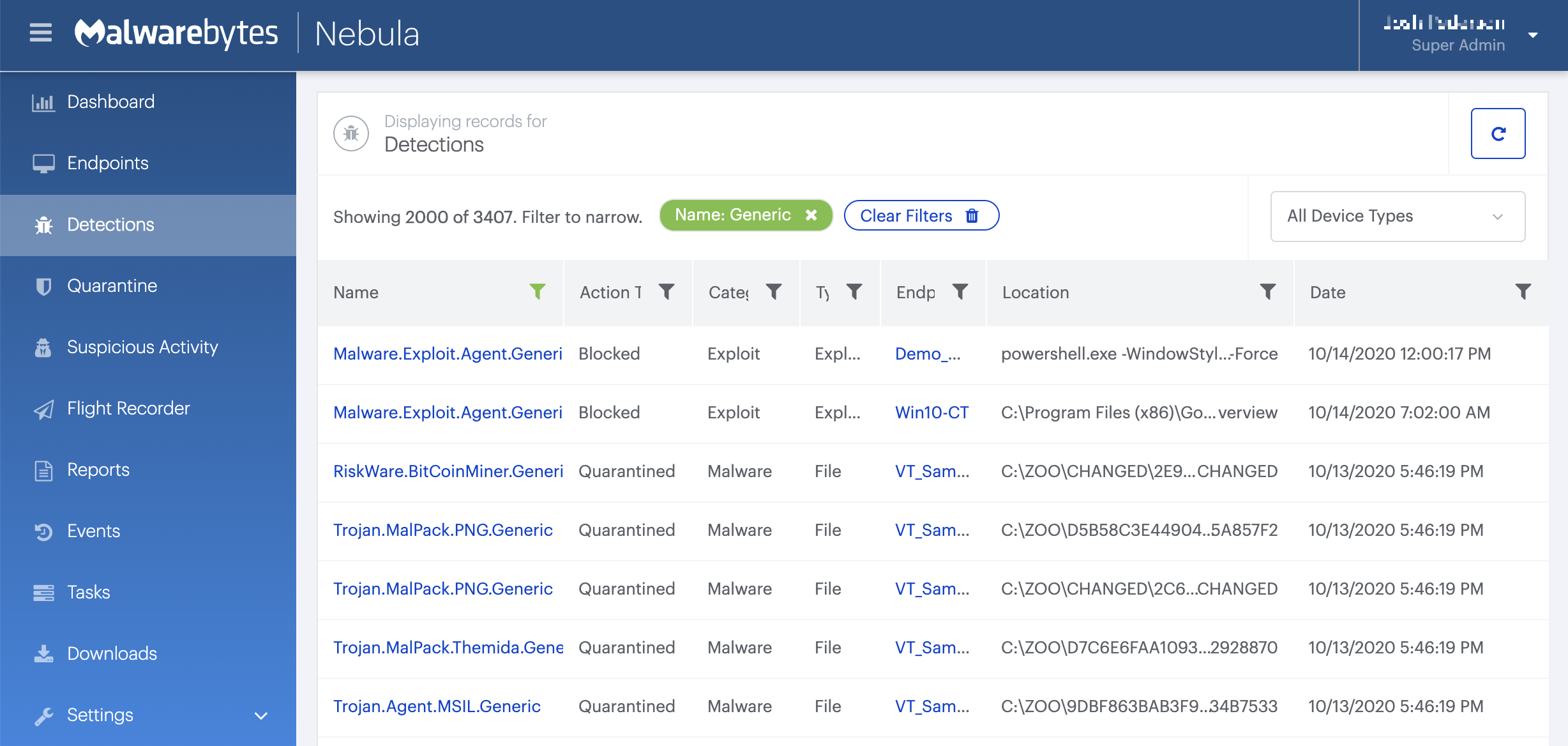
On the Quarantine page you can see which threats were quarantined and restore them if necessary.
Malwarebytes removal log
A Malwarebytes log of removal will look similar to this:
Malwarebytes
www.malwarebytes.com
-Log Details-
Scan Date: 10/22/18
Scan Time: 1:10 PM
Log File: 249fb954-d5eb-11e8-a82a-00ffdcc6fdfc.json
-Software Information-
Version: 3.6.1.2711
Components Version: 1.0.463
Update Package Version: 1.0.7465
License: Premium
-System Information-
OS: Windows 7 Service Pack 1
CPU: x64
File System: NTFS
User: {USERNAME}-PC\{USERNAME}
-Scan Summary-
Scan Type: Threat Scan
Scan Initiated By: Manual
Result: Completed
Objects Scanned: 237975
Threats Detected: 3
Threats Quarantined: 3
Time Elapsed: 2 min, 50 sec
-Scan Options-
Memory: Enabled
Startup: Enabled
Filesystem: Enabled
Archives: Enabled
Rootkits: Enabled
Heuristics: Enabled
PUP: Detect
PUM: Detect
-Scan Details-
Process: 1
Trojan.FakeMBAM, C:\USERS\{USERNAME}\DOWNLOADS\MBHELPER.EXE, Quarantined, [9667], [573188],1.0.7465
Module: 1
Trojan.FakeMBAM, C:\USERS\{USERNAME}\DOWNLOADS\MBHELPER.EXE, Quarantined, [9667], [573188],1.0.7465
Registry Key: 0
(No malicious items detected)
Registry Value: 0
(No malicious items detected)
Registry Data: 0
(No malicious items detected)
Data Stream: 0
(No malicious items detected)
Folder: 0
(No malicious items detected)
File: 1
Trojan.FakeMBAM, C:\USERS\{USERNAME}\DOWNLOADS\MBHELPER.EXE, Quarantined, [9667], [573188],1.0.7465
Physical Sector: 0
(No malicious items detected)
WMI: 0
(No malicious items detected)
(end)Traces/IOCs
Hashes:
fb51328e4ff3b914989d8aaee423cd57 19c2a1d88b03f17d8f257daf4b69e864 8c5601578f7a58e1bae0aa0649bd3b78 b1a0d2c8cddd64cde4990de163bb259a 65907818c98bd87dac62d7aaa96504d6 92ec553c194b745bd2434d7ffef46d39 8c5601578f7a58e1bae0aa0649bd3b78 6d6ddc11c7ab241a482bc88a85b3a150
Associated threats
- Trojan.FakeMBAM.ED





