VirLocker is in no way new, it has been making a mess of victim’s machines for quite a few years now. VirLocker was the first example of a mainstream polymorphic ransomware and it left no expense of misery to its victims.
VirLocker can of course be propagated like any other malware from its author, but VirLocker has a trick up its sleeve when it comes to infecting other users. Because every file that VirLocker touches becomes VirLocker itself, so many users will accidentally send an infected version of a file to friends and colleagues, backups become infected, and even applications and EXE’s are not safe. Basically, when getting infected by VirLocker, you can no longer trust a single file that is on the affected machine.
This presents a problem when attempting to clean up the machine, because nothing can be trusted and every tool you use is dirty. Even attempting to download a tool to help you can prove a problem, because VirLocker will attempt to infect the new file before it is even opened if VirLocker is running on the machine.
However, if you find yourself infected with this variant DO NOT attempt to remove it yet! Not only does this article discuss the ransomware and how it works, but it will also show you how you can get your files back without paying the ransom.
Polymorphic functionality of VirLocker
VirLocker’s polymorphic abilities are a headache for everyone involved, researchers, victims, security companies, and more. Every time VirLocker adds itself to a file, the file is practically different in many ways than any other version of itself. VirLocker can add “Fake Code” to itself in certain sections to cause the file to be different, it can use different API’s in the main loader of the malware to avoid section fingerprinting, it can use different XOR and ROL seeds to make the encrypted content of the exe entirely different, and more. This level of polymorphic functionalities makes it astonishingly hard to deal with. When even the unpacker stub is different in every file, which could typically be used to fingerprint every variant, it only leaves behavior and heuristics as a possible method of detection.
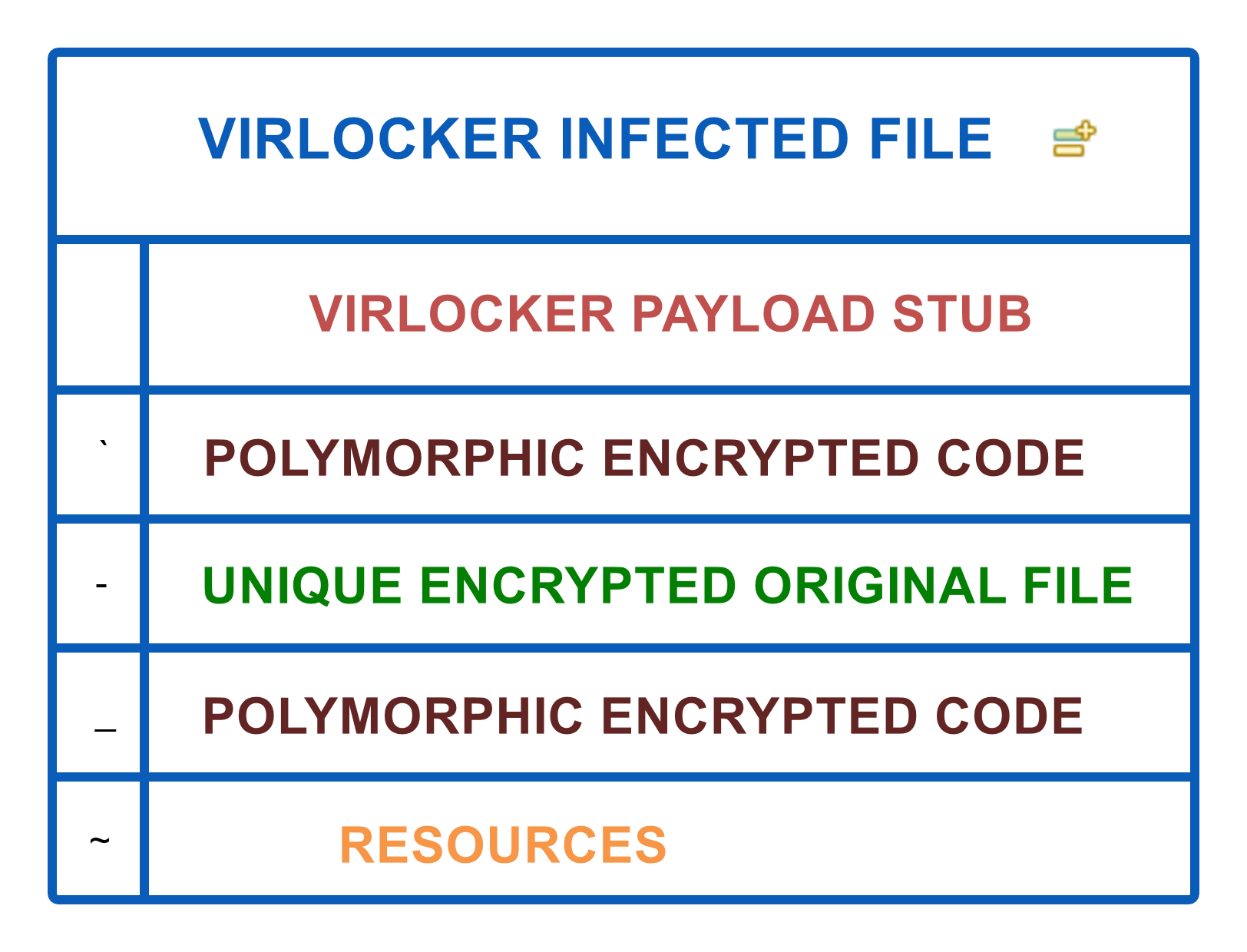
As you can see with the above graph of a sample VirLocker infected file, if the payload stub can be different each creation, and the encrypted code is always seeded different, the embedded original file will of course always be different, depending on the file it attacks, and the resources are just a small icon of the original file it attacked. This leaves very little that is suitable for detection.
VirLocker’s execution chain
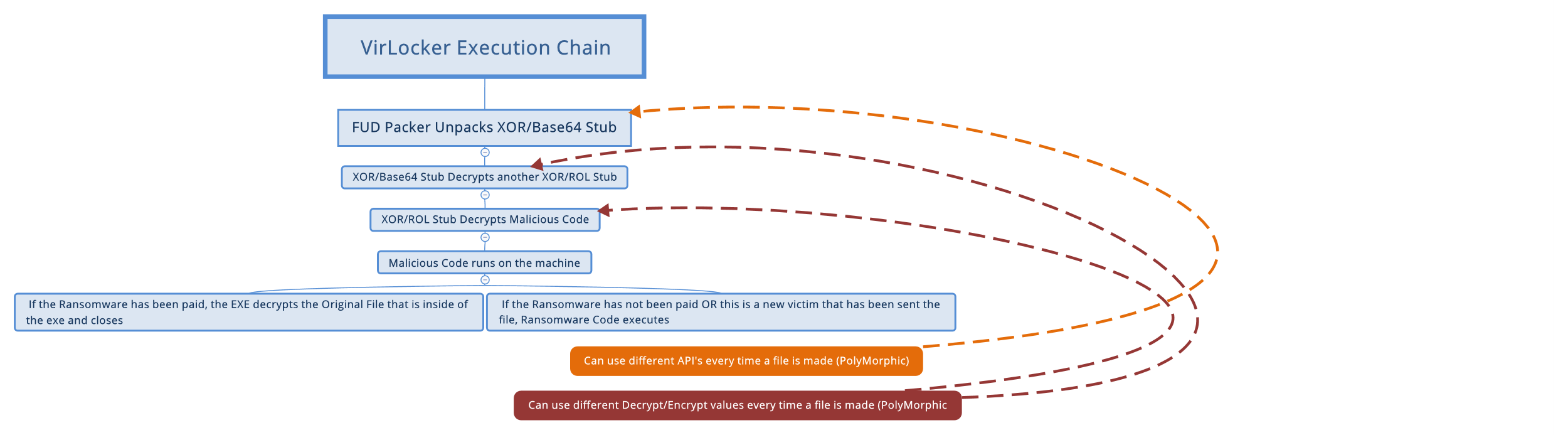
VirLocker’s execution is anything but simple and really reflects more of a mix of multiple protection types we have seen in single case ransomware scenarios. When the infection is executed, the FUD packer (which can be in some ways polymorphic itself) unpacks the first decryption function which is a mixture of Base64 and XOR and is always differently seeded. This new decryption function then decrypts another new decryption function that is a mixture of XOR/ROL and is always differently seeded. This decryption function then finally gets to the malicious code intended to run on the machine.
At this point the ransomware checks if it has already infected the machine, and if so, has it been paid? If it has been paid, the ransomware then becomes benign, and simply decrypts and extracts the original file that it had embedded inside of itself, and closes. If the user has been infected, but hasn’t paid, it simply opens the ransomware screen locker again, if it’s not open.
If it is a new victim, the ransomware opens the file embedded inside itself to make the user think all is well. For example, if the user B received a picture from their friend, user A, that was infected, once user B opens the file, the ransomware will show them the embedded intended picture, but then continue to infect the machine in the background. This is the background to how this ransomware self-replicates itself.
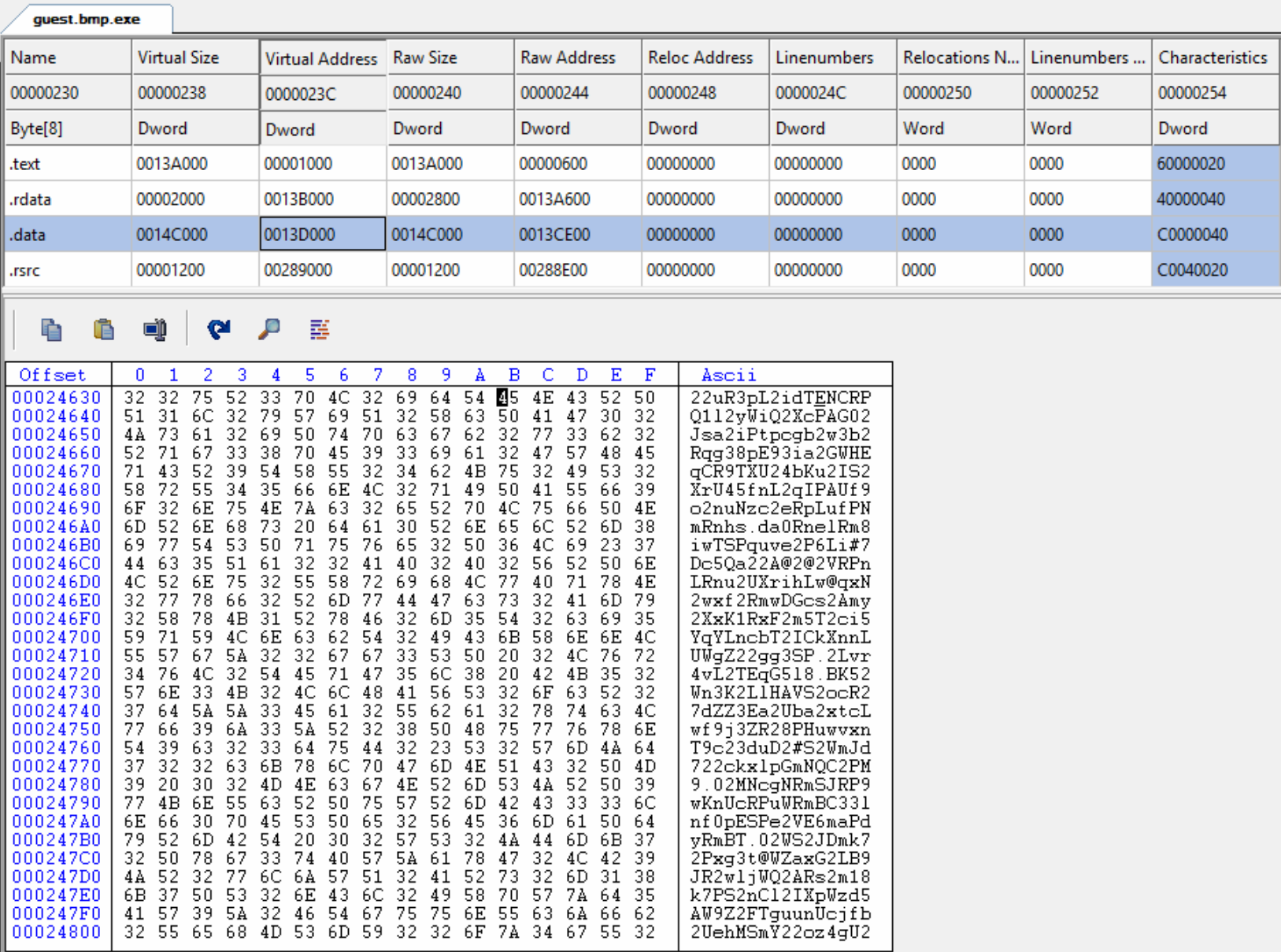
Example of what the original good file embedded in the virus looks like.“>
VirLocker overview

The image above shows the journey and issues that VirLocker presents. Not only is the virus hard to detect, it also has methods to continue existing without the help of the malware author. If anyone ever infected by VirLocker happened to send out any files after they were infected, thinking it was just a screen locker, those files will infect more people. This continuous loop of infection can cause VirLocker to spread like wildfire.
Upon opening VirLocker, it will add itself to nearly every file on the machine, ranging from mere pictures all the way to actual applications. Clicking on these files after the infection will only cause the ransomware to run again, or in the case of a new victim, infect them. Only after “Paying” the ransom, will these files extract their inner “Good Version” on the machine.
With all the madness that this ransomware causes, it has proven to be an amazing infection spreading method. Imagine you get this infection and think it’s just a screen locker like you have heard about. You somehow manage to remove the infection and think you are in the clear. Because extensions are turned off, you do not see that EVERY file on your machine now has a .exe extension added to it behind its original extension. You send your resume to a company you’re applying to and soon enough that whole business is infected.
VirLocker “Decryption” and clean up
DISCLAIMER: If you are infected with VirLocker, you are dealing with a very live and messy piece of malware. It is extremely easy to accidentally cause it to travel to other machines. It’s highly recommended before performing the steps below, that you isolate the machine from any other hardware or network. We cannot be responsible for anything that may happen to your or others machines while following the below instructions because of the nature of the malware.If you find yourself infected with VirLocker and want your files back, DON’T REMOVE IT RIGHT AWAY. We need to trick the infection into thinking that you have paid the ransom, so you may get your original files back first. If you have removed the infection, clicking on any of the “encrypted/infected” files will bring up the screen again that VirLocker uses.
IF YOU HAVE ALREADY CLEANED THE MACHINE, CONTACT PROFESSIONAL HELP BEFORE TRYING TO REINFECT IT. DO NOT REINFECT THE MACHINE TO SIMPLY FOLLOW THESE STEPS.
Because of how messy VirLocker is and seeing how it doesn’t even have a cleanup method or decryption method internally, our goal here is to help you get back your important files, and completely reformat the machine afterwards. This post will only focus on helping you get back important files. After this is completed, a complete reformat should be done, since nothing on the machine should be trusted after this infection.
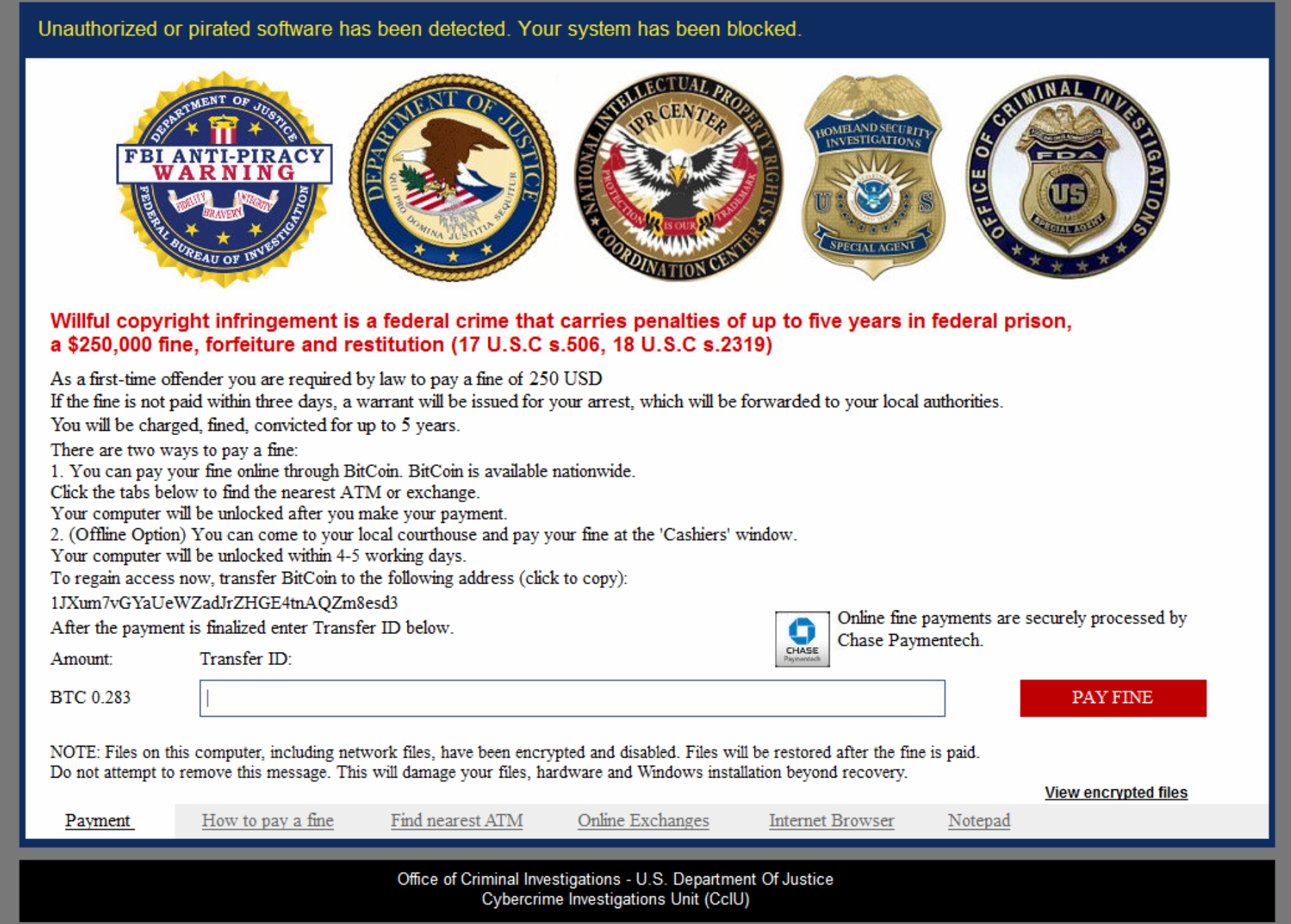
VirLock has screens that look like the above. They seem to always impersonate some type of legal authority. This one claims to be the Office of Criminal Investigation, where past versions called themselves “Operation Global 3” with different legal emblems.
The important part is the “Transfer ID:” text-box. We have found that any 64-length string will be accepted here as a real payment on this latest version of VirLocker. So, on your infected machine type the following into the Textbox:
0000000000000000000000000000000000000000000000000000000000000000
(That is 64 Zero’s.)
After you have done this, hit “Pay Fine”. This will cause the Ransom Lock Screen to disappear. VirLocker now thinks you have paid the ransom. Because of this, any of your infected files, upon double clicking them to open them, will no longer start the ransomware, but instead extract the original file inside of it.
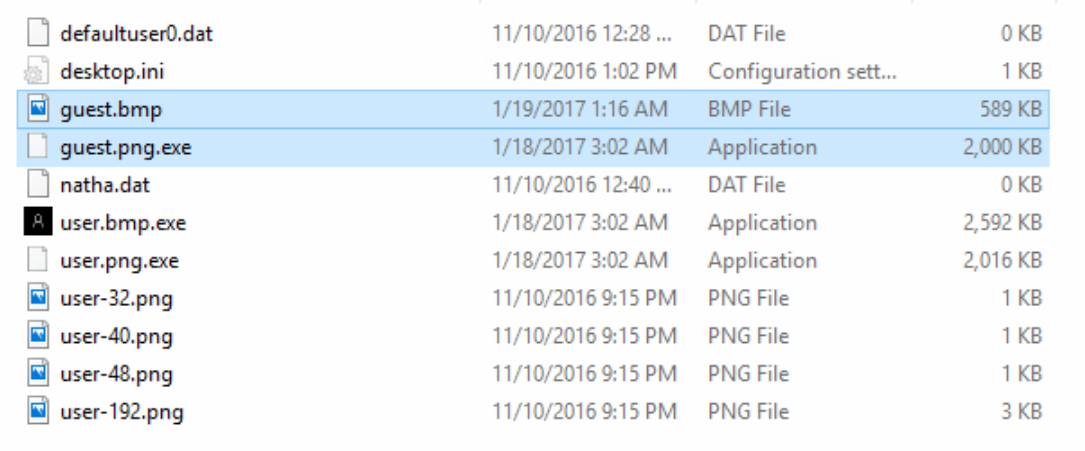
As you can see in the image above, clicking on the infected file “guest.bmp.exe” extracted the “guest.bmp” file, which is the original good version of the file. You may now use a non-important USB drive to back up all the files that are important and that you need recovered from this nasty infection.
ENSURE TO NEVER PUT ANY .EXE FILES ONTO YOUR BACKUP DRIVE WHEN DOING THIS, THIS CAN CAUSE THE INFECTION TO SPREAD. ONLY BACKUP THE EXTRACTED ORIGINAL FILES THE EXE’S SPIT OUT!
ONLY PERFORM THIS ACTION ON THE MACHINE YOU ENTERED THE “0’S” ON THE LOCKSCREEN. OPENING THE EXE FILES ON ANY OTHER MACHINE WILL INFECT THEM!
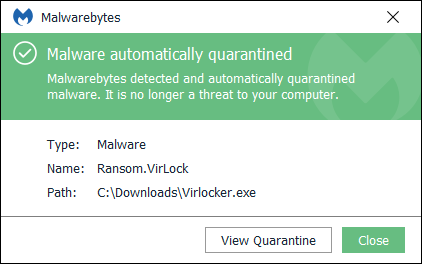
After you have obtained the files that are important to you, the machine should be completely wiped at this point. To avoid this type of infection in the future, consider using an anti-ransomware solution like Malwarebytes, which has anti-ransomware functionalities built into it!
Hashes used in this analysis:
d438f51fbb56c06c8d910344ceed79504360162c78559254afa7b3fa27eaf763
bfa26552ae53c77a4ff49177e1b27dc318ee4102ca7281aa7dd3afdeccbe58ff
932d7b340cb58cb635b2088421dc73bc1fe079c4b5cee940b2ad8e4dcbfe0f04
a9937f7b85a12f5bc2eda8240c9fa5972275b50bc851aa736402b5f166ef3b03
4d0c238a2cd530b6c9a724af5406dc50cf31988584d34cacf46ac9b2c5f63bcc
ff56e378a221100b160fae0d5cd4f94cb34c14b4e9b932c159c3c95c00526a35
505d86f5181bdd13e473bfa4ab5edbc4d9a6b4ba75f30404ea4966ff7a8ee8da
48abe6cdf1a3f3bc0934abbfaef189938e7ee981f77340cf2ca8b57fdad21a7e
6372a2d90dec71b21fa5991b34289dfd2e8777bca9f51e5991dce03c4e861cd6










