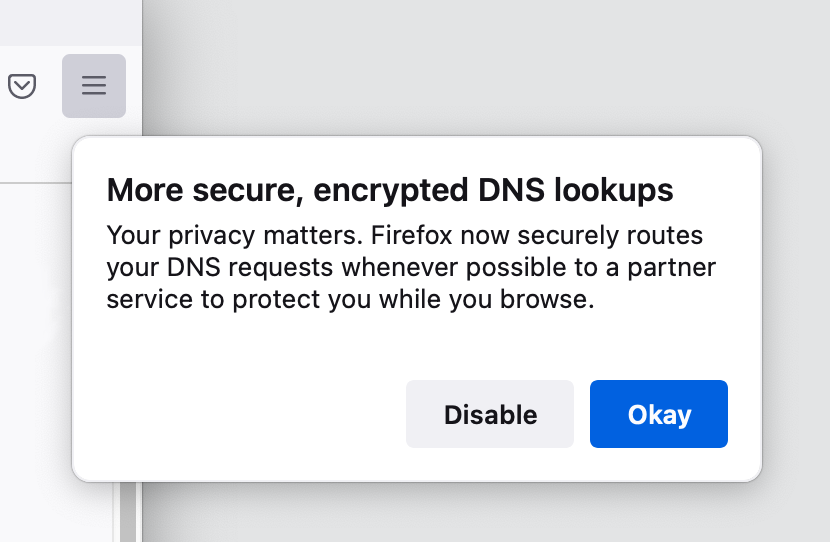
Firefox recently announced that it will be rolling out DNS-over-HTTPS (or DoH) soon to one percent of its Canadian users as part of its partnership with CIRA (the Canadian Internet Registration Authority), the Ontario-based organization responsible for managing the .ca top-level domain for Canada and a local DoH provider. The rollout will begin on 20 July until every Firefox Canada user is reached in late September 2021.
This announcement came five months after Firefox rolled out DoH by default for its US-based users.
The overall purpose of this rollout is to increase the privacy of all Firefox users by encrypting DNS requests. DNS requests are sent in plain text—meaning, any computer they pass through is able to see what website domains you’re looking up and likely visiting. This includes websites you visit over an encrypted connection, prefixed with https://. The DNS resolver the request is sent to also sees the DNS request, too. It needs to in order to convert the domain name users want to visit to the IP address equivalent for that destination. DNS-over-HTTPS is designed to shut out everyone else.
Because a DNS request has no encryption—again, regardless of whether the website you want to visit is encrypted or not—intermediates can monitor or modify DNS requests. This means that the organization you work for, your favorite coffee shop, or your ISP, can spy on your web browsing history without you knowing or letting you know what they do with the information.
“Today, we know that unencrypted DNS is not only vulnerable to spying but is being exploited, and so we are helping the internet to make the shift to more secure alternatives,” wrote Selena Deckelmann on Mozilla’s official blog. “We do this by performing DNS lookups in an encrypted HTTPS connection. This helps hide your browsing history from attackers on the network, helps prevent data collection by third parties on the network that ties your computer to websites you visit.”
The downside of encrypting DNS
Not everyone is a fan of DNS-over-HTTPS. To many, DNS-over-TLS is a more appropriate solution to the encryption problem but its “correctness” is also its great flaw. DNS-over-TLS communication (and nothing else) happens on port 853. Your ISP, or employer, can’t spy on your DNS requests if you use DNS-over-TLS but they can block port 853 and stop you from using it, leaving you no option but to revert to the unencrypted version of DNS on port 53, which they can spy on.
DoH communication happens on port 443, the port used for https:// web browsing. Because of that, DoH requests are indistinguishable from web traffic. Your ISP or employer can’t block port 443 to stop DoH without also stopping all web browsing. And an ISP that does that will quickly find itself with no customers.
So, from a personal privacy point of view, DoH is a clear win. But from a corporate security point of view it’s a problem. Security appliances like Next-Generation firewalls want to peer inside network traffic to identify security threats, and encryption like DoH makes that harder.
Some are also concerned about the way DoH might centralize trust. Using DNS-over-HTTPs is similar to using a third-party VPN in that it keeps your traffic private inside an encrypted tunnel, but you have to trust the VPN vendor or DNS resolver at the end of the tunnel an awful lot. Because DoH is relatively new there aren’t many DoH resolvers. So instead of everyone’s DNS requests being fulfilled by their respective ISPs they are sent to one of a relatively small number of DoH resolvers, operated by organizations like Google and CloudFlare.
CIRA Canadian Shield
In the case of Canadian Firefox users, their DNS resolver is CIRA. Canadian users who use DoH by default will begin seeing “CIRA Canadian Shield” as their default DNS provider. You can read more about CIRA Canadian Shield on CIRA’s official website here.
“Protecting the privacy of Canadians is a key element of restoring trust on the internet,” says CIRA President and CEO Byron Holland in a statement, “Our goal is to cover as many Canadians as possible with Canadian Shield, and that means finding like-minded partners who share our values. We are proud to be the first Canadian participant in the Trusted Recursive Resolver (TRR) Program and are always seeking out new ways to extend the reach of Canadian Shield to enhance the privacy of Canadians.”