We all know about tech support scams by this point. We know how they cold call, lie their way into your computer, and steal your money. Unfortunately for the scammers, banks know this as well, making it quite difficult at times to maintain an account to store the criminal’s ill-gotten gains. So how does the enterprising criminal cash out with your money? Let’s take a look.
High-risk payment processors
When a business owner is involved with a line of work that traditional payment processors don’t want to be involved with—typically pornography, pharma, and gambling—they use high-risk processors. In exchange for the perceived higher risk of processing payments in industries known for fraudulent activity, the processor takes a higher fee. The traditional tech support scam model used to rely heavily on these companies, typically through an Indian intermediary to offer an extra layer of anonymity.
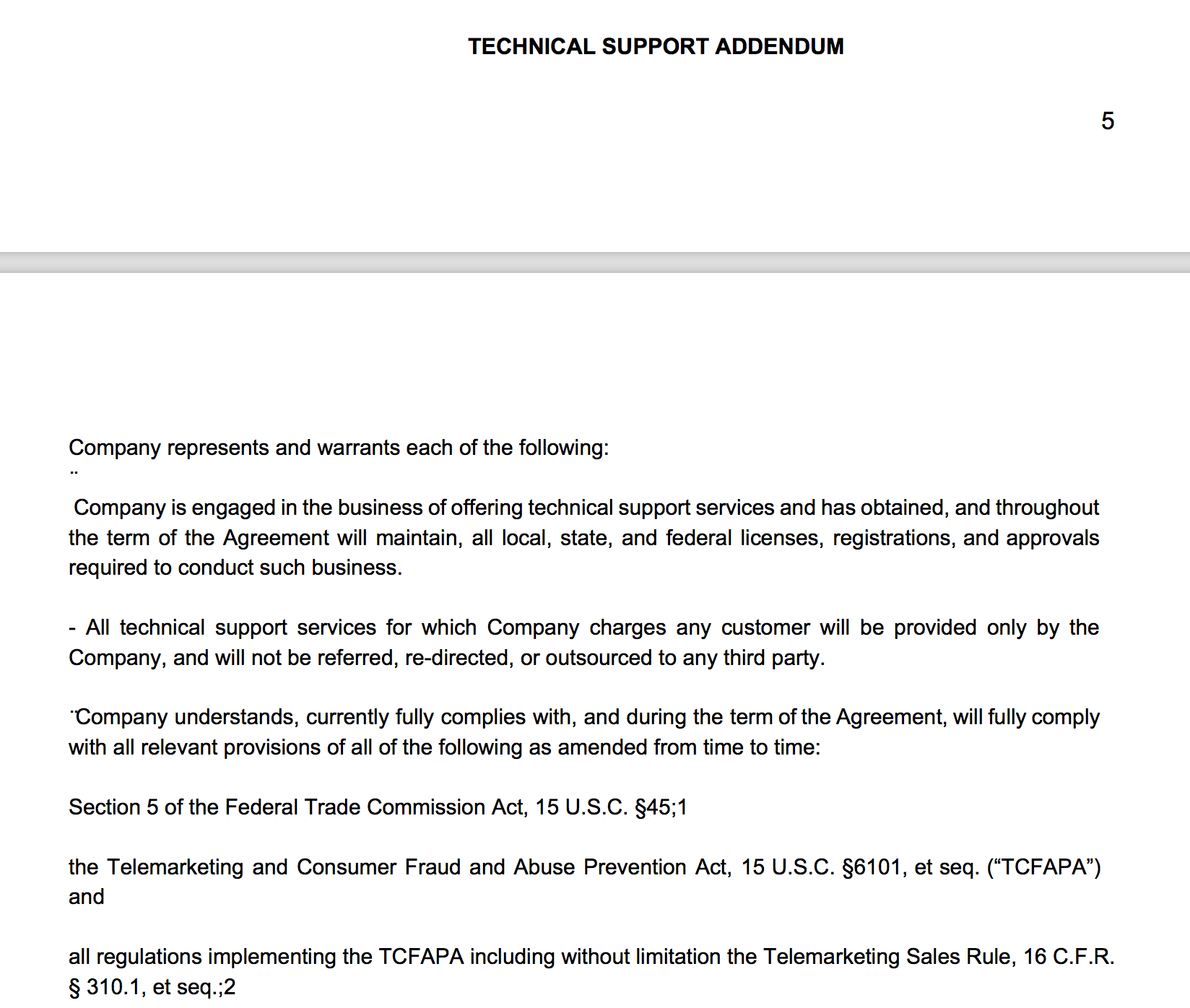
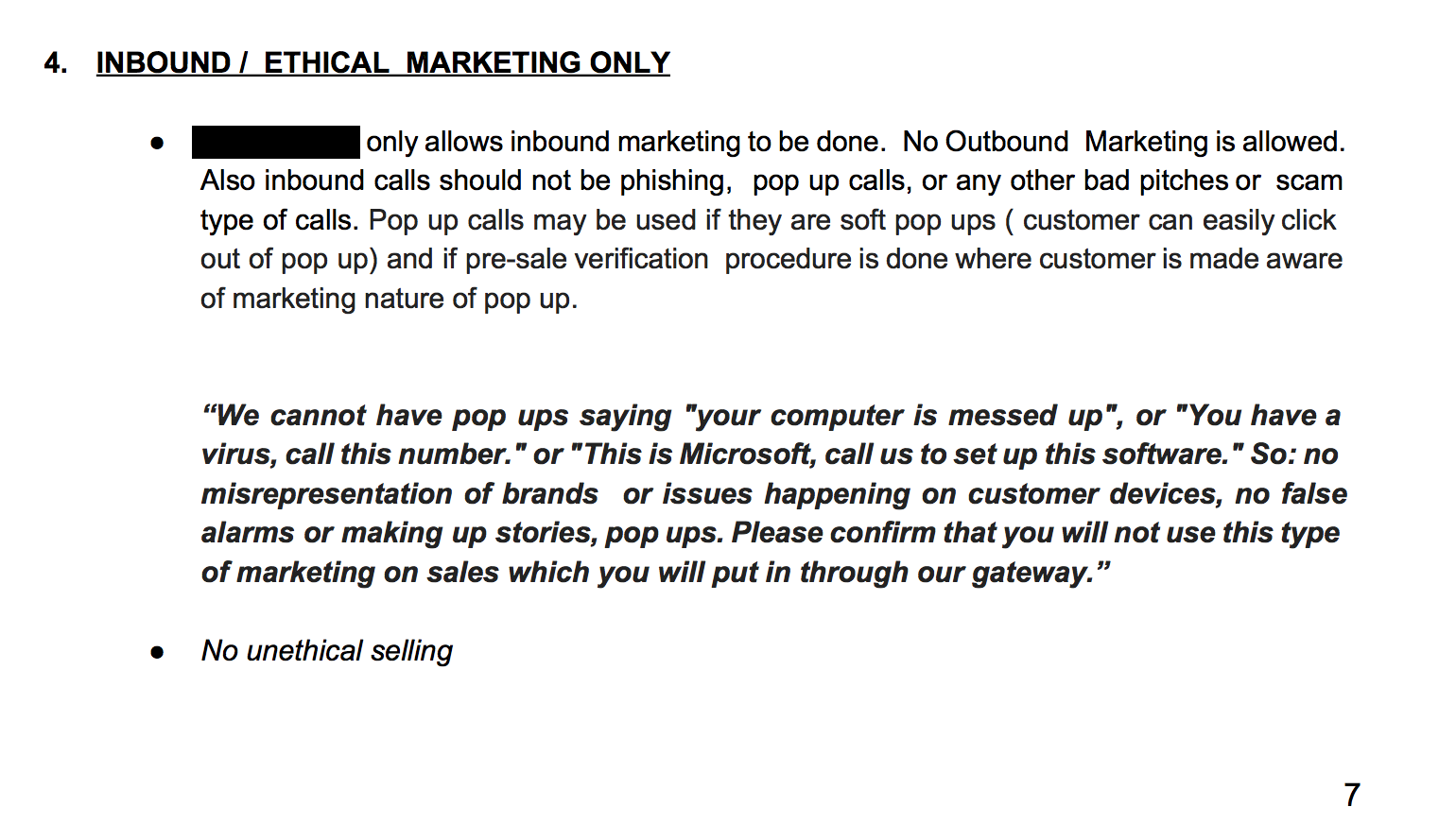
However, as the spotlight on tech support scams grew brighter and victims increasingly initiated chargebacks, high-risk processors have increasingly dropped overseas tech support companies in order to protect their relationships with more legitimate businesses, as well as the credit card companies who monitor customer chargeback rates. The processors that haven’t given up tech support yet tend to levy extra restrictions against overseas customers in their contractual agreements, as demonstrated in the example contract below.
So barred from traditional banks and losing access to high-risk processors, tech support scammers have gotten a little creative. An increasingly common method we’ve seen for payment is Apple or iTunes gift cards. The idea being the scammer gets a commodity that is easily laundered on the dark web and the victim sees Apple on their credit card statement, rather than FAKE COMPANY XYZ. This has the added benefit of making it extra tough for the victim to produce evidence that ties back to the scammer.
Apple has some pretty good advice on the subject here.
Suffice it to say, legitimate tech support companies do not do this. Malwarebytes has observed tech support scammers using Apple/iTunes gift cards, Amazon gift cards, Bitcoin, and even sending a FedEx guy to physically pick up a check. Non-standard payment methods like these are usually a pretty good signal that the tech support business in question has a hard time getting access to a credit card processor and you probably shouldn’t do business with them.
Lastly, scammers might collect payment using direct bank transfers via Automated Clearing House (ACH). Criminals love this method because it only requires two pieces of information to work—you account number and a routing number. Also, non-business victims only have 60 days to report losses in order to recover funds. More on ACH fraud here.
So if you’re ever on the phone with a support company that is insistent that you pay with third party gift cards, ask the operator, “Why can’t I use my credit card?” You might get some very creative answers. But the best defense when encountering this is to simply hang up the phone. If you’ve allowed the scammer remote access to your computer, close the window as well, or just disconnect your internet. For more on how to stay safe from tech support scams or find out more on what to do if you’ve had a run-in with them, check out our post here.