For the past couple of years, Office documents have largely replaced exploit kits as the primary malware delivery vector, giving threat actors the choice between social engineering lures and exploits or a combination of both.
While today’s malicious spam (malspam) heavily relies on macros and popular vulnerabilities (i.e. CVE-2017-11882), attackers can also resort to zero-days when trying to compromise a target of interest.
In separate blog posts, Gigamon and 360 Core Security reveal how a new zero-day (CVE-2018-15982) for the Flash Player (version 31.0.0.153 and earlier) was recently used in targeted attacks. Despite being a brand new vulnerability, Malwarebytes users were already protected against it thanks to our Anti-Exploit technology.
The Flash object is embedded into an Office document disguised as a questionnaire from a Moscow-based clinic.
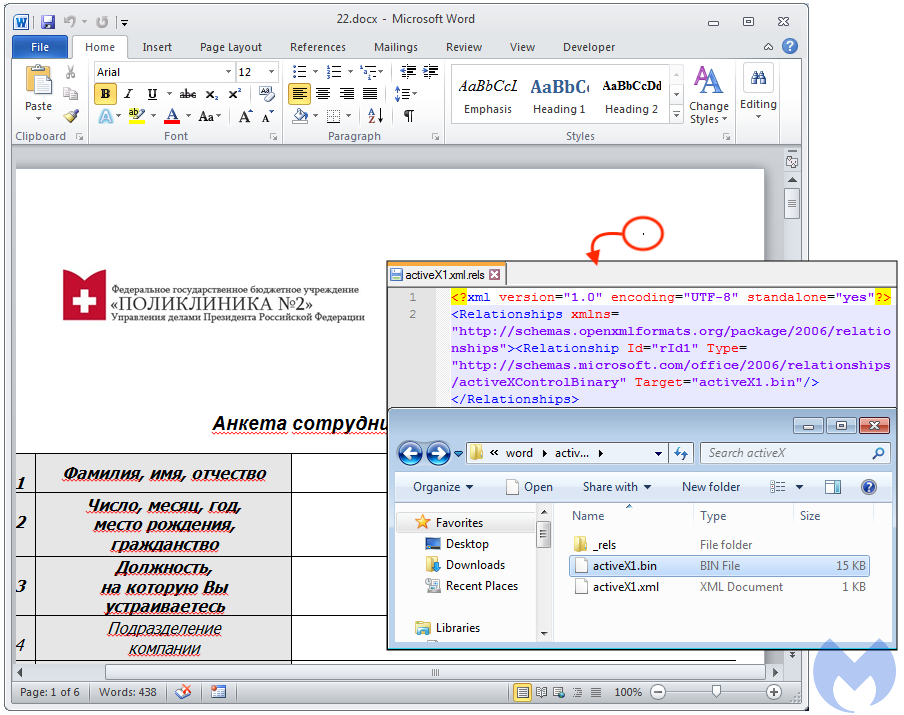
A dot reveals an embedded (and hidden) ActiveX object
Since Flash usage in web browsers has been declining over the past few years, the preferred scenario is one where a Flash ActiveX control is embedded in an Office file. This is something we saw earlier this year with CVE-2018-4878 against South Korea.
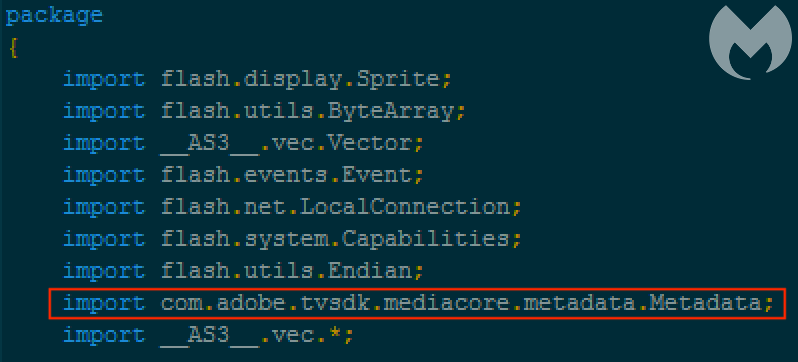
360 Core Security identified the zero-day as a Use After Free vulnerability in a Flash package called com.adobe.tvsdk.mediacore.metadata.
Victims open the booby-trapped document from a WinRAR archive that also contains a bogus jpeg file (shellcode) that will be used as part of the exploitation process that eventually loads a backdoor.
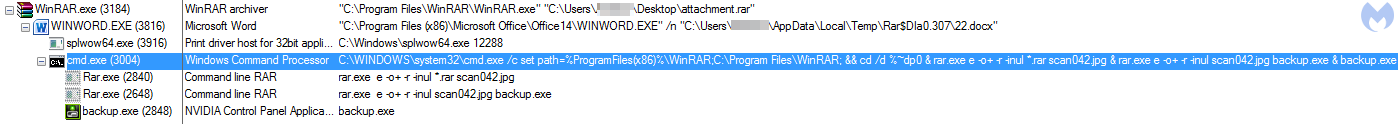
Exploitation flow showing the processes involved in the attack
As Qihoo 360 security researchers noted, the timing with this zero-day attack is close to a recent real-world incident between Russia and Ukraine. Cyberattacks between the two countries have been going on for years and have affected major infrastructure, such as the power grid
Malwarebytes users were already protected against this zero-day without the need to update any signatures. We detect the malware payload as Trojan.CrisisHT.APT.
Zero-day attack flow stopped by Malwarebytes
Adobe has patched this vulnerability (security bulletin APSB18-42) and it is highly recommended to apply this patch if you are still using Flash Player. Following the typical exploit-patch cycle, zero-days often become mainstream once other attackers get their hands on the code. For this reason, we can expect to see this exploit integrated into document exploit kits as well as web exploit kits in the near future.










