Author’s Note: We at Malwarebytes continue to do our part in educating our product users and constant blog readers about day-to-day online threats and how they can avoid falling prey to them. “PUP Friday”, our latest attempt at getting users acquainted with files they may need to watch out for in the Wild Web, offers an in-depth look at some interesting and quite notable potentially unwanted programs (PUPs). Expect to see this type of content pushed out twice a month at the end of a work week.
For this week’s PUP Friday post, we’re going to take a look into two pieces of programs claiming to be two different security software, being housed in a domain purporting to be a safe antivirus download hub. The destination in question, however, has been known to serve a fake Malwarebytes installer. The domain is antivirus-dld[DOT]com, and users must avoid visiting it or block it with their browsers.
Below are screenshots of its subdomains where users can supposedly download the AVG and AdwCleaner programs:
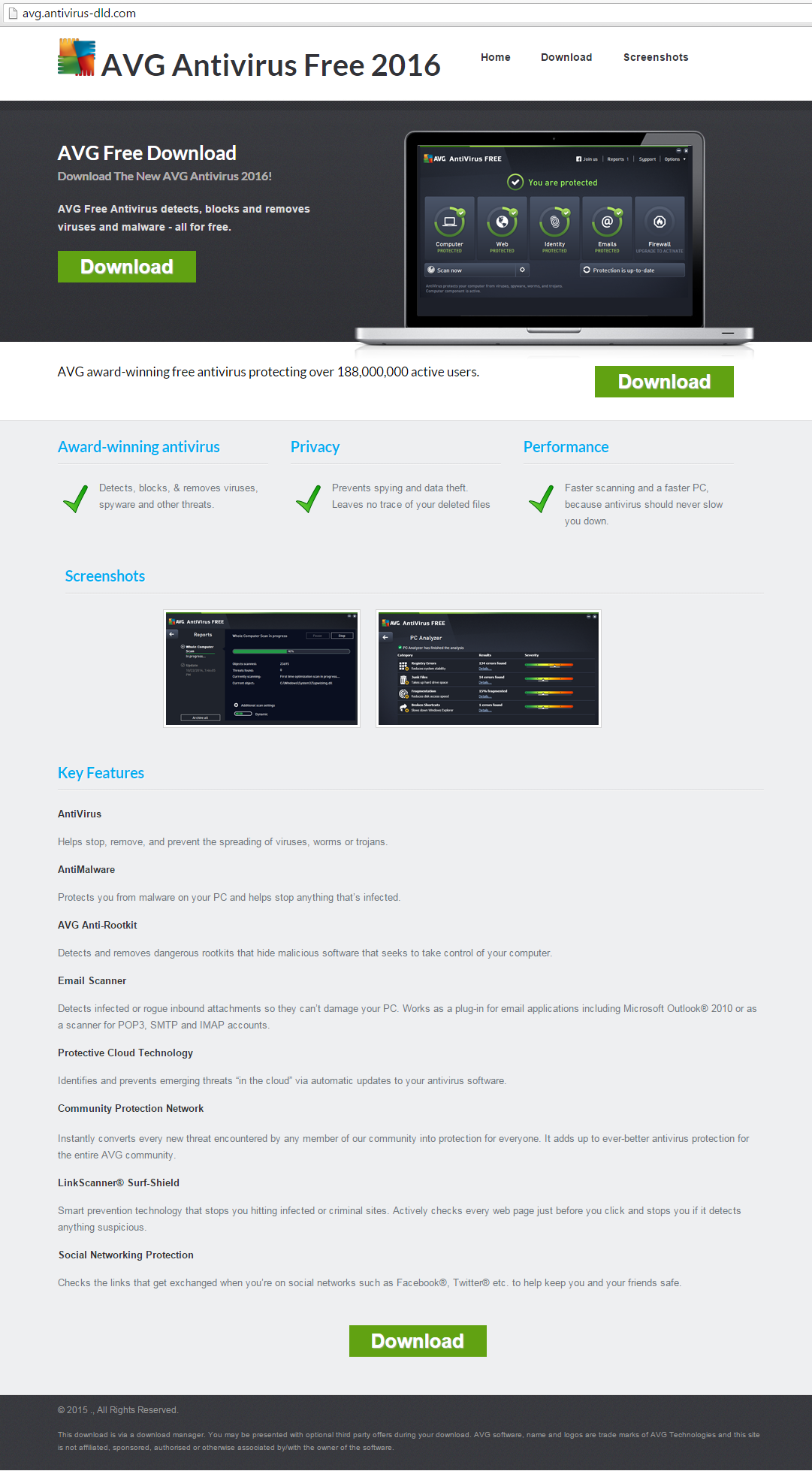
click to enlarge
click to enlarge
Although both installers show differences in file names and hashes, they exhibit more identical markings than what we see on the surface. Malwarebytes Anti-Malware (MBAM) detects both files as PUP.Optional.BundleInstaller. AV engines detect these as variants of the SoftPulse family.
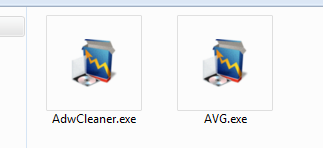
Below is a sequence of events in a slideshow when we tested AVG.exe.
As this “Thank you” GUI window is displayed, the supposed program, in this case AVG, is then downloaded and installed automatically. Users can’t see this happening at first because the installer’s GUI is overlaying the real program’s GUI.
click to enlarge
Immediately after installation, the default browser opens to reveal an advertisement of an online dating site. We reckon that various ads are randomized.
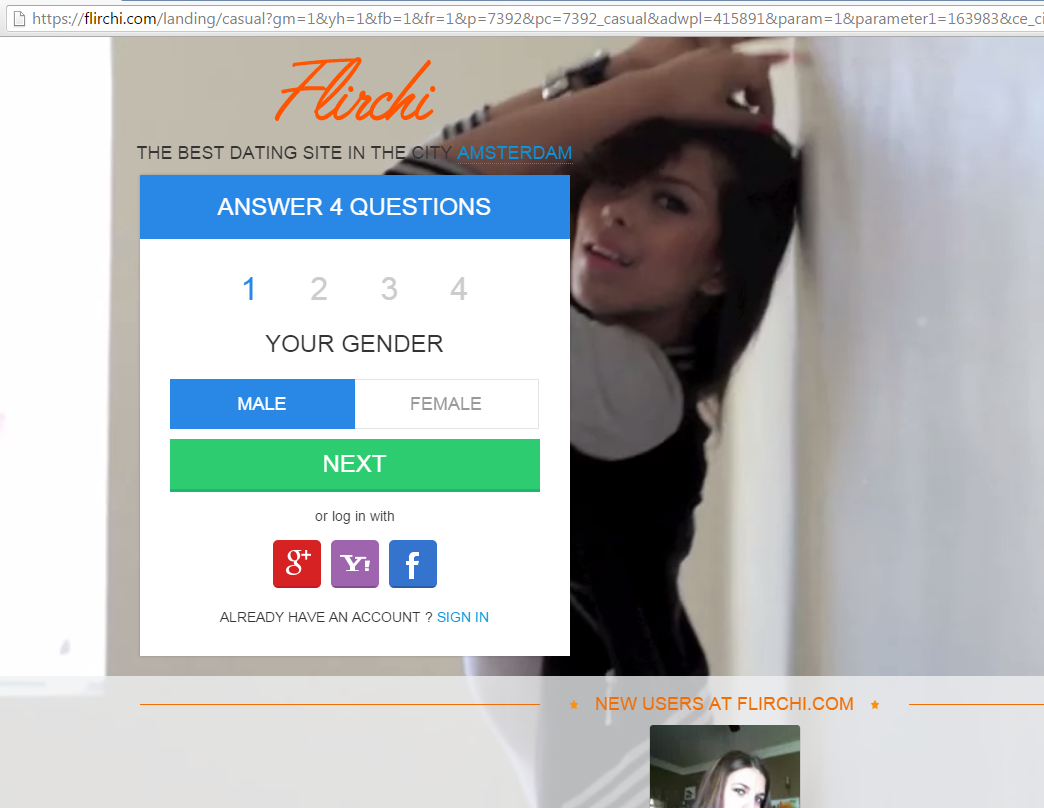
click to enlarge
Funnily enough, after downloading the actual AVG program, it was able to scan and detect the installer file that led to its download to begin with.
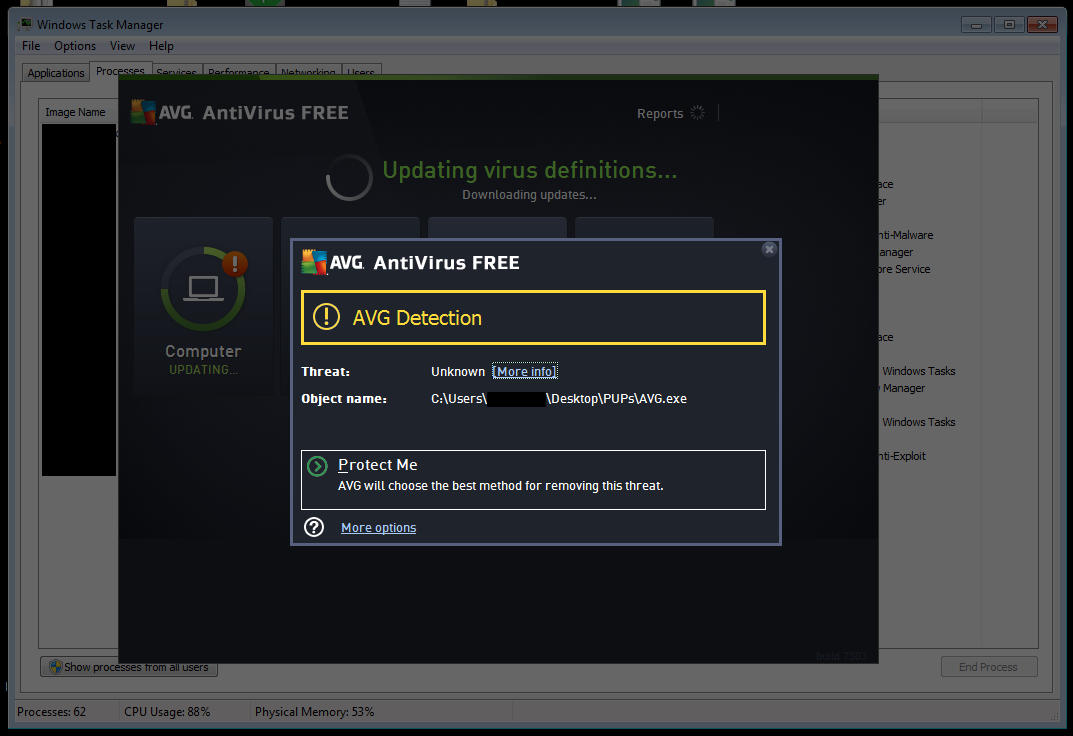
click to enlarge
The file AdwCleaner.exe undergoes an identical installation sequence as well. However, instead of downloading the legitimate program, like what AVG.exe has done, it directs users to a site (screenshot below) where they can download the file themselves. So much for using an installer.
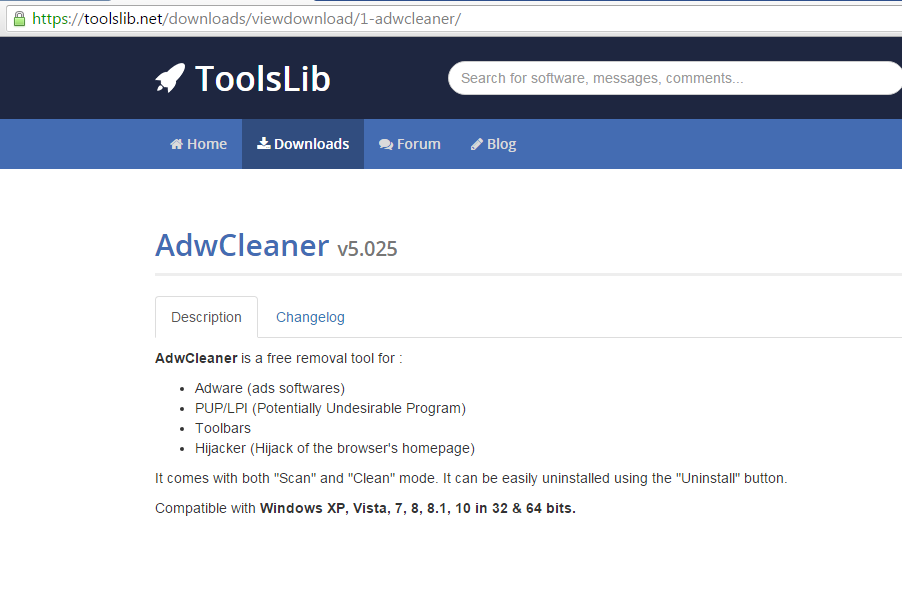
click to enlarge
There are almost non-discernible text links at the bottom part of the installation GUI. Below is an enhancement of that portion:

click to enlarge
Clicking any of these links directs users to magno2soft[DOT]com, a domain that the Google Chrome browser blocks, tagging it as malicious. Additionally, we did a quick look up of their “24/7 free support” phone number—(+1) 844 326 2917—to see if something comes up. It turns out that this number is also used by other domains, such as (but not limited to) the following:
- 4f1le[DOT]com
- defilesimple[DOT]com
- filesoftwred[DOT]com
- jmagno[DOT]com
- legal-conditions[DOT]com
- magnodownload[DOT]com
- moresoftwr[DOT]com
- myfiletor[DOT]com
- mymagnocfile[DOT]com
- needsoft4wer[DOT]com
- newsoft4ter[DOT]com
- newsoftwrth[DOT]com
- nwfields[DOT]com
- packfilebox[DOT]com
- promagno[DOT]com
- themagno[DOT]com
- themagnosoft[DOT]com
- thesoftwred[DOT]com
- twof1ler[DOT]com
- youdllfile[DOT]com
We have also noted that their contents are also identical to Magno2soft’s. Be advised to not visit these sites as some of them automatically download an executable file.
For a technical but comprehensive view of what the files actually do once executed onto a system, below are links to incident response reports that you can browse, courtesy of Payload Security’s sandbox:
If you’re looking for download sites of programs you wish to install onto your machine or simply try out, you, dear Reader, would be better off dropping by their official websites. Domains like antivirus-dld[DOT]com may only appear legitimate, but they’re just hubs distributing pieces of software you may not want lurking in your hard drive.
Jovi Umawing










