There are two kinds of spam associated with social media. There are spam ads that actually live on social media, and there is spam that comes in your inbox, courtesy of social media. Both thrive by using data from your social media accounts. But how do spammers know how to target you and send you the mails that you are most likely to click on?
There is a real chance that you revealed that information yourself. To understand the relationship between the spam you get in your mailbox, your social media presence, and the ways that criminals try to scam users, you must first understand a few basic principles about how advertising works on social media.
Interest-based advertising
First of all, let’s differentiate between the spam we see on social media and the spam that we get in the mail, but has a relationship with what we interact with on social media. Spam that we see on social media is called interest-based advertising, which we have talked about before. It is also known as personalized or targeted advertising.
This is the foundation of what people perceive as “Facebook and Google knowing about every search I do and every article I read.” If you are interested in limiting the number of personalized ads you see on social media, Google offers an opt-out of interest-based Google ads in this article.
There are several different options for opting out of interest-based advertising. For example, if you do not want to see any advertisements on the sites you visit, you should look into installing an adblocker. Keep in mind that many sites can only stay in business because they are funded by advertising—that doesn’t mean they have the right to invade your privacy, though.
Logging off
If you are a Facebook user and wondering whether it pays off to log off after every session, according to Facebook, it does. Logging off should theoretically prevent social media sites from picking up on your browsing habits to serve you ads. But others have noticed that devices that come with Facebook installed transmit mysterious information in the background to Facebook’s servers—even when the user is not on Facebook. One thing is sure: as long as you have your Facebook timeline open in a browser and you are using the same browser to surf, Facebook will pick up on your interests.
The Facebook pixel
But that is not the only way companies utilize social media for targeted advertising. The Facebook pixel is another marketing tool. A pixel is a tiny object that can be placed on websites that use re-marketing based on which other sites their visitors have looked at. To the visitor these pixels are invisible, unless they have an anti-tracking tool installed.
If the visitor is considered interesting enough for the websites’ company, a targeted advertisement will be placed on the visitors’ Facebook page. This is why you will regularly see advertisements from companies whose website you have visited recently. For the webmaster, the pixel offers a lot more perks, but for the visitor it simply means more data mining is taking place.
Share, Like, Tweet, +1
Every site (including our own) that has buttons to share or promote an article on social media does send information about you to their respective owners (again, unless you are using an anti-tracking solution). Based on what articles you share, like, or otherwise engage with, social media networks can spot patterns and recognize your interests.
Spam based on social media data
While interest-based advertising is something we have learned to cope with, even though it may seem scary how much “they” know about us, it is far less dangerous than the spam you may receive based on your online behavior. Why? Let’s dive in.
Development of spam
While the huge, blanket spam campaigns that ensnare millions of email addresses still exist, todays threat actors are well aware of their diminishing effects. A targeted and well-constructed mail that looks like it comes from your bank offers a much bigger success rate then one coming from some random bank you have never done business with. And the same is true if the spam pretends to be from one of the online shops that you have given a thumbs-up to on social media.
A successful, targeted spam email trumps an annoying breach of trust that still delivers mostly legitimate ads. All it takes is one email to fake out an unsuspecting user into providing their own crucial information to criminals, who can then infect your computer, steal your data, or simply spy on you. But it’s got to be pretty difficult to get that information from users, right?
How do they know?
Providing spammers with the knowledge to scam you more effectively is probably not what you had in mind when you joined your social media network(s).
But of course, we never reveal sensitive, personal information on our social media accounts. Or do we?
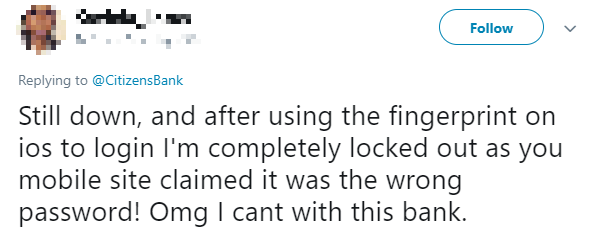
If some scammer had the email associated with this Twitter account, they could pull off a real convincing scam attempt. And if you are the intended target, the threat actors will have the email addresses they need.
It is actually terrifying to know how the tiniest amount of information in the wrong hands can have a devastating impact on your life. Identity theft is a possible nightmare lurking around the corner. Once criminals have a starting point, they can use data from various breaches to gather more intel about their victims.
Recognizing spam: fake login requests vs. Nigerian Prince
There are two main categories of fraudulent spam: fake login requests and the Nigerian Prince variety.
The first category can be very convincing, especially if the emails seem to come from your actual bank. But if your bank sends out emails soliciting login credentials, I would advise switching to another bank (because they shouldn’t be doing that).
The emails themselves will have convincing logos and even appear to come from email addresses belonging to the bank or a credit card provider. And the websites they send you to are exact copies (content wise) of the real one, even including a green padlock that makes the site look legit.
Before you check any such mail, remember that your bank should never send you such an email in the first place. But if you look for these signs, you will see right through them. And the signs apply to many other cases like Netflix or iTunes scams. Ways to spot a targeted spam campaign include:
- Comparing the domain in the email address to the one that your bank owns. You may spot (a small) discrepancy, such as slight spelling differences or random sub-domains.
- Hovering over the links in the email. Do they lead to your bank’s actual site?
- Checking the salutations. Does your bank address you with your first name or as “Dear customer”? Not likely. They will generally address you as Mr. or Ms. Last name.
Nigerian scams
These started out as ridiculous messages from a Nigerian prince who claimed, “We have a huge amount of money waiting for you here in a strange and far away country, and all we need from you is a little payment and some information to transfer it into your bank account.” Users duped by this scam would never see their original payment back, let alone the huge amount of cash promised to them. This type of scam has evolved to into many different stories and is nowadays also used to recruit money mules.
And, guess what? You don’t need a computer or email to get scammed either. It only takes a little bit of information, a good story, and a friendly victim to get scammed.
A real-world scenario
A woman gets a text from her brother telling her he has a new phone number, but now he can’t log in to his bank, and he needs to make an urgent payment. Can she do it for him? He’ll pay her back as soon as he has everything sorted. The message has her brother’s avatar and the story seems plausible. Not everyone will fall for this, but probably enough to make it worth trying. You don’t need to do much digging on someone’s Facebook profile to gather everything you need to spam and scam victims.
As much as it may pain you, don’t be that friendly person. In the last scenario, you should tell your brother to call you. That isn’t too much to ask if he needs your help that urgently, is it? And dump those scammy emails in the trash where they belong. Should you ever really be in doubt whether some email actually came from your bank, they won’t mind if you call them to verify that information. In fact, they will be glad that you were so cautious.
Now if only we could get everyone to be more cautious about what they share on social media.
Stay safe!