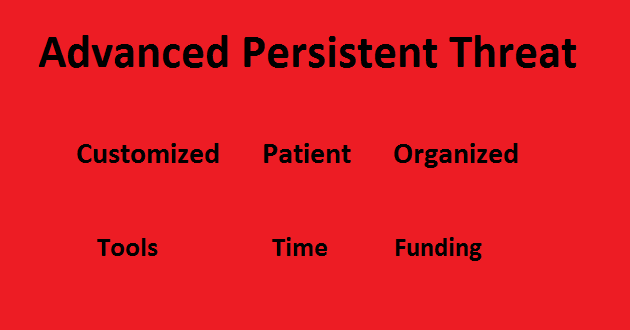
An advanced persistent threat (APT) is a prolonged, aimed attack on a specific target with the intention to compromise their system and gain information from or about that target.
The target can be a person, an organization or a business. When these threats were dubbed their targets were governments and military organizations. The word threat doesn’t mean to imply that there is only one kind of malware involved, because an APT usually consists of several different attacks.
Too many professionals in the security field an attack only qualifies as an APT if it is initiated by a government (agency) or a similar organization. Given the needed resources and patience this certainly make sense.
So what does that mean in the current threat landscape?
Threat actors use different “tools” and methods to get a foothold and to widen the breach once they are in. When it comes to stealing information, an important part of the job is to keep the breach a secret. This is because often the stolen information will lose its value rather fast once the object of the breach is aware of the situation.
Obviously, it’s also important to hide the identity of the attackers, as APT attribution could lead to some real world conflicts. So the attackers will want to hide their tracks. It is not uncommon to see the use of unpatched vulnerabilities (zero-days) in this kind of operations.
Accomplishing a foothold. Get a target to run the malware on his system which is inside the targets network.
- Carefully widen the scope from the created foothold. For example reconnaisance of the network from an infected computer. This includes putting malware and other tools on the compromised system and hiding them.
- Find and steal the sought after or other valuable information. To do so, it may be necessary to raise the privileges of the compromised ssytem in the network.
- Once a firm grip on the network is established it may be necessary to move or widen the entry points in the network so a more permanent access to the information is secured. If there is no need for a permanent monitoring, the tools will usually be removed to cover up the tracks. Sometimes a backdoor is left in place to make a return easier.
Groaning security professionals
The reason security researchers will groan when they hear the expression APT is the fact that some people tend to use it in cases where the threat does not meet the requirements that we specified in our definition.”
Apparently, it sounds less bad when you explain that you have been breached by something “Advanced” rather than by some malware that should have been detected months ago.
For example a worm that attacks only computers that run a certain kind of software, almost exclusively used in hospitals is not an APT. It is targeted at a type of organizations and not at a particular organization.
Summary
This article explains that Advanced Persistent Threats are specialized and prolonged attacks aimed at specific targets. They are usually sponsored by nations or very large organizations.
Links
CyberCriminals and their APT and AVT Techniques
Pieter Arntz











