Virlock.Ransom.FileInfector.DDS
Short bio
Virlock.Ransom.FileInfector.DDS is Malwarebytes detection name for the Virlock ransomware detected by Malwarebytes’ Katana engine.
The detection names are produced by Malwarebytes 4 and Malwarebytes business products. These generic malware detections are due to our new automated signature system called BytesTotal and specifically the DDS engine that are based on Machine Learning technology with 100% autonomous learning which don’t require any human interaction to correctly identify malware. These techniques are part of Malwarebytes’ Katana engine and were developed for automated mass detection of wide ranges of malware and adware.
Type and source of infection
Even though the VirlLock ransomware is relatively old (it was first seen in 2014) we still see an occasional infection. It is able to spread through shared applications and cloud storage. Besides being polymorphic it also avoids detection by using multiple layers of encoding. It gains persistence by registering itself as a service on the infected system.
Symptoms
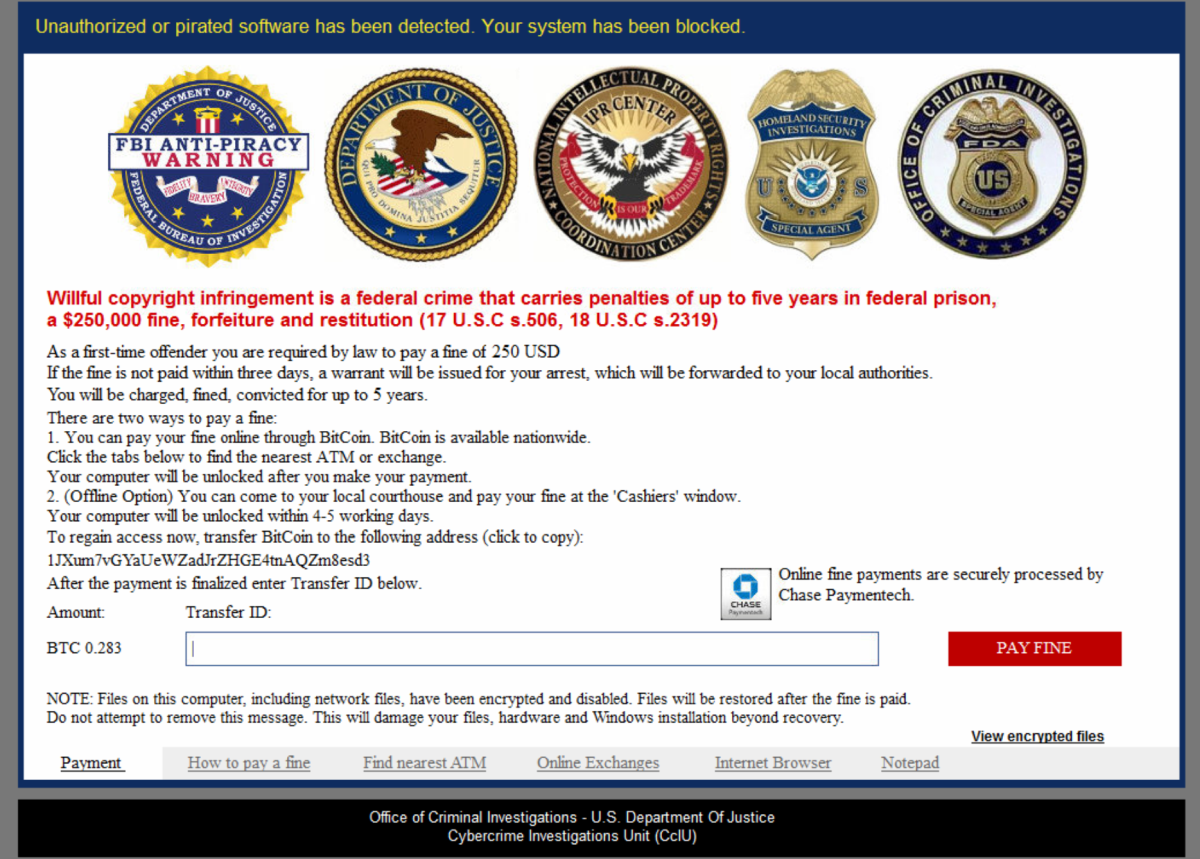
The screenlock shows a warning that localized authorities have found pirated software on the system and ask for a ransom payment in Bitcoin.
Aftermath
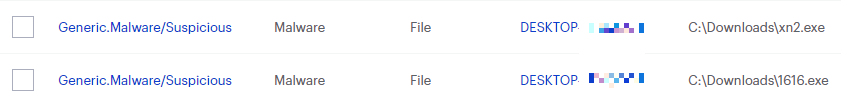
Virlock.Ransom.FileInfector.DDS often renders the infected system useless because it also infects executable files. This makes cleaning an affected machine very hard.
Home remediation
Malwarebytes can detect and remove Virlock.Ransom.FileInfector.DDS without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Take note, however, that removing this ransomware does not decrypt your files.You can only get your files back from backups you made before the infection happened.
Business remediation
How to remove Virlock.Ransom.FileInfector.DDS with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.

On the Quarantine page you can see which threats were quarantined and restore them if necessary.
All component/technology detections are passed to the remediation engine for complete removal from infected systems. This industry leading technology uses patented techniques in identifying all cohorts or associated files for a single threat and removes them all together to prevent malware from resuscitating itself. If you are using Malwarebytes Ransomware Rollback technology, it allows you to wind back the clock to negate the impact of ransomware by leveraging just-in-time backups.





